Preauth RCE on NVIDIA Triton Server
https://sites.google.com/site/zhiniangpeng/blogs/Triton-RCE
CDK Global cyberattack impacts thousands of US car dealerships
https://www.bleepingcomputer.com/news/security/cdk-global-cyberattack-impacts-thousands-of-us-car-dealerships/
Scathing report on Medibank cyberattack highlights unenforced MFA
https://www.bleepingcomputer.com/news/security/scathing-report-on-medibank-cyberattack-highlights-unenforced-mfa/
Advance Auto Parts confirms data breach exposed employee information
https://www.bleepingcomputer.com/news/security/advance-auto-parts-confirms-data-breach-exposed-employee-information/
Binary Ninja - Restructuring the Binary Ninja Decompiler
https://binary.ninja/2024/06/19/restructuring-the-decompiler.html
Behind the Great Wall Void Arachne Targets Chinese-Speaking Users With the Winos 4.0 CC Framework | Trend Micro (US)
https://www.trendmicro.com/en_us/research/24/f/behind-the-great-wall-void-arachne-targets-chinese-speaking-user.html
Cloaked and Covert: Uncovering UNC3886 Espionage Operations | Google Cloud Blog
https://cloud.google.com/blog/topics/threat-intelligence/uncovering-unc3886-espionage-operations
"Researchers" exploit Kraken exchange bug, steal $3 million in crypto
https://www.bleepingcomputer.com/news/security/researchers-exploit-kraken-exchange-bug-steal-3-million-in-crypto/
Chrome 126 Update Patches Vulnerability Exploited at Hacking Competition - SecurityWeek
https://www.securityweek.com/chrome-126-update-patches-vulnerability-exploited-at-hacking-competition/
I Will Fucking Piledrive You If You Mention AI Again — Ludicity
https://ludic.mataroa.blog/blog/i-will-fucking-piledrive-you-if-you-mention-ai-again/
2024 Talk Schedule - Google スプレッドシート
https://docs.google.com/spreadsheets/d/1bWoJzp7WP5ATK0X337nZbdZerDcViAaP5qgay0xCdzk/edit?usp=sharing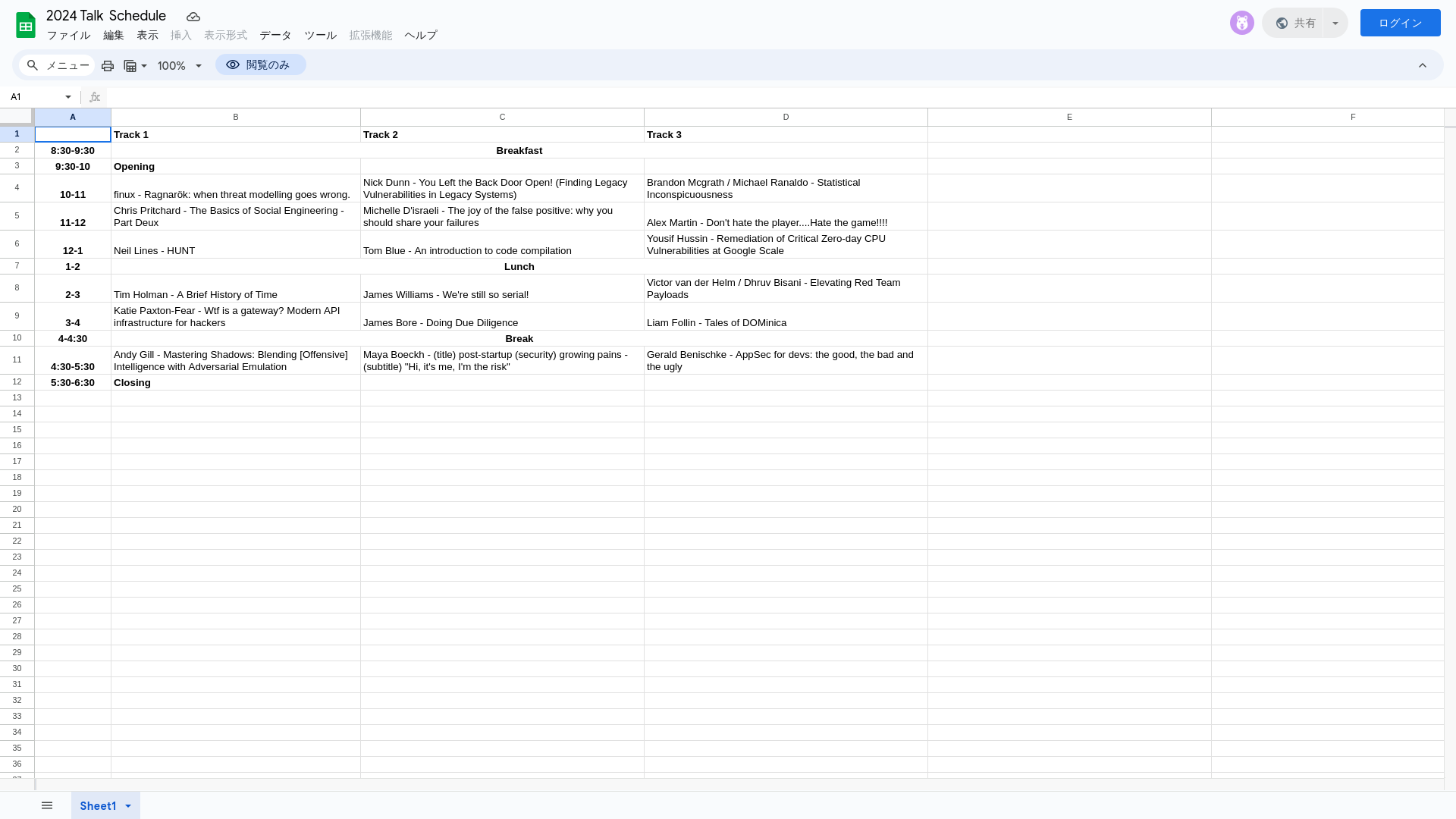
Warning: Markopolo's Scam Targeting Crypto Users via Fake Meeting Software
https://thehackernews.com/2024/06/warning-markopolos-scam-targeting.html
Talks | SteelCon
https://www.steelcon.info/the-event/talk-schedule/
AMD investigates breach after data for sale on hacking forum
https://www.bleepingcomputer.com/news/security/amd-investigates-breach-after-data-for-sale-on-hacking-forum/
wstunnel: Tunnel all your traffic over Websocket or HTTP2 - Bypass firewalls/DPI
https://meterpreter.org/wstunnel-tunnel-all-your-traffic-over-websocket-or-http2-bypass-firewalls-dpi/
Crown Equipment confirms a cyberattack disrupted manufacturing
https://www.bleepingcomputer.com/news/security/crown-equipment-confirms-a-cyberattack-disrupted-manufacturing/
Reversing UK mobile rail tickets
https://eta.st/2023/01/31/rail-tickets.html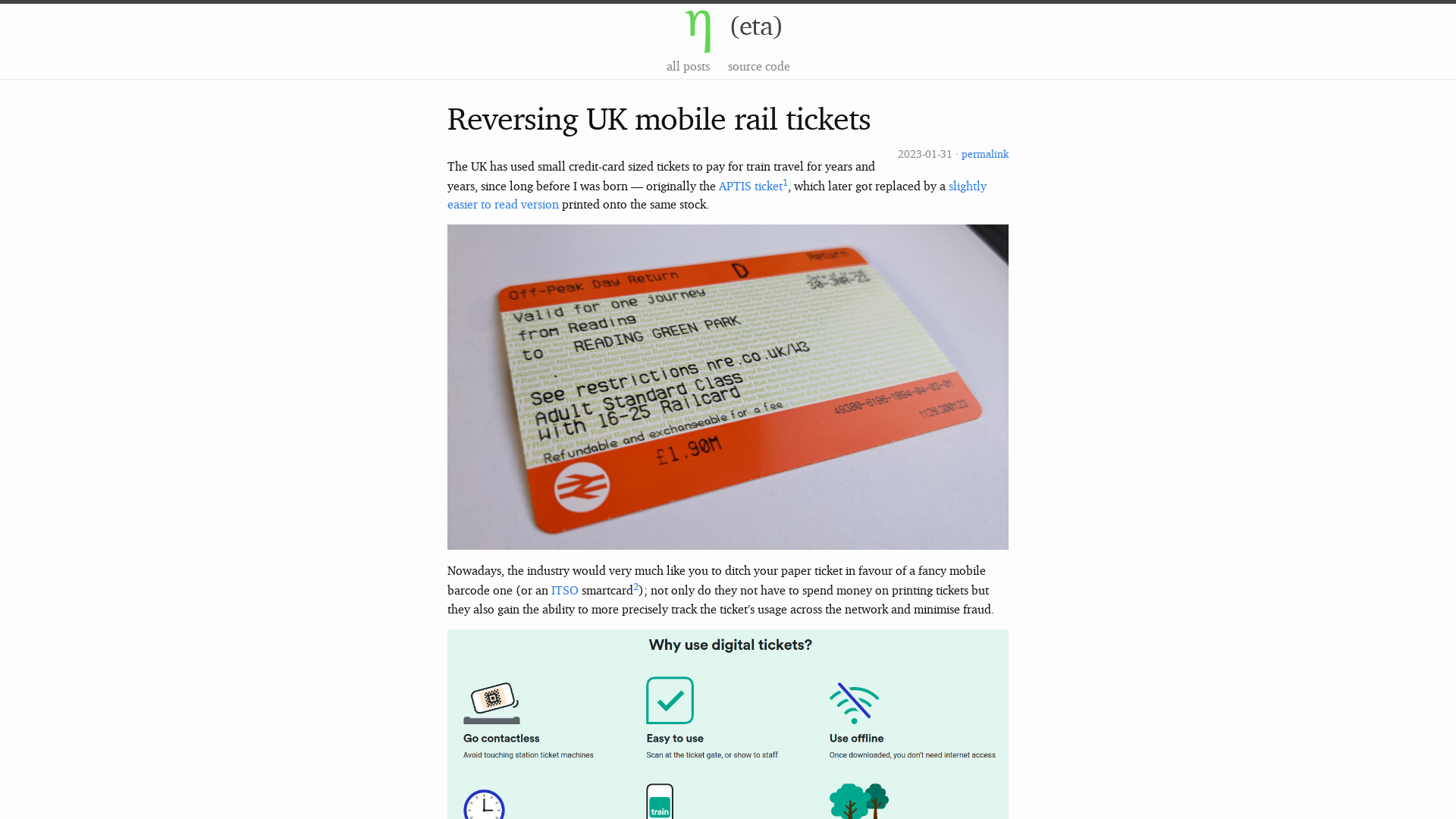
Amtrak Says Guest Rewards Accounts Hacked in Credential Stuffing Attacks - SecurityWeek
https://www.securityweek.com/amtrak-says-guest-rewards-accounts-hacked-in-credential-stuffing-attacks/
![Tools for Humanity | Report #2515808 - [Meetup][World ID][OIDC] Insufficient Filtering of "state" Parameter in Response Mode form_post leads to XSS and ATO | HackerOne](/image/screenshot/8a4e0f34f37cd9d210bfc3535db5bf44.png)
Mailcow Mail Server Flaws Expose Servers to Remote Code Execution
https://thehackernews.com/2024/06/mailcow-mail-server-flaws-expose.html
New Threat Actor 'Void Arachne' Targets Chinese Users with Malicious VPN Installers
https://thehackernews.com/2024/06/void-arachne-uses-deepfakes-and-ai-to.html
(Web-)Insecurity Blog | Sign-in with World ID: XSS and ATO via OIDC Form Post Response Mode
https://security.lauritz-holtmann.de/advisories/tfh-form_post-xss-ato/
EU chat control law proposes scanning your messages — even encrypted ones
https://apple.news/AOl1yIXrtRISFLbYRmCrOSg
Kraken Crypto Exchange Hit by $3 Million Theft Exploiting Zero-Day Flaw
https://thehackernews.com/2024/06/kraken-crypto-exchange-hit-by-3-million.html
http://redsiege.com/wedoff
http://redsiege.com/wedoff
Active Directory Methodology in Pentesting: A Comprehensive Guide | by Very Lazy Tech | Jun, 2024 | Medium
https://medium.com/@verylazytech/active-directory-methodology-in-pentesting-a-comprehensive-guide-fa7e8e5ff9d3
AMD investigates a data breach
https://securityaffairs.com/164676/data-breach/amd-investigates-data-breach.html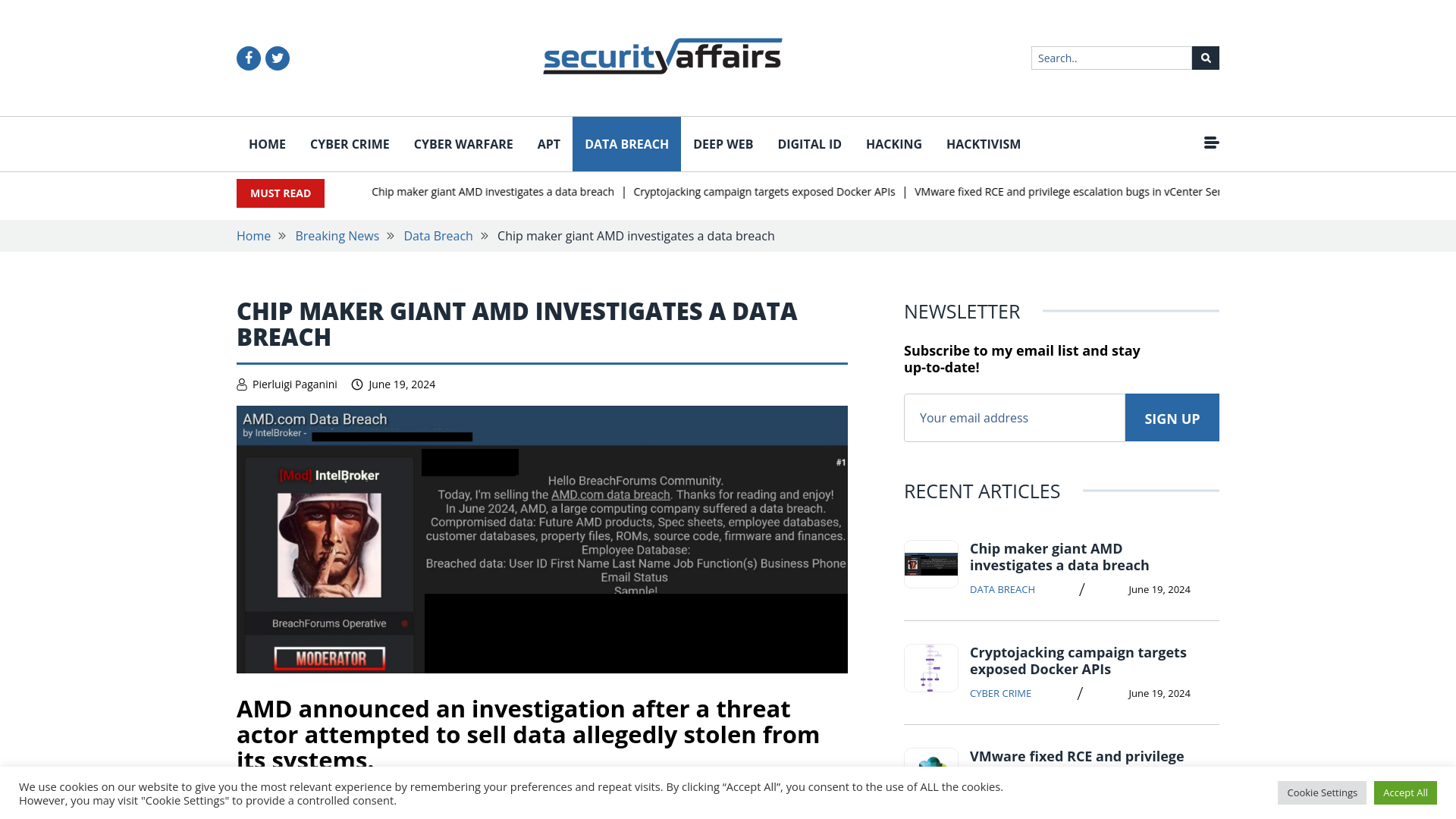
Unveiling the Highly Evasive Loader Targeting Chinese Organizations
https://cybersecurity.att.com/blogs/labs-research/highly-evasive-squidloader-targets-chinese-organizations
UNC3886 Uses Fortinet, VMware 0-Days and Stealth Tactics in Long-Term Spying
https://thehackernews.com/2024/06/chinese-cyber-espionage-group-exploits.html
AMD Investigating Breach Claims After Hacker Offers to Sell Data - SecurityWeek
https://www.securityweek.com/amd-investigating-breach-claims-after-hacker-offers-to-sell-data/