Project Zero: Project Naptime: Evaluating Offensive Security Capabilities of Large Language Models
https://googleprojectzero.blogspot.com/2024/06/project-naptime.html
GitHub - x86matthew/DOSVisor: x86 Real-Mode MS-DOS Emulator using Windows Hypervisor Platform
https://github.com/x86matthew/DOSVisor
T-Mobile denies it was hacked, links leaked data to vendor breach
https://www.bleepingcomputer.com/news/security/t-mobile-denies-it-was-hacked-links-leaked-data-to-vendor-breach/
Binary Ninja - Restructuring the Binary Ninja Decompiler
https://binary.ninja/2024/06/19/restructuring-the-decompiler.html
SolarWinds Serv-U path traversal flaw actively exploited in attacks
https://www.bleepingcomputer.com/news/security/solarwinds-serv-u-path-traversal-flaw-actively-exploited-in-attacks/
An unpatched bug allows anyone to impersonate Microsoft corporate email accounts
https://securityaffairs.com/164675/hacking/expert-warns-of-a-spoofing-bug.html
Preauth RCE on NVIDIA Triton Server
https://sites.google.com/site/zhiniangpeng/blogs/Triton-RCE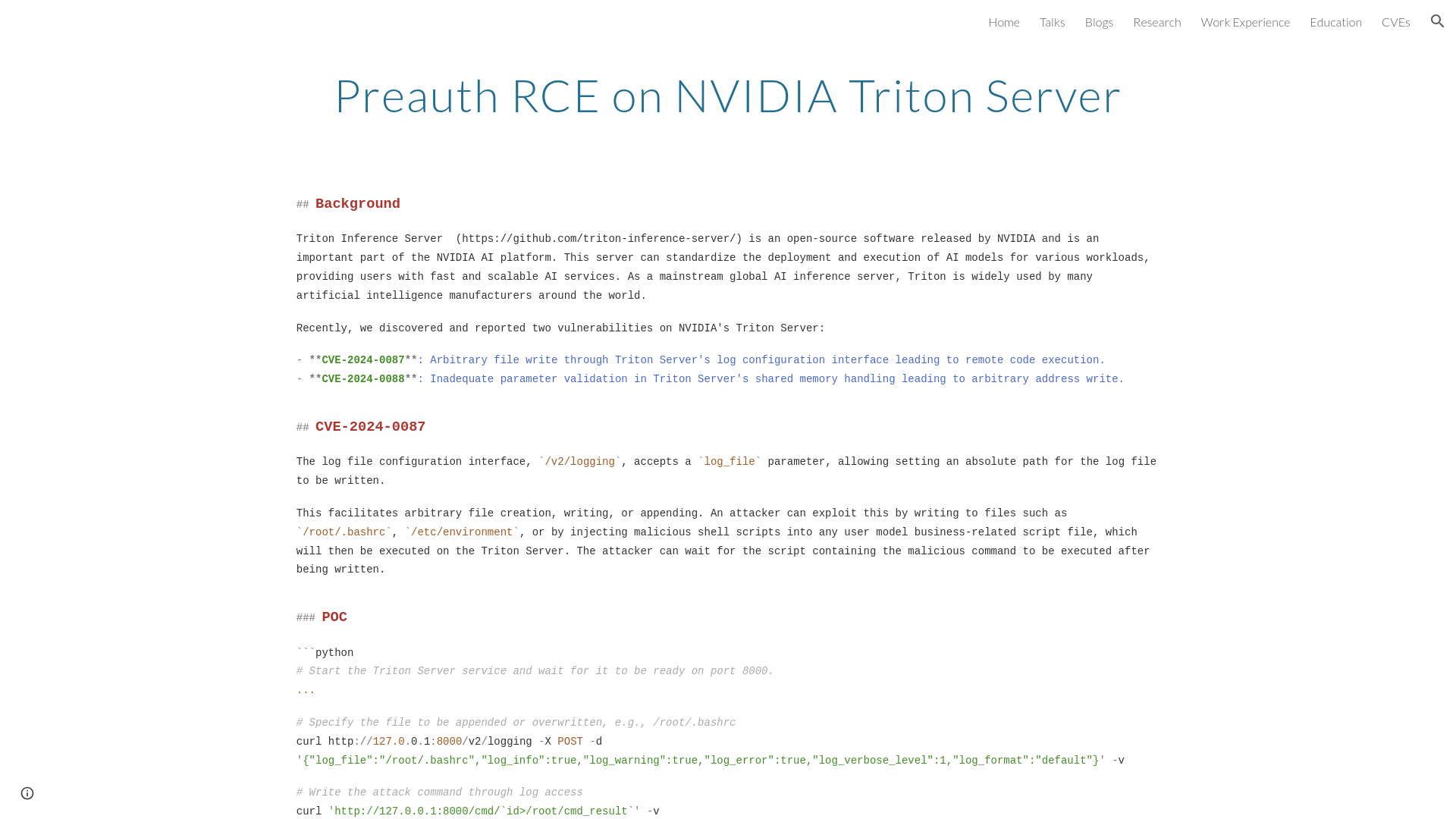
CDK Global hacked again while recovering from first cyberattack
https://www.bleepingcomputer.com/news/security/cdk-global-hacked-again-while-recovering-from-first-cyberattack/
Beyond the @ Symbol: Exploiting the Flexibility of Email Addresses For Offensive Purposes / modzero
https://modzero.com/en/blog/beyond_the_at_symbol/
TURPENTINE: CVE-2024-27815
https://jprx.io/cve-2024-27815/
Experts Uncover New Evasive SquidLoader Malware Targeting Chinese Organizations
https://thehackernews.com/2024/06/experts-uncover-new-evasive-squidloader.html
Analyzing Mutation-Coded - VM Protect and Alcatraz English | Keowu Blog's
https://keowu.re/posts/Analyzing-Mutation-Coded-VM-Protect-and-Alcatraz-English/
Researchers Uncover UEFI Vulnerability Affecting Multiple Intel CPUs
https://thehackernews.com/2024/06/researchers-uncover-uefi-vulnerability.html
Sustained Campaign Using Chinese Espionage Tools Targets Telcos | Symantec Enterprise Blogs
https://symantec-enterprise-blogs.security.com/threat-intelligence/telecoms-espionage-asia
Atlassian Patches High-Severity Vulnerabilities in Confluence, Crucible, Jira - SecurityWeek
https://www.securityweek.com/atlassian-patches-high-severity-vulnerabilities-in-confluence-crucible-jira/
Alleged researchers stole $3 million from Kraken exchange
https://securityaffairs.com/164694/hacking/kraken-zero-day-cyber-theft.html
Hundreds of PC, Server Models Possibly Affected by Serious Phoenix UEFI Vulnerability - SecurityWeek
https://www.securityweek.com/hundreds-of-pc-server-models-possibly-affected-by-serious-phoenix-uefi-vulnerability/
Reversing UK mobile rail tickets
https://eta.st/2023/01/31/rail-tickets.html
TikTok facing fresh lawsuit in US over children's privacy | Malwarebytes
https://www.malwarebytes.com/blog/news/2024/06/tiktok-facing-fresh-lawsuit-in-us-over-childrens-privacy
Russian spies' hacking campaign is 'endangering' French diplomatic interests
https://therecord.media/france-anssi-warning-russia-hacking-campaign-svr
Analysis 4a553b2e2ff7003b55a8923047d2f76cacd258317810b0107004aa7101e0fca2.exe (MD5: C812ECF0E689B3E85A15D43943F6E077) Malicious activity - Interactive analysis ANY.RUN
https://app.any.run/tasks/900dc8c9-ef72-4b27-8f1d-840c61ce43cf/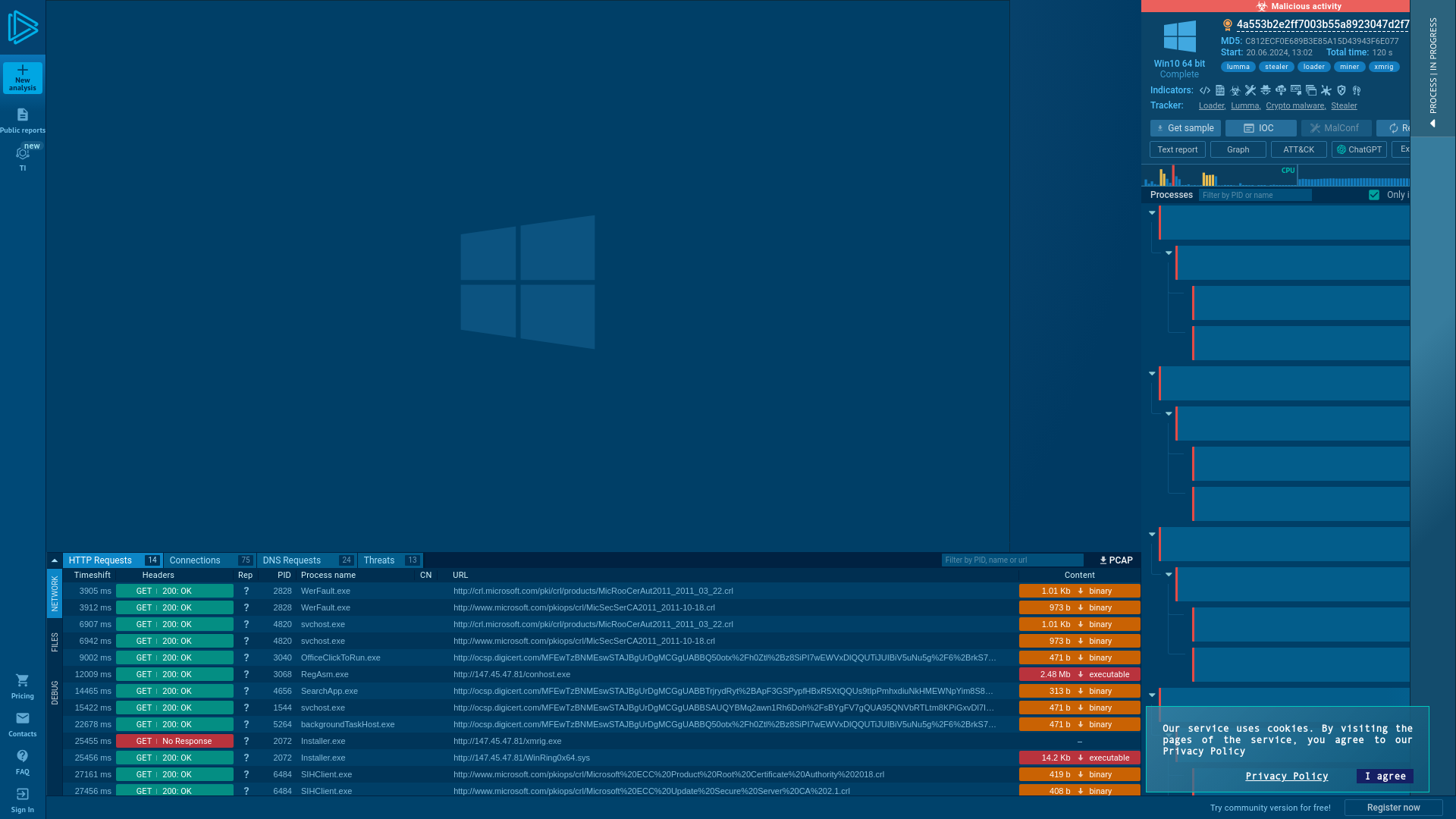
How to break the token theft cyber-attack chain - Microsoft Community Hub
https://techcommunity.microsoft.com/t5/microsoft-entra-blog/how-to-break-the-token-theft-cyber-attack-chain/ba-p/4062700
New Rust-based Fickle Malware Uses PowerShell for UAC Bypass and Data Exfiltration
https://thehackernews.com/2024/06/new-rust-based-fickle-malware-uses.html
UNC3886 hackers use Linux rootkits to hide on VMware ESXi VMs
https://www.bleepingcomputer.com/news/security/unc3886-hackers-use-linux-rootkits-to-hide-on-vmware-esxi-vms/
KrebsOnSecurity Threatened with Defamation Lawsuit Over Fake Radaris CEO – Krebs on Security
https://krebsonsecurity.com/2024/06/krebsonsecurity-threatened-with-defamation-lawsuit-over-fake-radaris-ceo/
Exploiting CVE-2024-21378 – Remote Code Execution in Microsoft Outlook
https://www.netspi.com/blog/technical-blog/red-team-operations/microsoft-outlook-remote-code-execution-cve-2024-21378/
Atlassian fixed six high-severity bugs in Confluence
https://securityaffairs.com/164743/security/atlassian-confluence-crucible-jira-flaws.html
Fickle Stealer Distributed via Multiple Attack Chain | FortiGuard Labs
https://www.fortinet.com/blog/threat-research/fickle-stealer-distributed-via-multiple-attack-chain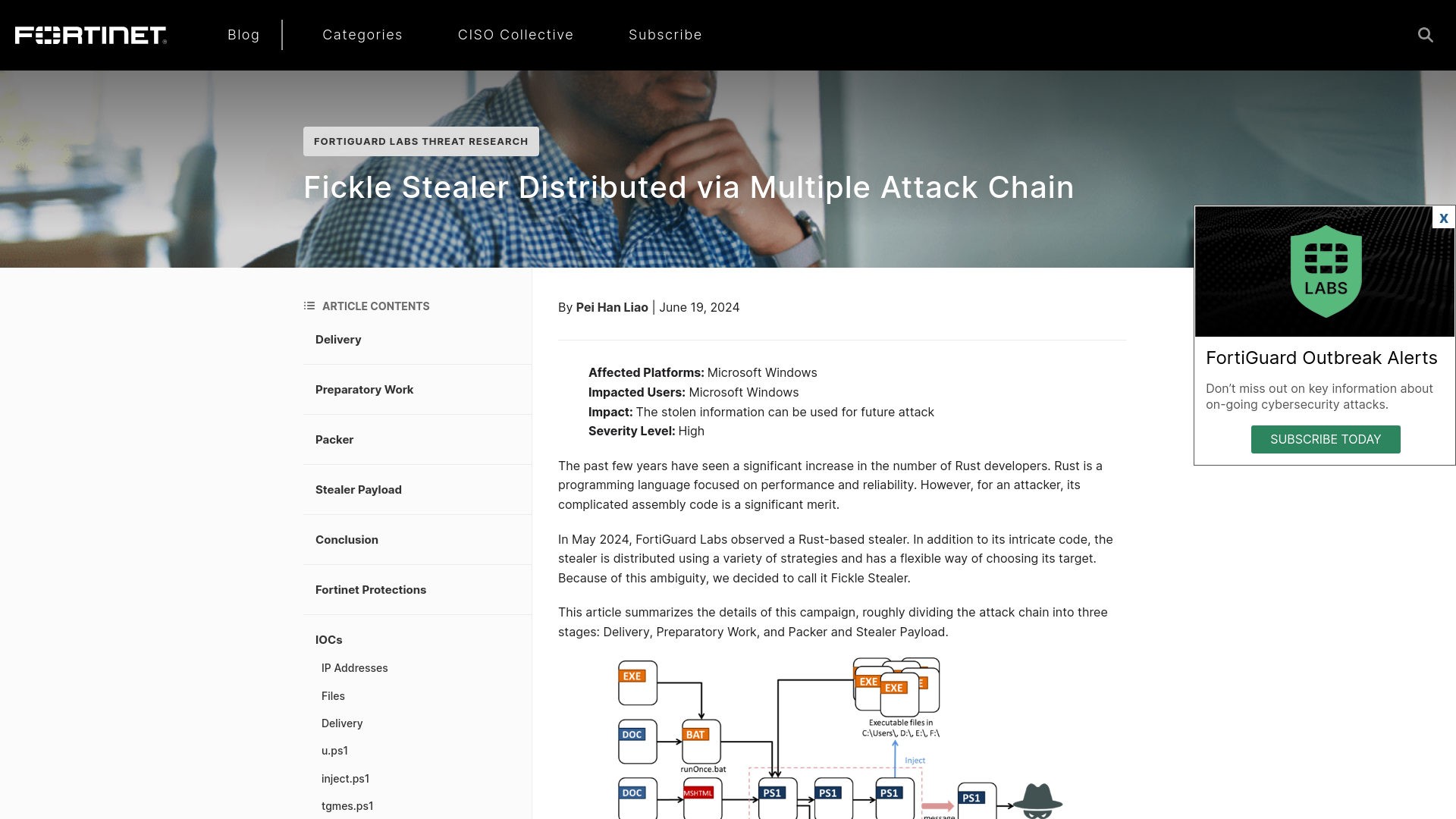
Linux version of RansomHub ransomware targets VMware ESXi VMs
https://www.bleepingcomputer.com/news/security/linux-version-of-ransomhub-ransomware-targets-vmware-esxi-vms/
Chinese Cyber Espionage Targets Telecom Operators in Asia Since 2021
https://thehackernews.com/2024/06/chinese-cyber-espionage-targets-telecom.html
Decade-Long Cyber Assault on Asian Telecoms Traced to Chinese State Hackers - SecurityWeek
https://www.securityweek.com/long-running-chinese-espionage-campaign-targets-telecom-firms-in-asian-country/