VMware fixes critical vCenter RCE vulnerability, patch now
https://www.bleepingcomputer.com/news/security/vmware-fixes-critical-vcenter-rce-vulnerability-patch-now/
[Linux Kernel Exploitation 0x0] Debugging the Kernel with QEMU
https://blog.k3170makan.com/2020/11/linux-kernel-exploitation-0x0-debugging.html![[Linux Kernel Exploitation 0x0] Debugging the Kernel with QEMU](/image/screenshot/de98caf8aeee872ce15b3aaa836d9fa9.png)
Google Bug Hunters - Google Bug Hunters
http://bughunters.google.com
Fake Google Chrome errors trick you into running malicious PowerShell scripts
https://www.bleepingcomputer.com/news/security/fake-google-chrome-errors-trick-you-into-running-malicious-powershell-scripts/
Everything You Need to Know About IDOR (Insecure Direct Object References) | by ayşe bilge gündüz | Medium
https://medium.com/@aysebilgegunduz/everything-you-need-to-know-about-idor-insecure-direct-object-references-375f83e03a87
Cybercriminals Exploit Free Software Lures to Deploy Hijack Loader and Vidar Stealer
https://thehackernews.com/2024/06/cybercriminals-exploit-free-software.html
How to analyze main input file & its dependencies in a single IDA database - YouTube
https://youtu.be/paNBm7bvGtY
Mobile OAuth Attacks - iOS URL Scheme Hijacking Revamped :: Evan Connelly - Security Research Blog
https://evanconnelly.github.io/post/ios-oauth/
How quickly can attackers guess your password? | Securelist
https://securelist.com/passworde-brute-force-time/112984/
TROOPERS24
https://troopers.de/troopers24/agenda/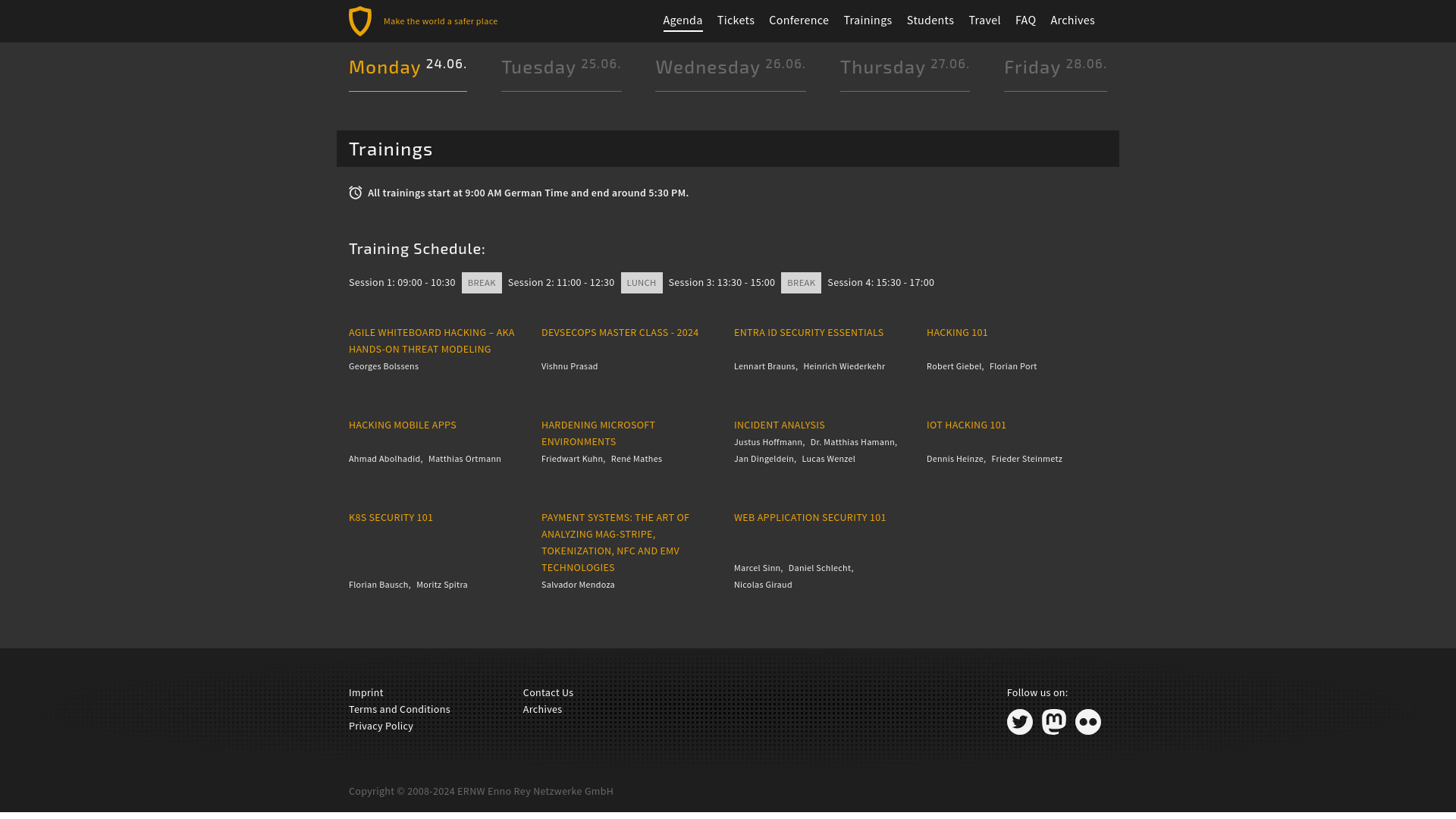
Surface UEFI: Evolution in boot, security & device management to build an industry leading secure PC - Microsoft Community Hub
https://techcommunity.microsoft.com/t5/surface-it-pro-blog/surface-uefi-evolution-in-boot-security-amp-device-management-to/ba-p/4159998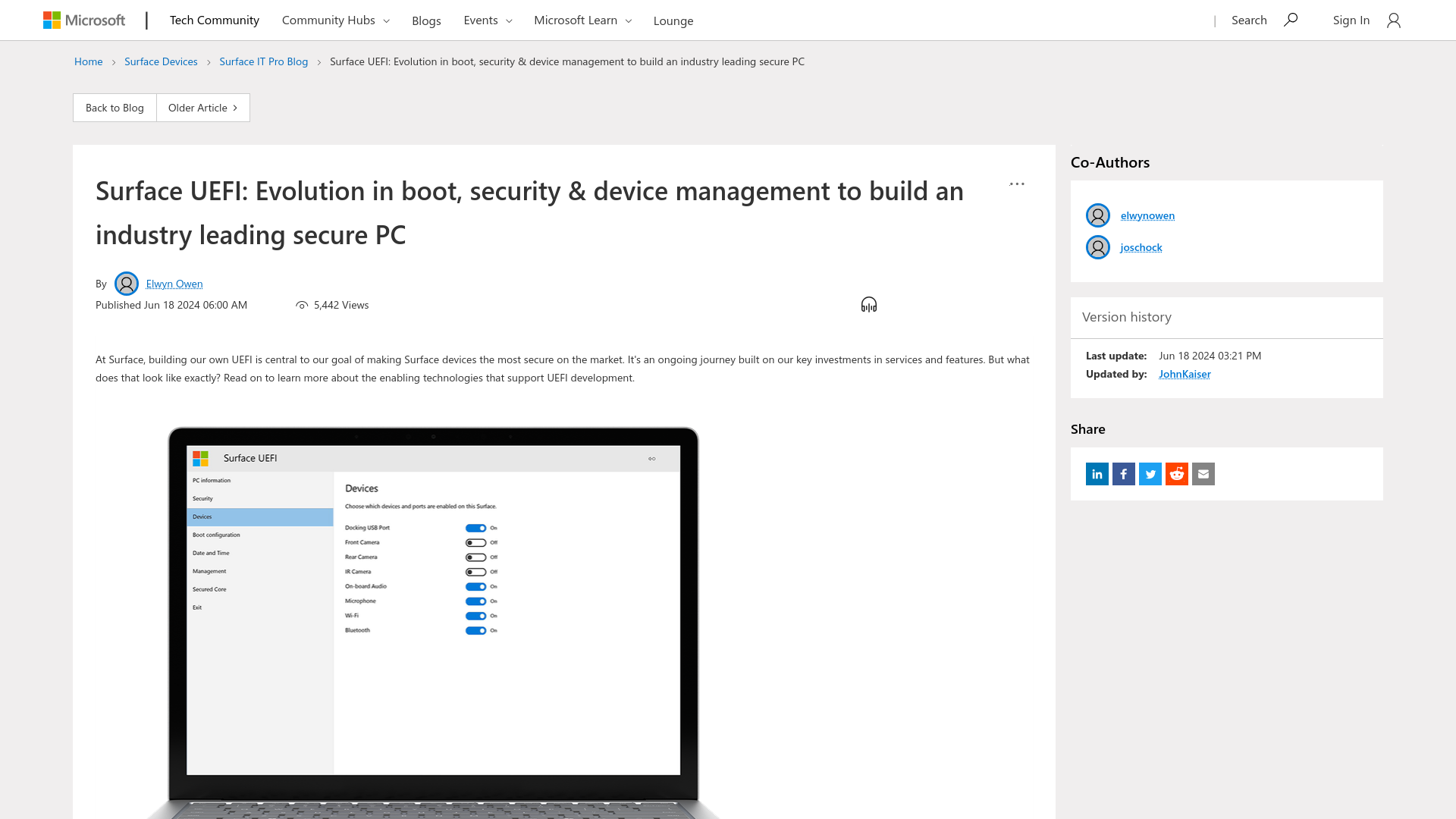
How Twitch Helper Can Be Used for Privilege Escalation
https://blog.kandji.io/twitch-privileged-helper
GitHub - YaS5in3/Bug-Bounty-Wordlists
https://github.com/YaS5in3/Bug-Bounty-Wordlists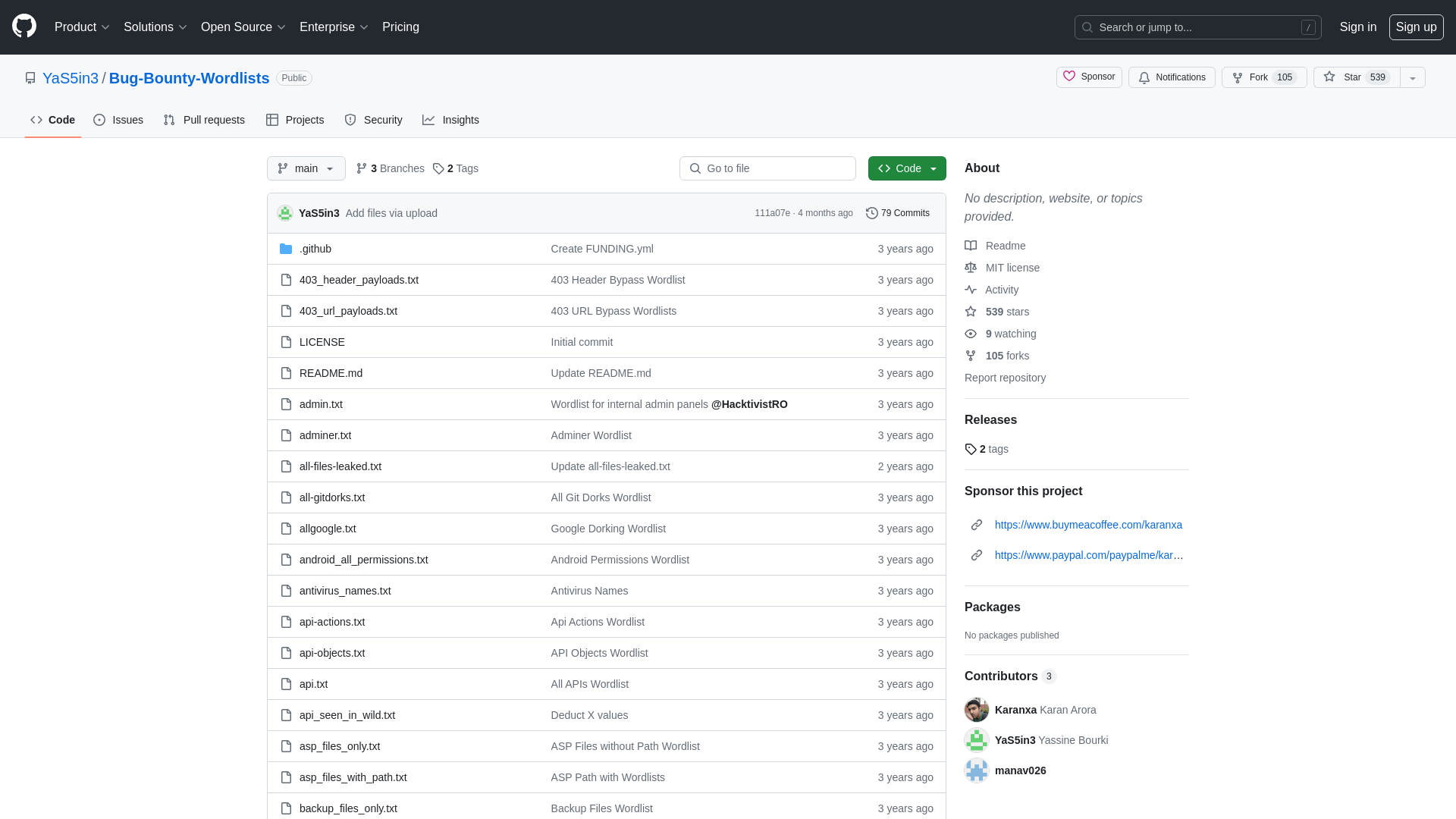
Singapore Police Extradites Malaysians Linked to Android Malware Fraud
https://thehackernews.com/2024/06/singapore-police-extradites-malaysians.html
Edge services are extremely attractive targets to attackers - Help Net Security
https://www.helpnetsecurity.com/2024/06/18/vulnerable-software-mass-exploitation/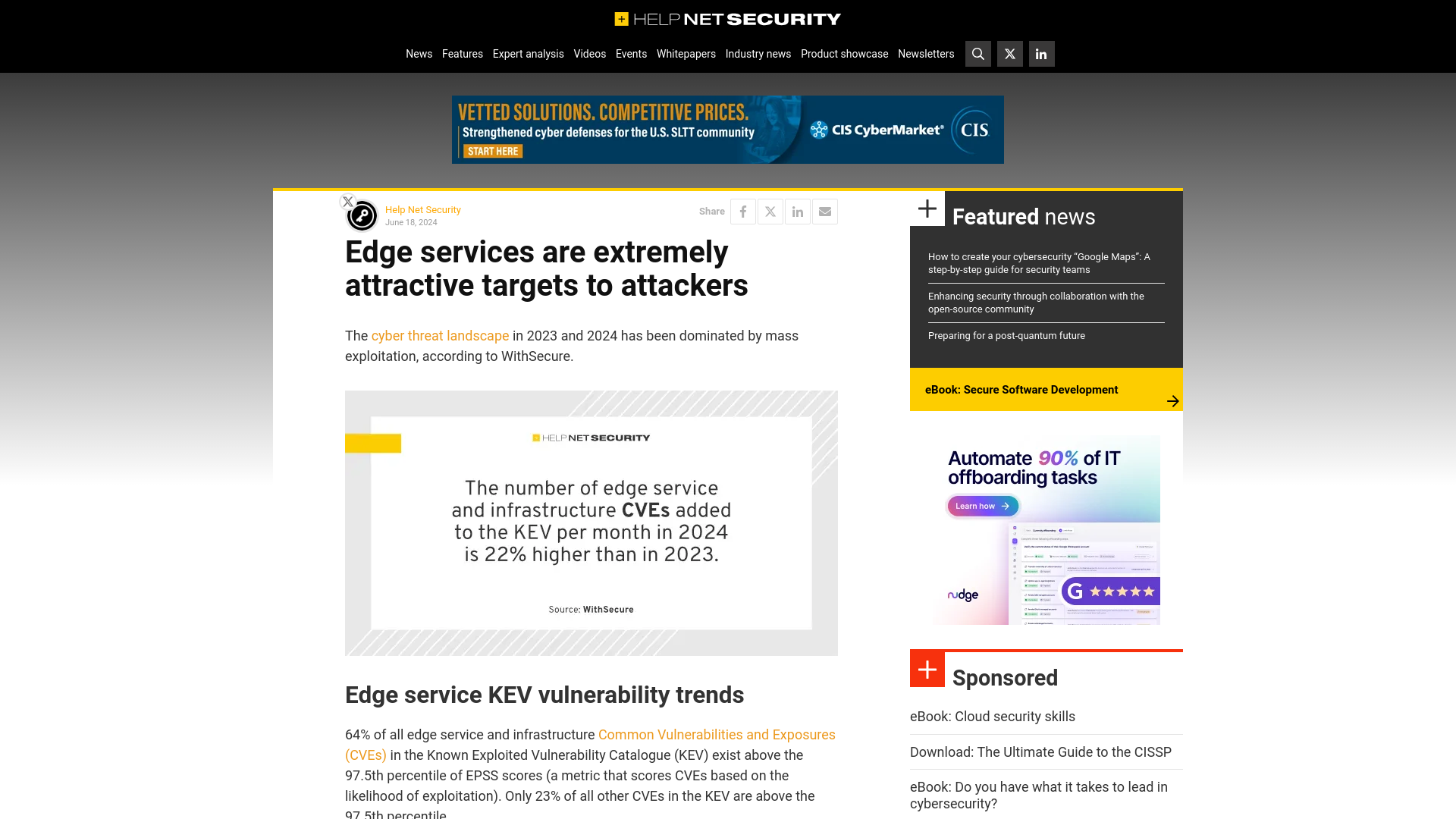
[2406.10016] Deobfuscation of Semi-Linear Mixed Boolean-Arithmetic Expressions
https://arxiv.org/abs/2406.10016![[2406.10016] Deobfuscation of Semi-Linear Mixed Boolean-Arithmetic Expressions](/image/screenshot/8f35c4087b4f61a5f5a9d9dde1efc661.png)
Keytronic confirms data breach after ransomware attack
https://securityaffairs.com/164642/data-breach/keytronic-blackbasta-ransomware.html
VMware Issues Patches for Cloud Foundation, vCenter Server, and vSphere ESXi
https://thehackernews.com/2024/06/vmware-issues-patches-for-cloud.html
New BadSpace Backdoor Deployed in Drive-By Attacks - SecurityWeek
https://www.securityweek.com/new-badspace-backdoor-deployed-in-drive-by-attacks/
ONNX phishing service targets Microsoft 365 accounts at financial firms
https://www.bleepingcomputer.com/news/security/onnx-phishing-service-targets-microsoft-365-accounts-at-financial-firms/
Bug Bounty Programs, Hacking Contests Power China's Cyber Offense
https://www.darkreading.com/cybersecurity-operations/bug-bounty-programs-hacking-contests-power-chinas-cyber-offense
Forest Compromise Through AMA Abuse – Q&D Security
https://blog.qdsecurity.se/2024/04/07/forest-compromise-through-ama-abuse/
Support Content Notification - Support Portal - Broadcom support portal
https://support.broadcom.com/web/ecx/support-content-notification/-/external/content/SecurityAdvisories/0/24453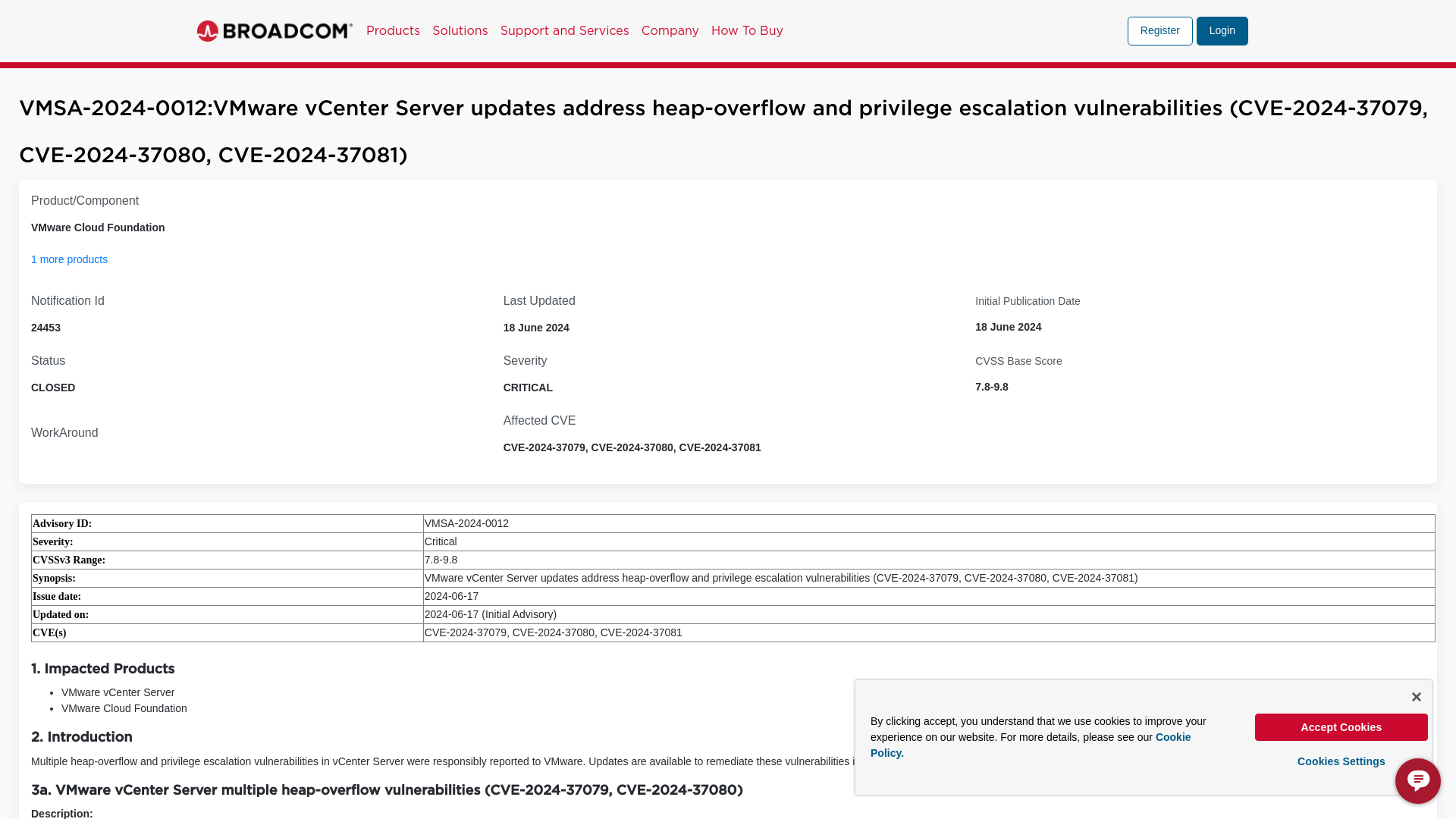
Signal Foundation Warns Against EU's Plan to Scan Private Messages for CSAM
https://thehackernews.com/2024/06/signal-foundation-warns-against-eus.html