Malicious VSCode extensions with millions of installs discovered
https://www.bleepingcomputer.com/news/security/malicious-visual-studio-code-extensions-with-millions-of-installs-discovered/
Fuzzing Redux, leveraging AFL++ Frida-Mode on Android native libraries - KnifeCoat
https://knifecoat.com/Posts/Fuzzing+Redux%2C+leveraging+AFL%2B%2B+Frida-Mode+on+Android+native+libraries
The CTI Analyst Challenge
https://blog.bushidotoken.net/2024/06/the-cti-analyst-challenge.html
New York Times source code stolen using exposed GitHub token
https://www.bleepingcomputer.com/news/security/new-york-times-source-code-stolen-using-exposed-github-token/
GitHub - dazzyddos/HSC24RedTeamInfra: Slides and Codes used for the workshop Red Team Infrastructure Automation
https://github.com/dazzyddos/HSC24RedTeamInfra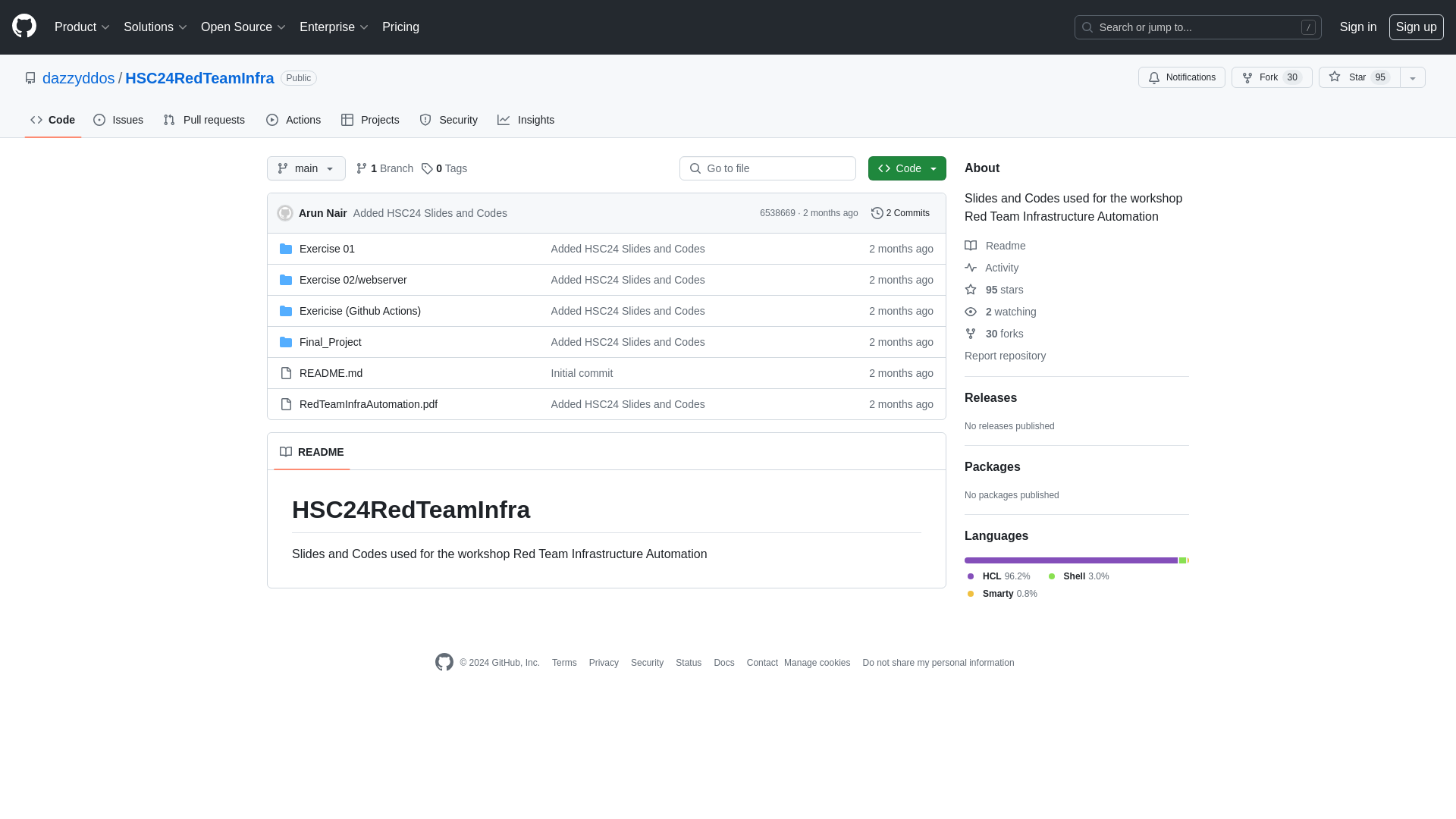
Abusing auto mail responders to access internal workplaces | by Rikesh Baniya | Jun, 2024 | Medium
https://link.medium.com/O0D1BuLugKb
PE Section names – re-visited, again | Hexacorn
https://www.hexacorn.com/blog/2024/06/08/pe-section-names-re-visited-again-2/
Develop your own C# Obfuscator – Ribbit-ing Cybersecurity
https://www.ribbiting-sec.info/posts/2024-06-05_csharp_obfuscator/
Workshops - DEATHCon 2024 - Detection Engineering and Threat Hunting
https://deathcon.io/workshops.html
Malware and cryptography 28: RC4 payload encryption. Simple Nim example. - cocomelonc
https://cocomelonc.github.io/malware/2024/06/01/malware-cryptography-28.html
CyberDefenseReport_%20From%20Vegas%20to%20Chengdu.pdf
https://css.ethz.ch/content/dam/ethz/special-interest/gess/cis/center-for-securities-studies/pdfs/CyberDefenseReport_%20From%20Vegas%20to%20Chengdu.pdf
GhostRace - vusec
https://www.vusec.net/projects/ghostrace/
Week 23 – 2024 – This Week In 4n6
https://thisweekin4n6.com/2024/06/09/week-23-2024/