TangledWinExec/ProtectedProcess at main · daem0nc0re/TangledWinExec · GitHub
https://github.com/daem0nc0re/TangledWinExec/tree/main/ProtectedProcess#ppeditor
CyberThreatIntel/Yara.md at master · StrangerealIntel/CyberThreatIntel · GitHub
https://github.com/StrangerealIntel/CyberThreatIntel/blob/master/101/Yara.md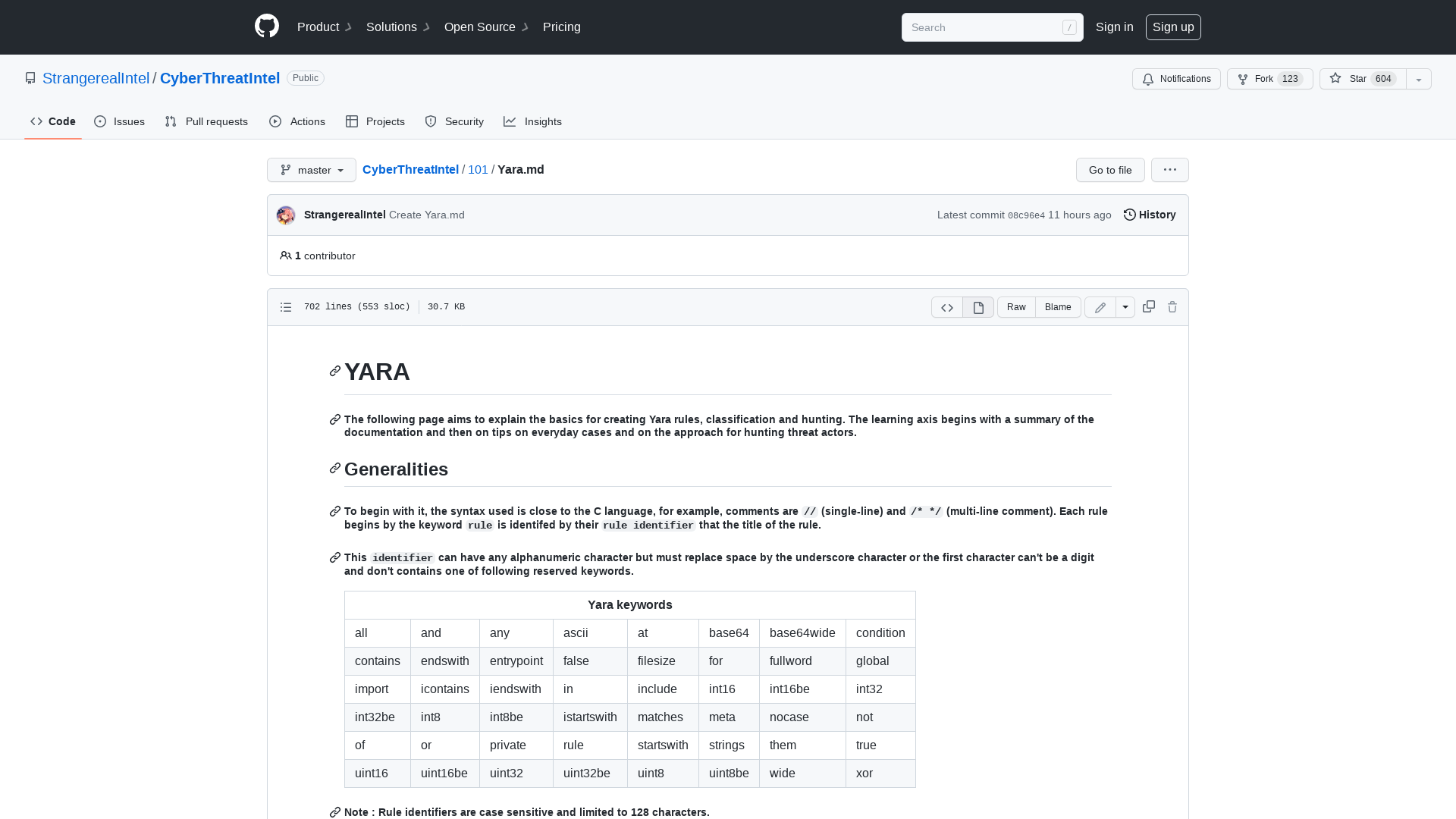
Introduction to the Windows Filtering Platform – Pavel Yosifovich
http://scorpiosoftware.net/2022/12/25/introduction-to-the-windows-filtering-platform/
ProxyNotShellRelay | rw.md
https://rw.md/2022/11/09/ProxyNotRelay.html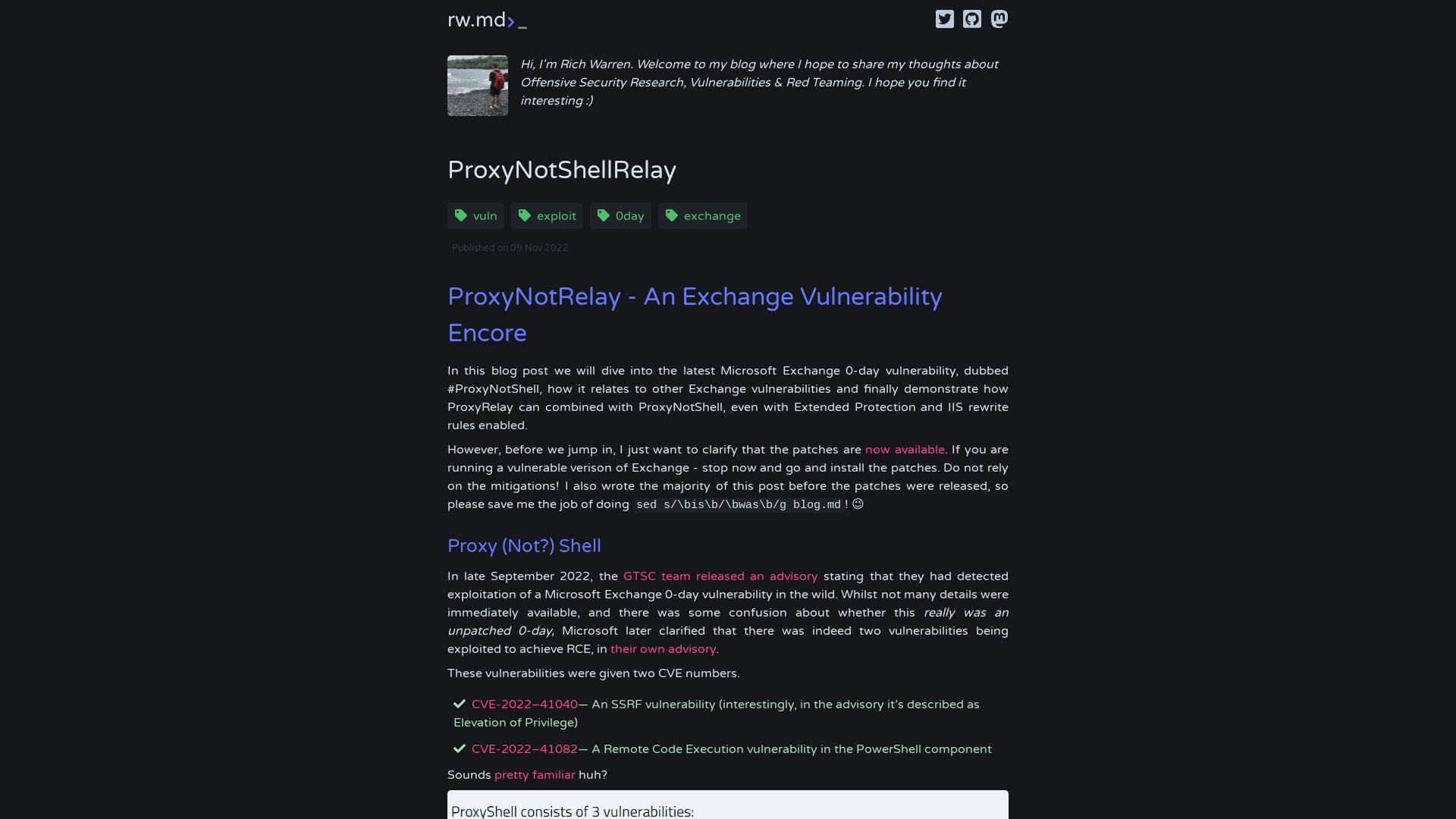
What you need to know about OpenAI's new ChatGPT bot - and how it affects your security | SANS Webinar
https://www.sans.org/u/1ofA
PrivateLoader PPI Service Found Distributing Info-Stealing RisePro Malware
https://thehackernews.com/2022/12/privateloader-ppi-service-found.html
GuLoader Malware Utilizing New Techniques to Evade Security Software
https://thehackernews.com/2022/12/guloader-malware-utilizing-new.html
ThreatFox | Aurora Stealer
https://threatfox.abuse.ch/browse/tag/Aurora%20Stealer/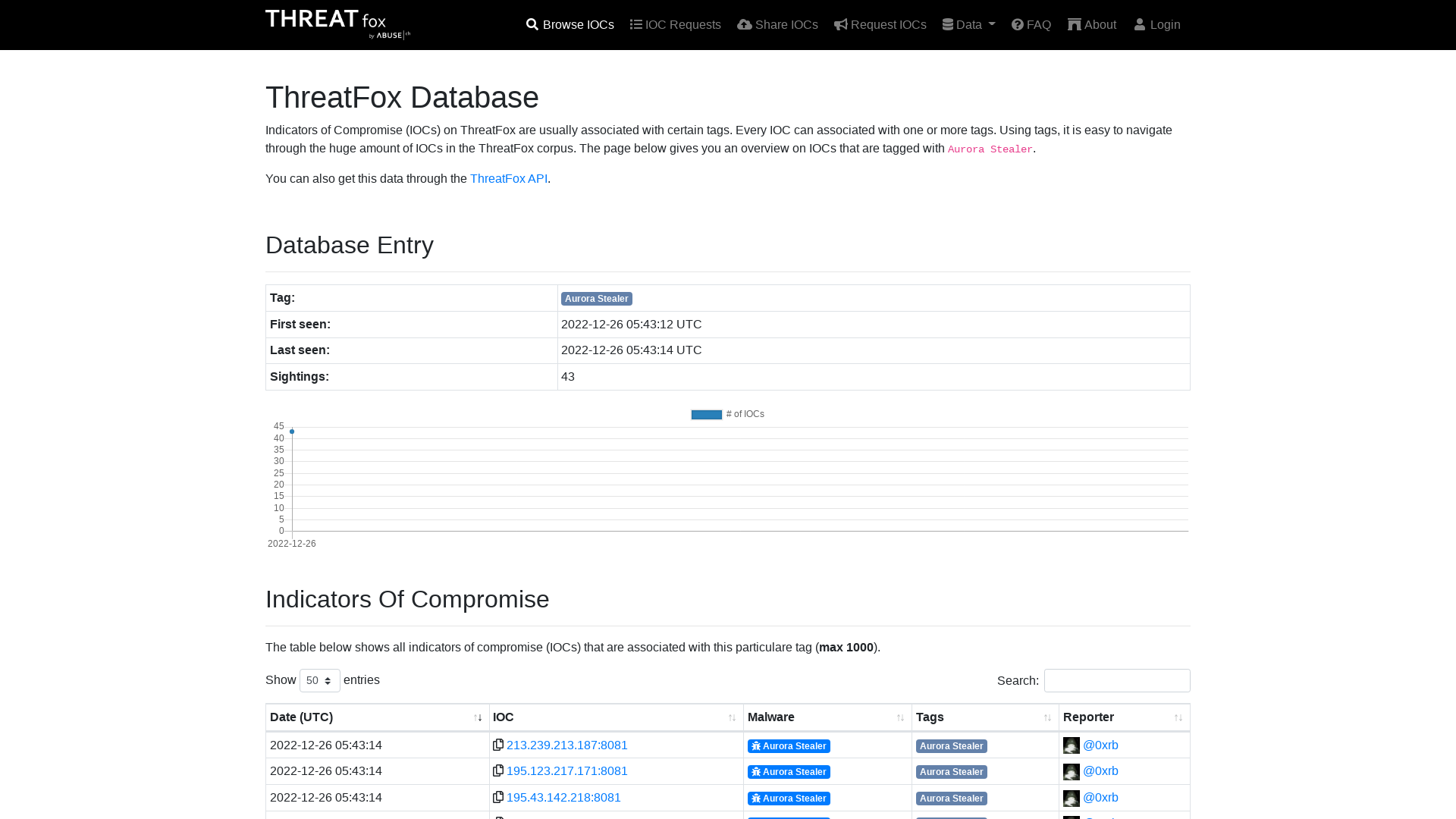
GitHub - zhuowei/WDBFontOverwrite: Proof-of-concept app to overwrite fonts on iOS using CVE-2022-46689.
https://github.com/zhuowei/WDBFontOverwrite
sophoslabs-uncut-mykings-report.pdf
https://www.sophos.com/en-us/medialibrary/pdfs/technical-papers/sophoslabs-uncut-mykings-report.pdf
Exploit Notes
https://exploit-notes.hdks.org/
Trojanized Windows 10 Operating System Installers Targeted Ukrainian Government | Mandiant
https://www.mandiant.com/resources/blog/trojanized-windows-installers-ukrainian-government
Linux kernel exploit development - Breaking Bits
https://breaking-bits.gitbook.io/breaking-bits/exploit-development/linux-kernel-exploit-development
Lord Of The Ring0 - Part 2 | A tale of routines, IOCTLs and IRPs - Ido Veltzman - Security Blog
https://idov31.github.io/2022/08/04/lord-of-the-ring0-p2.html
GitHub - harsh-bothra/SecurityExplained: SecurityExplained is a new series after the previous learning challenge series #Learn365. The aim of #SecurityExplained series is to create informational content in multiple formats and share with the community to enable knowledge creation and learning.
https://github.com/harsh-bothra/SecurityExplained
OFRAK - Unpack, Modify, And Repack Binaries
http://www.kitploit.com/2022/12/ofrak-unpack-modify-and-repack-binaries.html
Lord Of The Ring0 - Part 1 | Introduction - Ido Veltzman - Security Blog
https://idov31.github.io/2022/07/14/lord-of-the-ring0-p1.html
FENICSインターネットサービスに関するネットワーク機器からの不正な通信について : 富士通
https://www.fujitsu.com/jp/services/infrastructure/network/news/2022/1223.html
APT_REPORT/VB2022-Exploit-archaeology-a-forensic-history-of-in-the-wild-NSO-Group-exploits.pdf at master · blackorbird/APT_REPORT · GitHub
https://github.com/blackorbird/APT_REPORT/blob/master/NSOGroup/VB2022-Exploit-archaeology-a-forensic-history-of-in-the-wild-NSO-Group-exploits.pdf
Lord Of The Ring0 - Part 3 | Sailing to the land of the user (and debugging the ship) - Ido Veltzman - Security Blog
https://idov31.github.io/2022/10/30/lord-of-the-ring0-p3.html
GitHub - Bdenneu/CVE-2022-33679: One day based on https://googleprojectzero.blogspot.com/2022/10/rc4-is-still-considered-harmful.html
https://github.com/Bdenneu/CVE-2022-33679
OWASSRF: CrowdStrike Identifies New Method for Bypassing ProxyNotShell Mitigations
https://www.crowdstrike.com/blog/owassrf-exploit-analysis-and-recommendations/
Windows 11 reverse shell | defender bypass | Medium
https://medium.com/@vostiar.patrik/windows-11-reverse-shell-in-7steps-undetected-by-windows-defender-1c4e5e3e8d30
MISP 2.4.167 released with many improvements, bugs fixed and security fixes.
https://www.misp-project.org/2022/12/26/MISP.2.4.167.released.html/
TKC会員事務所向けに提供しているメールサービスが不正アクセスを受けた可能性のご報告 | トピックス | TKCグループ
https://www.tkc.jp/company/topics/2022/20221223/
Guide to Reversing and Exploiting iOS binaries Part 2: ARM64 ROP Chains
https://www.inversecos.com/2022/06/guide-to-reversing-and-exploiting-ios.html
2022 Top Five Immediate Threats in Geopolitical Context
https://thehackernews.com/2022/12/2022-top-five-immediate-threats-in.html
GitHub - PabloMK7/ENLBufferPwn: Information and PoC about the ENLBufferPwn vulnerability
https://github.com/PabloMK7/ENLBufferPwn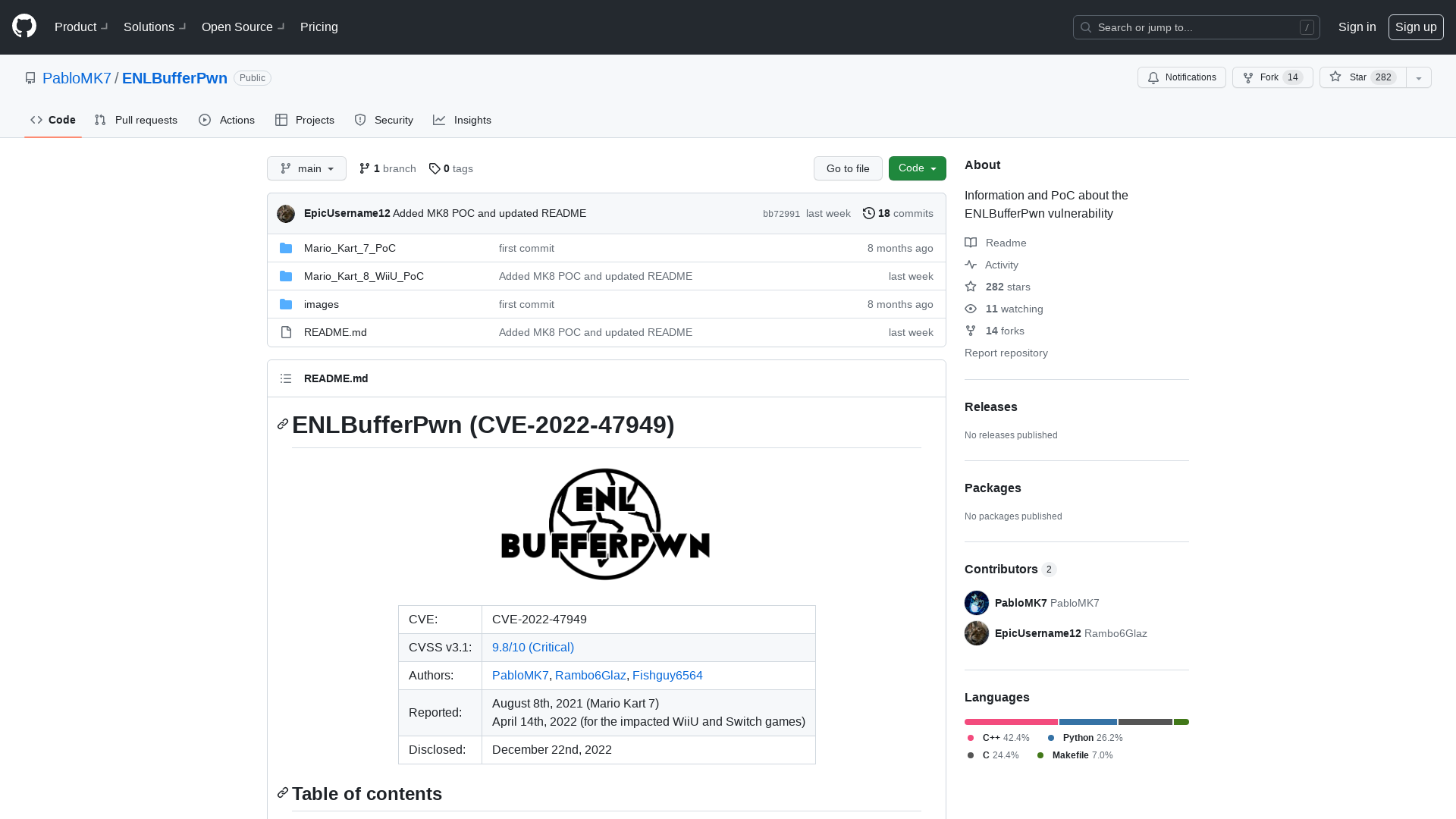
GitHub - mgeeky/Penetration-Testing-Tools: A collection of more than 170+ tools, scripts, cheatsheets and other loots that I've developed over years for Red Teaming/Pentesting/IT Security audits purposes.
https://github.com/mgeeky/Penetration-Testing-Tools
GitHub - sensepost/impersonate: A windows token impersonation tool
https://github.com/sensepost/impersonate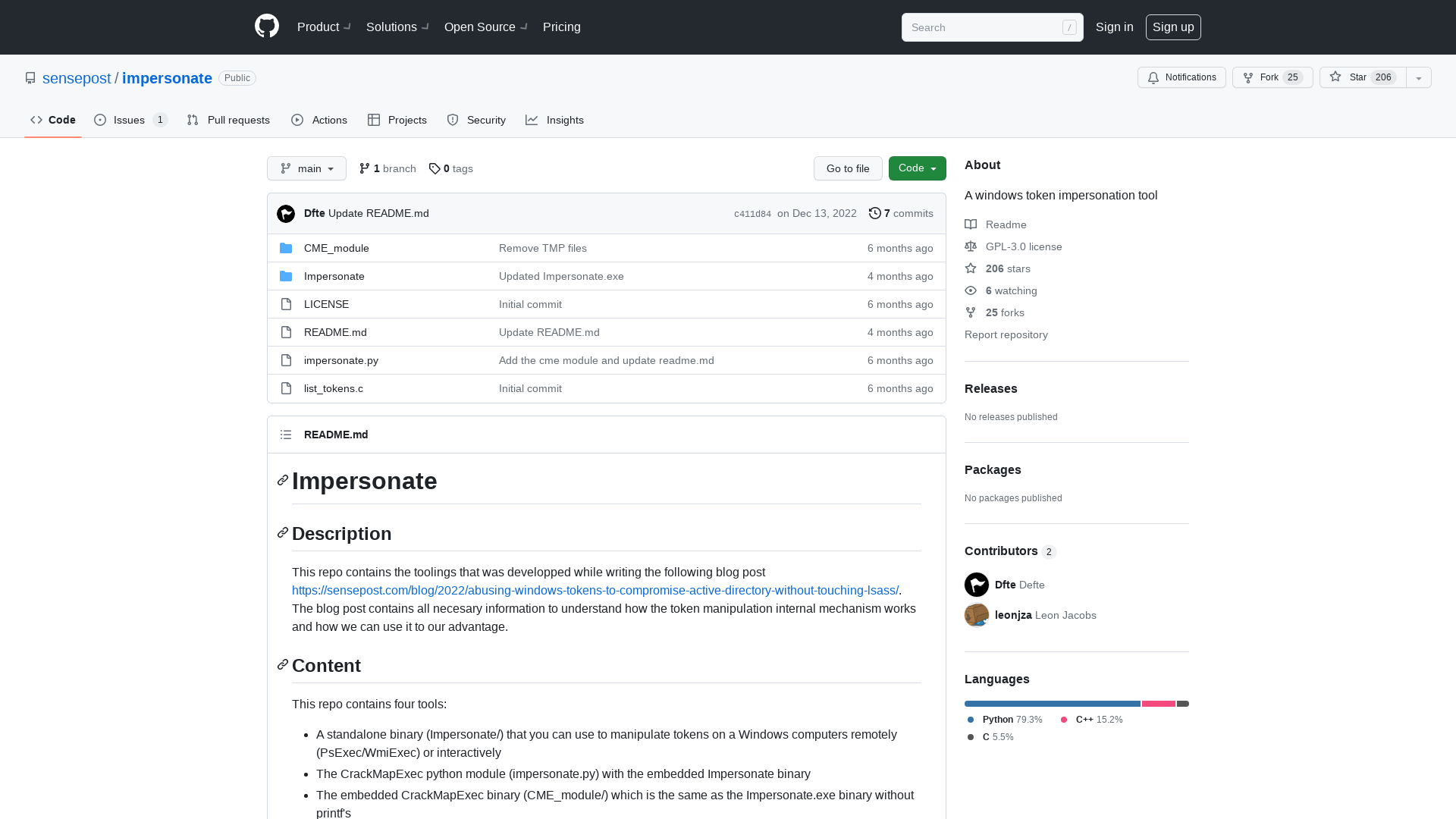
Sleeping with the Enemy: A Best Practice Guide for Attacker Engagement - YouTube
https://youtu.be/CIqGCPRY8WU
Reverse Engineering Tiktok's VM Obfuscation (Part 1)
https://nullpt.rs/reverse-engineering-tiktok-vm-1
How to Reverse Engineer and Patch an iOS Application for Beginners: Part I
https://www.inversecos.com/2022/06/how-to-reverse-engineer-and-patch-ios.html
Havoc - Modern and malleable post-exploitation command and control framework
https://ift.tt/w2hU5Rs
Overview of GLIBC heap exploitation techniques
https://0x434b.dev/overview-of-glibc-heap-exploitation-techniques/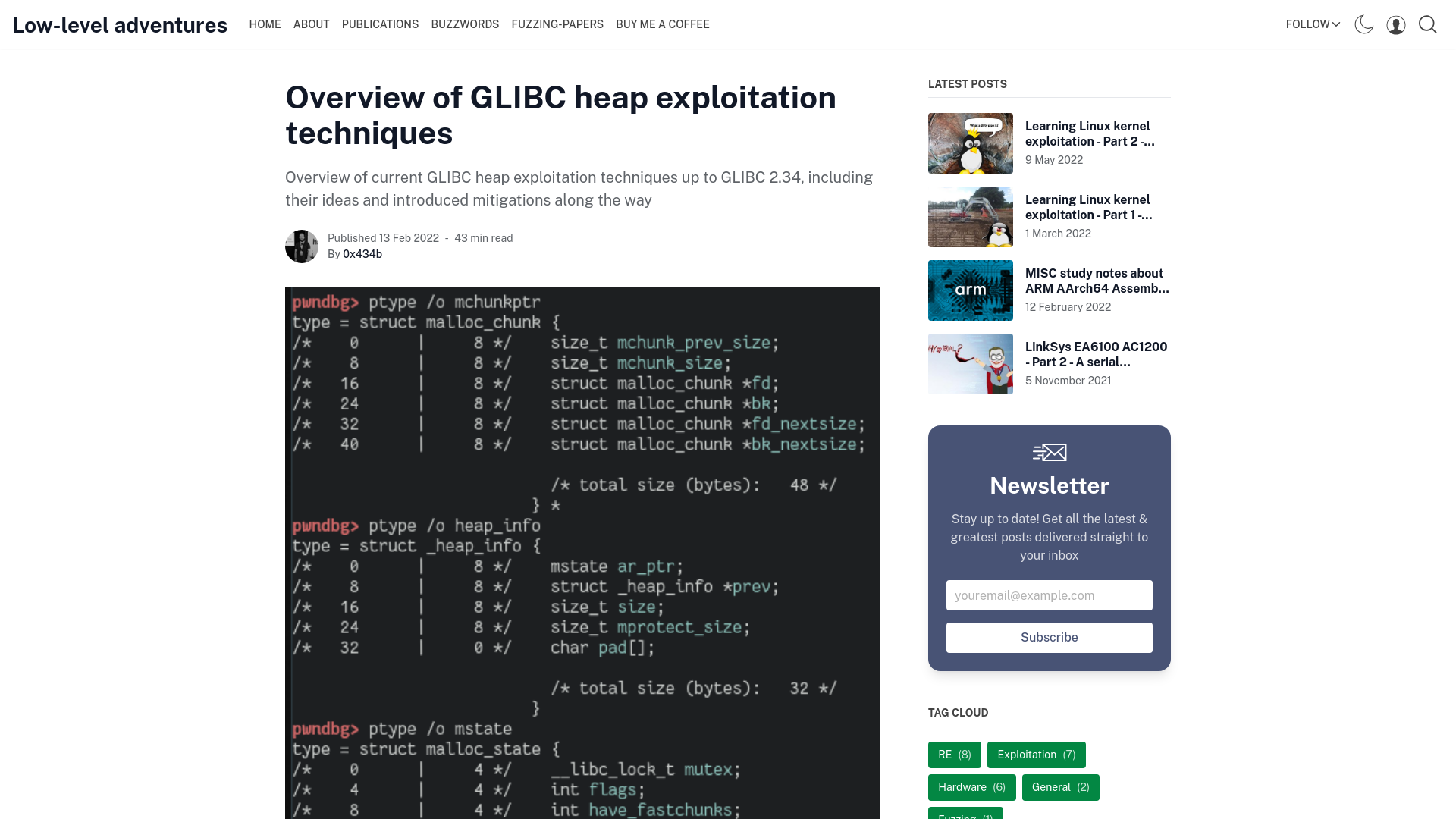
Project Zero: RC4 Is Still Considered Harmful
https://googleprojectzero.blogspot.com/2022/10/rc4-is-still-considered-harmful.html
Data of 400 Million Twitter users up for saleSecurity Affairs
https://securityaffairs.co/wordpress/139993/data-breach/twitter-400-million-users-leak.html
Instituto SANS | Recursos en Español
https://www.sans.org/u/1nUx
CVE-2022-46175: JSON5 Prototype Pollution Vulnerability
https://securityonline.info/cve-2022-46175-json5-prototype-pollution-vulnerability/
総務省|報道資料|「サイバー攻撃被害に係る情報の共有・公表ガイダンス(案)」に対する意見募集
https://www.soumu.go.jp/menu_news/s-news/01cyber01_02000001_00154.html
弊社が運営する「つの食品webショップ」への不正アクセスによる 個人情報漏えいに関するお詫びとお知ら | つの食品 通販|米ぬかで暮らしを豊かに 築野食品工業
https://www.tsunorice.com/contents/20221226_information.php
脆弱性に附番されるCVE番号を管理する「cve.mitre.org」がリニューアルへ - やじうまの杜 - 窓の杜
https://forest.watch.impress.co.jp/docs/serial/yajiuma/1466887.html
Zyxel authentication bypass patch analysis (CVE-2022-0342) - hn security
https://security.humanativaspa.it/zyxel-authentication-bypass-patch-analysis-cve-2022-0342/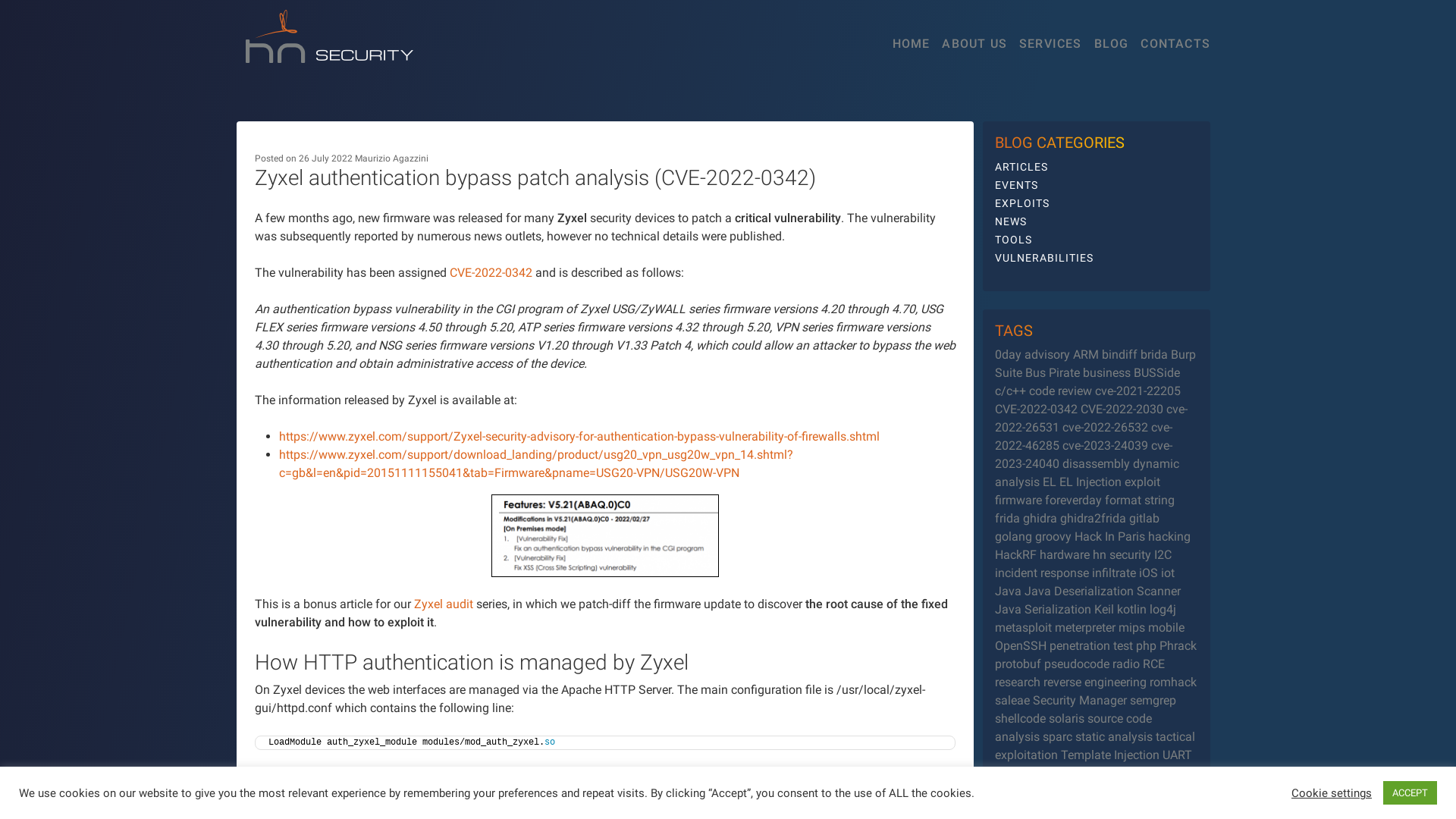
SANS Secure Mexico 2023 | Capacitación en Ciberseguridad
https://www.sans.org/u/1odu
Divide And Bypass: A new Simple Way to Bypass AMSI | x4sh3s
https://x4sh3s.github.io/posts/Divide-and-bypass-amsi/
GitHub - novitae/sterraxcyl: Instagram OSINT tool to export and analyse followers | following with their details
https://github.com/novitae/sterraxcyl
SensePost | Abusing windows’ tokens to compromise active directory without touching lsass
https://sensepost.com/blog/2022/abusing-windows-tokens-to-compromise-active-directory-without-touching-lsass/