10 Python Libraries for Malware Analysis and Reverse Engineering | by Thomas Roccia | SecurityBreak
https://blog.securitybreak.io/10-python-libraries-for-malware-analysis-and-reverse-engineering-622751e6ebd0
EXCLUSIVE: U.S. Government Ordered Travel Companies To Spy On Russian Hacker For Years And Report His Whereabouts Every Week
https://www.forbes.com/sites/thomasbrewster/2022/06/08/exclusive-us-government-ordered-travel-companies-to-spy-on-russian-hacker-for-years-and-report-his-whereabouts-every-week/
Follina — a Microsoft Office code execution vulnerability | by Kevin Beaumont | DoublePulsar
https://doublepulsar.com/follina-a-microsoft-office-code-execution-vulnerability-1a47fce5629e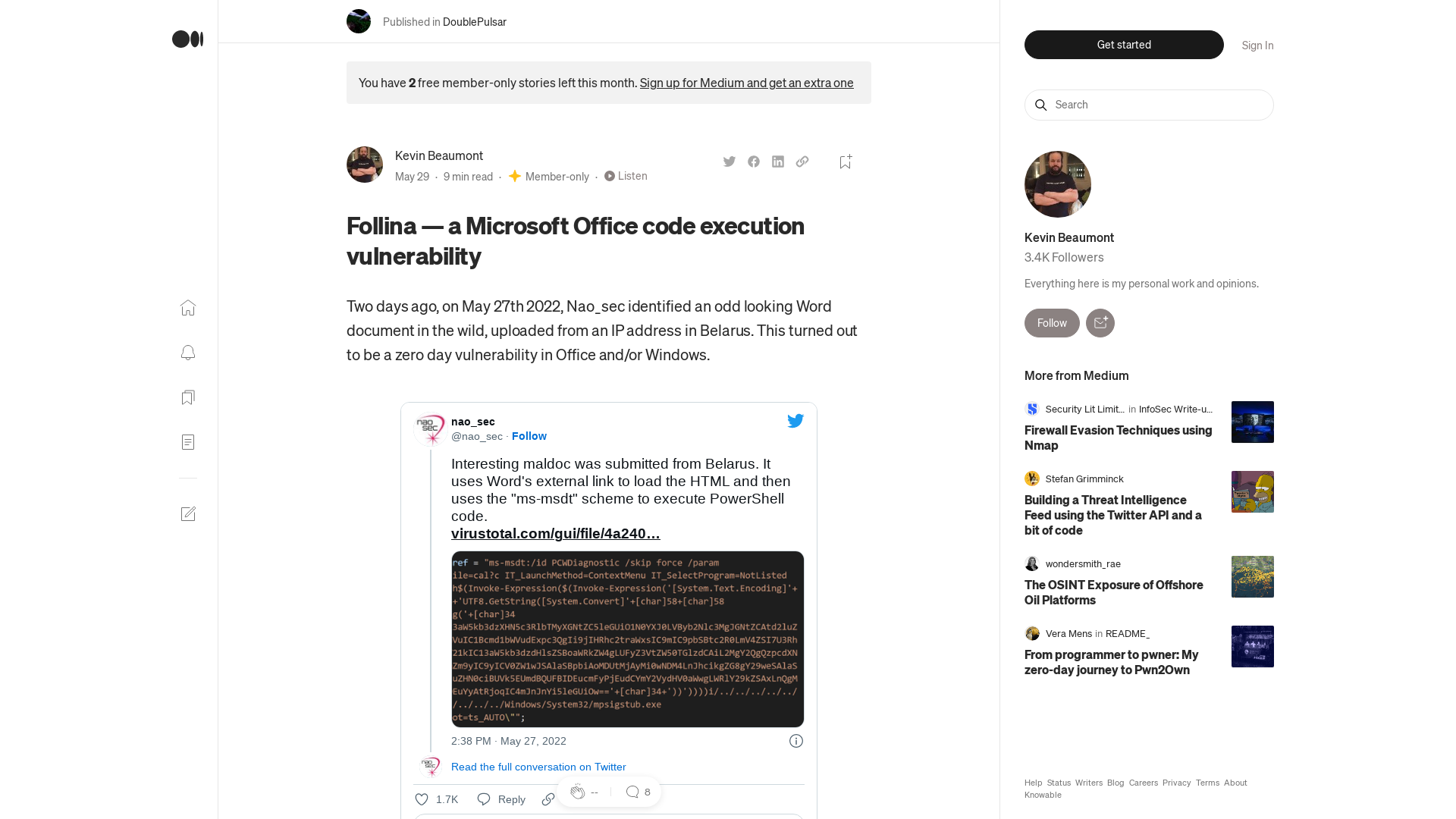
People’s Republic of China State-Sponsored Cyber Actors Exploit Network Providers and Devices | CISA
https://www.cisa.gov/uscert/ncas/alerts/aa22-158a
random/follinaqbot.csv at main · aanubhav-ioc/random · GitHub
https://github.com/aanubhav-ioc/random/blob/main/follinaqbot.csv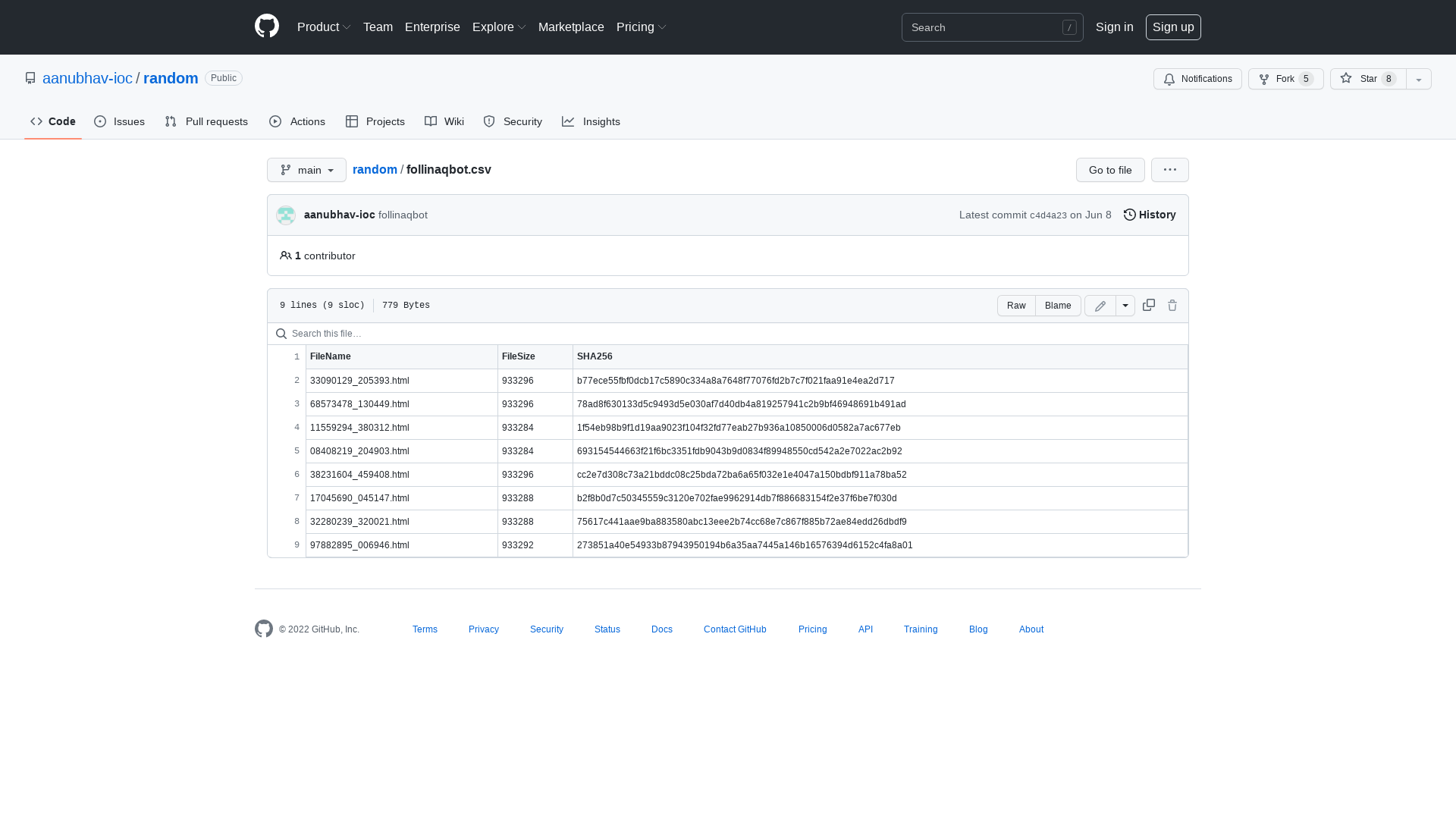
GitHub - synacktiv/ica2tcp: A SOCKS proxy for Citrix.
https://github.com/synacktiv/ica2tcp
VirusTotal - File - 7641c3d8e2a5159333fb99a851ac8c400bb7fd62fc61c58e6016747045cab0c1
https://virustotal.com/gui/file/7641c3d8e2a5159333fb99a851ac8c400bb7fd62fc61c58e6016747045cab0c1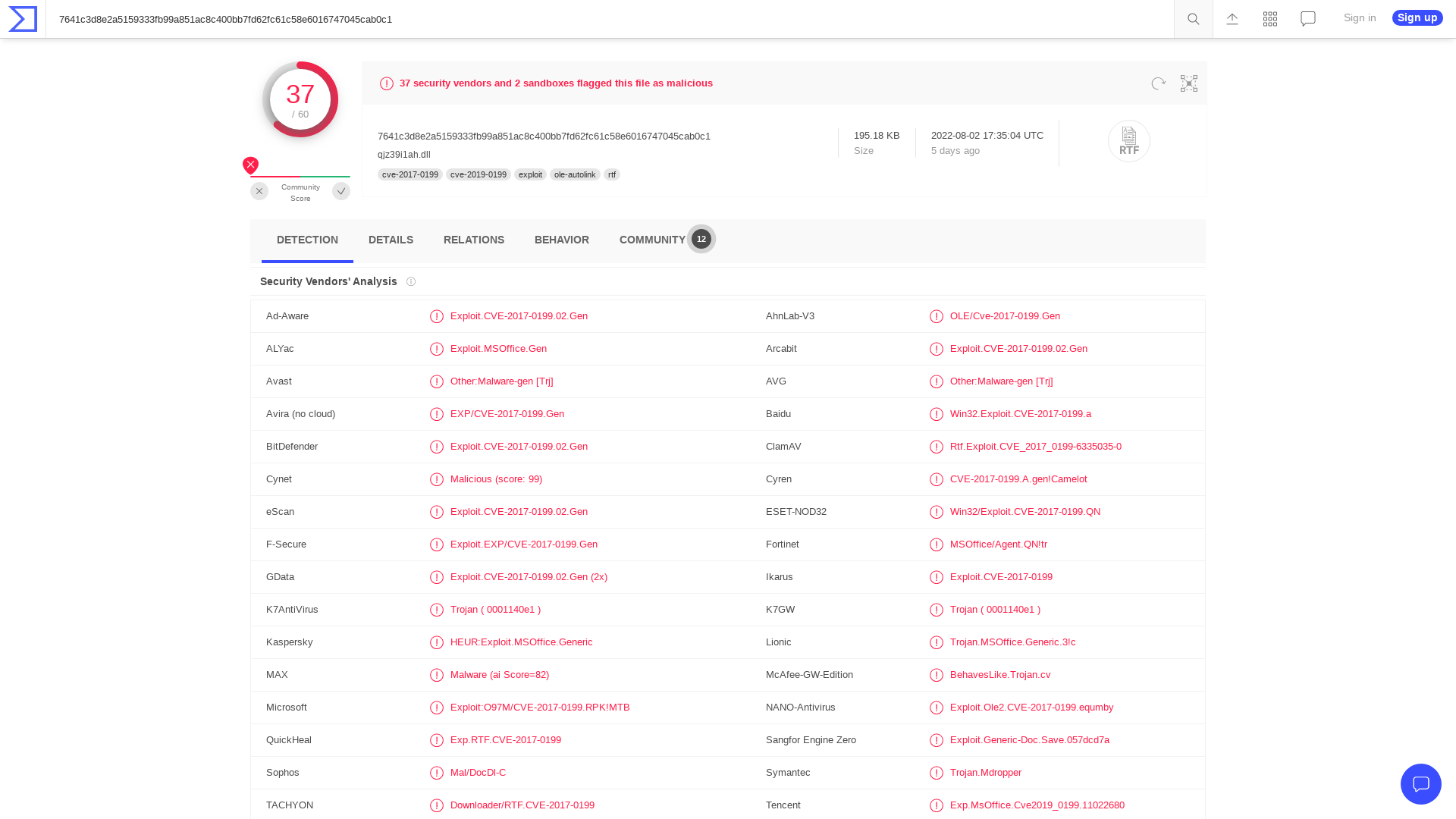
Hatching Triage | Malware sandboxing report by Hatching Triage
https://tria.ge/220607-232zjscdgr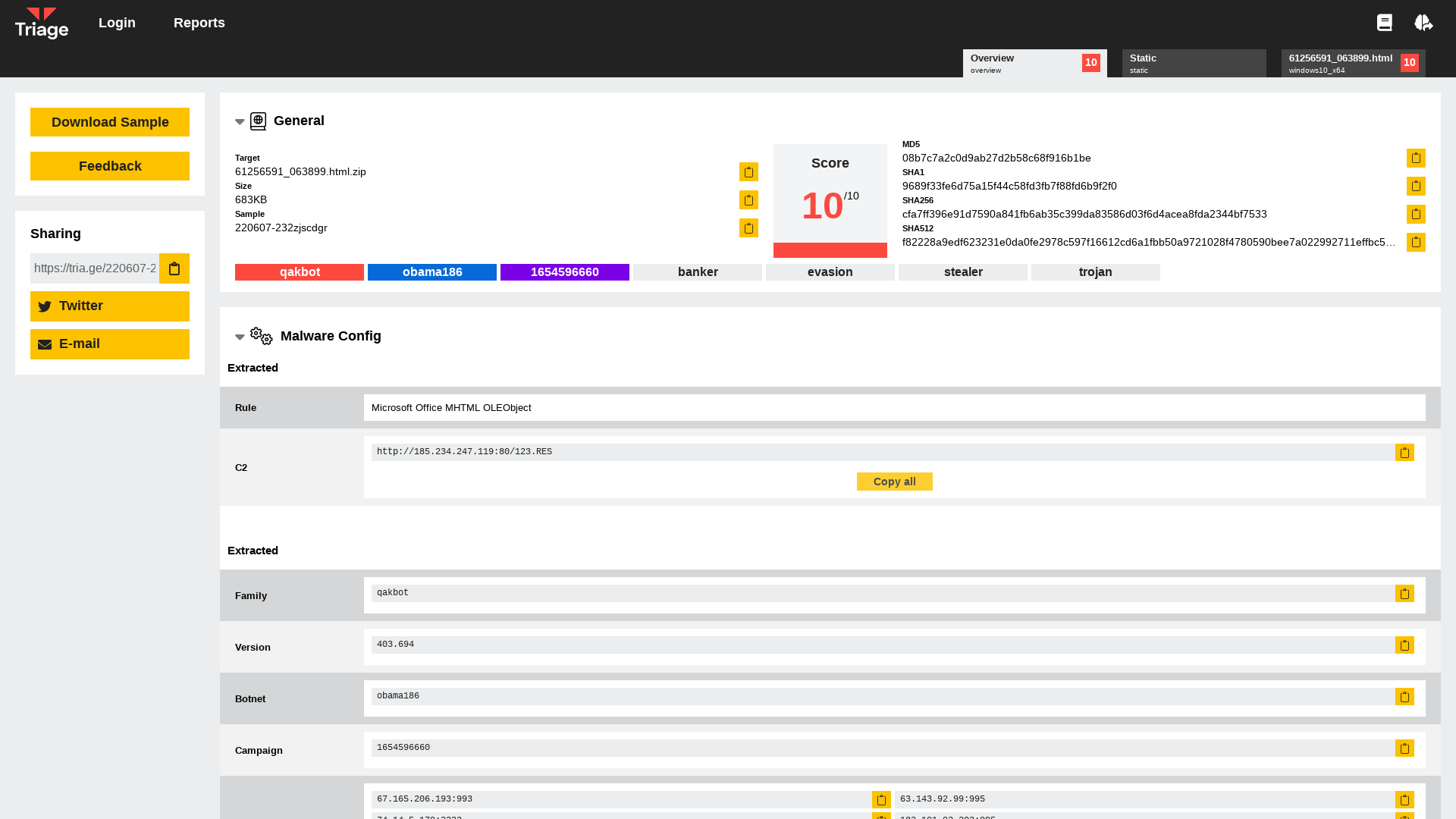
Managed Identity Attack Paths, Part 3: Function Apps | by Andy Robbins | Jun, 2022 | Posts By SpecterOps Team Members
https://posts.specterops.io/300065251cbe
Lateral Movement Survey
https://forms.gle/P8hGmfZF9QpDUu948
Pastebin.com - Not Found (#404)
https://pastebin.com/raw/FjmZMPRL
Poisoned CCleaner search results spread information-stealing malware
https://www.bleepingcomputer.com/news/security/pirated-ccleaner-search-results-spread-information-stealing-malware/
VirusTotal - File - 038276cb9c77684c17b7ed8d473874afb7f432d4755e9f3f7b6e1379b93ab55c
https://www.virustotal.com/gui/file/038276cb9c77684c17b7ed8d473874afb7f432d4755e9f3f7b6e1379b93ab55c/detection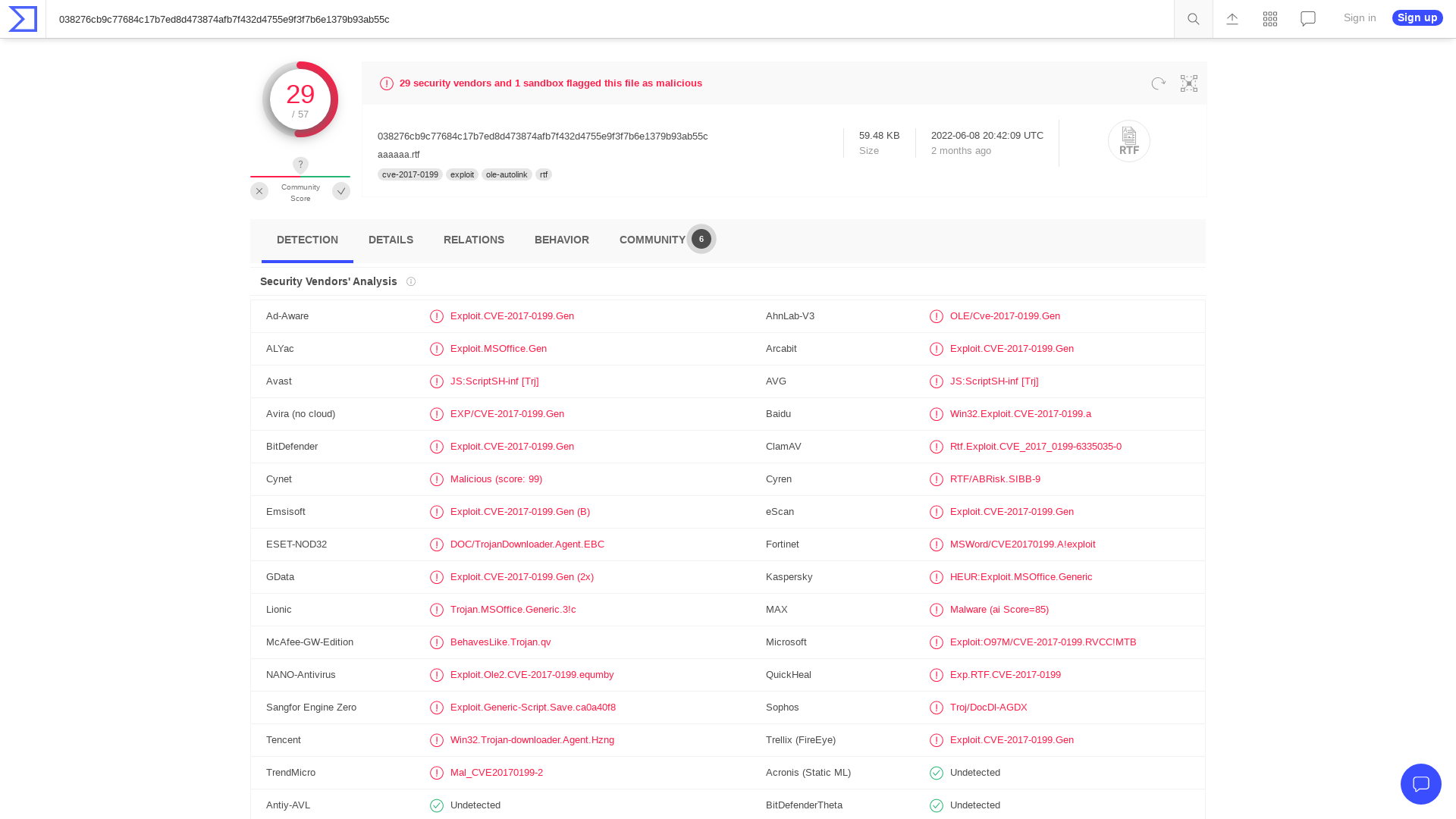
U.S. Agencies Warn About Chinese Hackers Targeting Telecoms and Network Service Providers
https://thehackernews.com/2022/06/us-agencies-warn-about-chinese-hackers.html
BlackCat — In a Shifting Threat Landscape, It Helps to Land on Your Feet: Tech Dive
https://www.advintel.io/post/blackcat-in-a-shifting-threat-landscape-it-helps-to-land-on-your-feet-tech-dive
Jennifer Nielsen, Esq. on Twitter: "If you are in family litigation, TURN OFF iMESSAGES. @Apple's new iOS update will allow people to change or delete messages up to 15 minutes after they send it, which is a TERRIBLE thing if you are relying on text message evidence to protect yourself or your kids in court. https://t.co/Scsr3vw2Kg" / Twitter
https://twitter.com/FamilyLawOhio/status/1534354269389864963
NSA Cyber on Twitter: "PRC sponsored cyber actors have exploited telecommunications and other network service providers to expand targeting worldwide. Our latest report with @CISAgov and @FBI outlines continued general trends and specific TTPs used in this targeting. https://t.co/jU2XcYP2x2 https://t.co/r4JNC1XXaH" / Twitter
https://twitter.com/NSACyber/status/1534295755028156418
S3cur3Th1sSh1t on Twitter: "The last two weekends plus some evenings I spend my time writing a Nim Packer/Loader, which will be provided to Sponsors only via private repo. It's capable of packing C# Assemblies, Shellcode or PE-Files. (1/3) https://t.co/5PtfM8n17V https://t.co/ZdQMFEzPLx https://t.co/p9OWDOM16B" / Twitter
https://twitter.com/ShitSecure/status/1482428360500383755
Operation(काराकोरम) Tejas:蜷居在昆仑山脉的残喘枯象
https://mp-weixin-qq-com.translate.goog/s/8j_rHA7gdMxY1_X8alj8Zg?_x_tr_sl=zh-CN&_x_tr_tl=en&_x_tr_hl=en

http://go.usa.gov/xJkz5
http://go.usa.gov/xJkz5
Operation(काराकोरम) Tejas:蜷居在昆仑山脉的残喘枯象
https://mp.weixin.qq.com/s/8j_rHA7gdMxY1_X8alj8Zg
C2IntelFeedsBot on Twitter: "Cobalt Strike Server Found C2: HTTPS @ 158[.]255[.]2[.]245:443 C2 Server: 158[.]255[.]2[.]245,/__utm[.]gif Country: Russia ASN: HOSTKEY-RU-AS #C2 #cobaltstrike" / Twitter
https://twitter.com/drb_ra/status/1529184738958876674![C2IntelFeedsBot on Twitter: "Cobalt Strike Server Found C2: HTTPS @ 158[.]255[.]2[.]245:443 C2 Server: 158[.]255[.]2[.]245,/__utm[.]gif Country: Russia ASN: HOSTKEY-RU-AS #C2 #cobaltstrike" / Twitter](/image/screenshot/39622107a1d49499e698b460fa6b622b.png)
Emotet malware now steals credit cards from Google Chrome users
https://www.bleepingcomputer.com/news/security/emotet-malware-now-steals-credit-cards-from-google-chrome-users/
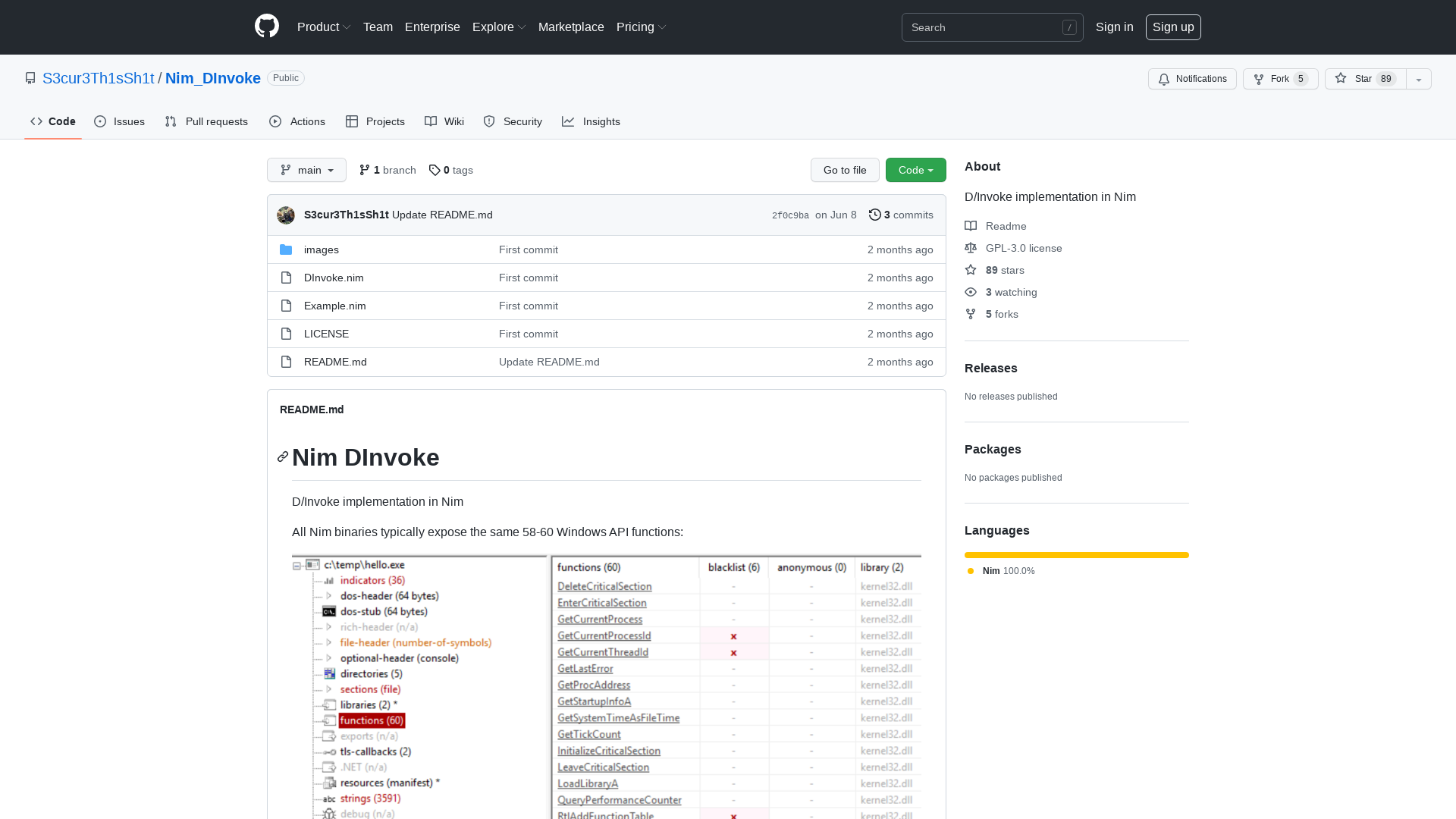
GitHub - S3cur3Th1sSh1t/Nim_DInvoke: D/Invoke implementation in Nim
https://github.com/S3cur3Th1sSh1t/Nim_DInvoke