The Surreal Case of a C.I.A. Hacker’s Revenge | The New Yorker
https://www.newyorker.com/magazine/2022/06/13/the-surreal-case-of-a-cia-hackers-revenge
SVCReady: A New Loader Gets Ready | HP Wolf Security
https://threatresearch.ext.hp.com/svcready-a-new-loader-reveals-itself/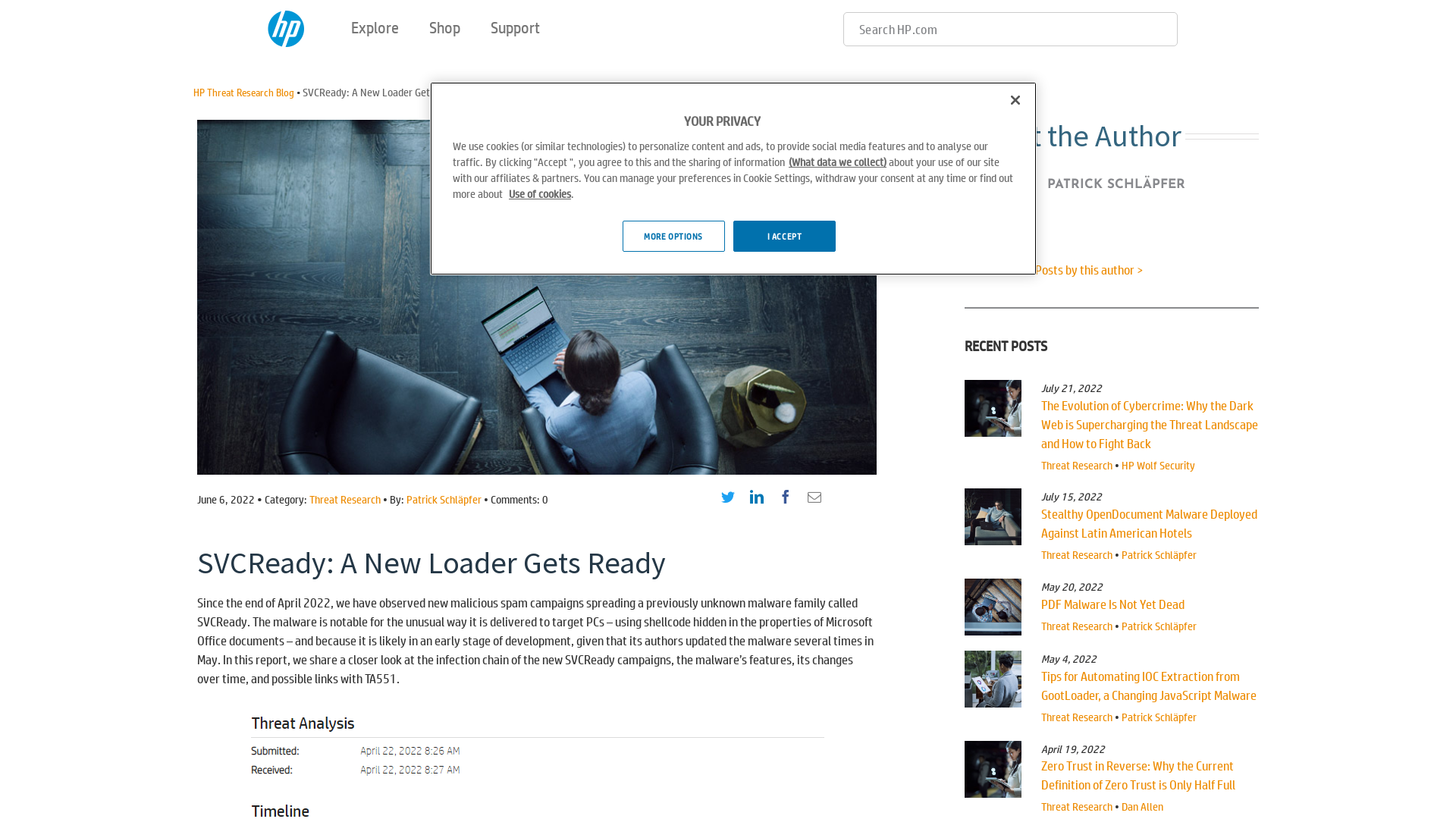
Hatching Triage | Malware sandboxing report by Hatching Triage
https://tria.ge/220607-q7bglsbcan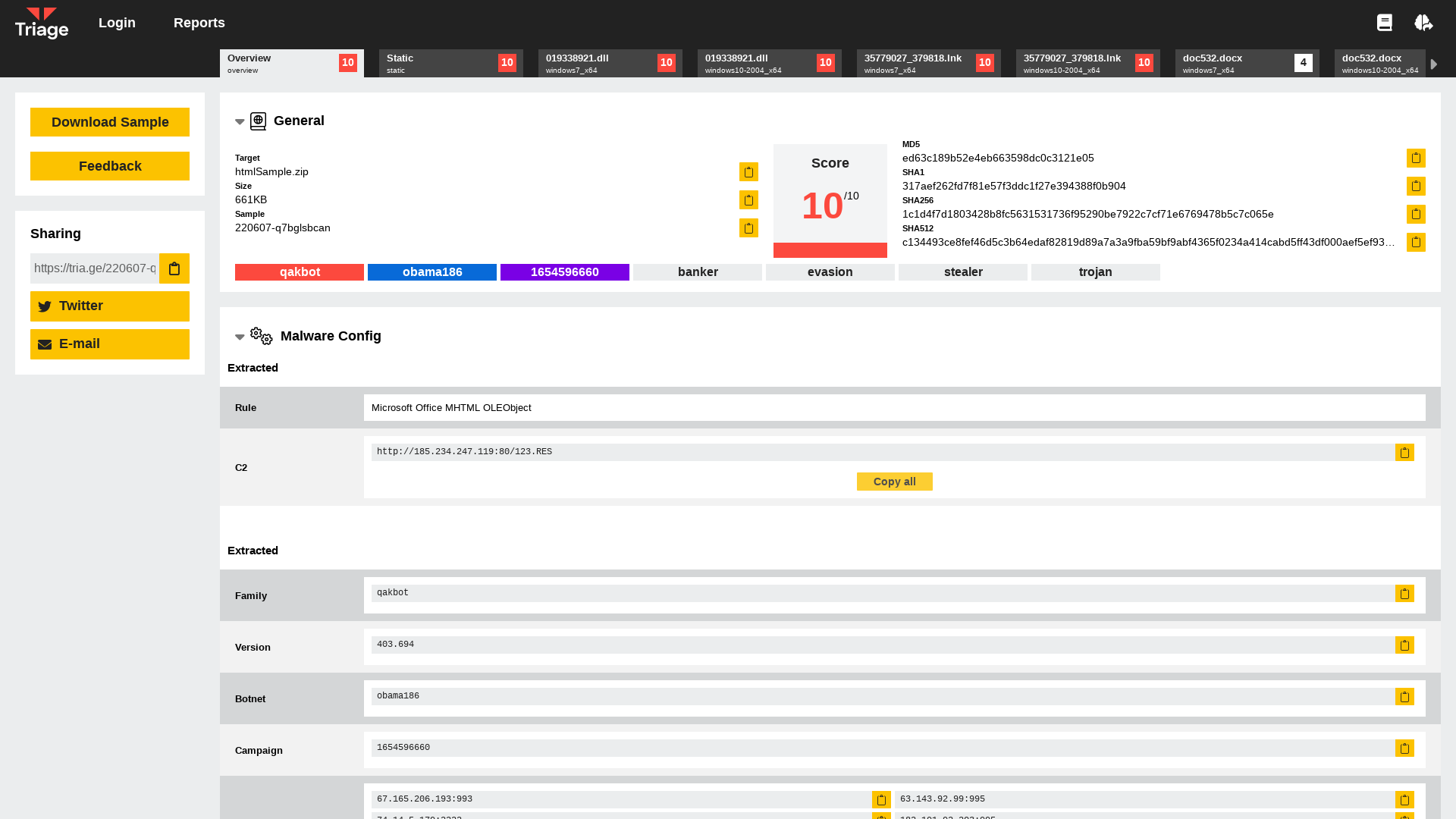
Lily Hay Newman on Twitter: "MongoDB is taking a big swing with a searchable encryption database feature called Queryable Encryption. They worked with cryptographers @senykam and @TarikMoataz to make research practical and it's open source today. AND they claim it's actually fast https://t.co/L0NulgEslb" / Twitter
https://twitter.com/lilyhnewman/status/1534162571531456512
RPC Firewall 2.0 tutorial - YouTube
https://youtu.be/BNzfmYwkioY
Managed Identity Attack Paths, Part 2: Logic Apps | by Andy Robbins | Posts By SpecterOps Team Members
https://posts.specterops.io/52b29354fc54
Mandiant: “No evidence” we were hacked by LockBit ransomware
https://www.bleepingcomputer.com/news/security/mandiant-no-evidence-we-were-hacked-by-lockbit-ransomware/
BlackCat — In a Shifting Threat Landscape, It Helps to Land on Your Feet: Tech Dive
https://www.advintel.io/post/blackcat-in-a-shifting-threat-landscape-it-helps-to-land-on-your-feet-tech-dive
Shining the Light on Black Basta – NCC Group Research
https://research.nccgroup.com/2022/06/06/shining-the-light-on-black-basta/
How to Reverse Engineer and Patch an iOS Application for Beginners: Part I
https://www.inversecos.com/2022/06/how-to-reverse-engineer-and-patch-ios.html
🥝 Benjamin Delpy on Twitter: "@GossiTheDog @Tom_From_The_UK Yes saw it , does not reflect our test .. don’t know why they make this status" / Twitter
https://twitter.com/gentilkiwi/status/1534120224571772933
Mandiant: “No evidence” we were hacked by LockBit ransomware
https://mndt.info/3xpYOwF
VirusTotal - File - 87b8c12b32af3a2f0ffa4fbc4f8bc9c10789e5130ce73d02dfbfe1b6d9463619
https://www.virustotal.com/gui/file/87b8c12b32af3a2f0ffa4fbc4f8bc9c10789e5130ce73d02dfbfe1b6d9463619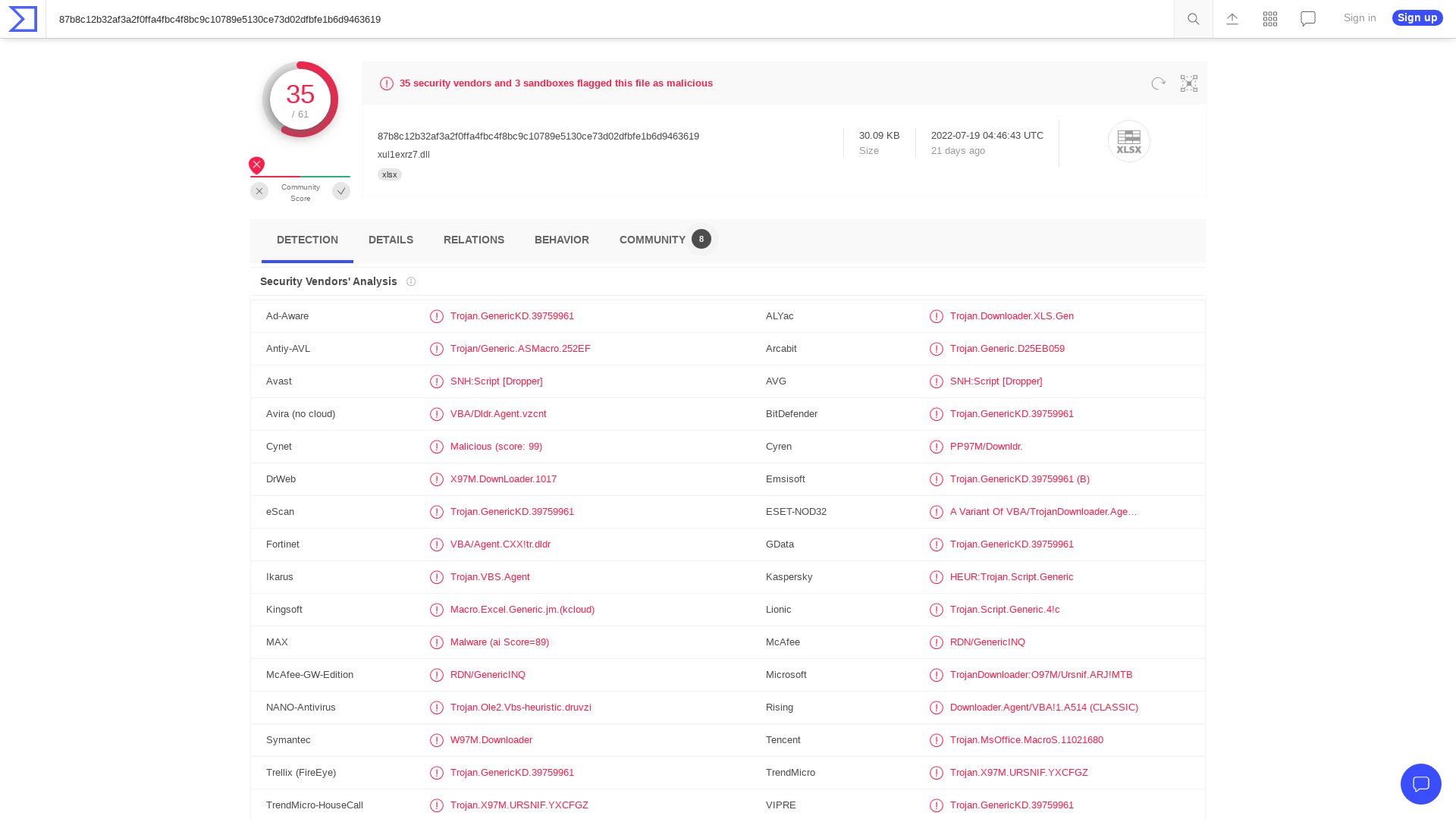
Get the latest GreyNoise research on Confluence CVE-2022-26134
https://www.greynoise.io/blog/observed-in-the-wild-atlassian-confluence-server-cve-2022-26134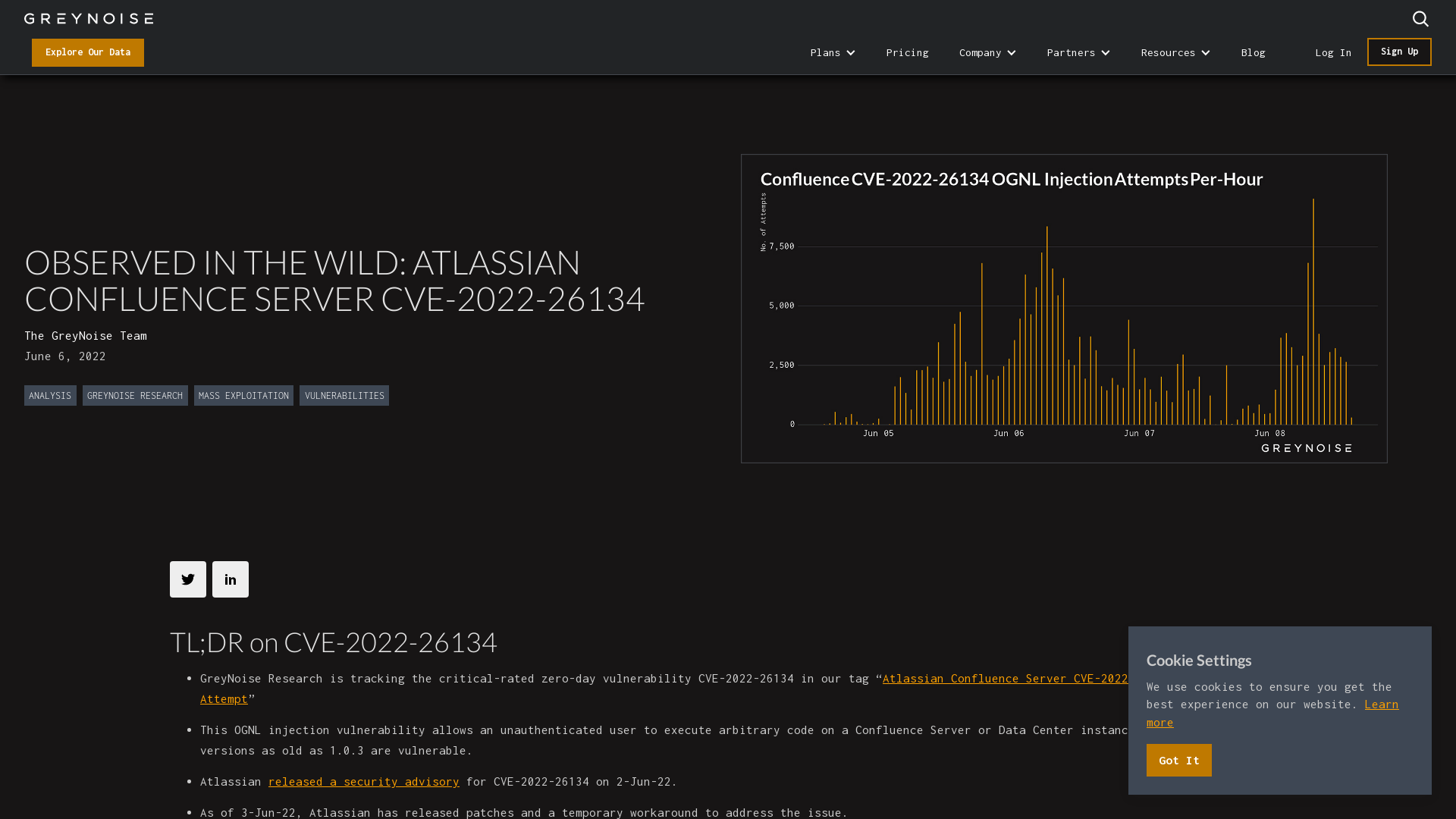
Firmware key extraction by gaining EL3 - The Cave
https://blog.xilokar.info/firmware-key-extraction-by-gaining-el3.html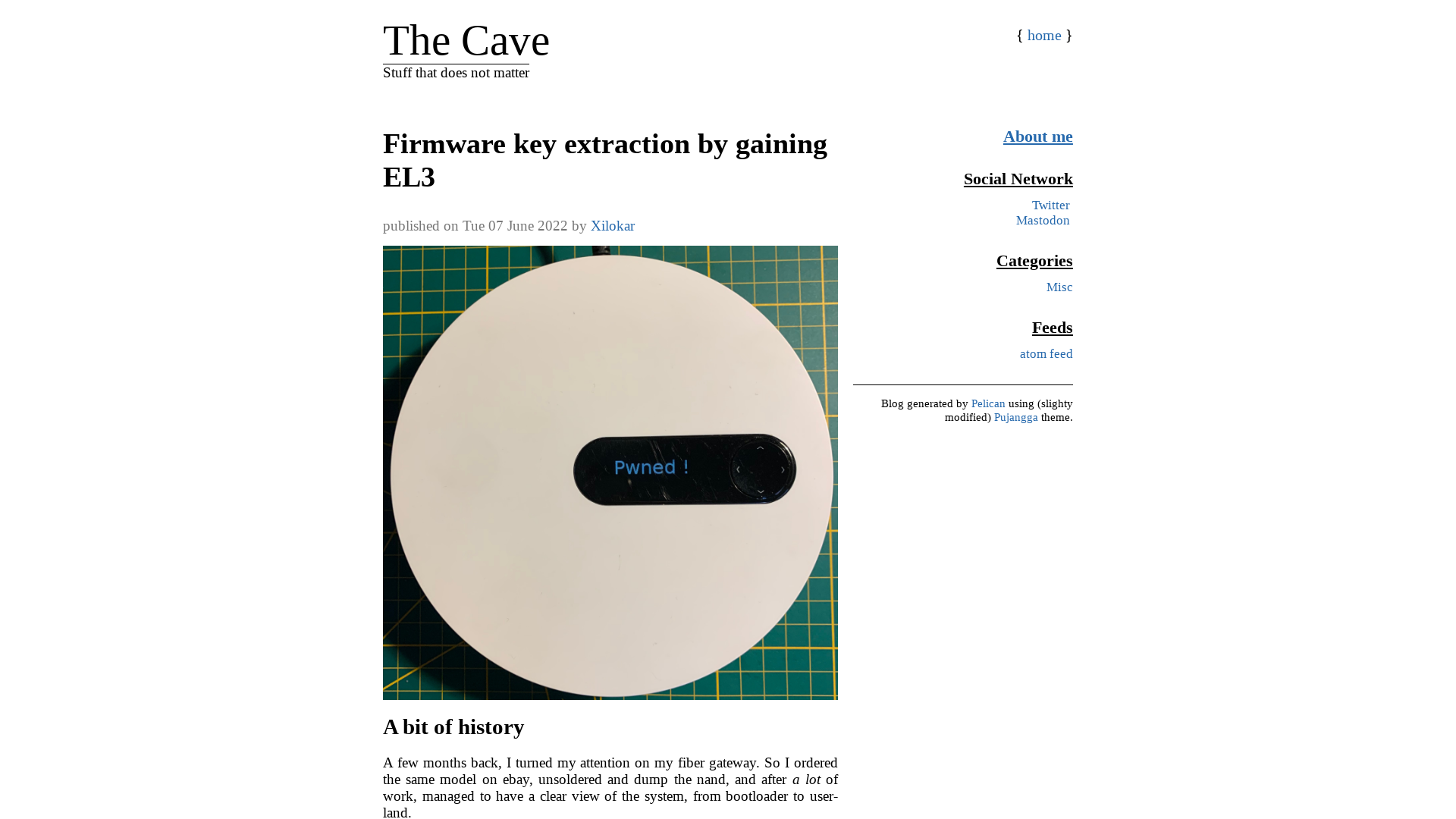
404 Page not found | STAR Labs
https://starlabs.sg/blog/2022/06/trying-to-exploit-a-windows-kernel-arbitrary-read-vulnerability/
Hatching Triage | Behavioral Report
https://tria.ge/220607-j4l1lsgeej/behavioral1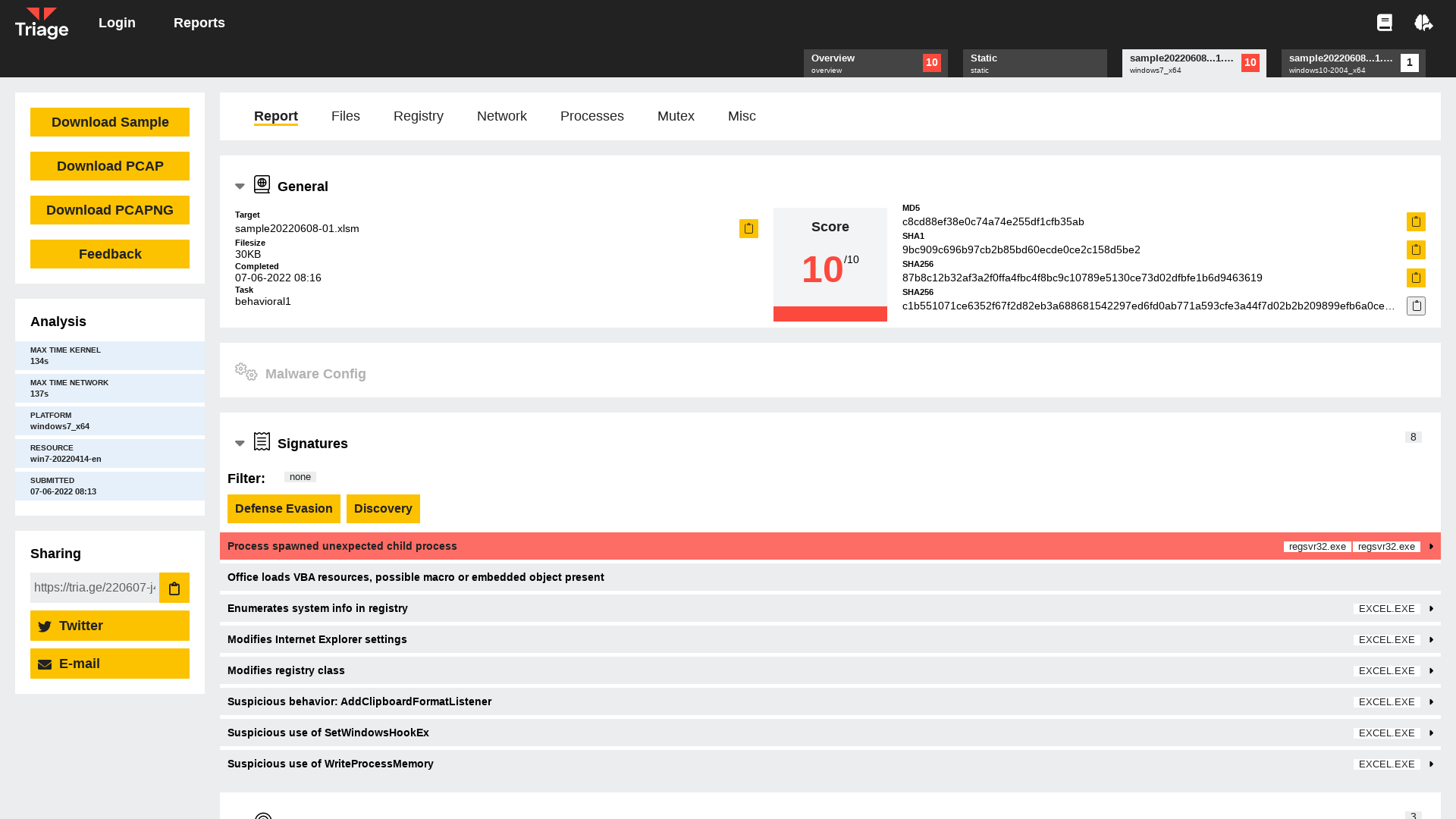
鲨鱼的狂欢 — APT-C-55 Kimsuky组织近期BabyShark组件披露
https://mp-weixin-qq-com.translate.goog/s/ZV8AOTd7YGUgCTTTZtTktQ?_x_tr_sl=zh-CN&_x_tr_tl=en&_x_tr_hl=en
Follina — a Microsoft Office code execution vulnerability | by Kevin Beaumont | DoublePulsar
https://doublepulsar.com/follina-a-microsoft-office-code-execution-vulnerability-1a47fce5629e
鲨鱼的狂欢 — APT-C-55 Kimsuky组织近期BabyShark组件披露
https://mp.weixin.qq.com/s/ZV8AOTd7YGUgCTTTZtTktQ
sample20220608-01.xlsm (MD5: C8CD88EF38E0C74A74E255DF1CFB35AB) - Interactive analysis - ANY.RUN
https://app.any.run/tasks/864ea9be-2525-4074-8e8a-d31176c99c8f/