Guidance for CVE-2022-30190 Microsoft Support Diagnostic Tool Vulnerability – Microsoft Security Response Center
https://msrc-blog.microsoft.com/2022/05/30/guidance-for-cve-2022-30190-microsoft-support-diagnostic-tool-vulnerability/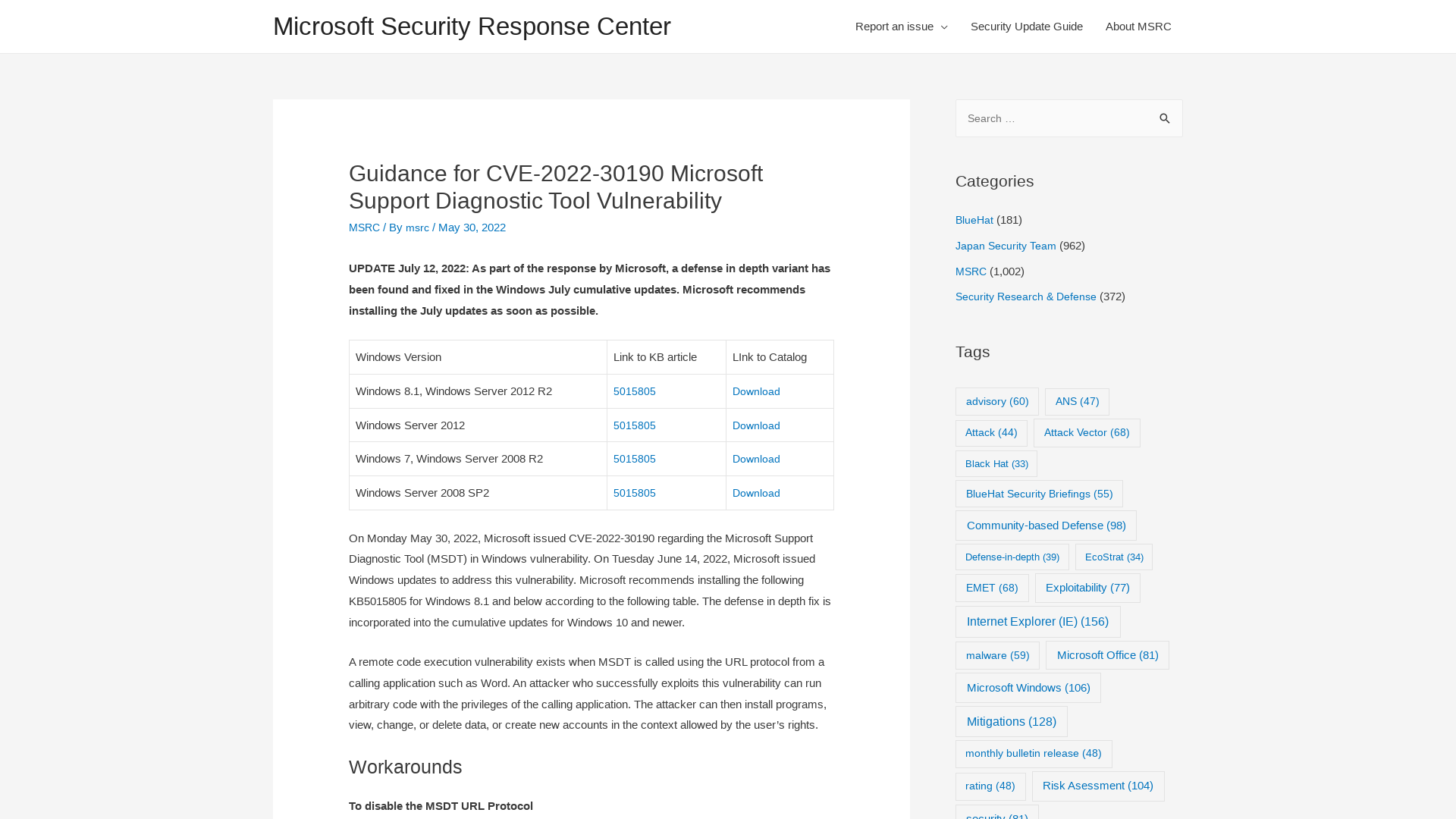
Bacco on Twitter: "Follina P2? Wget the html payload as user = auto execute??? https://t.co/Cb5J5nnCM3" / Twitter
https://twitter.com/0xbacco/status/1531599168363548672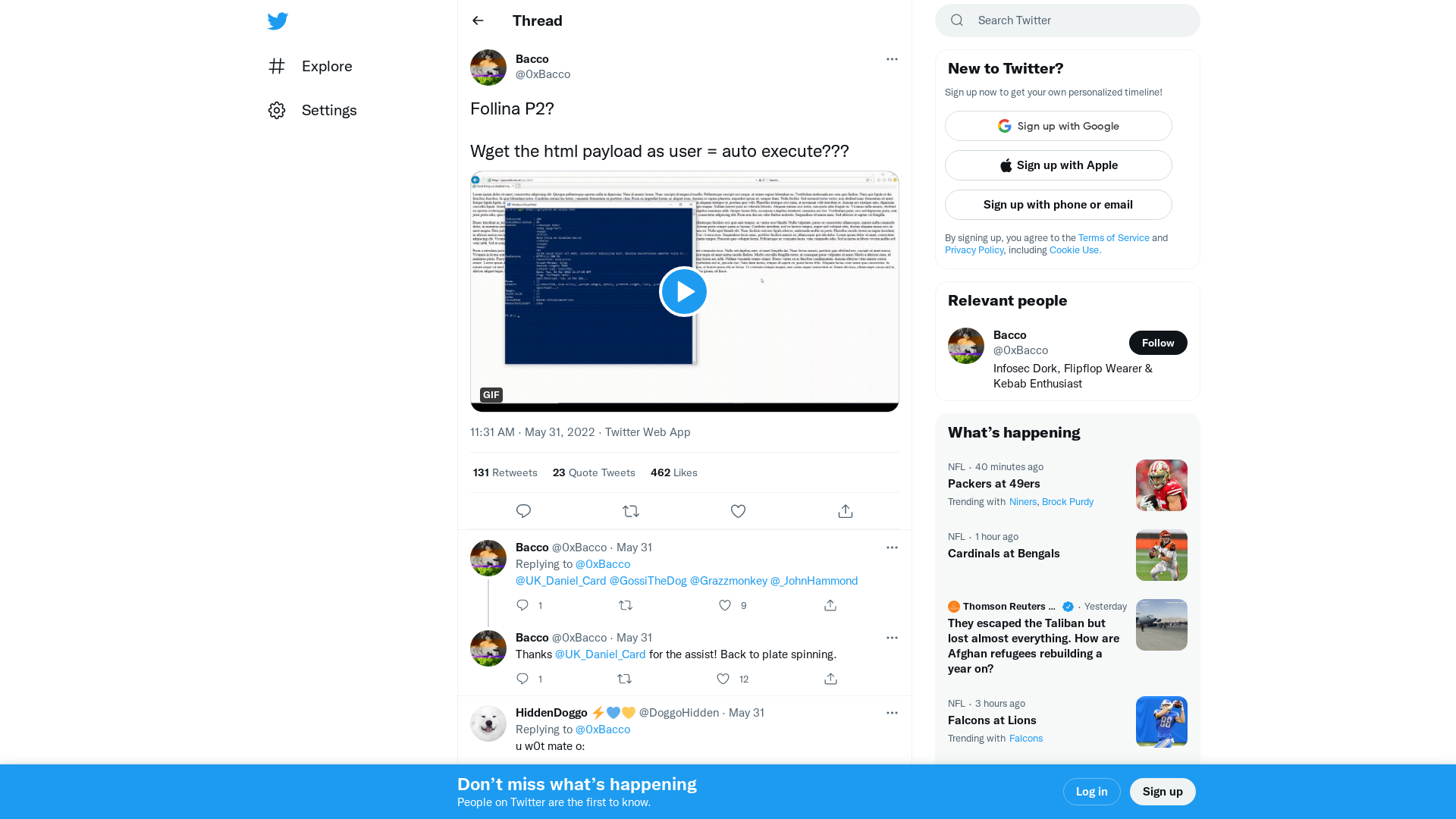
Troubleshooting: Allow users to access and run Troubleshooting Wizards
https://admx.help/?Category=Windows_10_2016&Policy=Microsoft.Policies.ScriptedDiagnostics::ScriptedDiagnosticsExecutionPolicy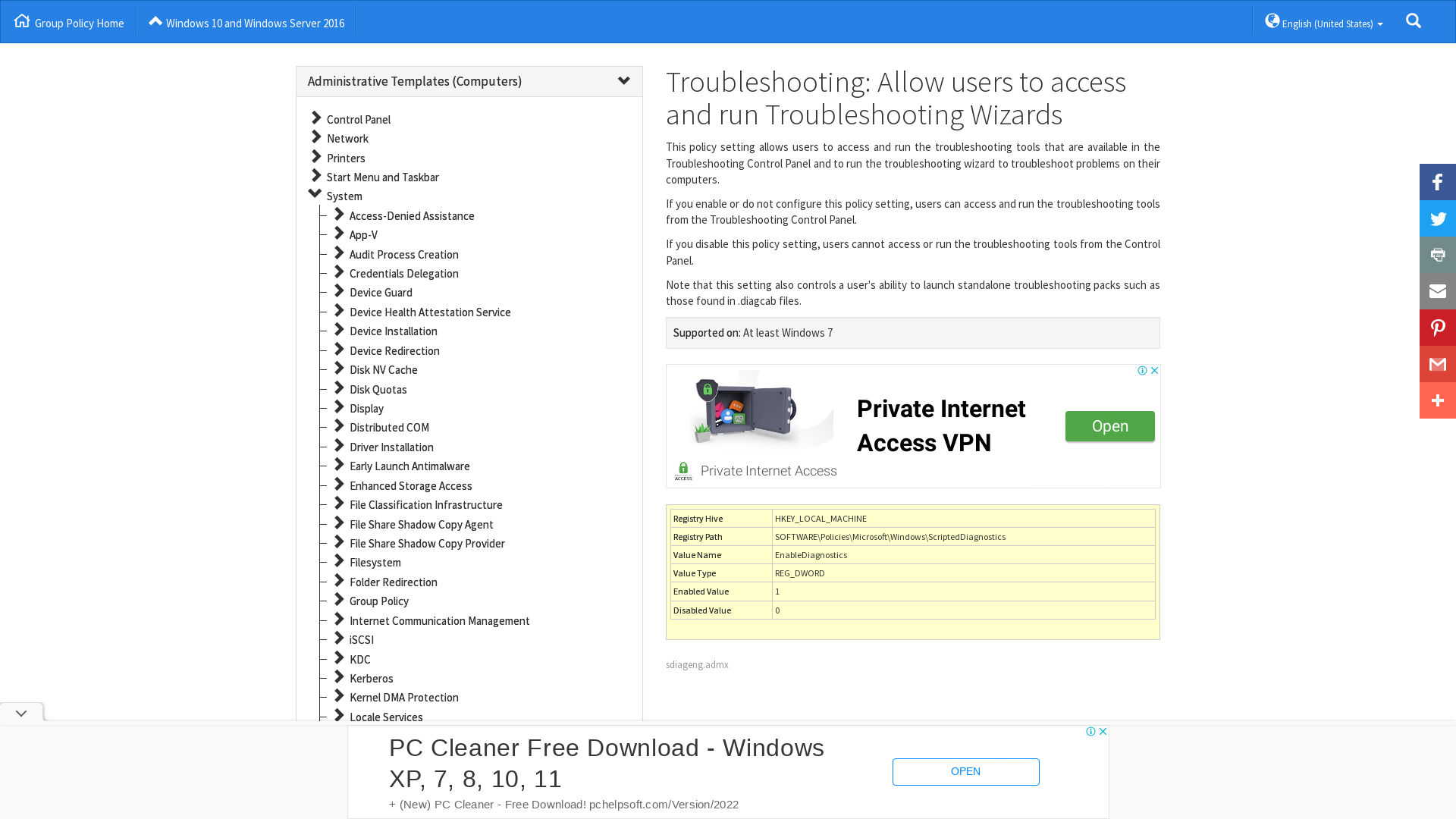
Follina — a Microsoft Office code execution vulnerability | by Kevin Beaumont | DoublePulsar
https://doublepulsar.com/follina-a-microsoft-office-code-execution-vulnerability-1a47fce5629e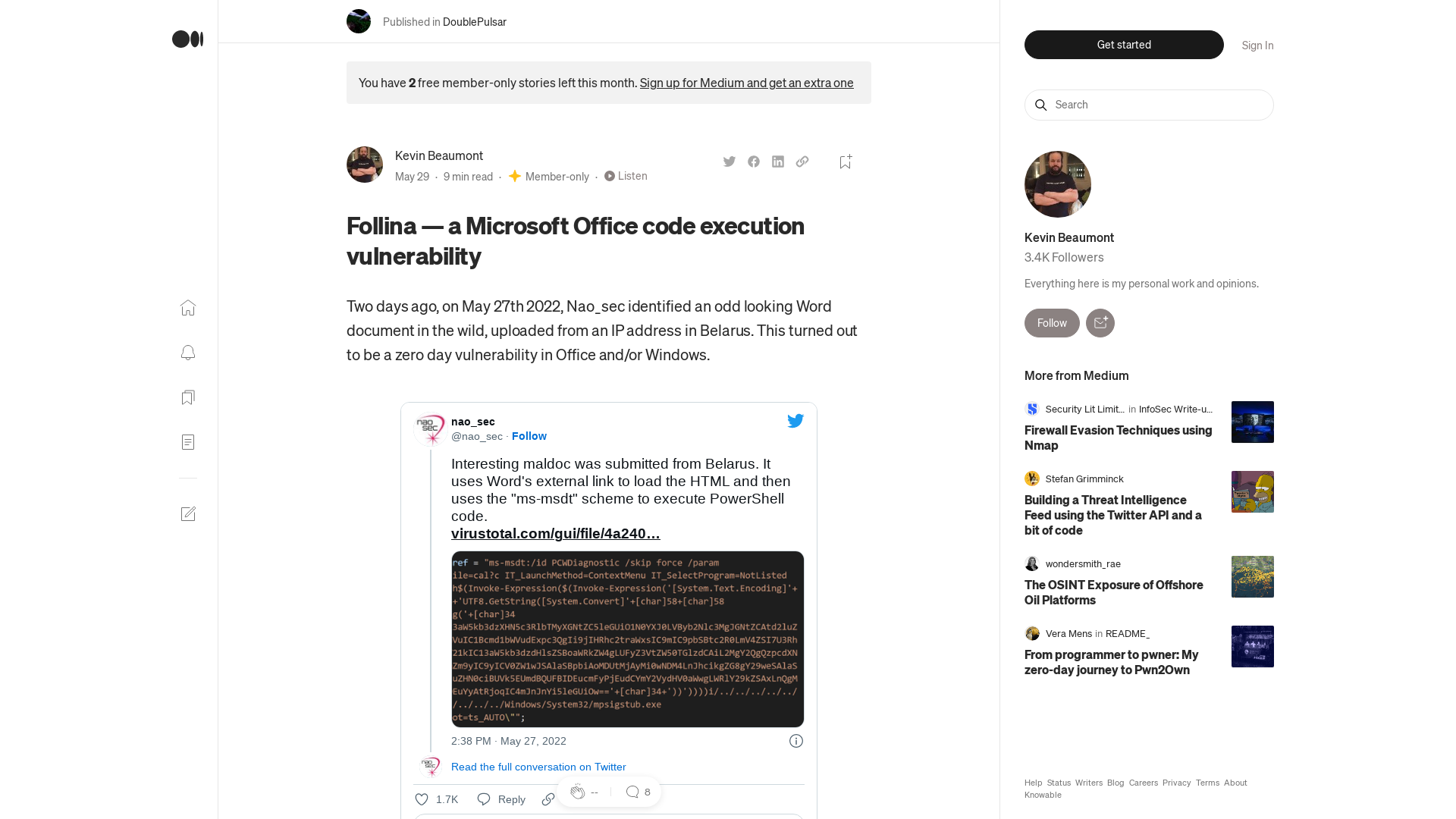
CVE-2022-30190 - Security Update Guide - Microsoft - Microsoft Windows Support Diagnostic Tool (MSDT) Remote Code Execution Vulnerability
https://msrc.microsoft.com/update-guide/en-US/vulnerability/CVE-2022-30190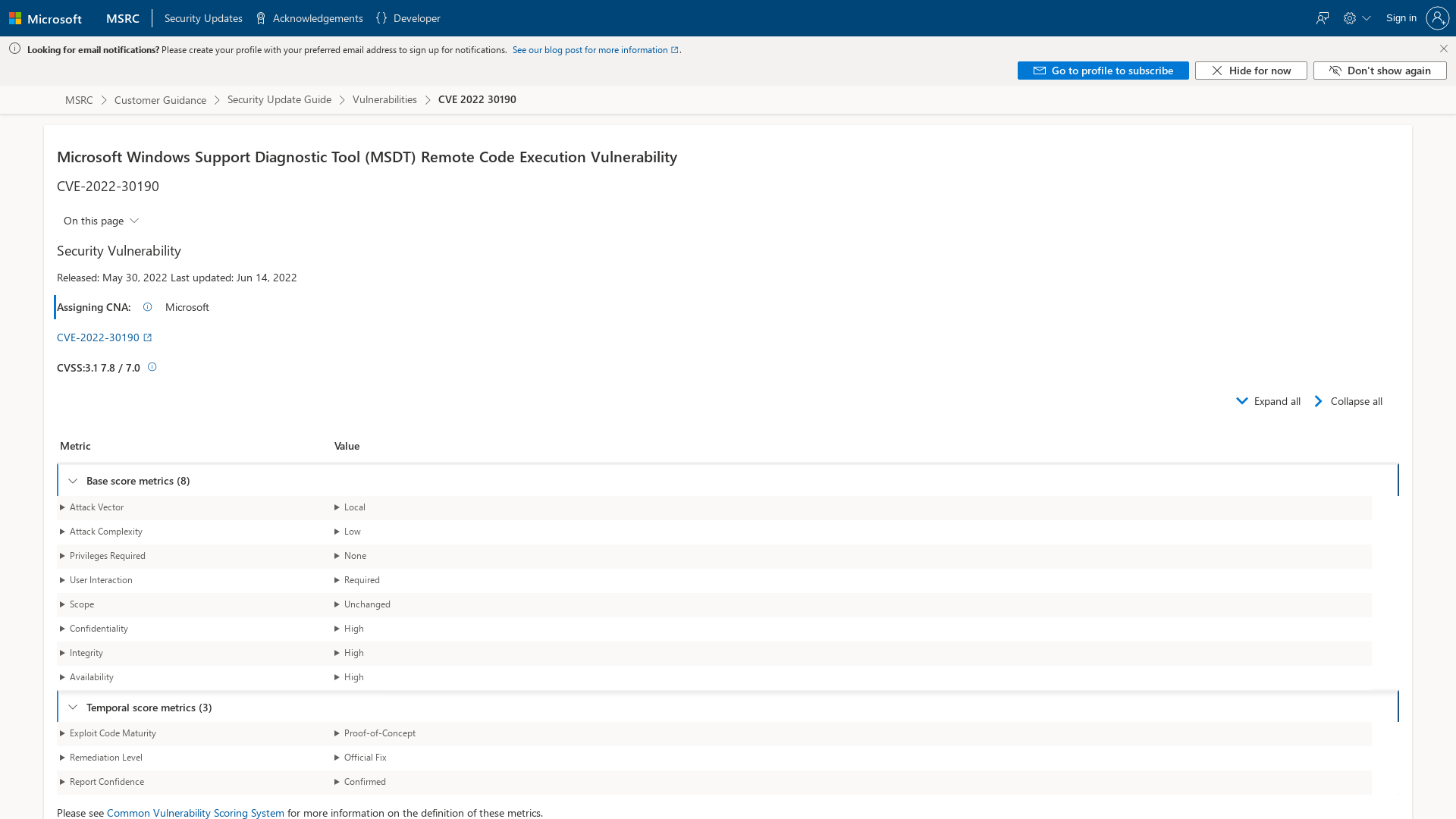
GitHub - HyperDbg/HyperDbg: State-of-the-art native debugging tool
http://github.com/HyperDbg/HyperDbg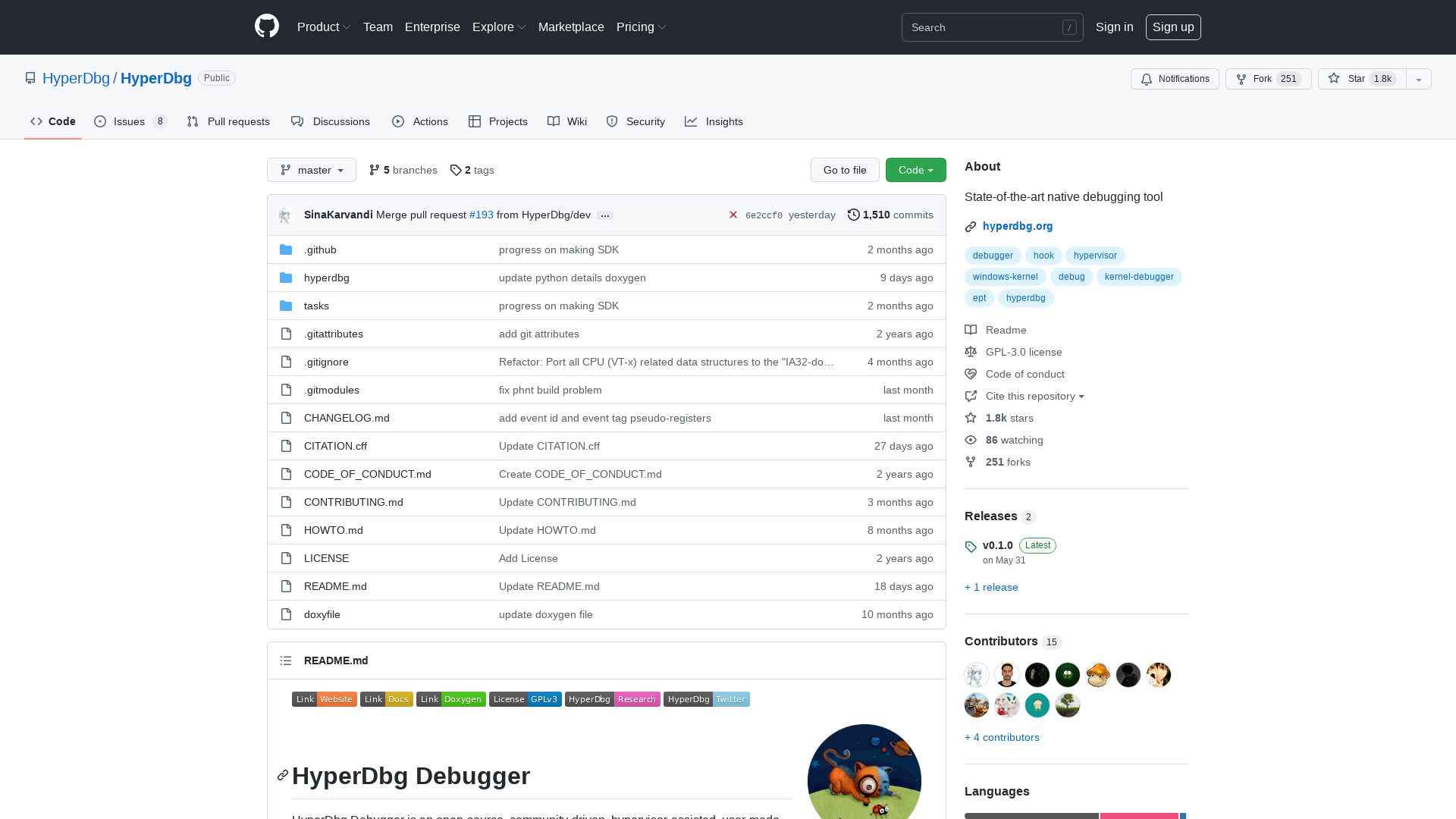
GitHub - klezVirus/CVE-2021-40444: CVE-2021-40444 - Fully Weaponized Microsoft Office Word RCE Exploit
https://github.com/klezVirus/CVE-2021-40444/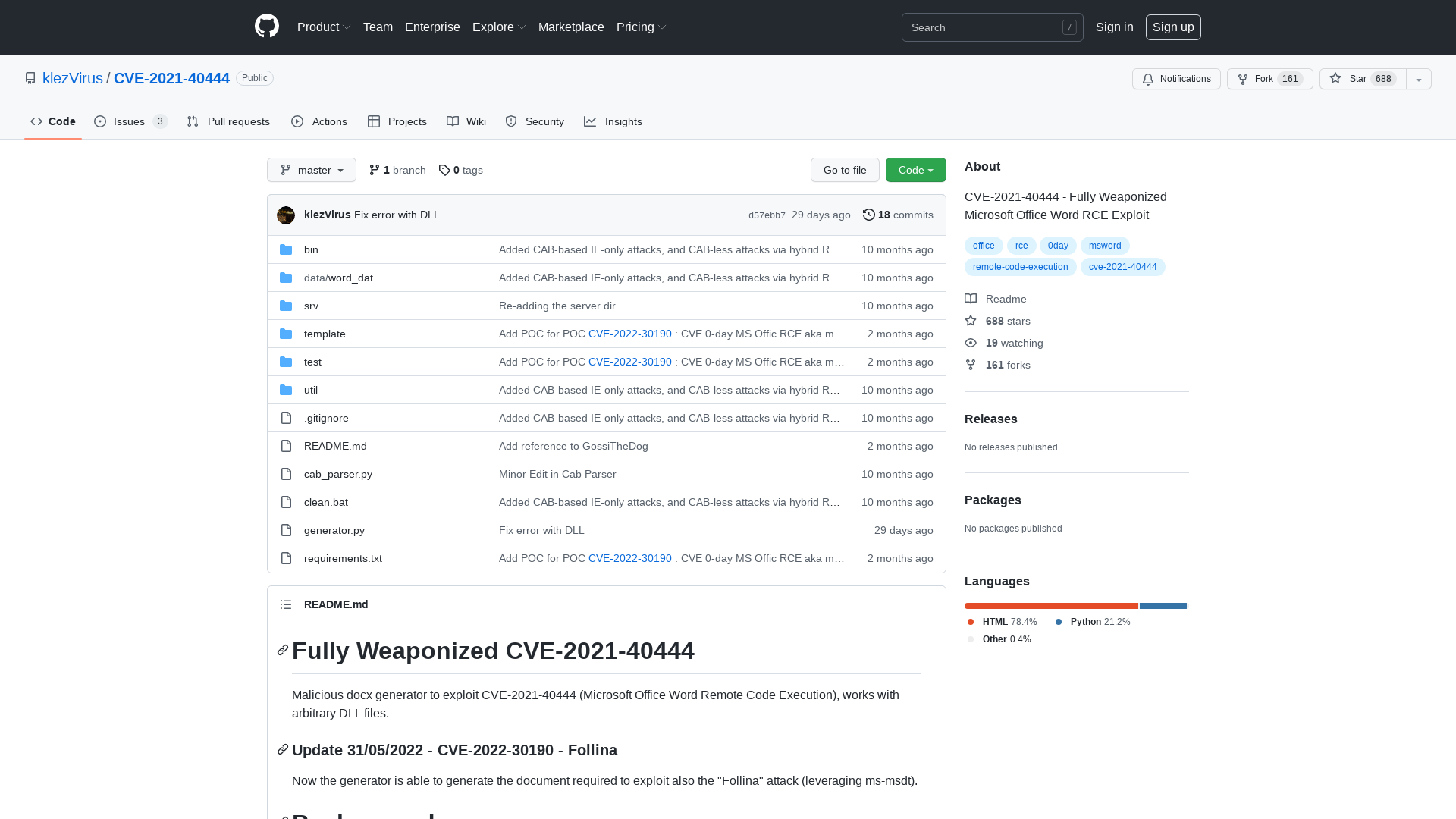
Discord Is the World’s Most Important Financial Messenger, and a Hotbed for Scammers
https://www.vice.com/en/article/n7n848/discord-is-the-worlds-most-important-financial-messenger-and-a-hotbed-for-scammers
thesis-electron.pdf
https://benjamin-altpeter.de/doc/thesis-electron.pdf
Space / Twitter
https://twitter.com/i/spaces/1DXGyDNWEgvKM
Microsoft shares mitigation for Office zero-day exploited in attacks
https://www.bleepingcomputer.com/news/microsoft/microsoft-shares-mitigation-for-office-zero-day-exploited-in-attacks/
Threat Insight on Twitter: "TA413 CN APT spotted ITW exploiting the #Follina #0Day using URLs to deliver Zip Archives which contain Word Documents that use the technique. Campaigns impersonate the "Women Empowerments Desk" of the Central Tibetan Administration and use the domain tibet-gov.web[.]app https://t.co/4FA9Vzoqu4" / Twitter
https://twitter.com/threatinsight/status/1531688214993555457![Threat Insight on Twitter: "TA413 CN APT spotted ITW exploiting the #Follina #0Day using URLs to deliver Zip Archives which contain Word Documents that use the technique. Campaigns impersonate the "Women Empowerments Desk" of the Central Tibetan Administration and use the domain tibet-gov.web[.]app https://t.co/4FA9Vzoqu4" / Twitter](/image/screenshot/c8b8921781a9590010b819ed95b533b3.png)
Gabor Szappanos on Twitter: "Weird how information can't find its' proper way because we don't know or care. The zero-day RCE in Office, that makes waves today, was just a sidenote in this research paper from two years ago (page 29) https://t.co/6vCsZ1UpkQ" / Twitter
https://twitter.com/gaborszappanos/status/1531306621166567430
Kevin Beaumont on Twitter: "Additional Follina issue, if you use wget in Powershell, it blindly executes any code via MSDT as it trusts all MS Protocol URIs. So to clarify, if you wget a webpage you don’t control and the webpage adds Follina exploit string, your server the runs the code." / Twitter
https://twitter.com/GossiTheDog/status/1531608245009367040
The Underground Company That Hacks iPhones for Ordinary Consumers
https://www.vice.com/en/article/jgmygb/checkm8-info-remove-icloud-activation-lock
MalwareBazaar | SHA256 344b6a7c3888aed4239480b4b79381bdf995e0ab8103f982912d1b769d2a8ec2 (IcedID)
https://bazaar.abuse.ch/sample/344b6a7c3888aed4239480b4b79381bdf995e0ab8103f982912d1b769d2a8ec2/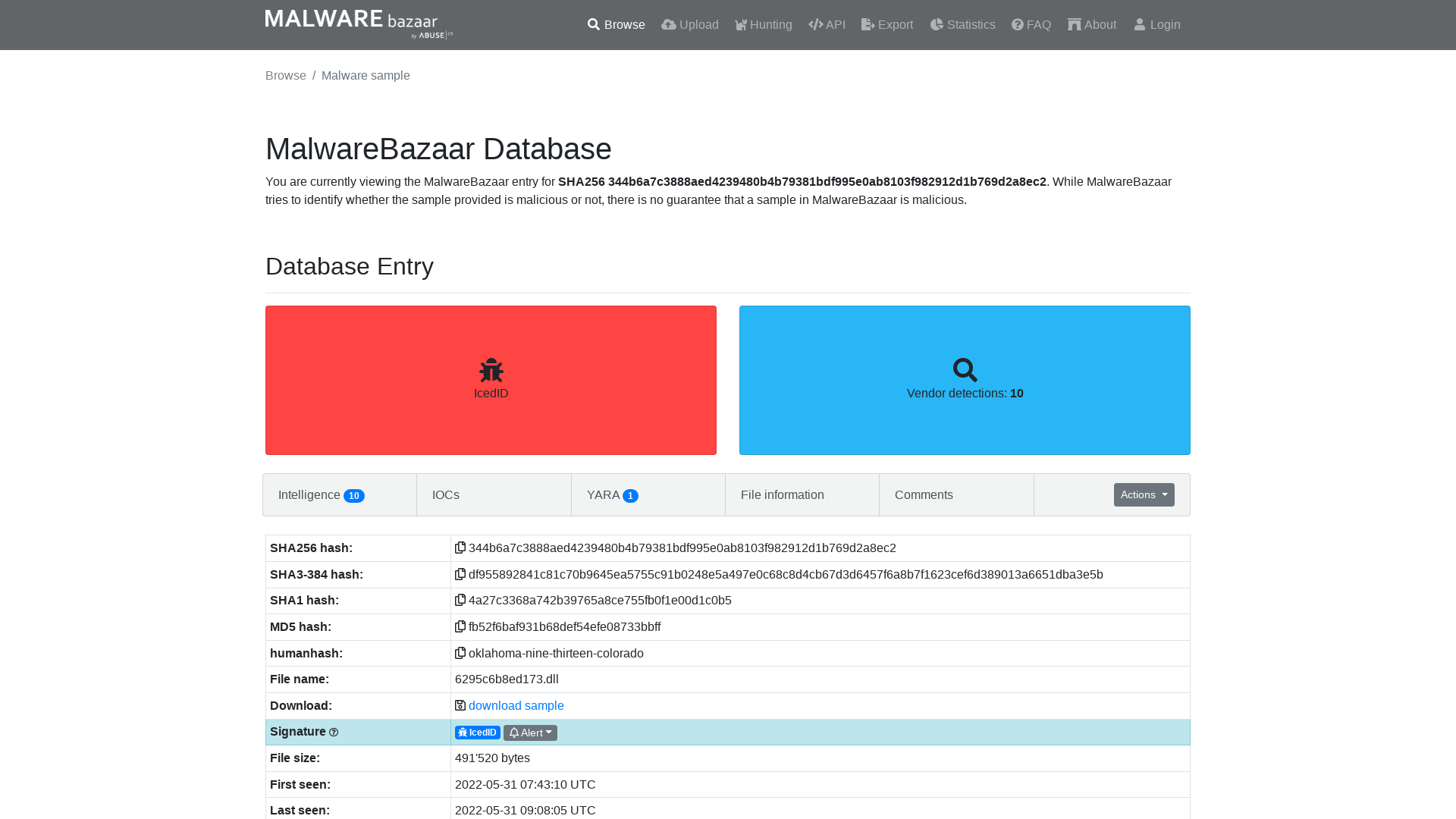
SANS Institute on Twitter: "🚨 EMERGENCY WEBCAST TOMORROW! 🚨 Join @malwarejake for this urgent webcast: #MSDT (MS Word) #ZeroDay. We'll identify how the vulnerability works, how to detect exploitation, and how to remediate. Register Here: https://t.co/PwgUlif5KV https://t.co/c9d552xzmC" / Twitter
https://twitter.com/sansinstitute/status/1531365738673590273
Microsoft Releases Workarounds for Office Vulnerability Under Active Exploitation
https://thehackernews.com/2022/05/microsoft-releases-workarounds-for.html
Rapid Response: Microsoft Office RCE - “Follina” MSDT Attack
https://www.huntress.com/blog/microsoft-office-remote-code-execution-follina-msdt-bug
GitHub - chvancooten/follina.py: POC to replicate the full 'Follina' Office RCE vulnerability for testing purposes
https://github.com/chvancooten/follina.py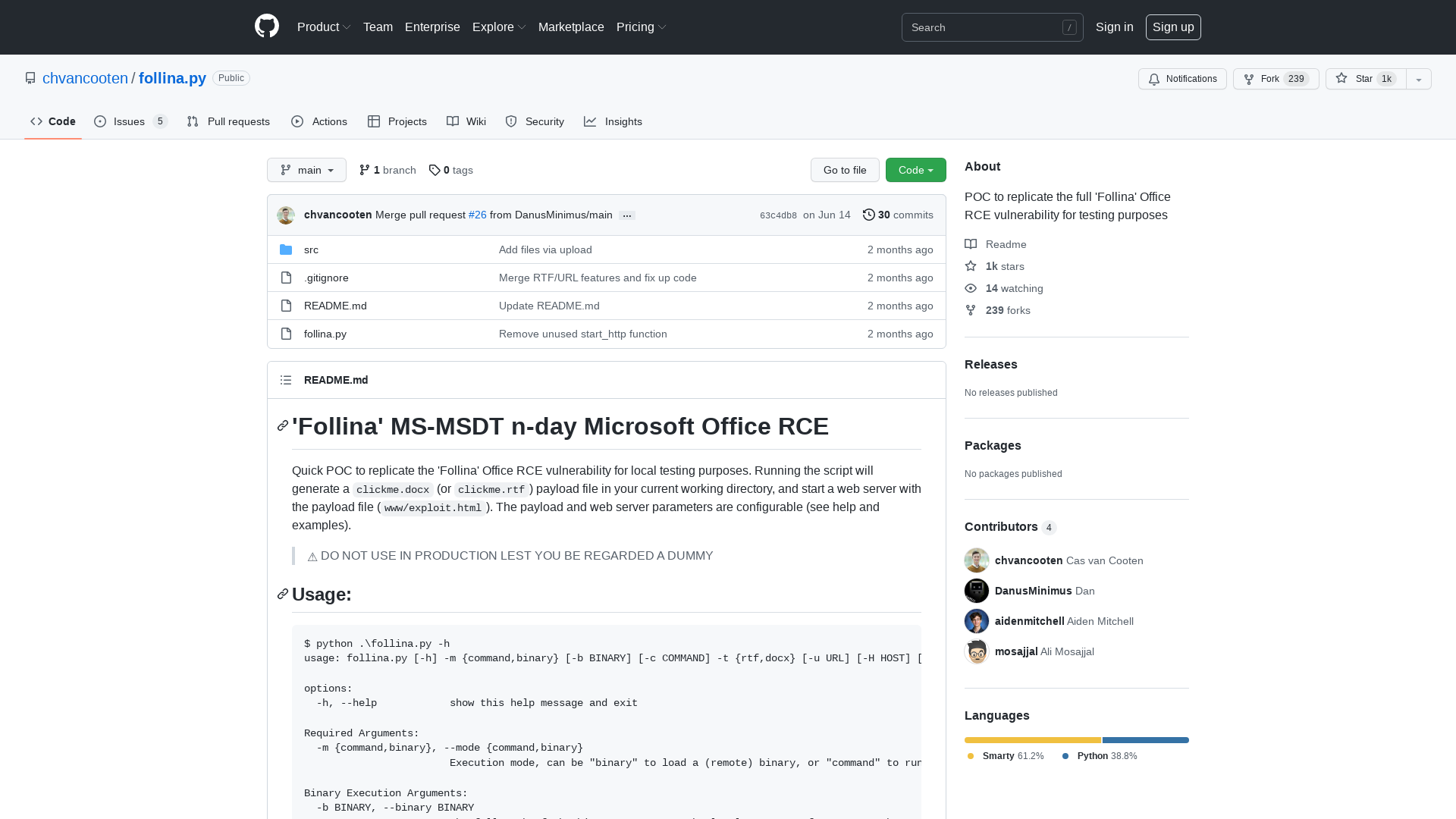
Will Dormann is not in Vegas on Twitter: "And of course the unfortunately named "wget" in PowerShell will blindly redirect to unsafe URIs and get exploited. No Office required! Of course it does. https://t.co/A9HMzrqYgO https://t.co/1na3rwpTRN" / Twitter
https://twitter.com/wdormann/status/1531619222295568384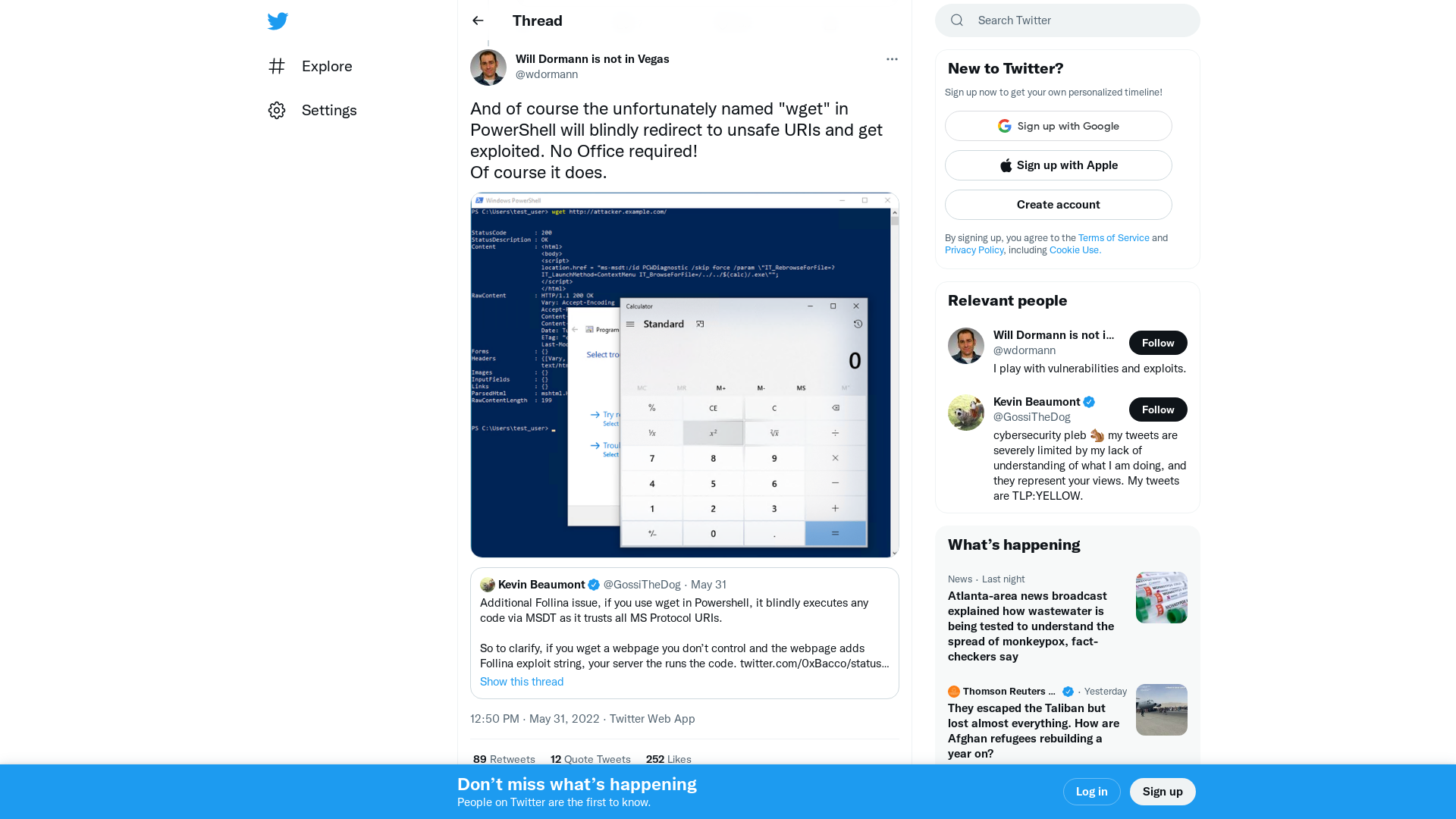
SCYTHE Library: Breaking: Follina (MSDT) Vulnerability
https://www.scythe.io/library/breaking-follina-msdt-vulnerability
Finding command execution sinks in decompiled JVM languages | $BLOG_TITLE
https://blog.deesee.xyz/code-review/reverse-engineering/2022/05/30/scala-kotlin-groovy-clojure-command-execution.html
SANS Emergency Webcast MSDT (MS Word) 0-day - Analysis and Remediation
http://ow.ly/E0jy50Jl9Wf
Exploiting MSDT 0-Day CVE-2022-30190 - YouTube
https://www.youtube.com/watch?v=dGCOhORNKRk
XLoader Botnet: Find Me If You Can - Check Point Research
https://research.checkpoint.com/2022/xloader-botnet-find-me-if-you-can/
Oddvar Moe's Blog – Notes from My adventures with Windows security
https://oddvar.moe/
| Job Preference
http://www.jobpreference.com
SANS Emergency Webcast MSDT (MS Word) 0-day - Analysis and Remediation
https://www.sans.org/u/1lBo
New XLoader botnet uses probability theory to hide its servers
https://www.bleepingcomputer.com/news/security/new-xloader-botnet-uses-probability-theory-to-hide-its-servers/