Follina — a Microsoft Office code execution vulnerability | by Kevin Beaumont | DoublePulsar
https://doublepulsar.com/follina-a-microsoft-office-code-execution-vulnerability-1a47fce5629e
VirusTotal - File - 4a24048f81afbe9fb62e7a6a49adbd1faf41f266b5f9feecdceb567aec096784
https://www.virustotal.com/gui/file/4a24048f81afbe9fb62e7a6a49adbd1faf41f266b5f9feecdceb567aec096784/detection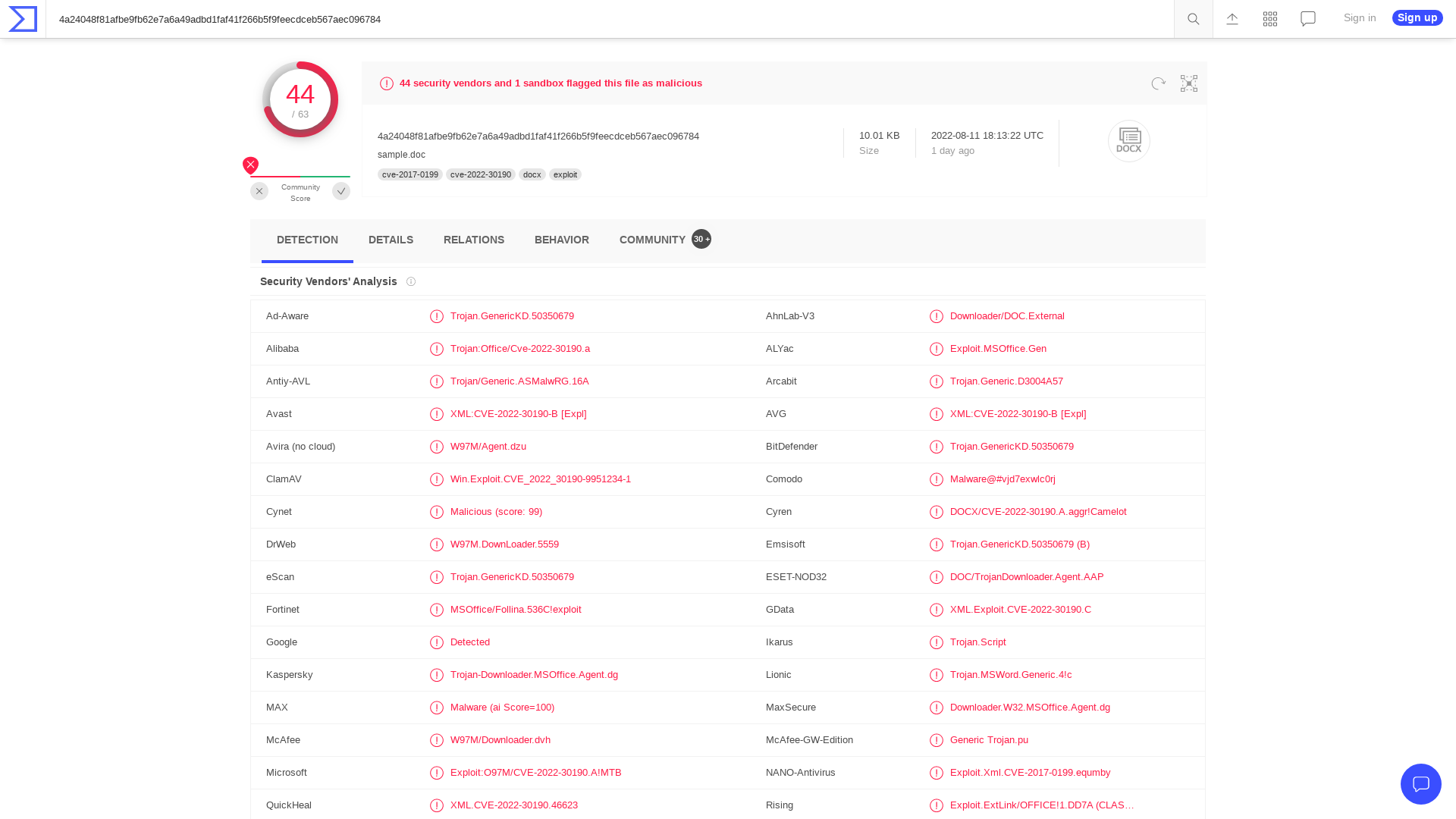
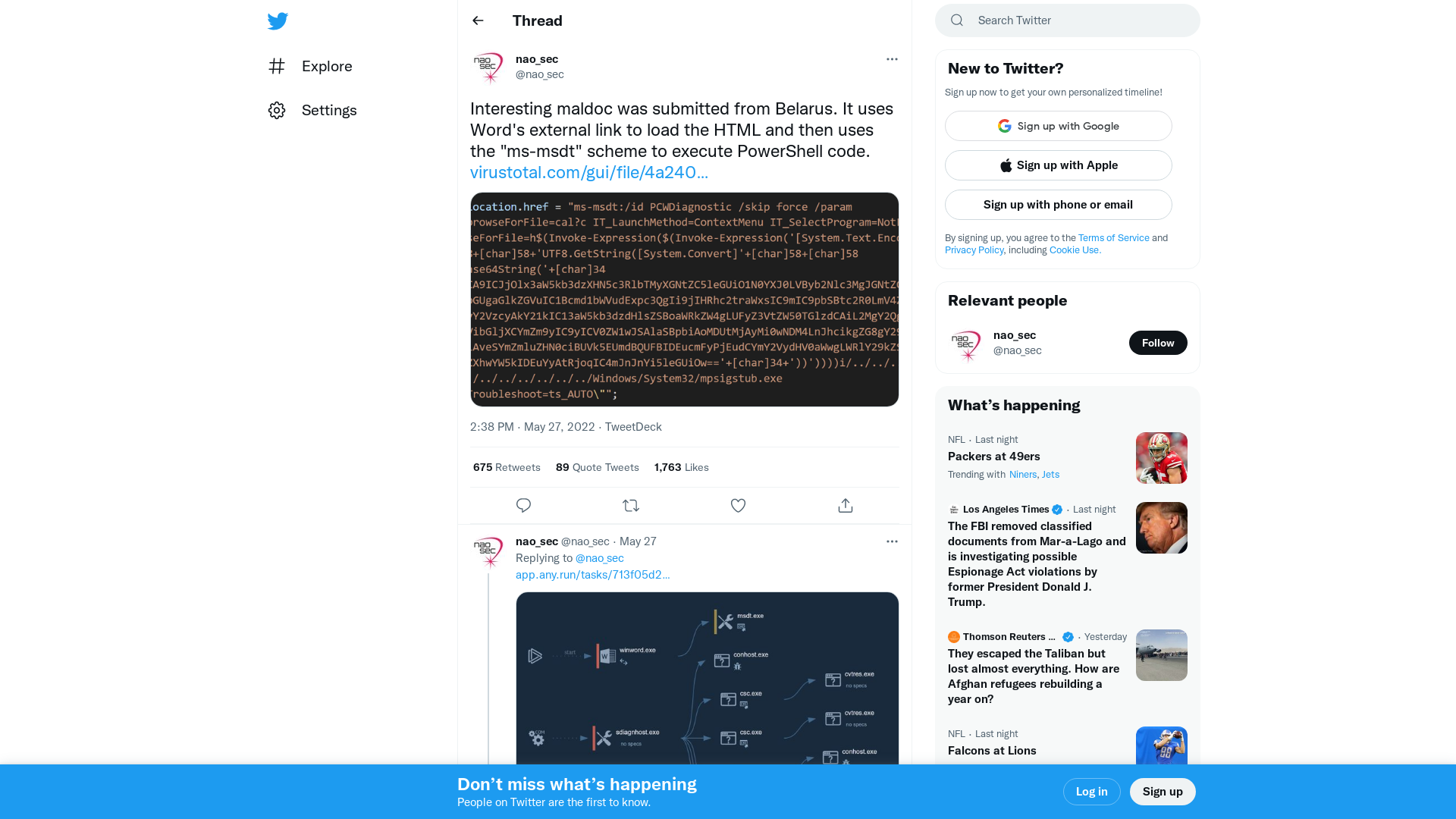
Kevin Beaumont on Twitter: "I did a writeup with detection rules and a BRILLIANT LOGO for Follina, an in the wild zero day in Microsoft Office, allowing code execution. https://t.co/9Z3asf6SqZ" / Twitter
https://twitter.com/GossiTheDog/status/1531011653235523586
The MS-MSDT 0-day Office RCE Proof-of-Concept Payload Building Process · GitHub
https://gist.github.com/tothi/66290a42896a97920055e50128c9f040
GitHub - chvancooten/follina.py: POC to replicate the full 'Follina' Office RCE vulnerability for testing purposes
https://github.com/chvancooten/follina.py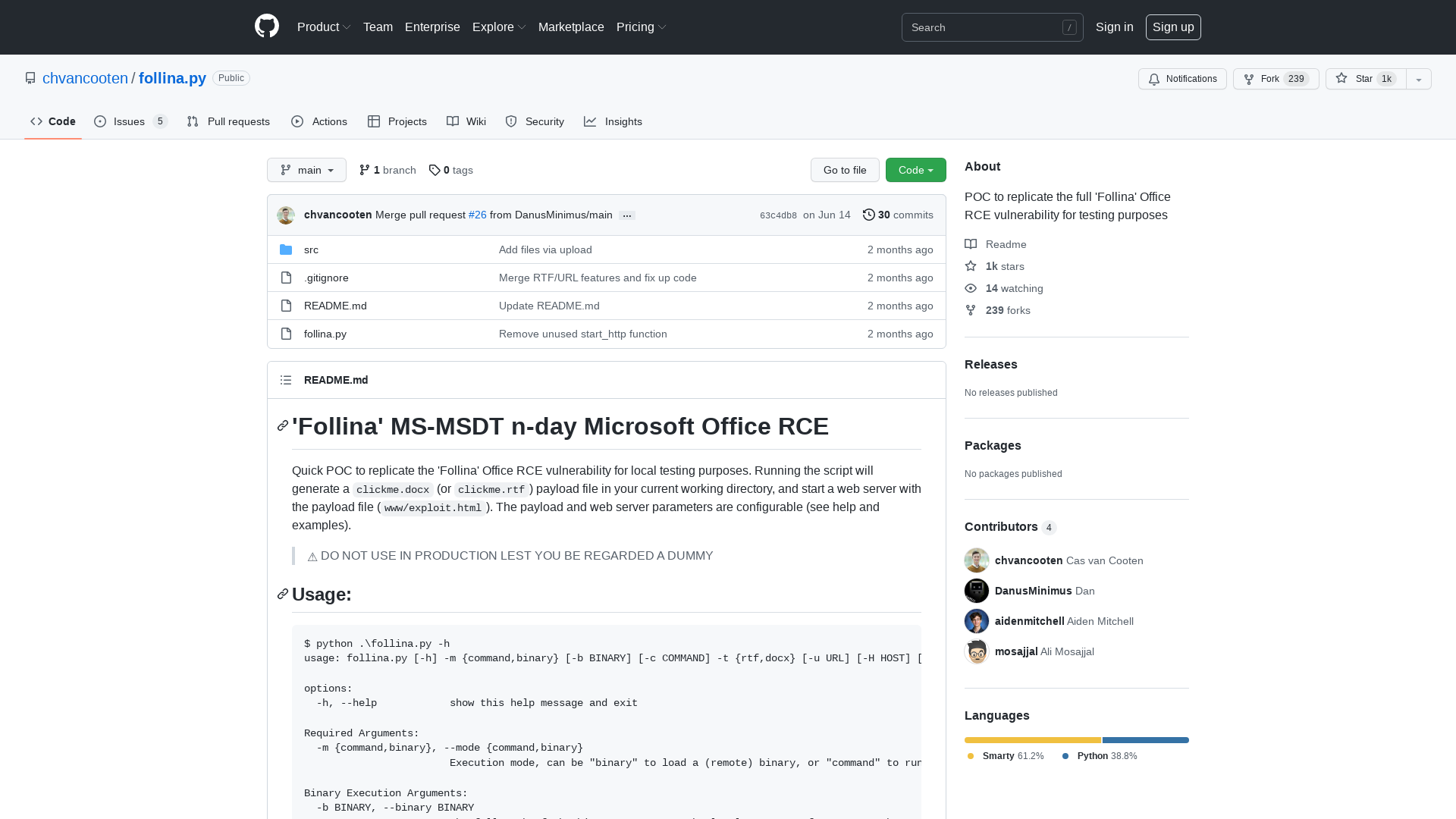
GitHub - klezVirus/NimlineWhispers3: A tool for converting SysWhispers3 syscalls for use with Nim projects
https://github.com/klezVirus/NimlineWhispers3/
Rapid Response: Microsoft Office RCE - “Follina” MSDT Attack
https://www.huntress.com/blog/microsoft-office-remote-code-execution-follina-msdt-bug
SANS Emergency Webcast MSDT (MS Word) 0-day - Analysis and Remediation
http://ow.ly/E0jy50Jl9Wf
Didier Stevens on Twitter: "FYI: https://t.co/t3ORRGaAnD" / Twitter
https://twitter.com/DidierStevens/status/1531033449561264128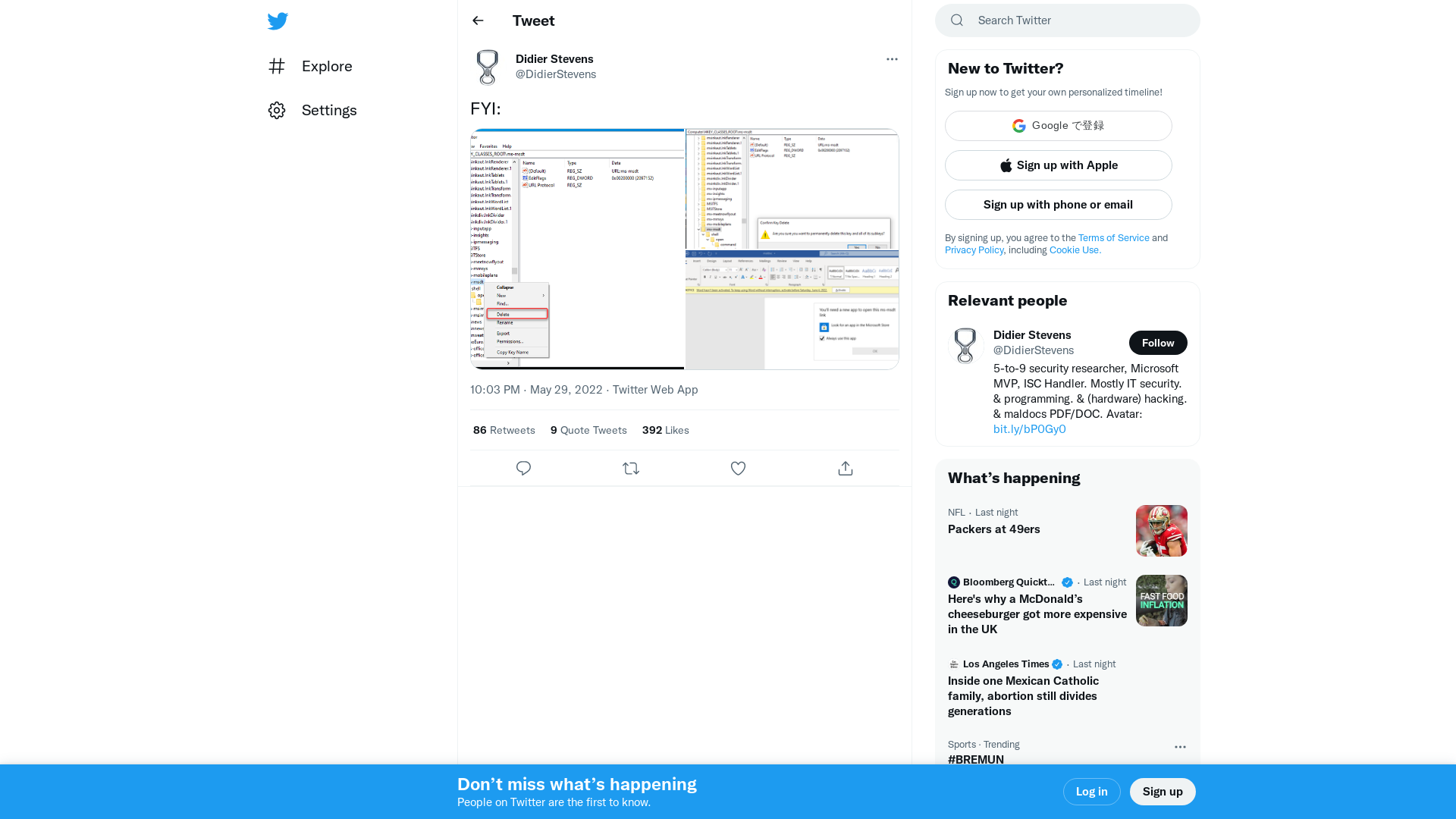
Threat Actor 2541: The Latest Tricks & Patterns - DISCARDED: Tales From the Threat Research Trenches | Podcast on Spotify
https://open.spotify.com/episode/61tEjtatHmWJrXfJ9MCHIl
Watch Out! Researchers Spot New Microsoft Office Zero-Day Exploit in the Wild
https://thehackernews.com/2022/05/watch-out-researchers-spot-new.html
New Microsoft Office zero-day used in attacks to execute PowerShell
https://www.bleepingcomputer.com/news/security/new-microsoft-office-zero-day-used-in-attacks-to-execute-powershell/
Kevin Beaumont on Twitter: "This is a nice find, looks like an EDR tooling gap from initial tests. (Possibly more, surprises Word didn’t block this)." / Twitter
https://twitter.com/GossiTheDog/status/1530844804061573120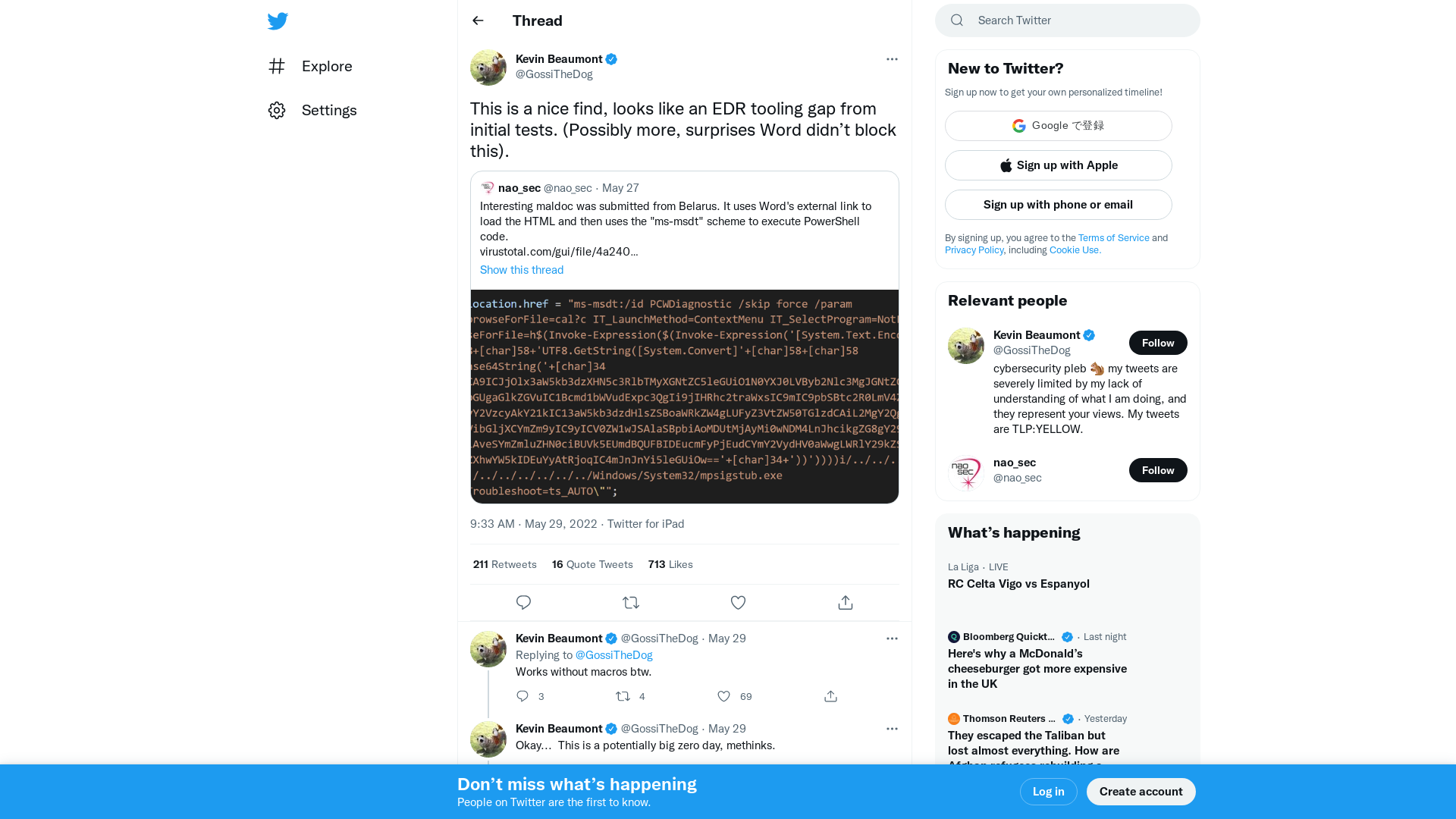
Jake Williams on Twitter: "Dear infosec: Sorry to barge in on your Memorial Day weekend, but if you're not following the msdt 0-day in MS Office you probably should be. I've validated it's working on my test systems and is trivial to exploit. First report here: https://t.co/x786bYr8iy" / Twitter
https://twitter.com/MalwareJake/status/1530974352660897793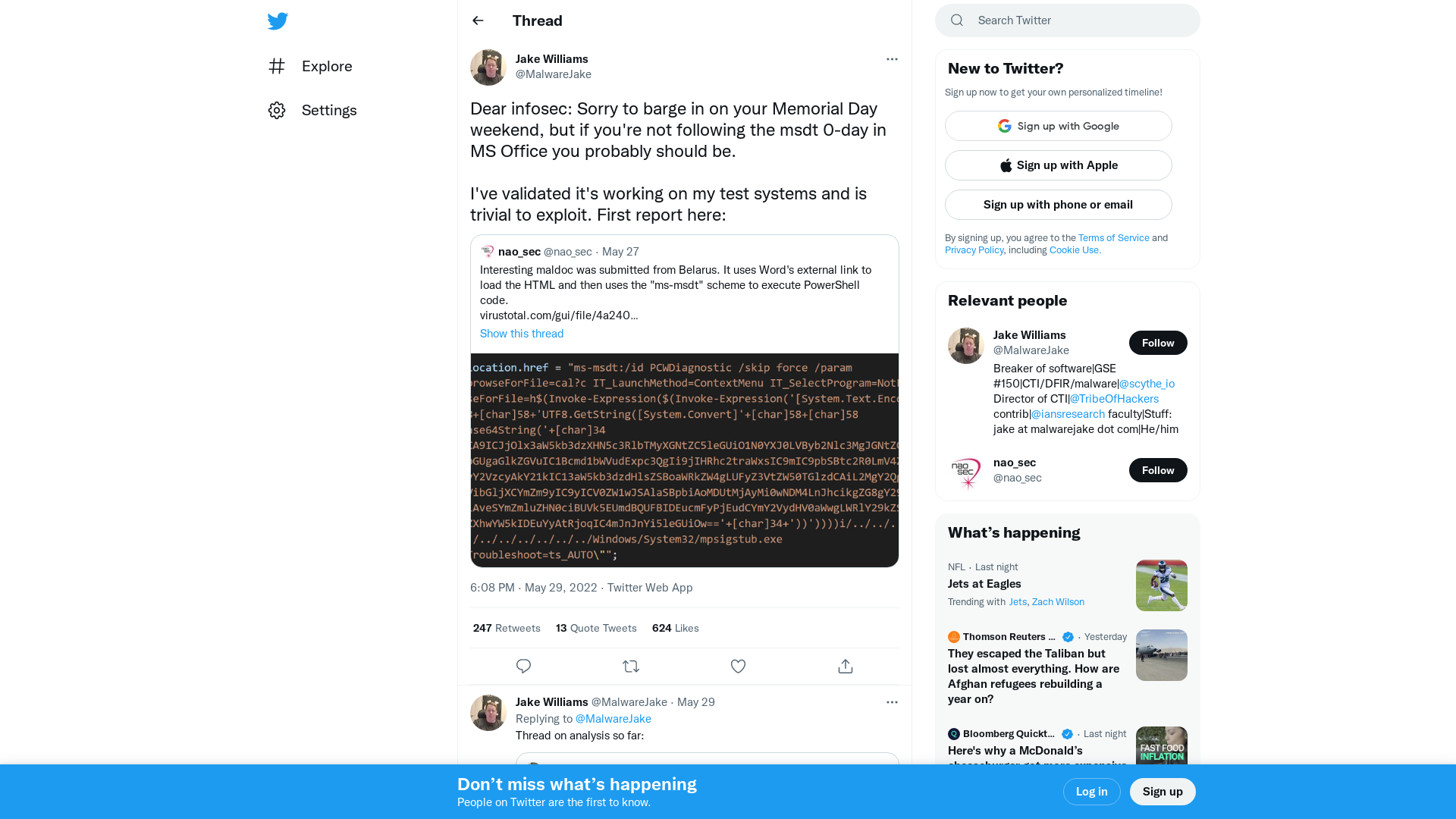
Space / Twitter
https://twitter.com/i/spaces/1ynJOZRDVrqGR
EnemyBot Linux Botnet Now Exploits Web Server, Android and CMS Vulnerabilities
https://thehackernews.com/2022/05/enemybot-linux-botnet-now-exploits-web.html
GitHub - Nautilus-Institute/quals-2022: Source code for the 2022 DEF CON Qualifiers.
https://github.com/Nautilus-Institute/quals-2022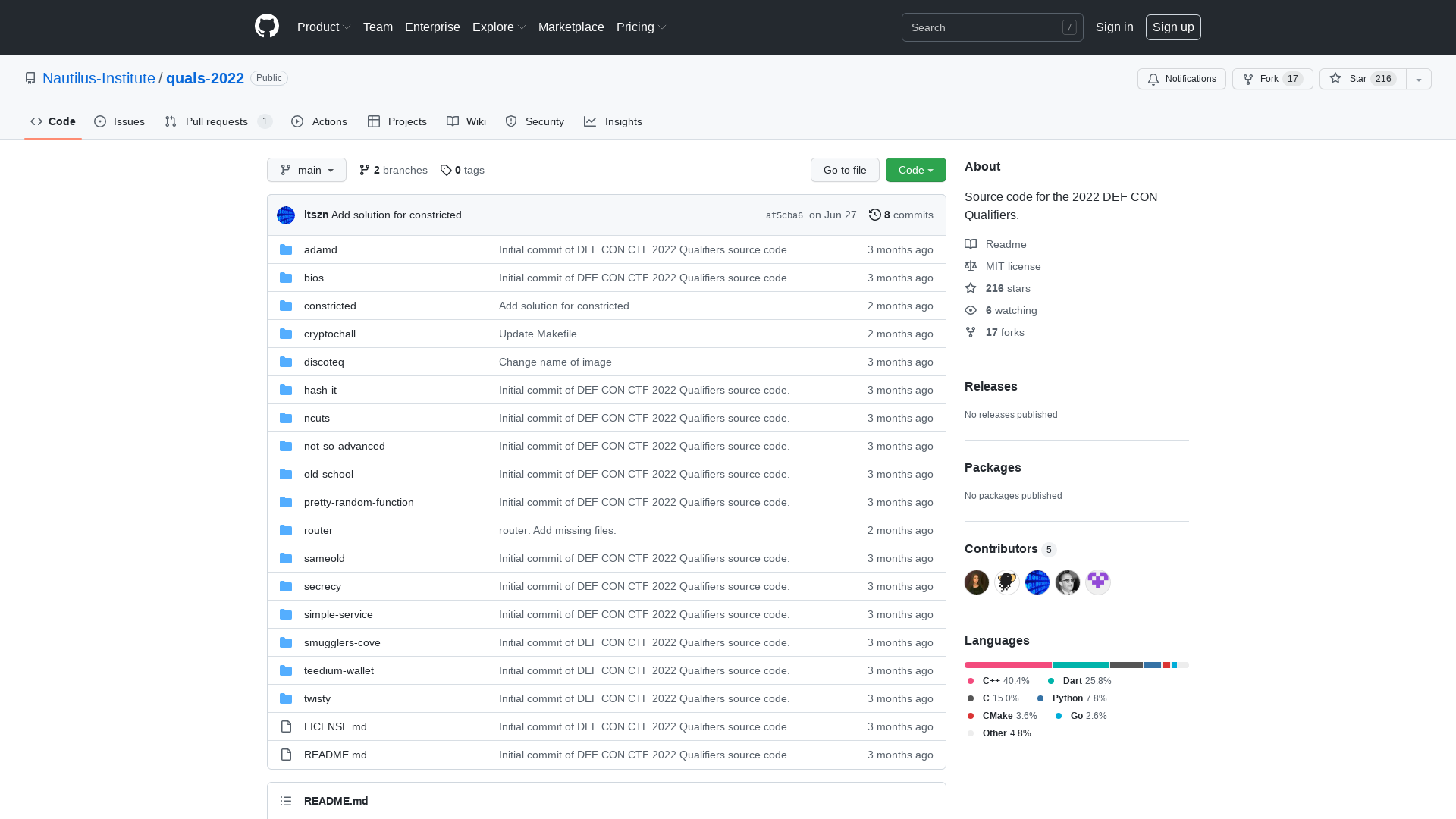
New 'GoodWill' Ransomware Forces Victims to Donate Money and Clothes to the Poor
https://thehackernews.com/2022/05/new-goodwill-ransomware-forces-victims.html
Bug Bounty Evolution: Not Your Grandson's Bug Bounty - Black Hat USA 2022 | Briefings Schedule
https://www.blackhat.com/us-22/briefings/schedule/#bug-bounty-evolution-not-your-grandsons-bug-bounty-27543
GitHub - Cracked5pider/KaynStrike: UDRL for CS
https://github.com/Cracked5pider/KaynStrike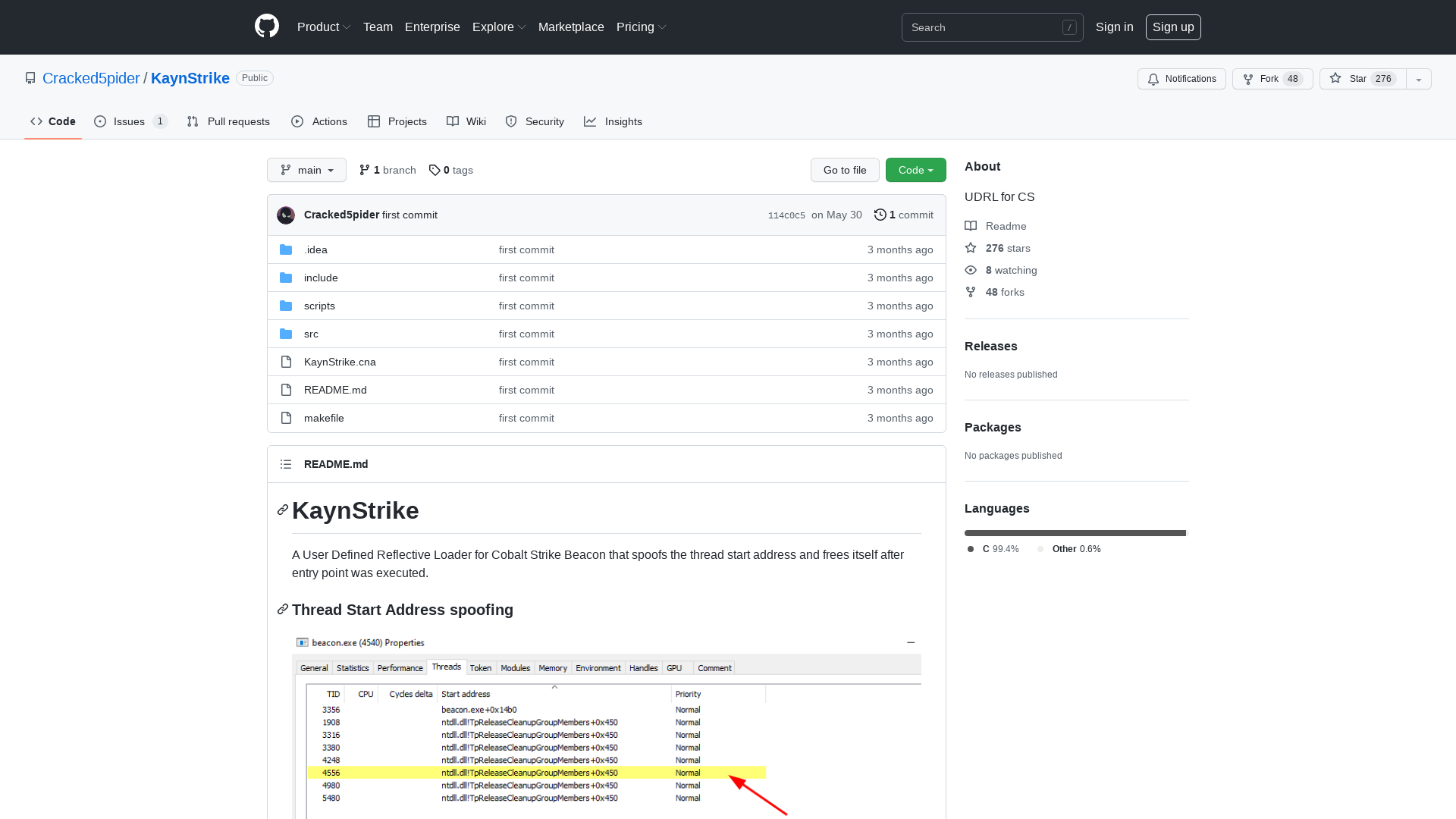
Jake Williams on Twitter: "Okay, so playing the #msdt 0-day a bit and here's what's happening: 1. The maldoc contains a linked HTML document 2. Word automatically retrieves the linked HTML document, which contains JS to reset the location to an ms-msdt protocol handler, which is present by default 1/ https://t.co/aJ1KenTvf1" / Twitter
https://twitter.com/MalwareJake/status/1531019243411623939
MISP 2.4.159 released with many improvements including performance
https://www.misp-project.org/2022/05/30/MISP.2.4.159.released.html/
GitHub - S4ntiagoP/freeBokuLoader: A simple BOF that frees UDRLs
https://github.com/S4ntiagoP/freeBokuLoader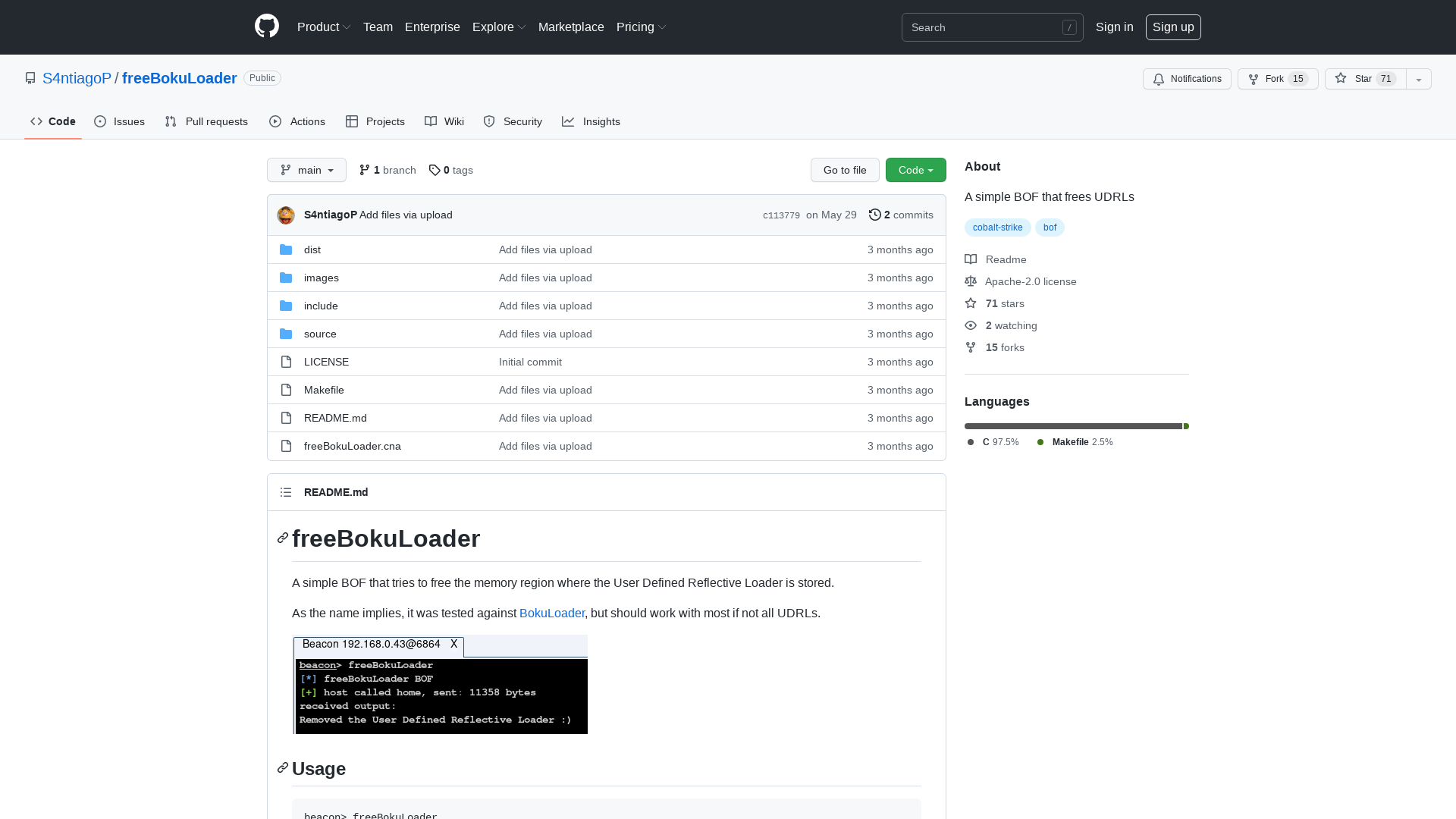
Troubleshooting: Allow users to access and run Troubleshooting Wizards
https://admx.help/?Category=Windows_10_2016&Policy=Microsoft.Policies.ScriptedDiagnostics::ScriptedDiagnosticsExecutionPolicy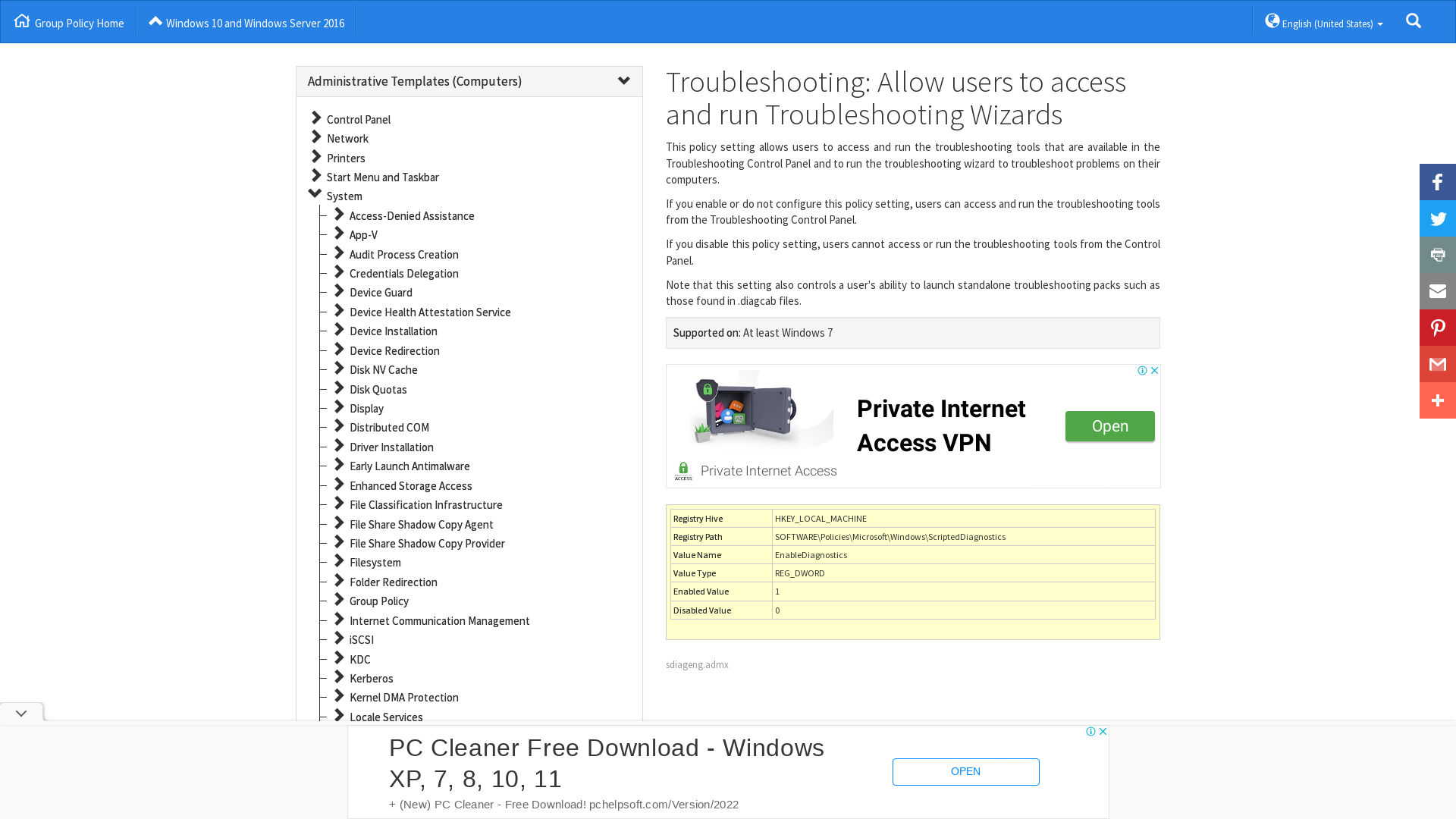
Bob Wachter on Twitter: "SF folks: it's now a big-time surge. No longer just cases (~500/d reported, so true # >2K, or ~250/100K/d). Also major uptick in hospitalizations: 98 in SF (vs 18 six wks ago). @UCSFHospitals 41 pts in hospital, twice April #. If you're trying to stay well, time to up your game. https://t.co/VNmhHal5EL" / Twitter
https://twitter.com/bob_wachter/status/1531315837264482304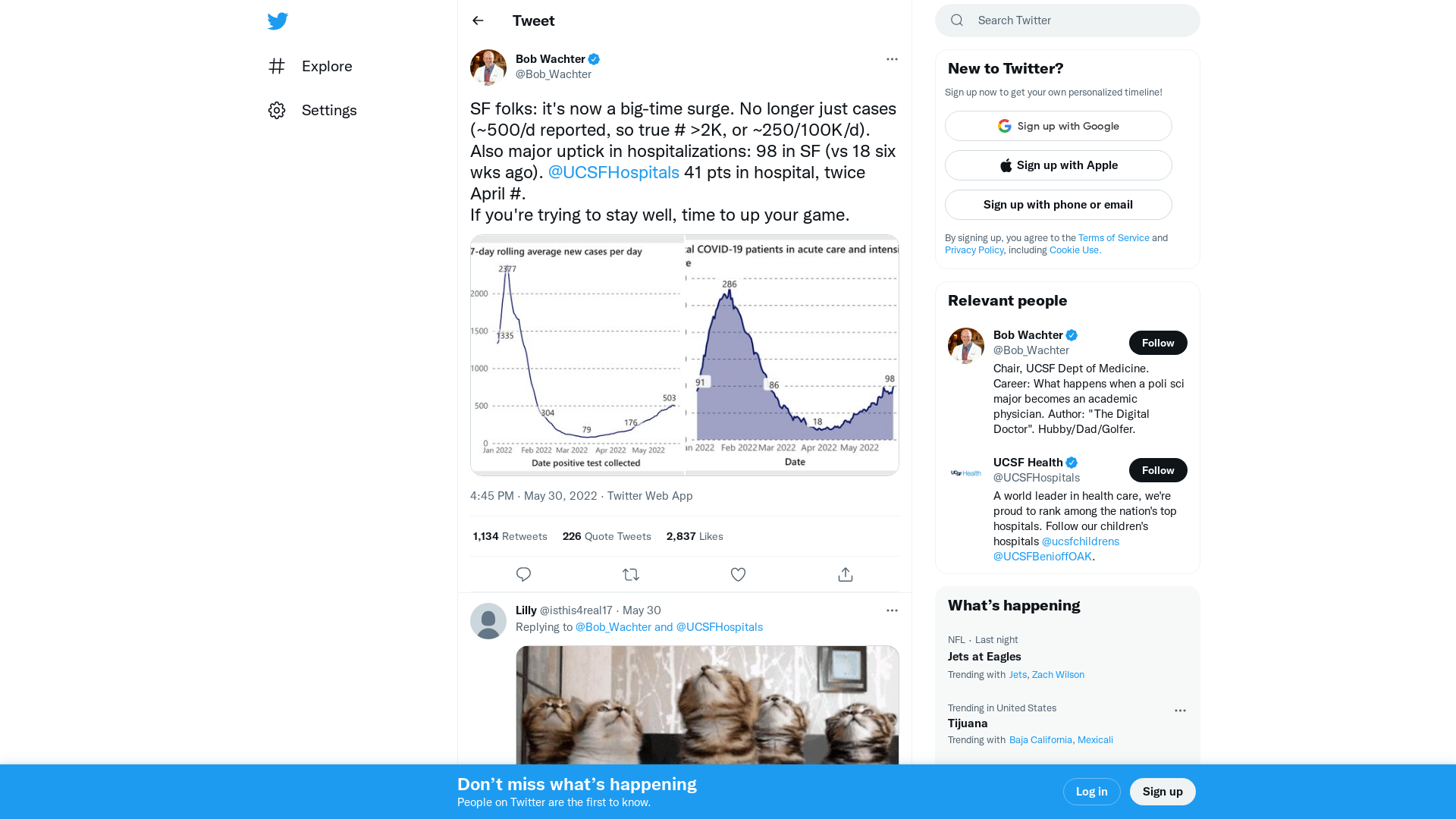
CNBC on Twitter: "Military-made cyberweapons could soon become available on the dark web, Interpol warns https://t.co/iTZaqryGnT" / Twitter
https://twitter.com/CNBC/status/1528769611121950724
SCYTHE Library: Breaking: Follina (MSDT) Vulnerability
https://www.scythe.io/library/breaking-follina-msdt-vulnerability