Hacker and Ransomware Designer Charged for Use and Sale of Ransomware, and Profit Sharing Arrangements with Cybercriminals | USAO-EDNY | Department of Justice
https://www.justice.gov/usao-edny/pr/hacker-and-ransomware-designer-charged-use-and-sale-ransomware-and-profit-sharing
Certifried combined with KrbRelayUp: non-privileged domain user to Domain Admin without adding/pre-owning computer accounts · GitHub
https://gist.github.com/tothi/f89a37127f2233352d74eef6c748ca25
http://go.usa.gov/xutwJ
http://go.usa.gov/xutwJ
Hacking Swagger-UI - from XSS to account takeovers
https://www.vidocsecurity.com/blog/hacking-swagger-ui-from-xss-to-account-takeovers/#newsletter
Nighthawk 0.2 - Catch Us If you Can - MDSec
https://www.mdsec.co.uk/2022/05/nighthawk-0-2-catch-us-if-you-can/
Lawrence Abrams on Twitter: "Microsoft is now calling info-stealers that target cryptocurrency wallets .... cryware! Almost all info-stealing malware steal crypto wallets, and have been for years. Please stop making up new malware classifications. It's confusing enough for many as it is. https://t.co/8C3rY9xSfW" / Twitter
https://twitter.com/LawrenceAbrams/status/1526598012440649728
NSA, Allies Issue Cybersecurity Advisory on Weaknesses that Allow Initial Access > National Security Agency/Central Security Service > Article
https://www.nsa.gov/Press-Room/News-Highlights/Article/Article/3033563/nsa-allies-issue-cybersecurity-advisory-on-weaknesses-that-allow-initial-access/
Data Marketplace Selling Info About Who Uses Period Tracking Apps
https://www.vice.com/en/article/v7d9zd/data-marketplace-selling-clue-period-tracking-data
Jon Gorenflo 🇺🇦🌻 on Twitter: "I've been doing security for...a while. There is a core set of tools that allow me to accomplish most of what's necessary. I keep seeing "hot" new tools that, after reading the code, I realize I accomplish with one liners. Forget tools, folks. Study the tech. #CyberSecurity" / Twitter
https://twitter.com/flakpaket/status/1526358211271483392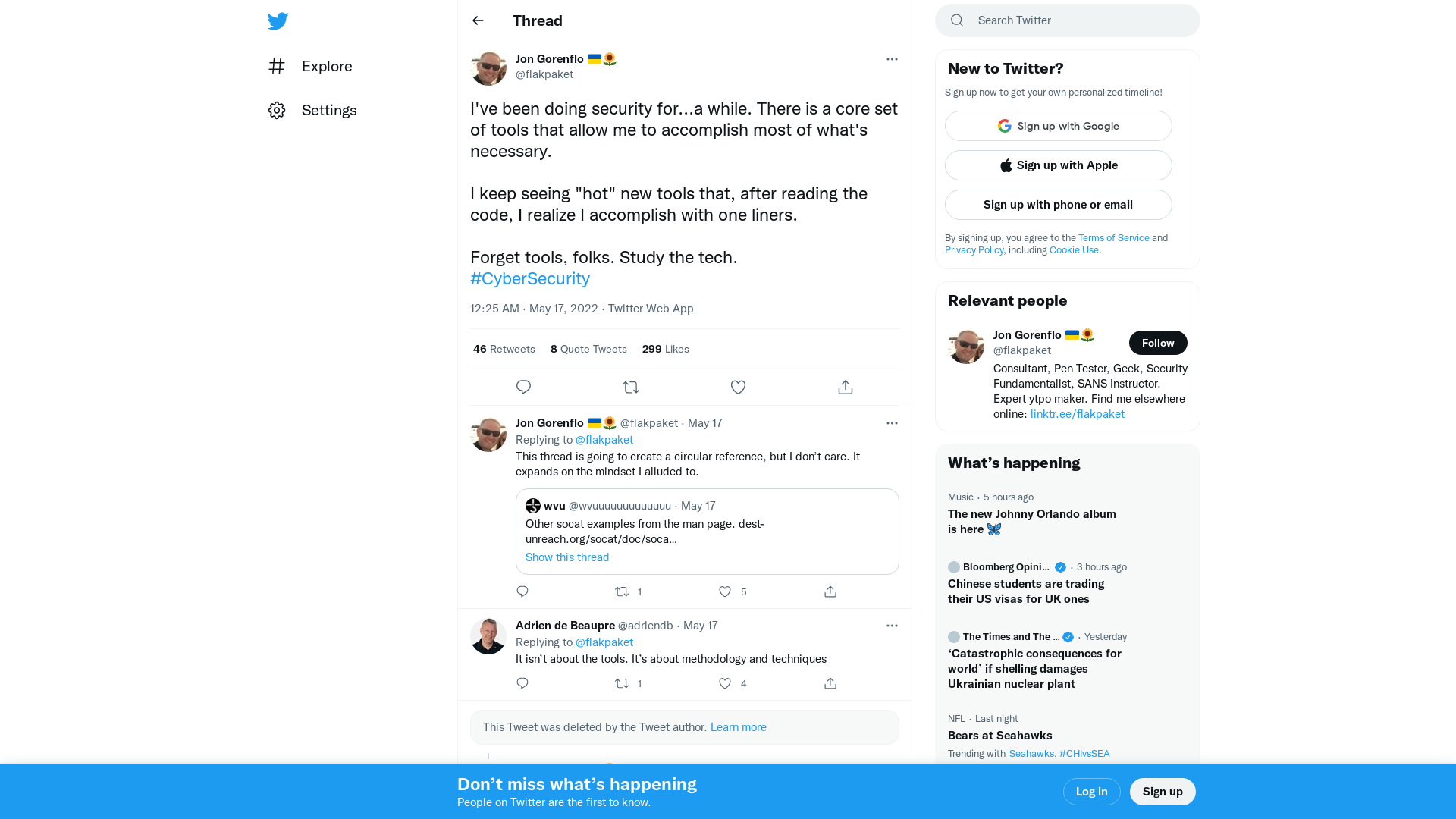
GitHub - sailay1996/SpoolTrigger: Weaponizing for privileged file writes bugs with PrintNotify Service
https://github.com/sailay1996/SpoolTrigger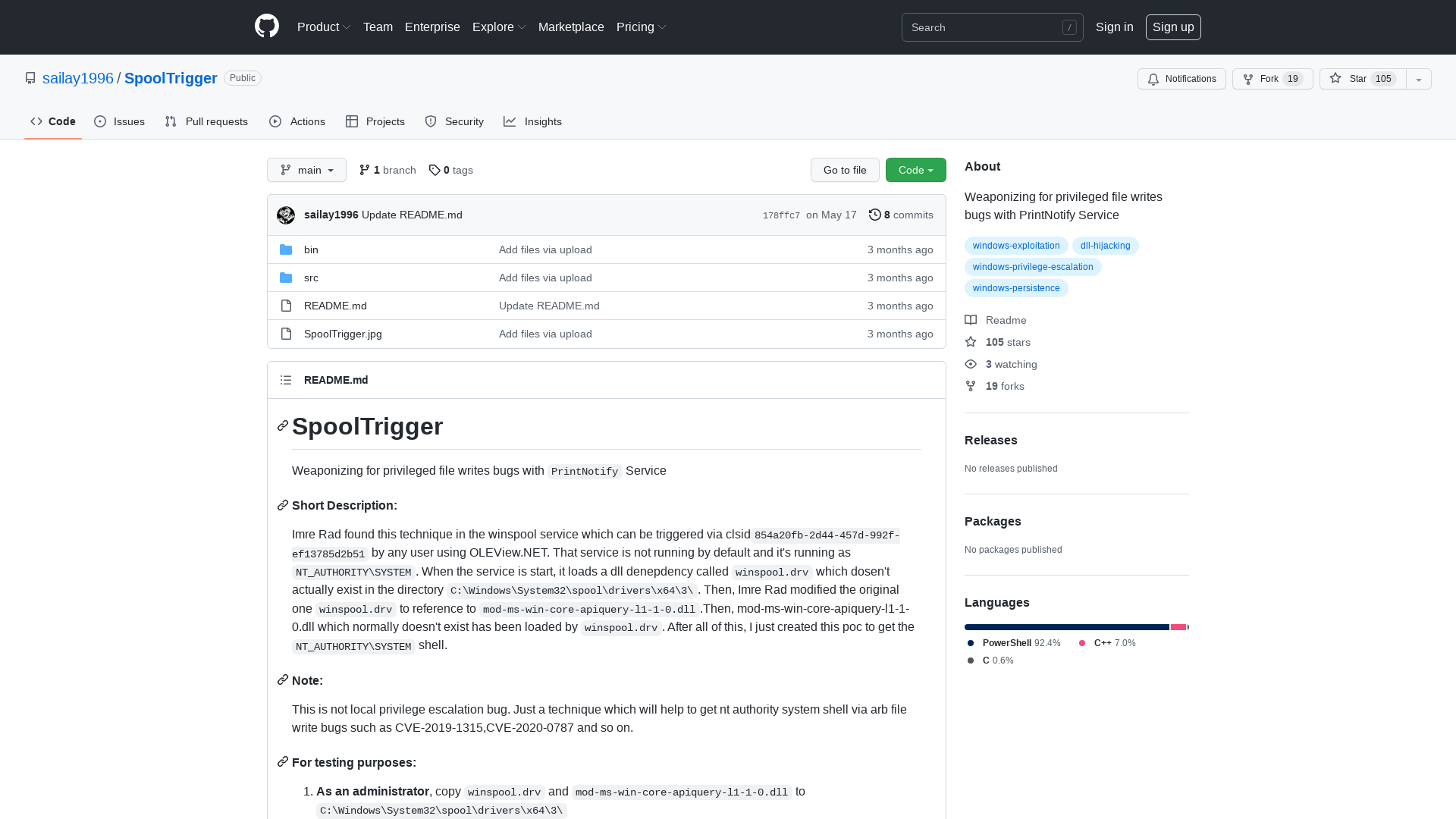
GitHub - GhostPack/SharpDPAPI: SharpDPAPI is a C# port of some Mimikatz DPAPI functionality.
https://github.com/GhostPack/SharpDPAPI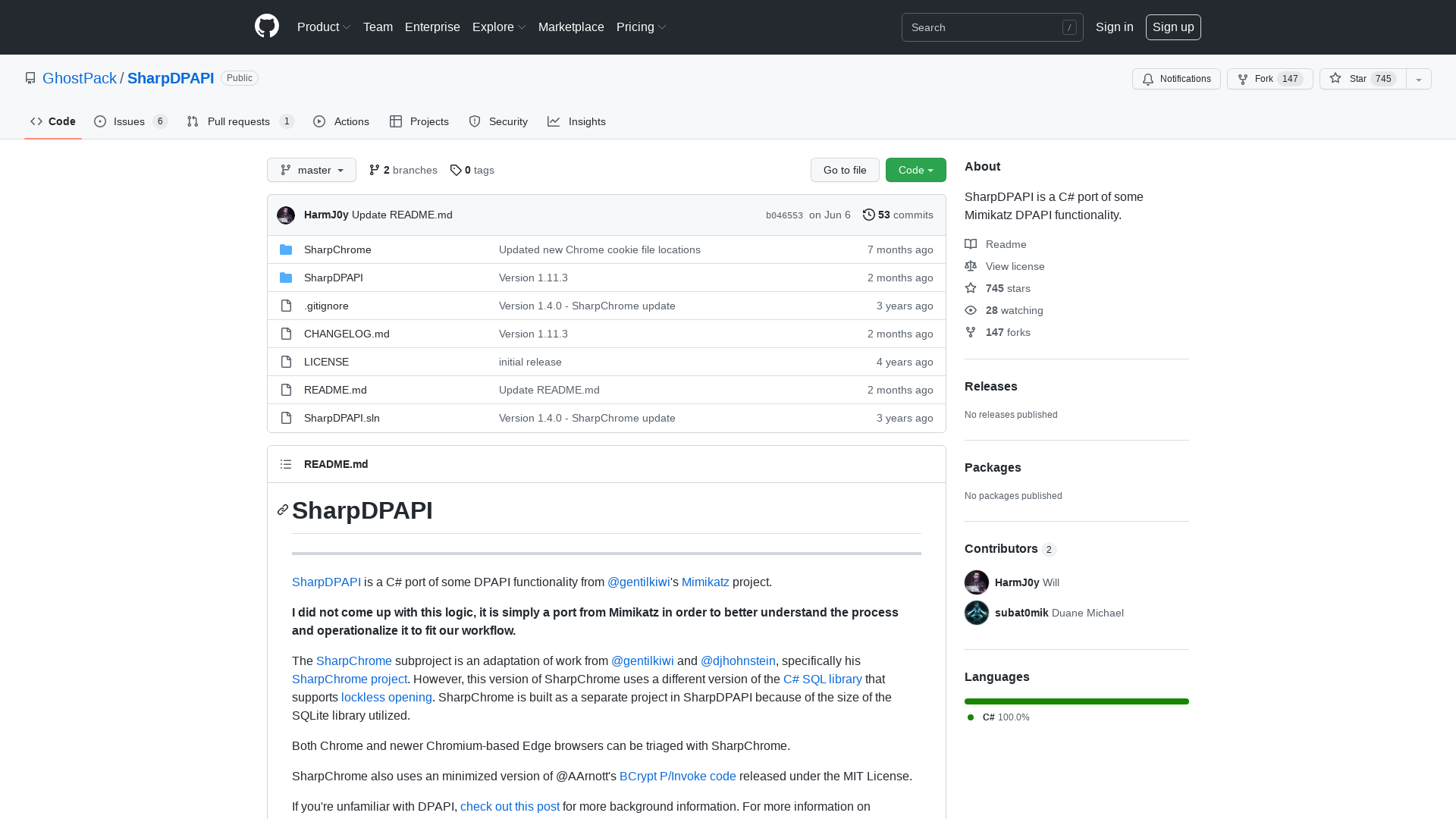
CVE-2022-22675: AppleAVD Overflow in AVC_RBSP::parseHRD | 0-days In-the-Wild
https://googleprojectzero.github.io/0days-in-the-wild/0day-RCAs/2022/CVE-2022-22675.html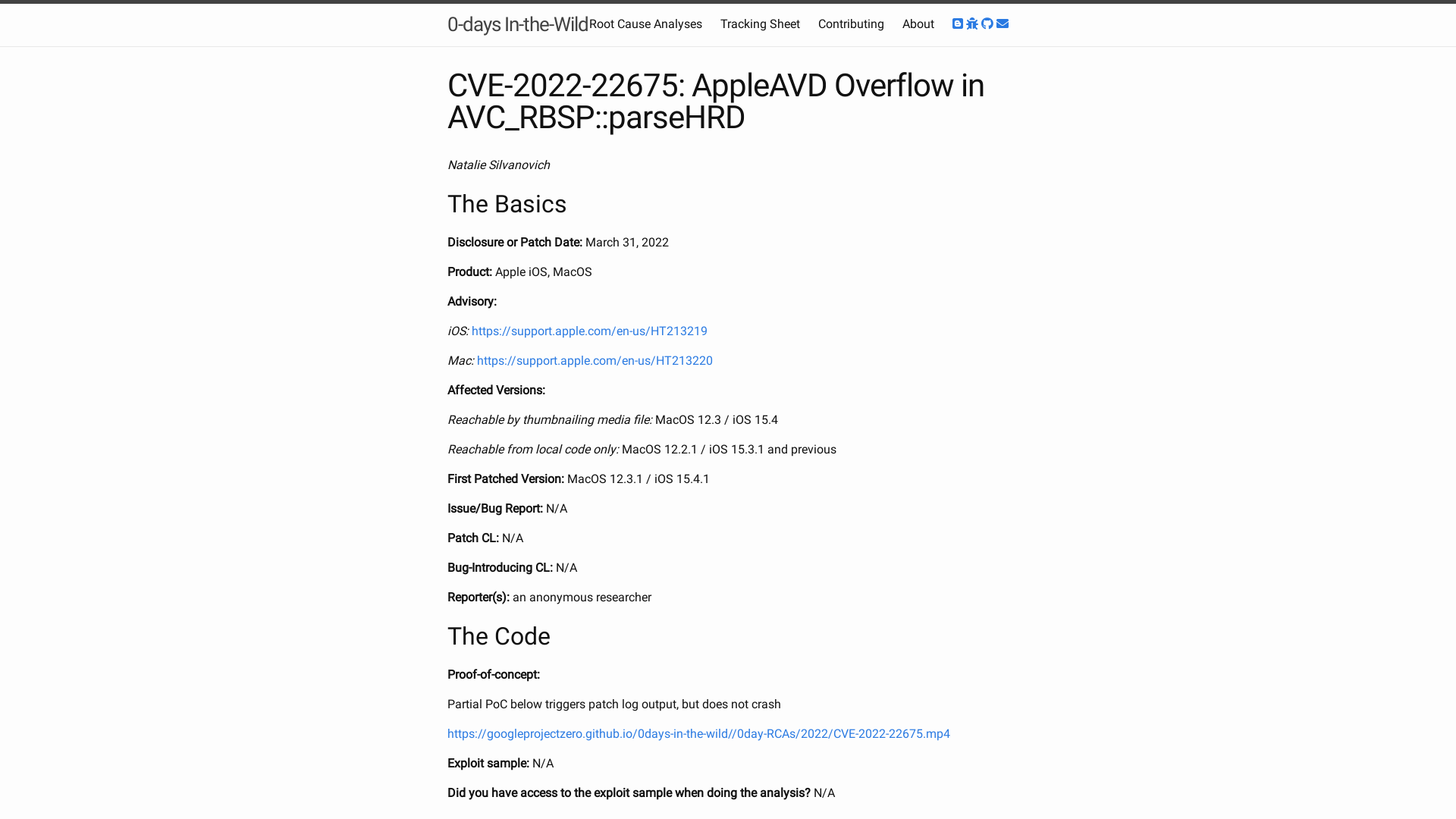
Blackhoodie at ReCon 2022 - Blackhoodie
https://blackhoodie.re/ReCon_Montreal/
Technical Advisory – Tesla BLE Phone-as-a-Key Passive Entry Vulnerable to Relay Attacks – NCC Group Research
https://research.nccgroup.com/2022/05/15/technical-advisory-tesla-ble-phone-as-a-key-passive-entry-vulnerable-to-relay-attacks/
Mapping MITRE ATT&CK with Window Event Log IDs - Security Investigation
https://www.socinvestigation.com/mapping-mitre-attck-with-window-event-log-ids/
Fake Mobile Apps Steal Facebook Credentials, Cryptocurrency-Related Keys
https://www.trendmicro.com/en_us/research/22/e/fake-mobile-apps-steal-facebook-credentials--crypto-related-keys.html
Hackers can steal your Tesla Model 3, Y using new Bluetooth attack
https://www.bleepingcomputer.com/news/security/hackers-can-steal-your-tesla-model-3-y-using-new-bluetooth-attack/
ICCL report on the scale of Real-Time Bidding data broadcasts in the U.S. and Europe - Irish Council for Civil Liberties
https://www.iccl.ie/digital-data/iccl-report-on-the-scale-of-real-time-bidding-data-broadcasts-in-the-u-s-and-europe/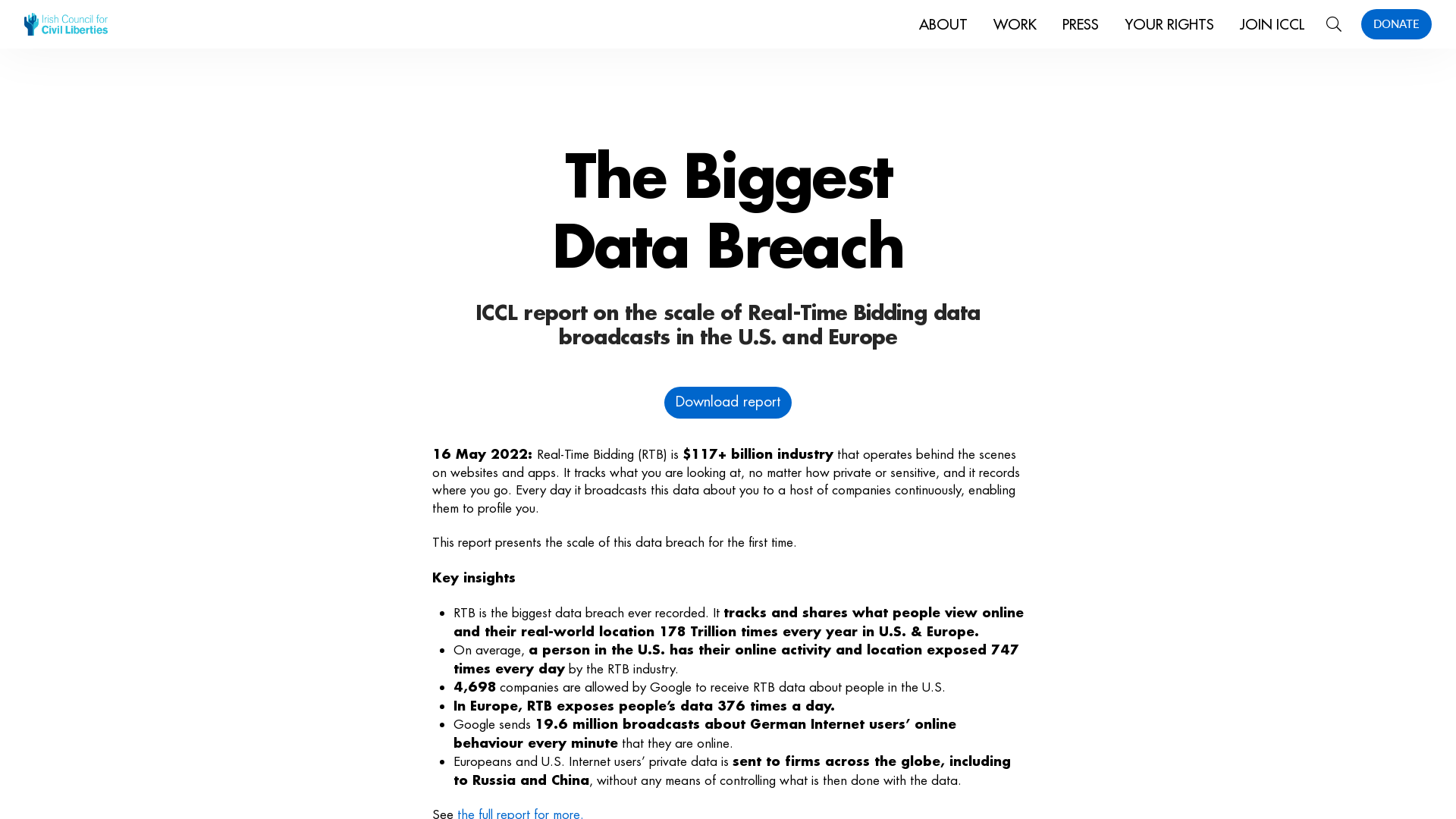
UpdateAgent Returns with New macOS Malware Dropper Written in Swift
https://thehackernews.com/2022/05/updateagent-returns-with-new-macos.html
New Sysrv Botnet Variant Hijacking Windows and Linux with Crypto Miners
https://thehackernews.com/2022/05/new-sysrv-botnet-variant-hijacking.html
briankrebs on Twitter: "1/ So you go shopping for a PIV card reader, because the US govt gave you one and you're curious to look at what's on it. You settle for this "DOD military USB common access smart card reader," because it's compatible with Mac OS. Cool! Only $15! What a bargain! https://t.co/MHPPkZVixp" / Twitter
https://twitter.com/briankrebs/status/1526297731748216833
Tetragon - eBPF-based Security Observability & Runtime Enforcement - Isovalent
https://isovalent.com/blog/post/2022-05-16-tetragon
New processor for BPF bytecode by Heurs · Pull Request #4258 · NationalSecurityAgency/ghidra · GitHub
https://github.com/NationalSecurityAgency/ghidra/pull/4258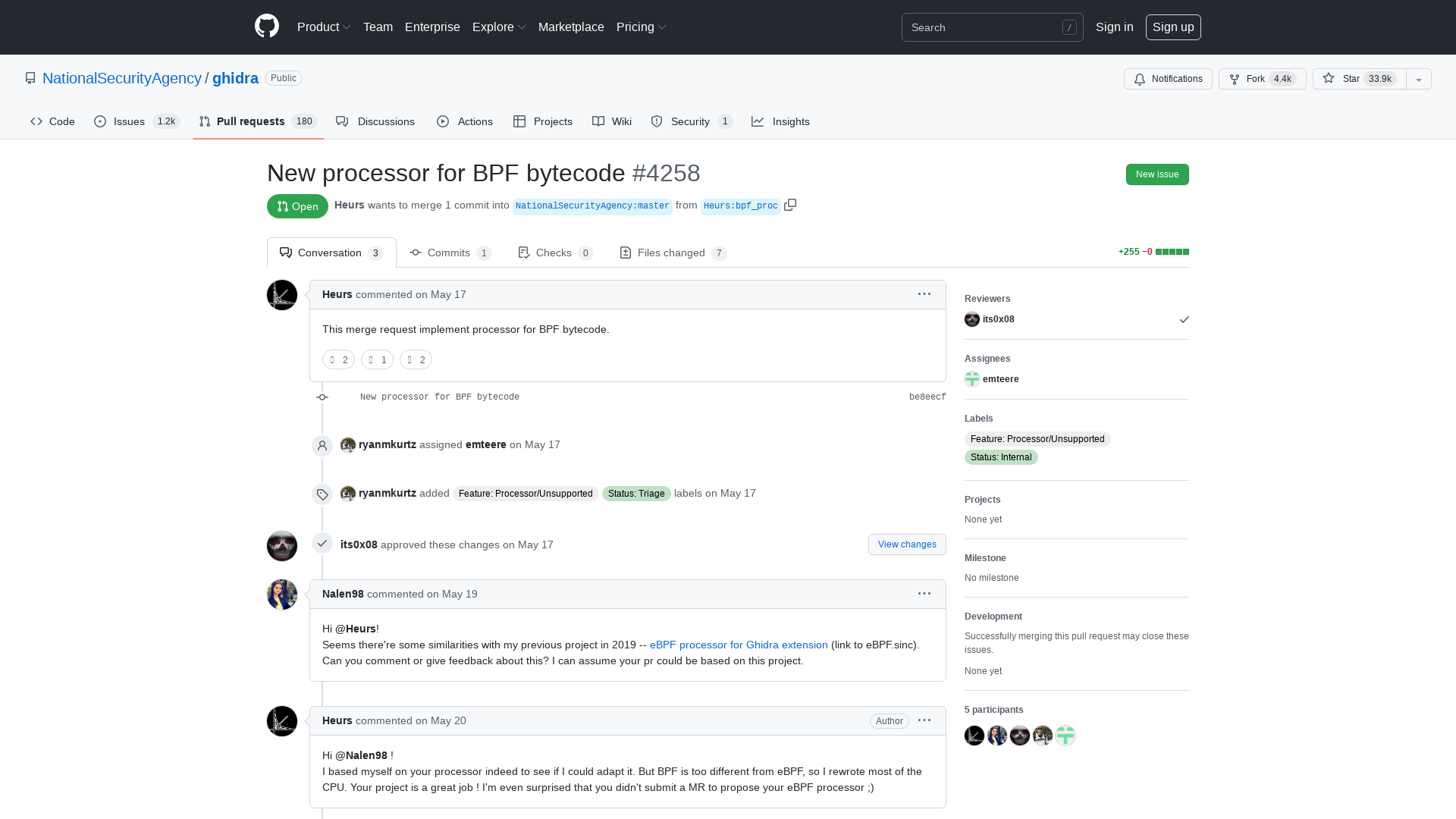
The invaders destroyed the National Gene Bank of Plants of Ukraine | odessa-journal.com
https://odessa-journal.com/the-invaders-destroyed-the-national-gene-bank-of-plants-of-ukraine/