Akamai Blog | Critical Remote Code Execution Vulnerabilities in Windows RPC Runtime
https://www.akamai.com/blog/security/critical-remote-code-execution-vulnerabilities-windows-rpc-runtime
Dismantling ZLoader: How malicious ads led to disabled security tools and ransomware - Microsoft Security Blog
https://www.microsoft.com/security/blog/2022/04/13/dismantling-zloader-how-malicious-ads-led-to-disabled-security-tools-and-ransomware/
Make phishing great again. VSTO office files are the new macro nightmare? | by Daniel Schell | Medium
https://medium.com/@airlockdigital/make-phishing-great-again-vsto-office-files-are-the-new-macro-nightmare-e09fcadef010
Exploiting Struts RCE on 2.5.26
https://mc0wn.blogspot.com/2021/04/exploiting-struts-rce-on-2526.html
Bypassing Cortex XDR | mr.d0x
https://mrd0x.com/cortex-xdr-analysis-and-bypass/
Project Zero: CVE-2021-1782, an iOS in-the-wild vulnerability in vouchers
https://googleprojectzero.blogspot.com/2022/04/cve-2021-1782-ios-in-wild-vulnerability.html
INCONTROLLER: New State-Sponsored Cyber Attack Tools Target Multiple Industrial Control Systems | Mandiant
https://www.mandiant.com/resources/incontroller-state-sponsored-ics-tool
Proof of Concept: CVE-2022-21907 HTTP Protocol Stack Remote Code Execution Vulnerability | Core Labs
https://www.coresecurity.com/core-labs/articles/proof-concept-cve-2022-21907-http-protocol-stack-remote-code-execution
GitHub - f8al/CVE-2022-26809: CVE-2022-26809 PoC
https://github.com/f8al/CVE-2022-26809
Offensive Driver Development
https://courses.zeropointsecurity.co.uk/courses/offensive-driver-development
Nina Luong on Twitter: "my university sent an email about providing $7,500 in assistance to those experiencing financial hardship due to the pandemic....turns out it was a PHISHING exercise... is this a joke???" / Twitter
https://twitter.com/nina_luong/status/1513997316134301698
Page Not Found - Google Careers
https://careers.google.com/jobs/results/137586428310627014/
pocs/windows/spooler-splenumforms-iov at main · grigoritchy/pocs · GitHub
https://github.com/grigoritchy/pocs/tree/main/windows/spooler-splenumforms-iov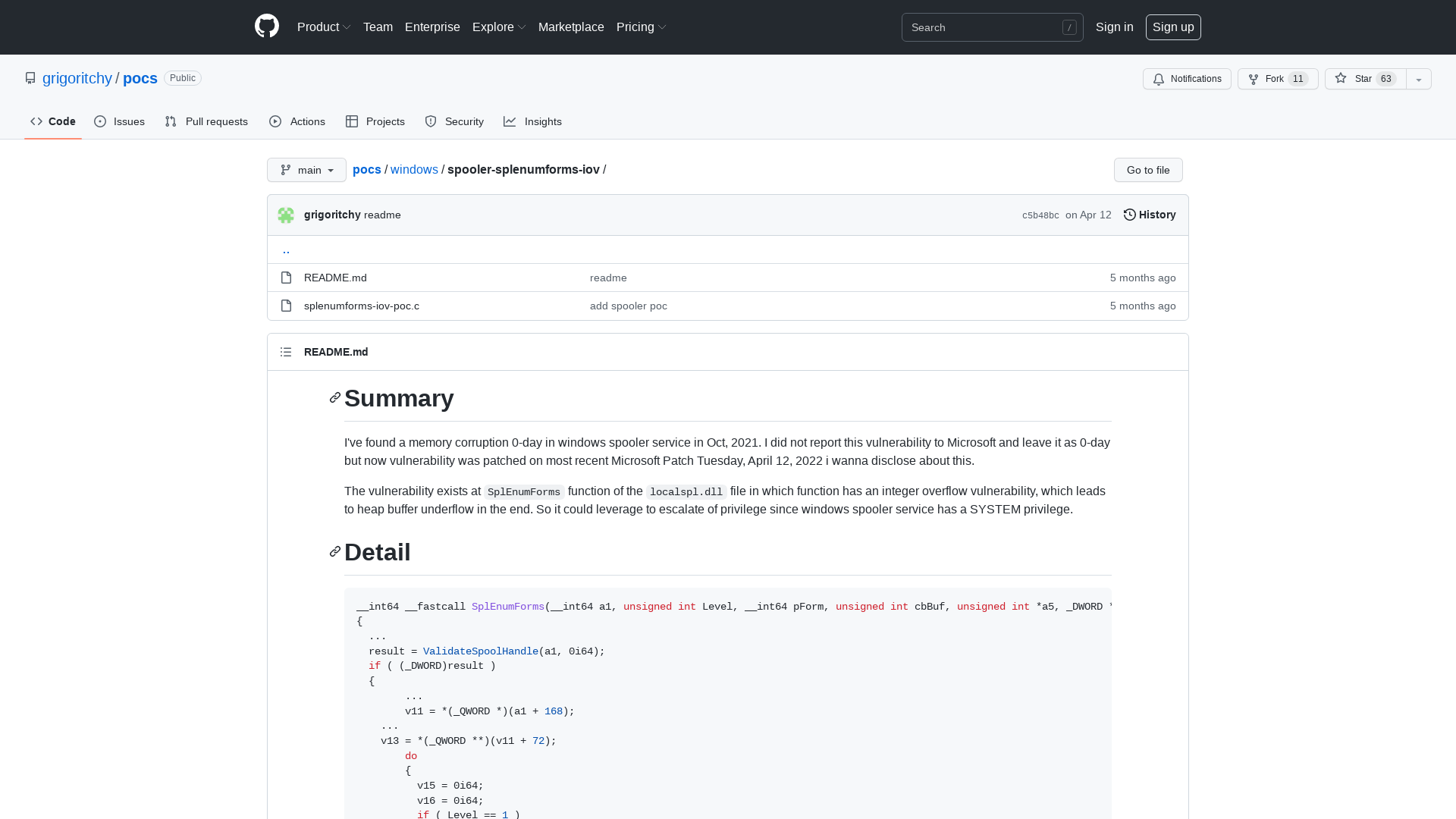
U.S. Warns of APT Hackers Targeting ICS/SCADA Systems with Specialized Malware
https://thehackernews.com/2022/04/us-warns-of-apt-hackers-targeting.html
| Job Preference
http://www.jobpreference.com
MicroBurst/Get-AzPasswords.ps1 at master · NetSPI/MicroBurst · GitHub
https://github.com/NetSPI/MicroBurst/blob/master/Az/Get-AzPasswords.ps1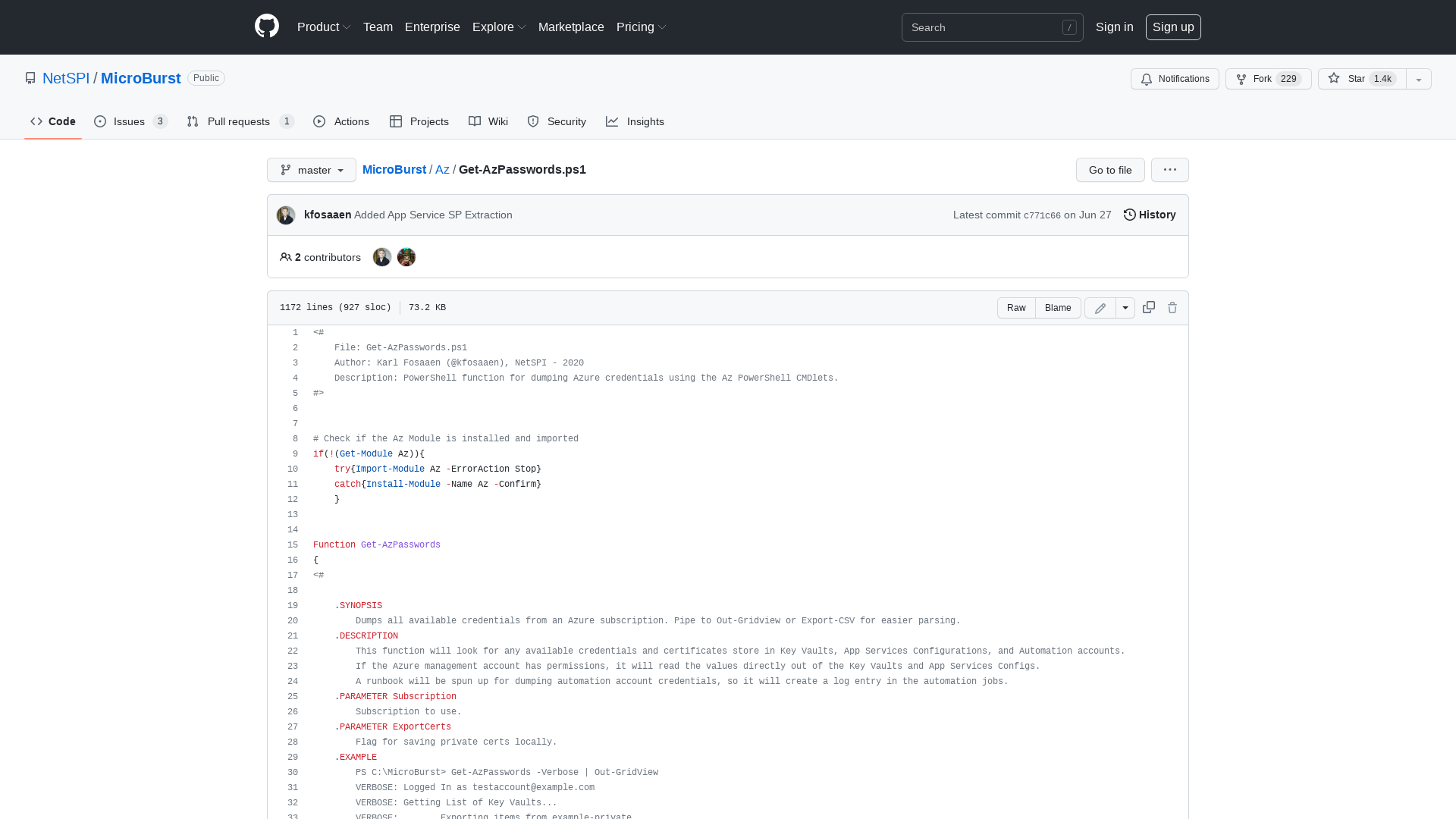
Red Canary on Twitter: "New from @jsecurity101: Nearly all activity in Windows can be tied back to an identity using access tokens. Therefore, having the ability to track a token back to its source would provide invaluable visibility for incident response, detection, and more. https://t.co/0Uaq7xtQHq" / Twitter
https://twitter.com/redcanary/status/1514629024684912642
Where To Find Us | SpecterOps
https://specterops.io/resources/upcoming-events
Simple, Secure Identity Verification | ID.me
http://ID.me
CVE-2022-26809 – Critical Windows RPC Vulnerability – PwnDefend
https://www.pwndefend.com/2022/04/14/cve-2022-26809/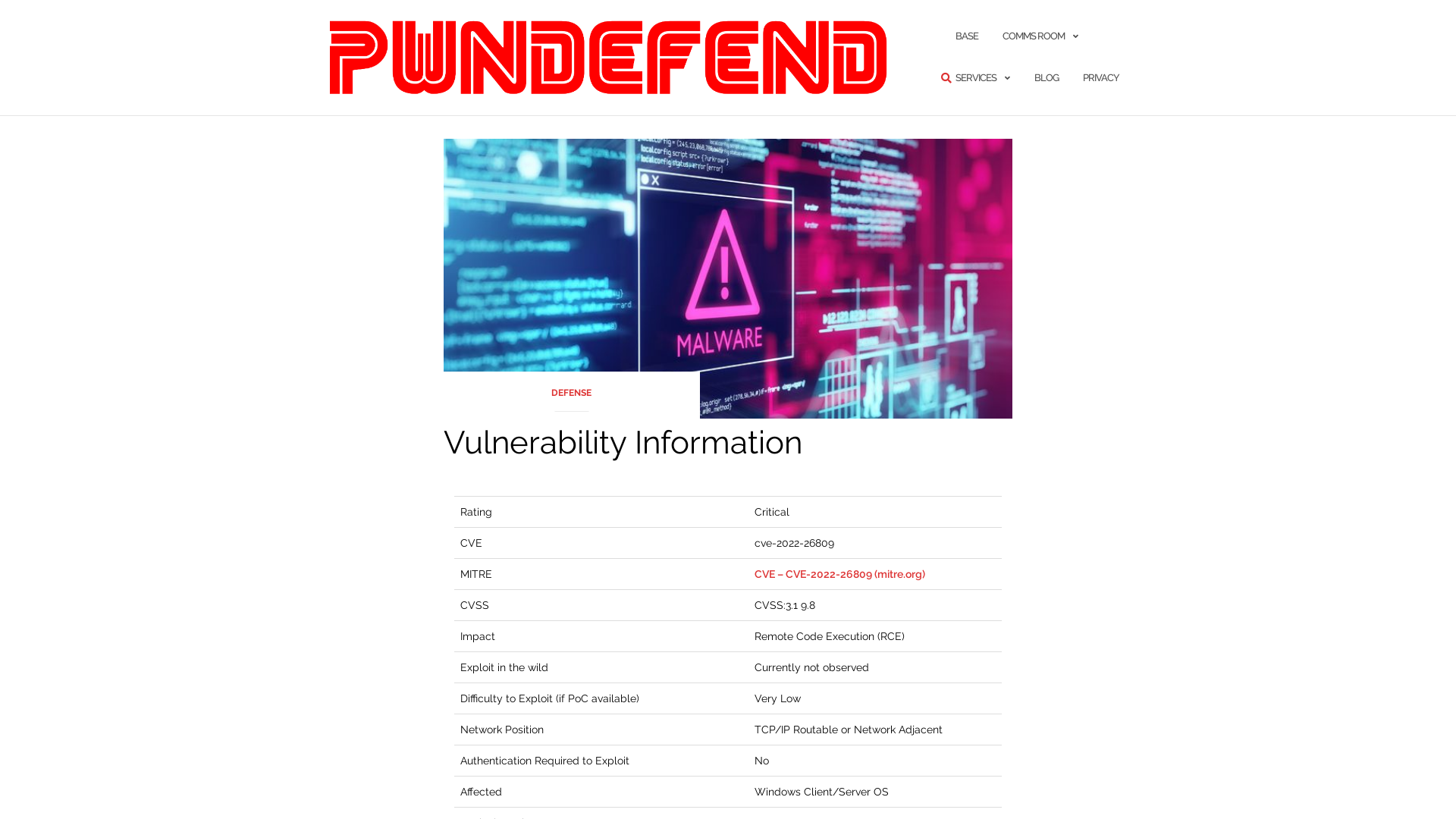
APT Cyber Tools Targeting ICS/SCADA Devices | CISA
https://www.cisa.gov/uscert/ncas/alerts/aa22-103a
Tarrask malware uses scheduled tasks for defense evasion - Microsoft Security Blog
https://www.microsoft.com/security/blog/2022/04/12/tarrask-malware-uses-scheduled-tasks-for-defense-evasion/
STÖK ✌️ on Twitter: "YES! WE are back again on Thursday 14/4 16:00 CET For another fresh BOUNTY THURSDAYS / ON-AIR! and this weeks topic is : CONTENT DISCOVERY! Join the fun, share your experiences, give us a MAD FLEX and get inspired by @Jhaddix and @Kuggofficial 💪 https://t.co/8WJZBH5YqH https://t.co/YWMsBmKE9z" / Twitter
https://twitter.com/stokfredrik/status/1513896734728073222
Microsoft Disrupts ZLoader Cybercrime Botnet in Global Operation
https://thehackernews.com/2022/04/microsoft-disrupts-zloader-cybercrime.html
Ned Pyle on Twitter: "CVE-2022-26809 has nothing to do with SMB, it's an RPC vuln where a variety of transports can be used, like TCP/135, SMB/445, etc. But I want to use this opportunity to talk about good techniques to stop an attacker from abusing SMB & the future of SMB security 🧵 /1" / Twitter
https://twitter.com/nerdpyle/status/1514633465462870020
Writing a Mutation Engine and breaking Aimware // Back Engineering
https://back.engineering/13/04/2022/
Army Combat Fitness Test
https://go.usa.gov/xugkU
Chainalysis on Twitter: "THREAD: Updates to OFAC’s SDN designation for Lazarus Group confirm that the North Korean cybercriminal group was behind the March hack of Ronin Bridge, in which over $600 million worth of ETH and USDC was stolen." / Twitter
https://twitter.com/chainalysis/status/1514645221027594245
Putin’s cyber blind spot
https://gru.gq/2022/04/14/putins-cyber-blind-spot/
Diving Deeper into WatchGuard Pre-Auth RCE - CVE-2022-26318 – Assetnote
https://blog.assetnote.io/2022/04/13/watchguard-firebox-rce/
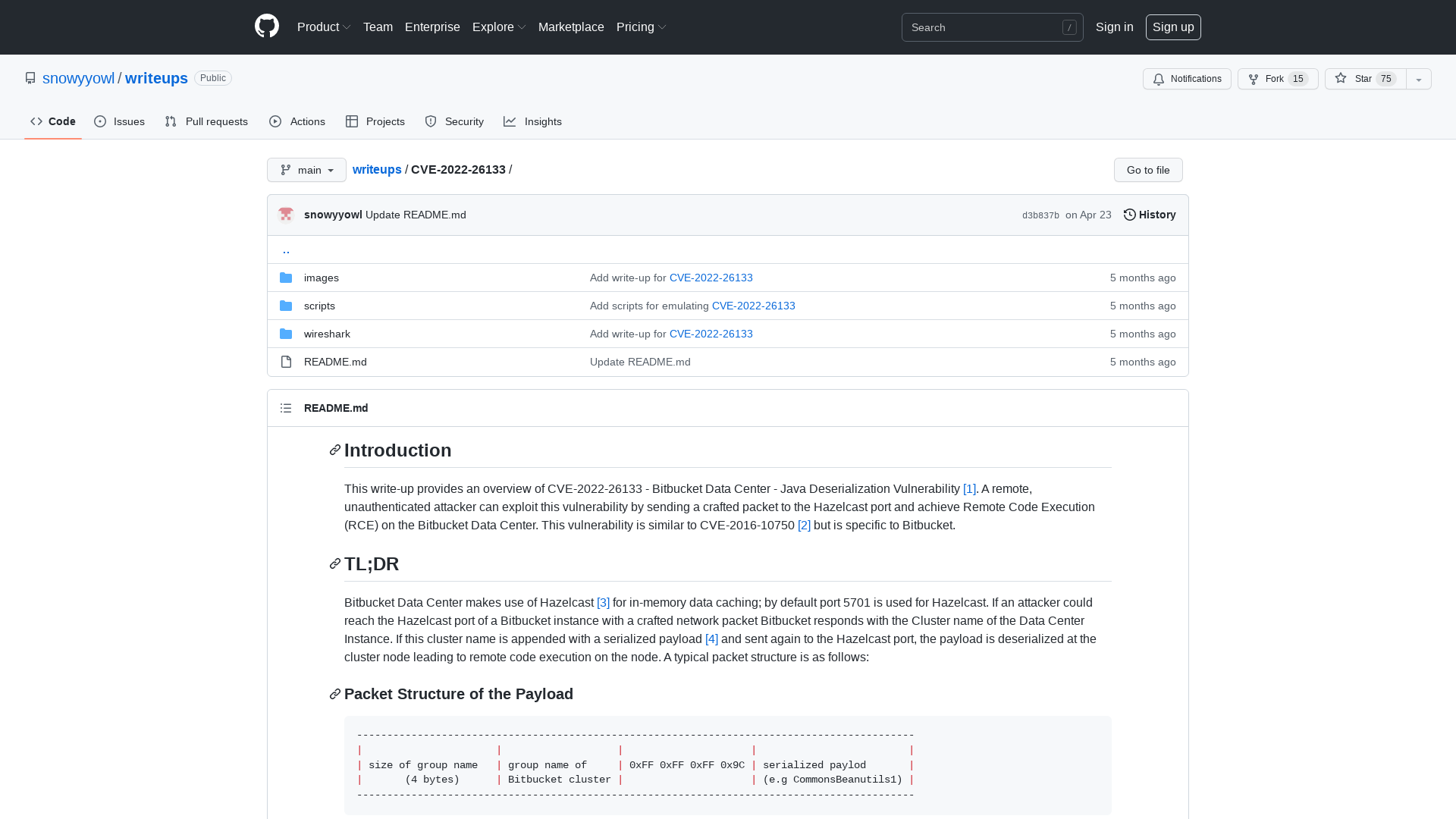
writeups/CVE-2022-26133 at main · snowyyowl/writeups · GitHub
https://github.com/snowyyowl/writeups/tree/main/CVE-2022-26133