DEV-0537 criminal actor targeting organizations for data exfiltration and destruction - Microsoft Security Blog
https://www.microsoft.com/security/blog/2022/03/22/dev-0537-criminal-actor-targeting-organizations-for-data-exfiltration-and-destruction/
Updated Okta Statement on LAPSUS$ | Okta
https://www.okta.com/blog/2022/03/updated-okta-statement-on-lapsus/
Infosecurity Magazine Cybersecurity Online Summit - 23rd March, 2022
https://bit.ly/3wtR8JM
Microsoft and Okta Confirm Breach by LAPSUS$ Extortion Group
https://thehackernews.com/2022/03/microsoft-and-okta-confirm-breach-by.html
Cryptolaemus on Twitter: "#Emotet 🚨Update 🚨 At approximately 1400UTC E4 has started to drop #Qakbot botnet ID azd which is a first since Emotet has come back. So far only E4 has been seen dropping Qakbot but it would not surprise me if we saw additional drops on E5. Several bots have received this 1/x" / Twitter
https://twitter.com/Cryptolaemus1/status/1506647250927300611
Windows Event Log Evasion via Native APIs
https://bit.ly/3D7KI4n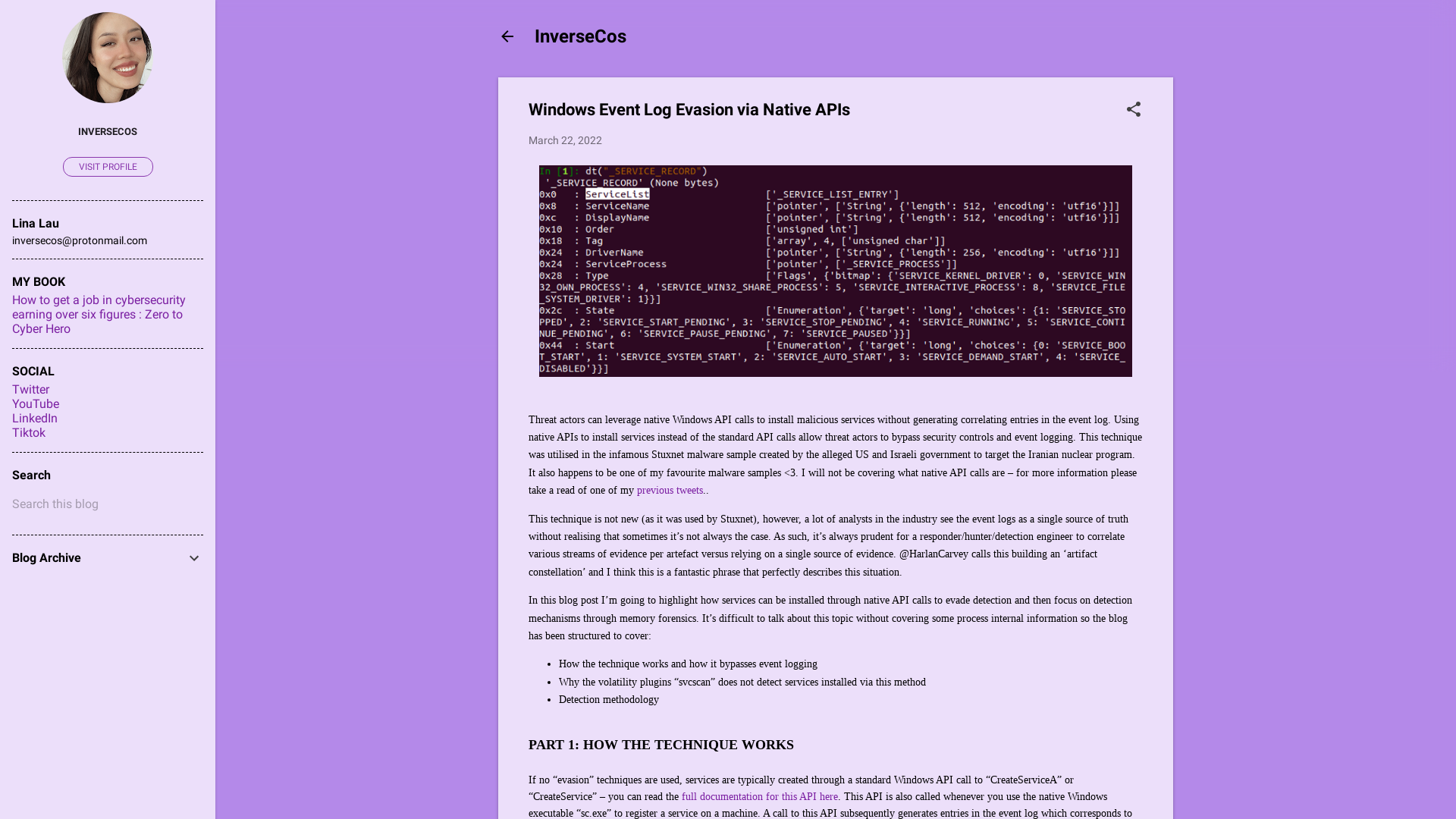
Mustang Panda’s Hodur: Old tricks, new Korplug variant | WeLiveSecurity
https://www.welivesecurity.com/2022/03/23/mustang-panda-hodur-old-tricks-new-korplug-variant/
Not So Lazarus: Mapping DPRK Cyber Threat Groups to Government Organizations | Mandiant
https://www.mandiant.com/resources/mapping-dprk-groups-to-government
Microsoft confirms they were hacked by Lapsus$ extortion group
https://www.bleepingcomputer.com/news/microsoft/microsoft-confirms-they-were-hacked-by-lapsus-extortion-group/
A Closer Look at the LAPSUS$ Data Extortion Group – Krebs on Security
https://krebsonsecurity.com/2022/03/a-closer-look-at-the-lapsus-data-extortion-group/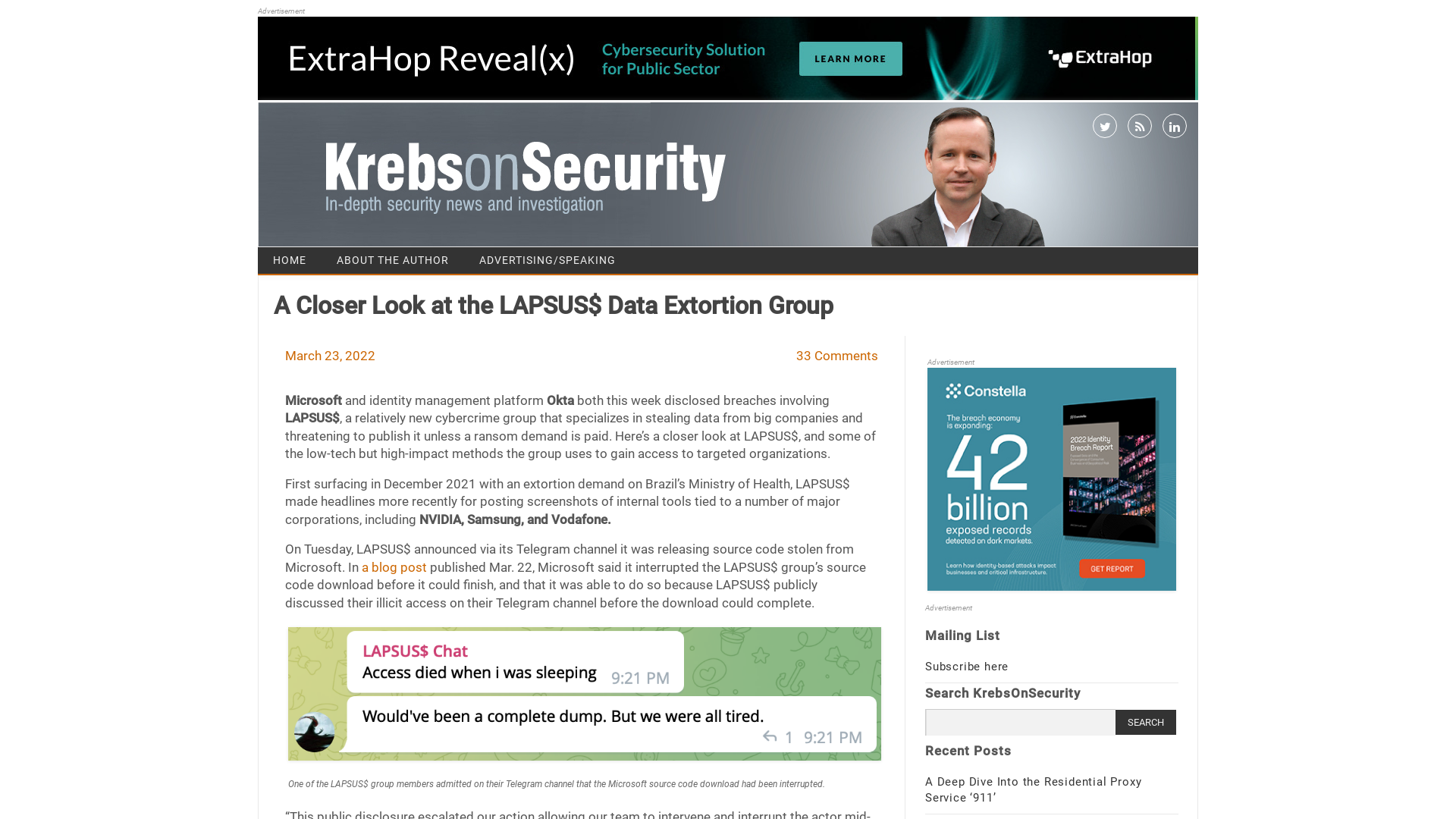
Cloudflare’s investigation of the January 2022 Okta compromise
https://blog.cloudflare.com/cloudflare-investigation-of-the-january-2022-okta-compromise/
Resources for Retired Events Links | 6Connex Event Tech
https://securityweek.6connex.com/event/SecuritySummit/en-us#!/Auditorium/n1418636
Okta’s Investigation of the January 2022 Compromise | Okta
https://www.okta.com/blog/2022/03/oktas-investigation-of-the-january-2022-compromise/
GOLD ULRICK leaks reveal organizational structure and relationships | Secureworks
https://www.secureworks.com/blog/gold-ulrick-leaks-reveal-organizational-structure-and-relationships
CVE-2021-22555: Turning \x00\x00 into 10000$ | security-research
https://google.github.io/security-research/pocs/linux/cve-2021-22555/writeup.html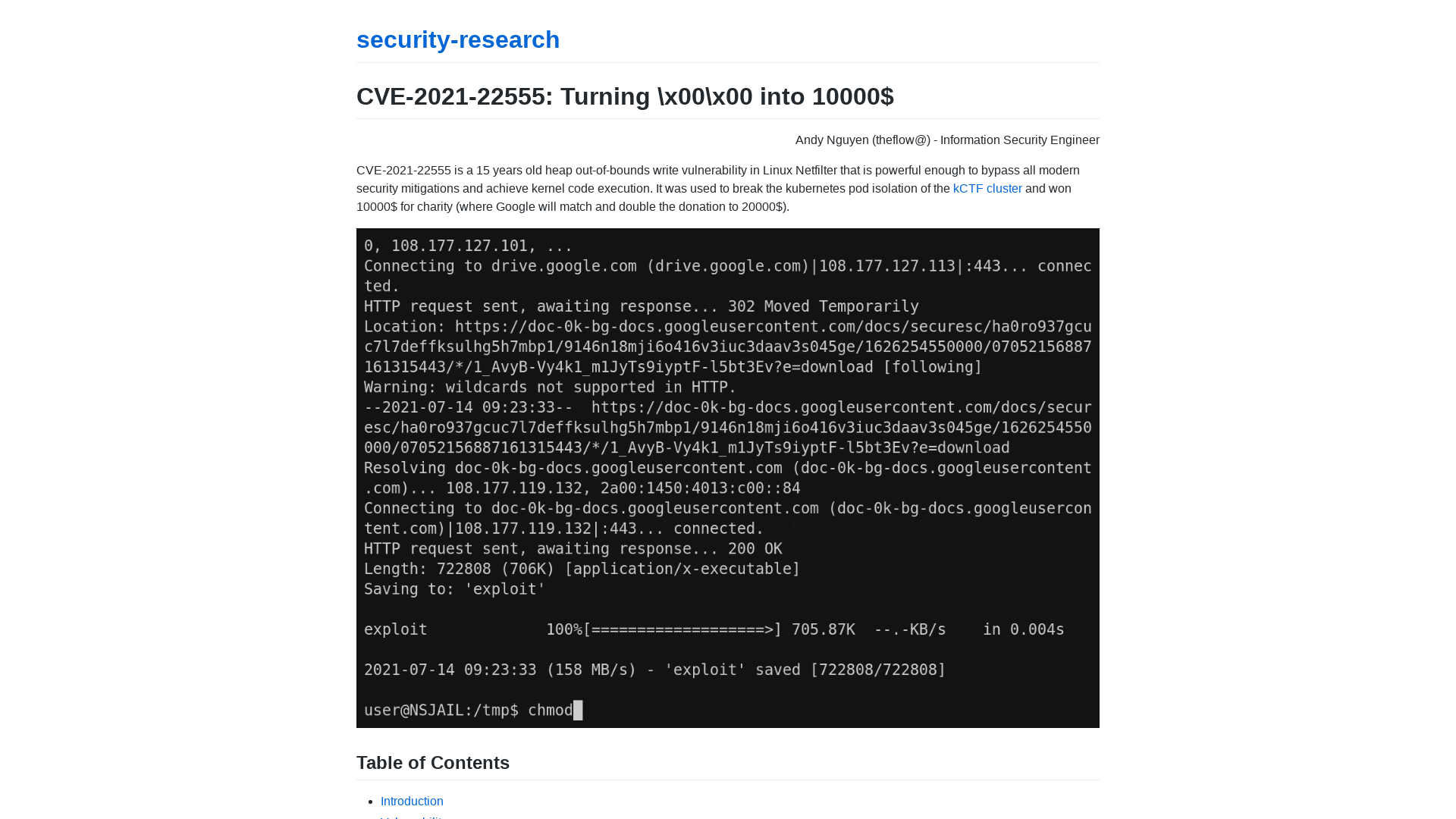
Operation Dragon Castling: APT group targeting betting companies - Avast Threat Labs
https://decoded.avast.io/luigicamastra/operation-dragon-castling-apt-group-targeting-betting-companies/
2244 - containerd: Insecure handling of image volumes - project-zero
https://bugs.chromium.org/p/project-zero/issues/detail?id=2244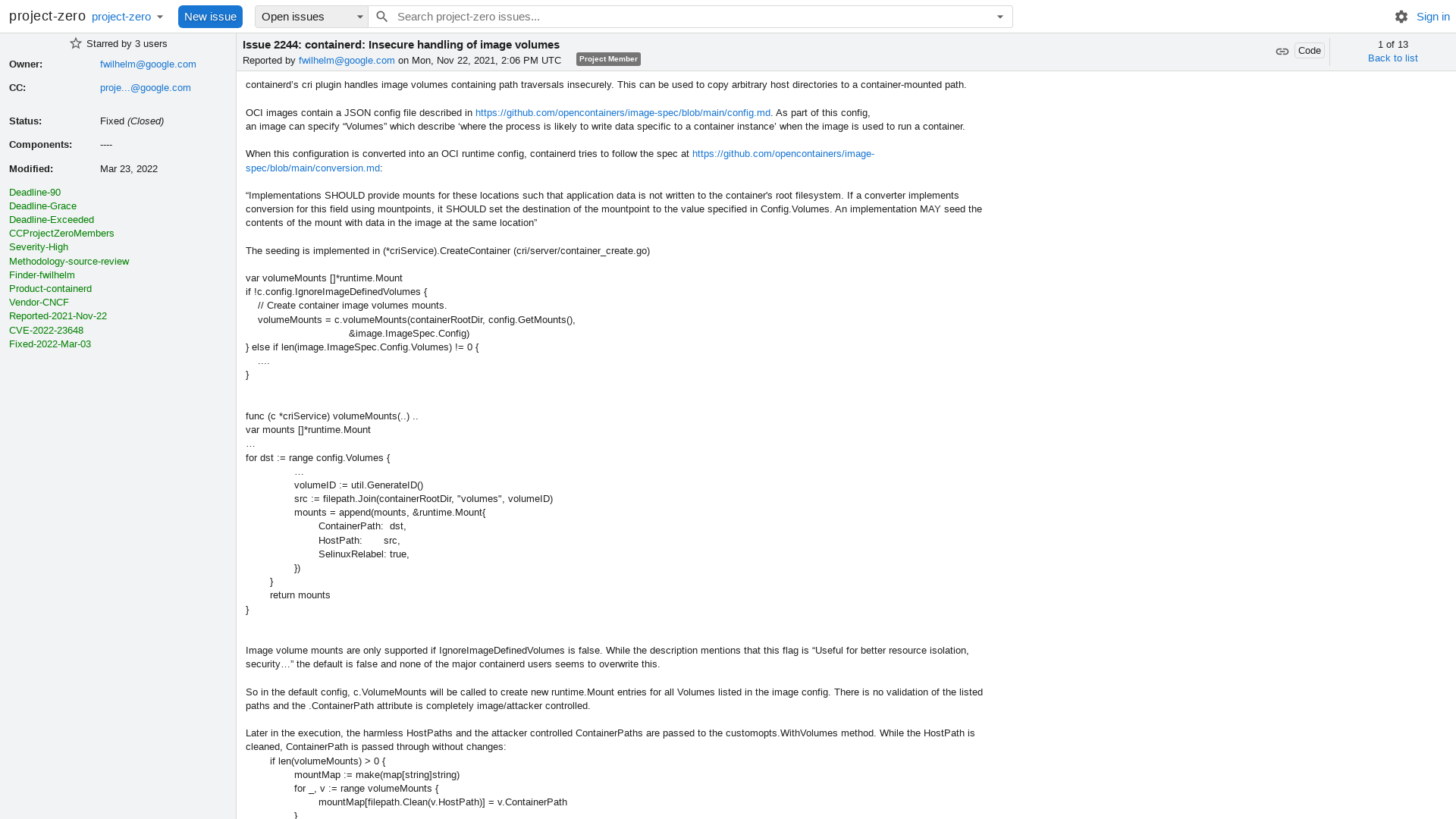
Tweet / Twitter
https://twitter.com/williamturton/status/1506739931456155648
New Variant of Chinese Gimmick Malware Targeting macOS Users
https://thehackernews.com/2022/03/new-variant-of-chinese-gimmick-malware.html
Bloomberg - Are you a robot?
https://www.bloomberg.com/news/articles/2022-03-23/teen-suspected-by-cyber-researchers-of-being-lapsus-mastermind?sref=ylv224K8
Azure Dominance Paths - Cloudbrothers
https://cloudbrothers.info/en/azure-dominance-paths/
Botnet of Thousands of MikroTik Routers Abused in Glupteba, TrickBot Campaigns
https://thehackernews.com/2022/03/over-200000-microtik-routers-worldwide.html
Malware-IOCs/2022-03-23_CobaltStrike_C2 at main · CronUp/Malware-IOCs · GitHub
https://github.com/CronUp/Malware-IOCs/blob/main/2022-03-23_CobaltStrike_C2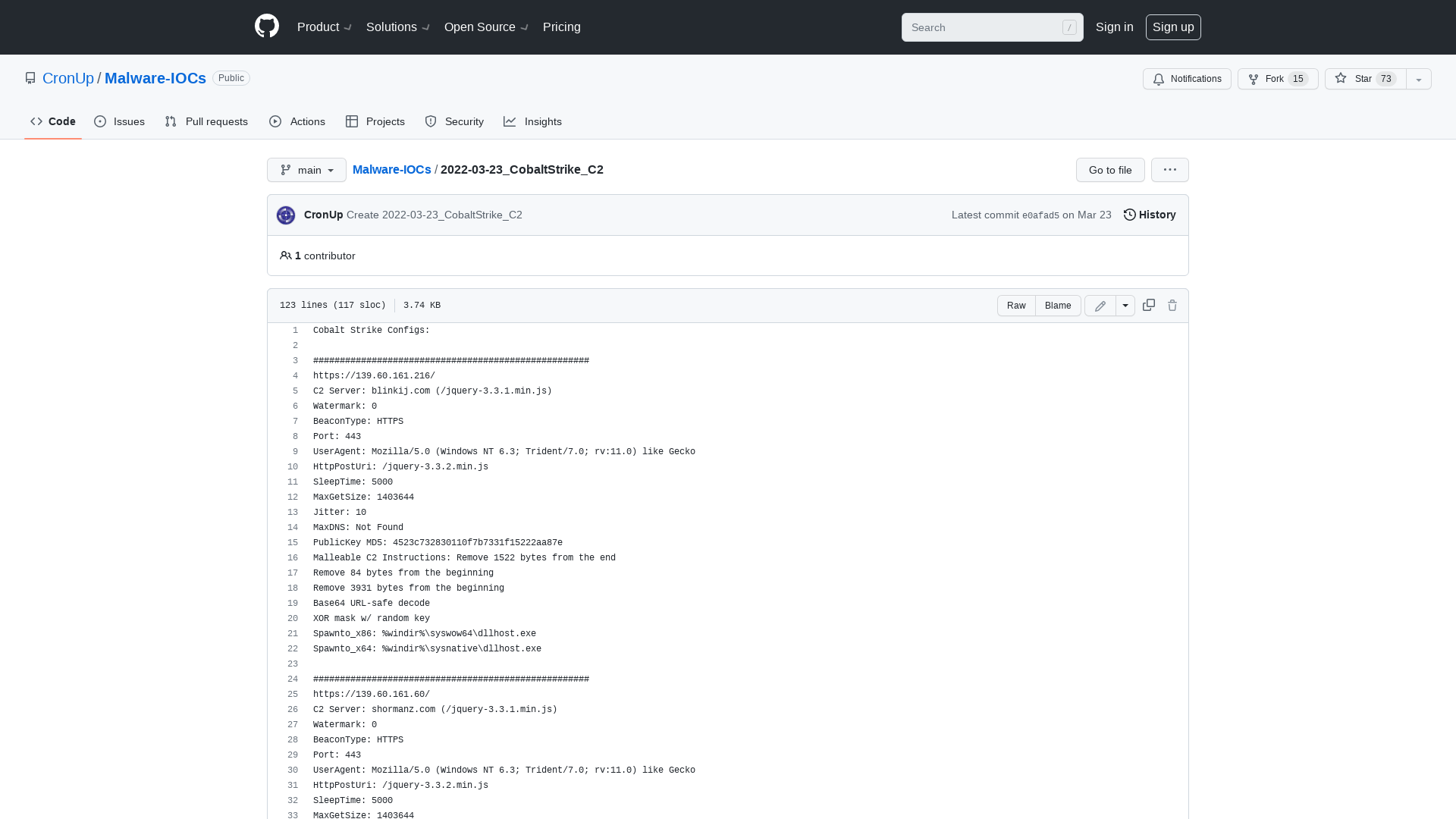
Triage | Malware sandboxing report by Hatching Triage
https://tria.ge/220323-rwqb3acabl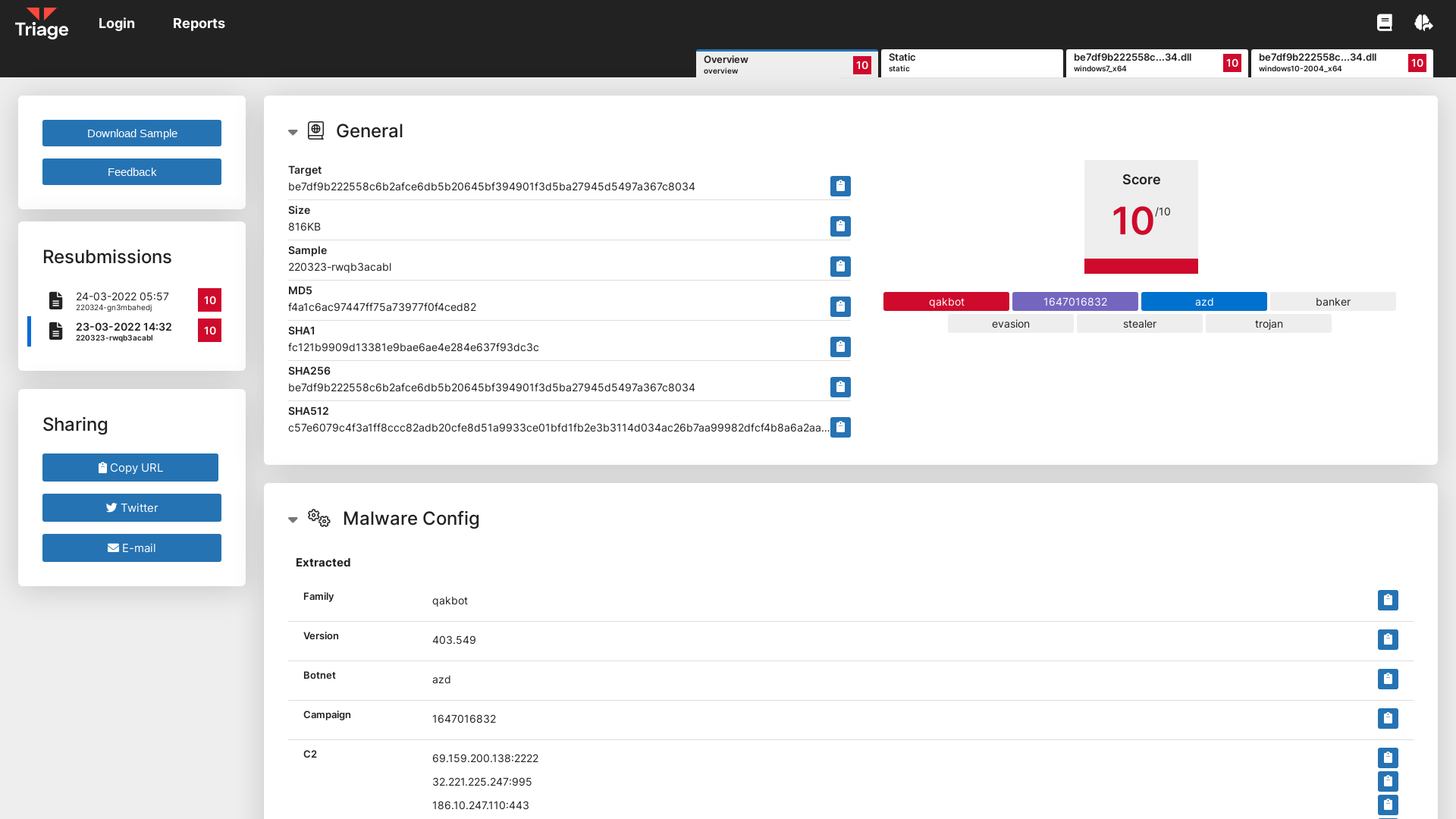
360°Radar on Twitter: "The advanced Russian electronic warfare system Krasucha-4, captured on the battlefield in Ukraine, will be transported to the United States for investigation, the British Daily Telegraph reported. https://t.co/kddN01agYw" / Twitter
https://twitter.com/wipljw/status/1506673602015473670
MalwareBazaar | SHA256 e93cc14c93709b38dc8d95fb58d70d1a8930576c7d16c64c3efbc4cc08d951ff (AZORult)
https://bazaar.abuse.ch/sample/e93cc14c93709b38dc8d95fb58d70d1a8930576c7d16c64c3efbc4cc08d951ff/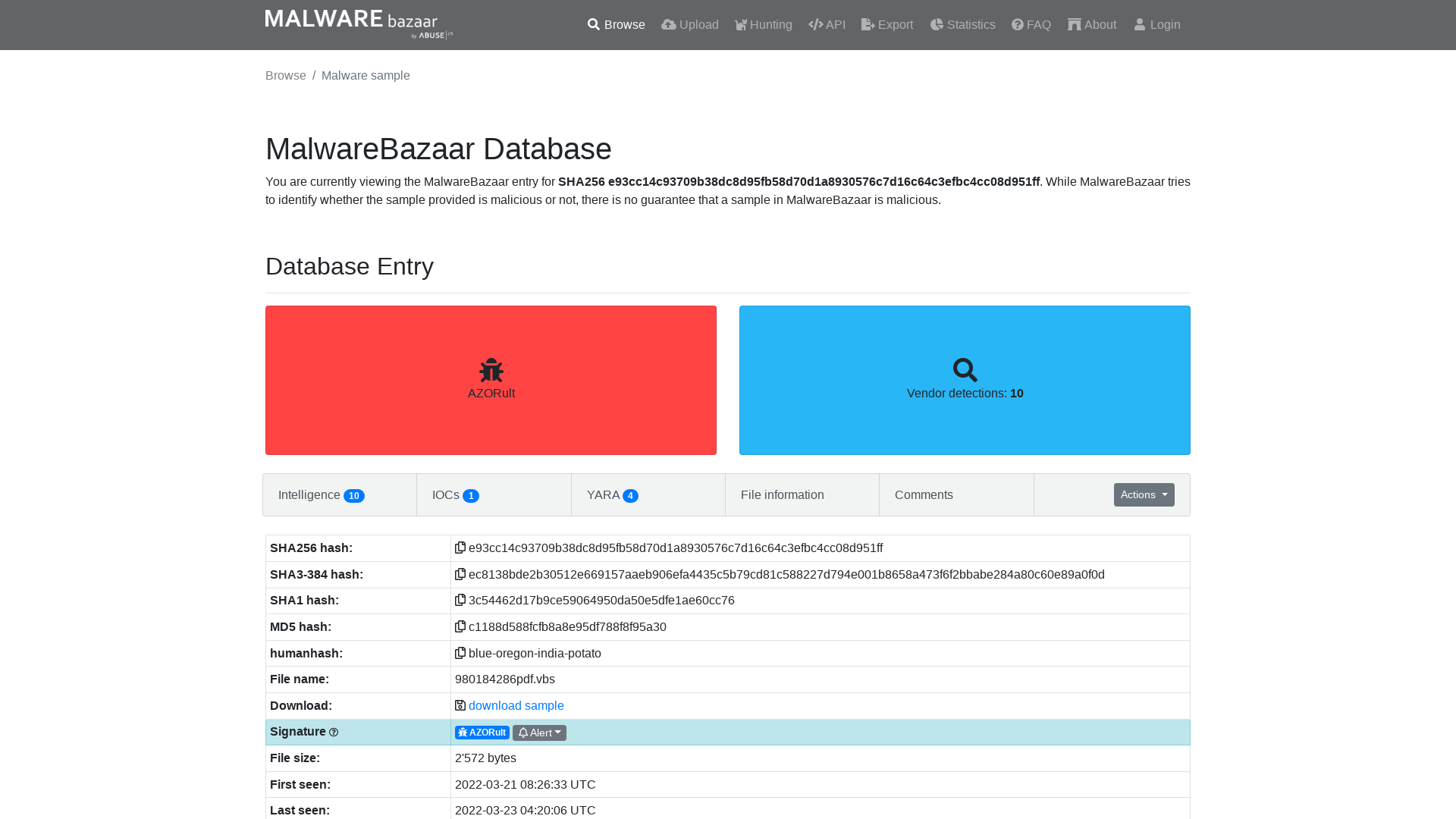
briankrebs on Twitter: "Experts say the LAPSUS$ data extortion group that hit Okta and Microsoft this week is run by a 17-year-old from the UK who recently bought the Doxbin doxing website, and then leaked its database. Naturally, Doxbin responded by doxing the LAPSUS$ leader. https://t.co/bJ2V4Xy74S" / Twitter
https://twitter.com/briankrebs/status/1506754458008670209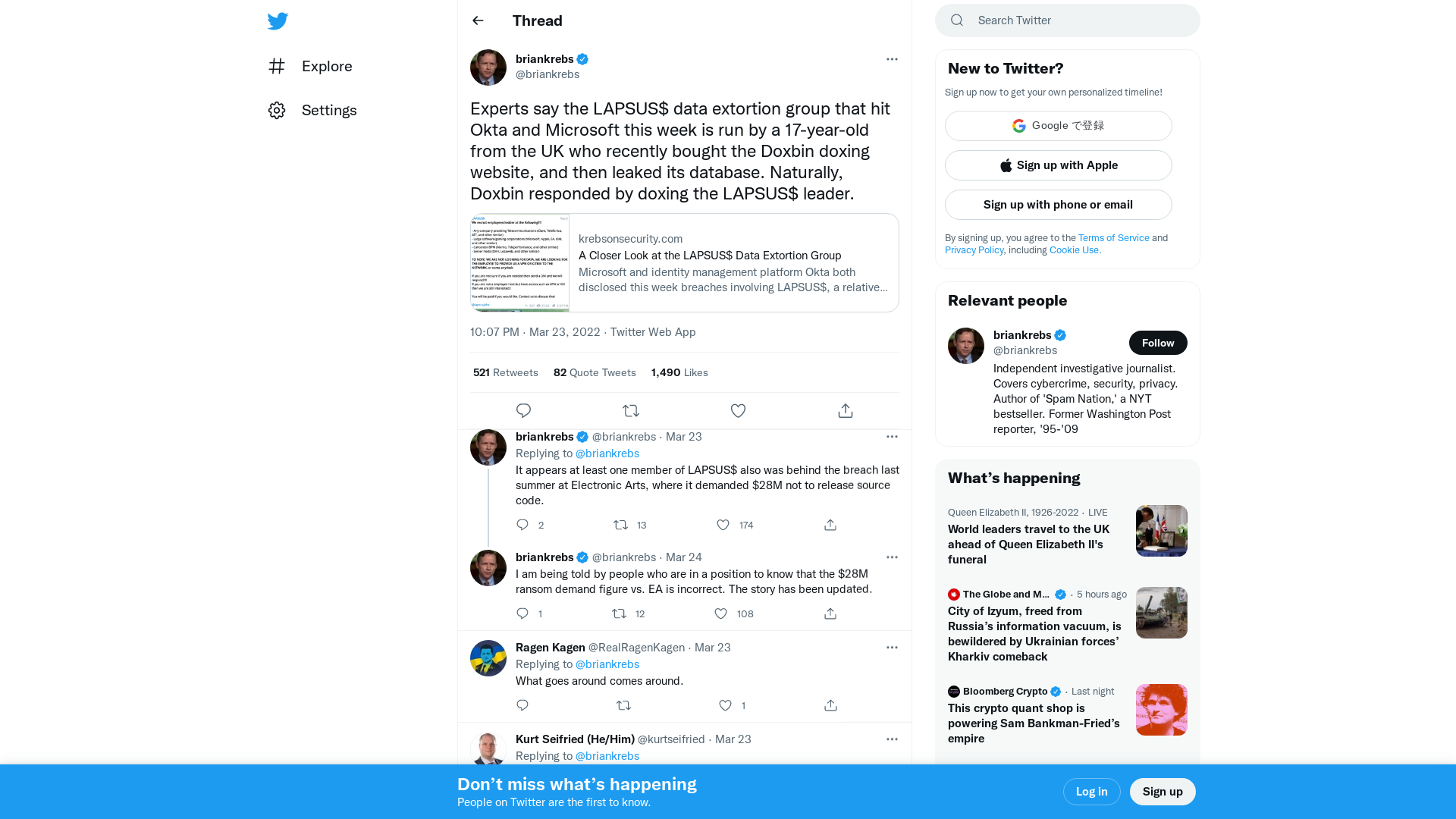
https://feodotracker.abuse.ch/downloads/ipblocklist_recommended.txt
https://feodotracker.abuse.ch/downloads/ipblocklist_recommended.txt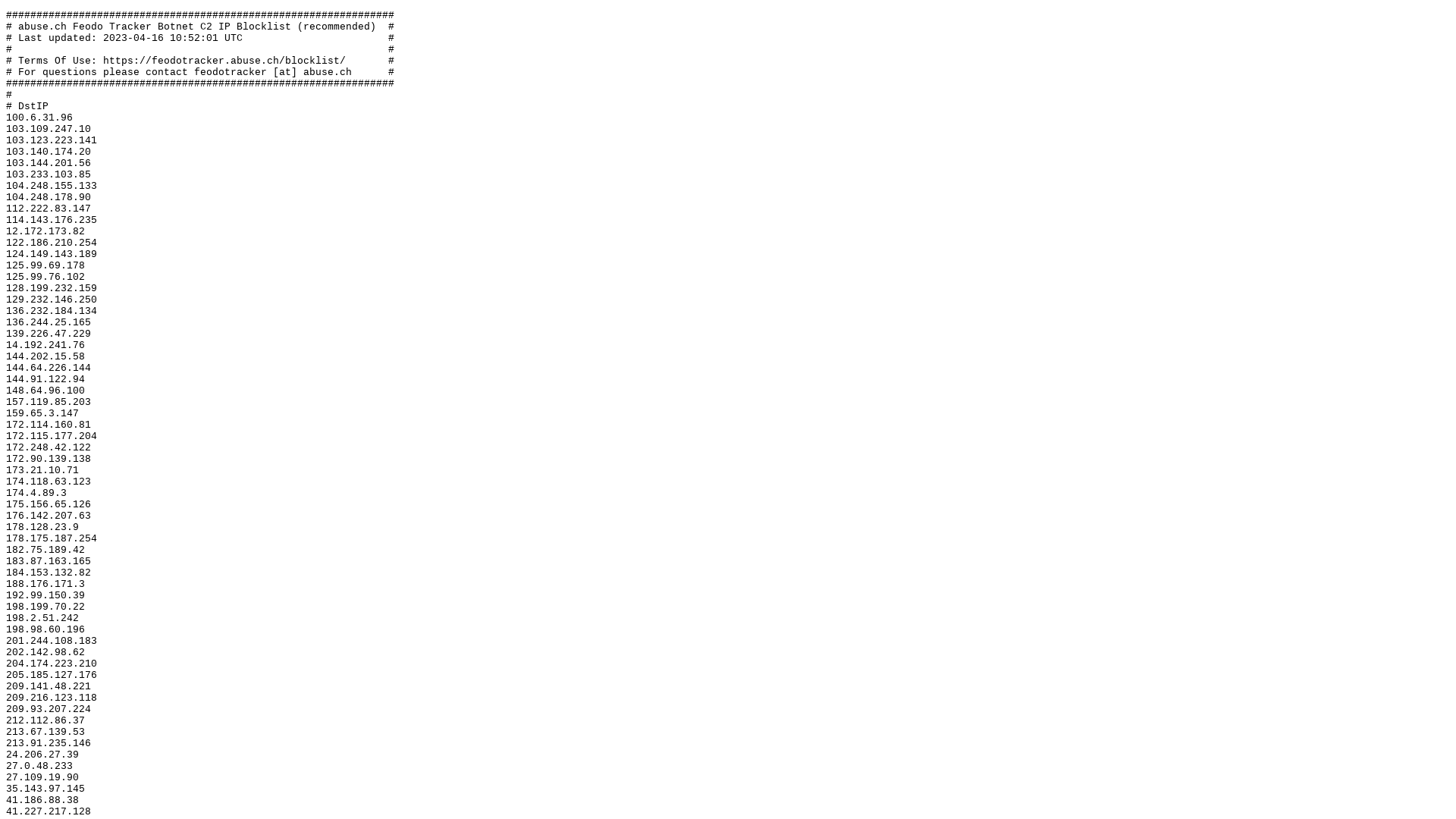
Raccoon Stealer – An Insight into Victim “Gates”
https://team-cymru.com/blog/2022/03/23/raccoon-stealer-an-insight-into-victim-gates/
IOCs/2022-03-23-AA-Qakbot-data-dump.zip at main · brad-duncan/IOCs · GitHub
https://github.com/brad-duncan/IOCs/blob/main/2022-03-23-AA-Qakbot-data-dump.zip
CISA Call with Critical Infrastructure Partners on Potential Russian Cyberattacks Against the U.S. - YouTube
https://www.youtube.com/watch?v=q-vnMmQHASY
https://gist.githubusercontent.com/plutooo/2aadbd4a718e269df474079dd2e584fb/raw/7b3af77b5202366c8934c88ef251f1e905967040/gistfile1.txt
https://gist.githubusercontent.com/plutooo/2aadbd4a718e269df474079dd2e584fb/raw/7b3af77b5202366c8934c88ef251f1e905967040/gistfile1.txt
What the Pack(er)? – cyber.wtf
https://cyber.wtf/2022/03/23/what-the-packer/