Ciaran Martin on Twitter: "Cyber & the war. My thoughts in @lawfareblog on: - unexpectedly low cyber activity so far; - high ongoing risk of cyber harassment & disruption against Ukraine & the west; - the limitations of cyber power; - implications for Western cyber posture. https://t.co/4uFyiDbro0" / Twitter
https://twitter.com/ciaranmartinoxf/status/1499010226934136833
Conti Ransomware Group Diaries, Part I: Evasion – Krebs on Security
https://krebsonsecurity.com/2022/03/conti-ransomware-group-diaries-part-i-evasion/
Cyber Realism in a Time of War - Lawfare
https://www.lawfareblog.com/cyber-realism-time-war
IsaacWiper and HermeticWizard: New wiper and worm targeting Ukraine | WeLiveSecurity
https://www.welivesecurity.com/2022/03/01/isaacwiper-hermeticwizard-wiper-worm-targeting-ukraine/
No need to declare captured Russian tanks, other equipment of invaders as income – NAPC
https://en.interfax.com.ua/news/general/804441.html
add PPL bypass · helpsystems/nanodump@9f52024 · GitHub
https://github.com/helpsystems/nanodump/commit/9f5202462168b109a57accc2781000f9f141887b
Malware-IOCs/2022-03-01_CobaltStrikeConfigs at main · CronUp/Malware-IOCs · GitHub
https://github.com/CronUp/Malware-IOCs/blob/main/2022-03-01_CobaltStrikeConfigs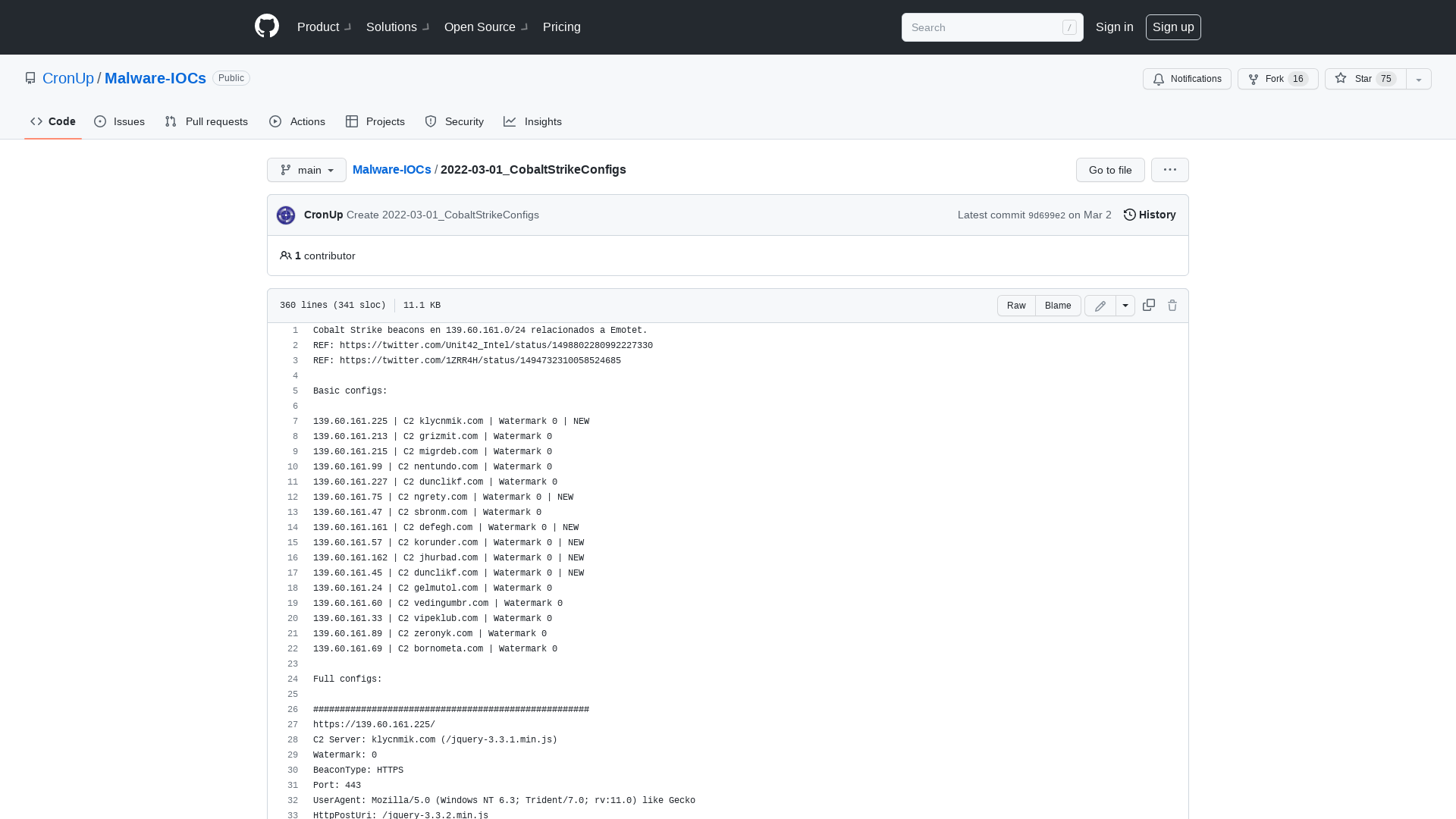
Asylum Ambuscade: State Actor Uses Compromised Private Ukrainian Military Emails to Target European Governments and Refugee Movement | Proofpoint US
https://www.proofpoint.com/us/blog/threat-insight/asylum-ambuscade-state-actor-uses-compromised-private-ukrainian-military-emails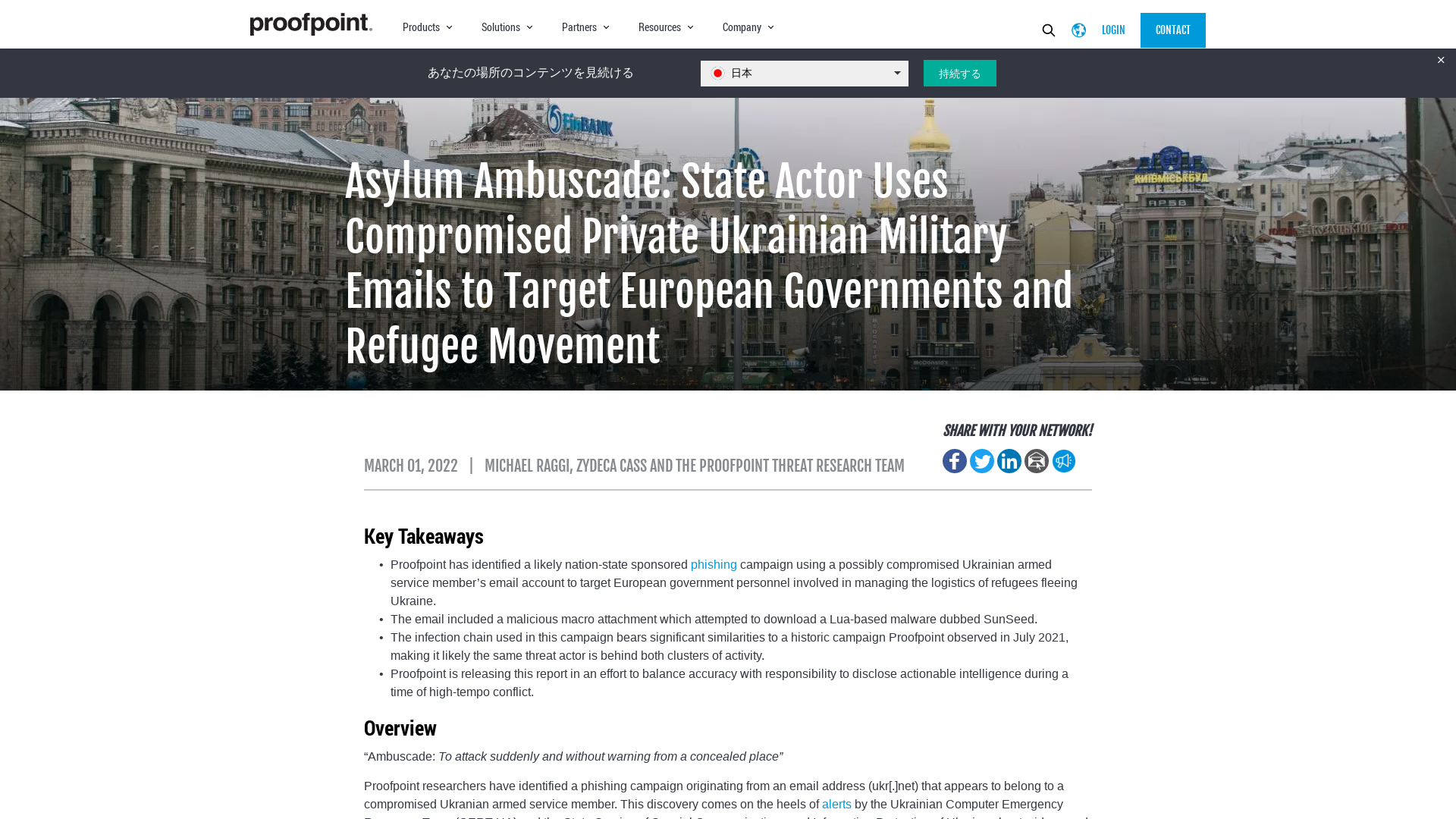
x86matthew - NTSockets - Downloading a file via HTTP using the NtCreateFile and NtDeviceIoControlFile syscalls
https://www.x86matthew.com/view_post?id=ntsockets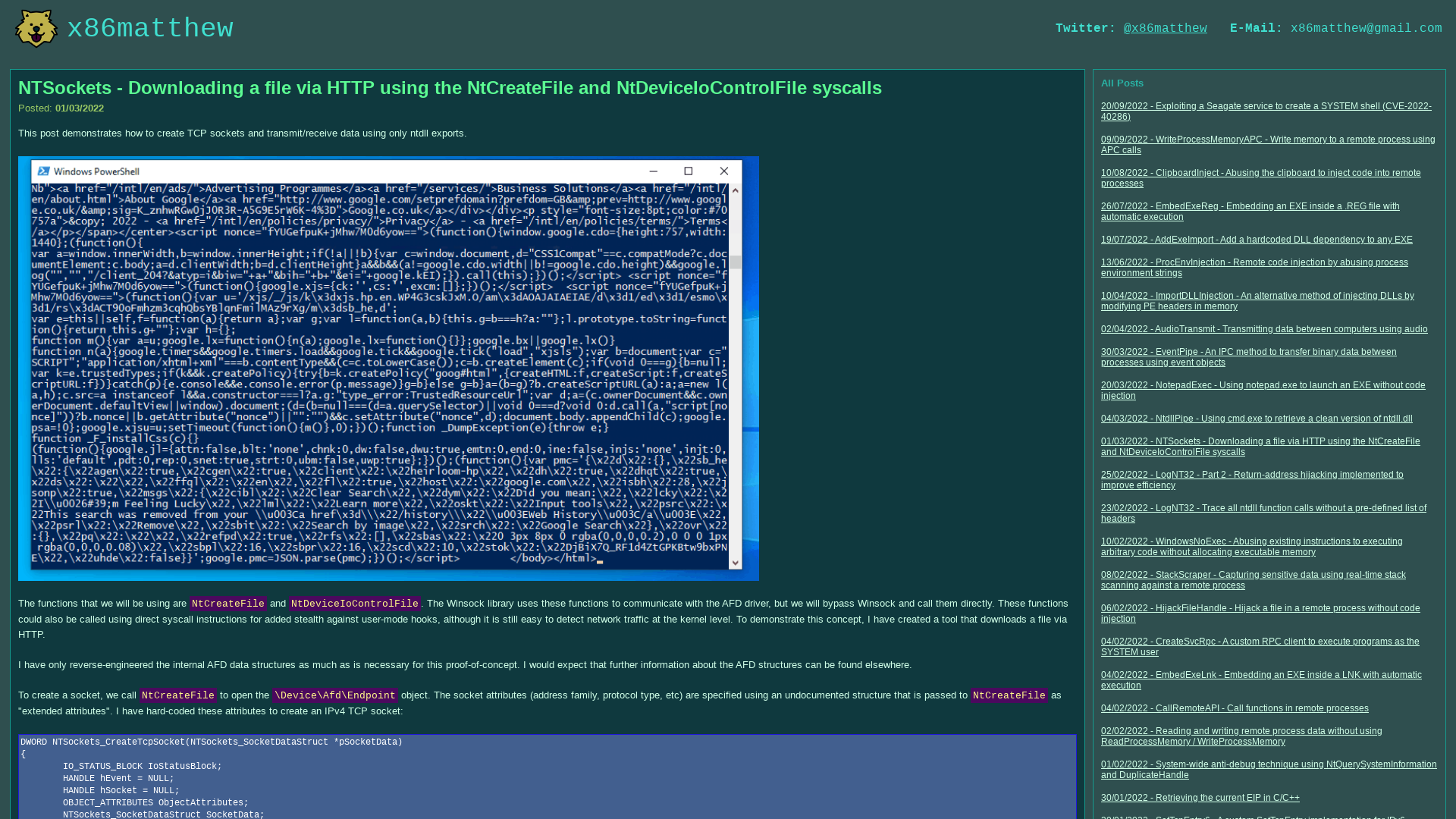
MAPPING THE CONTI NETWORK | Flourish
https://bit.ly/JGEU_CLNETMAP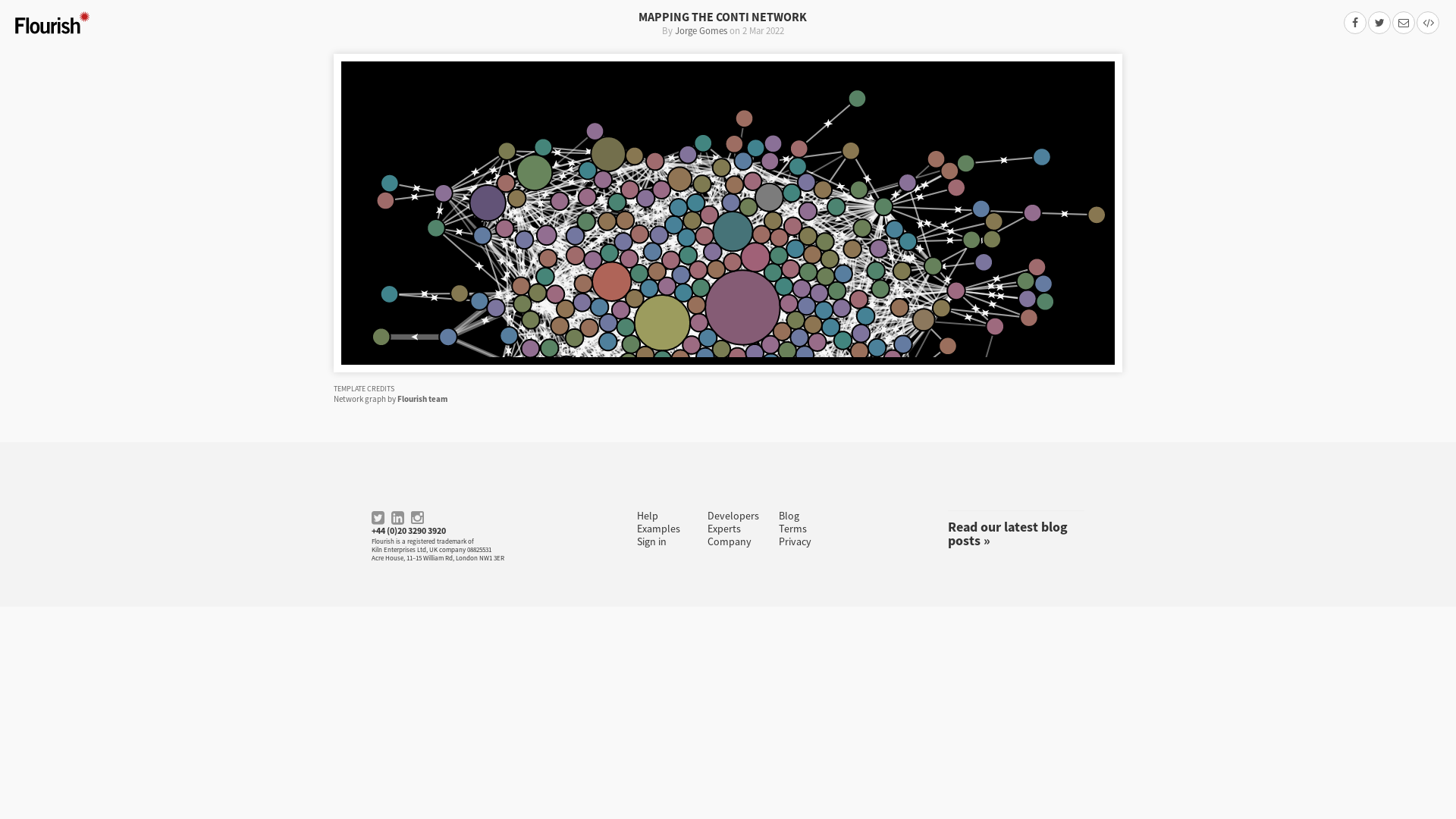
CVE-2022-22947: SpEL Casting and Evil Beans – Wya.pl
https://wya.pl/2022/02/26/cve-2022-22947-spel-casting-and-evil-beans/
Hackers Begin Weaponizing TCP Middlebox Reflection for Amplified DDoS Attacks
https://thehackernews.com/2022/03/hackers-begin-weaponizing-tcp-middlebox.html
21 Women in Cybersecurity You Need to Know – Making Space
https://www.makingspacepledge.org/21-women-in-cybersecurity-you-need-to-know/
Tweet / Twitter
https://twitter.com/WillWArmstrong/status/1498778609896415237
PR0CESS/UACBypassJF_RpcALPC at main · aaaddress1/PR0CESS · GitHub
https://github.com/aaaddress1/PR0CESS/tree/main/UACBypassJF_RpcALPC
[DarkTracer] Stealer Malware Intelligence Report - Government - Google スプレッドシート
https://bit.ly/3sA7f6s![[DarkTracer] Stealer Malware Intelligence Report - Government - Google スプレッドシート](/image/screenshot/088b6d65d5349fae93dfa4818d9e96dc.png)
Shields Up | CISA
http://cisa.gov/shields-up
Space / Twitter
https://twitter.com/i/spaces/1zqKVBWnXbZKB
2022 Russia-Ukraine war — Cyber group tracker. Update 2. - Cyberknow - Medium
https://cyberknow.medium.com/2022-russia-ukraine-war-cyber-group-tracker-update-2-e62239184510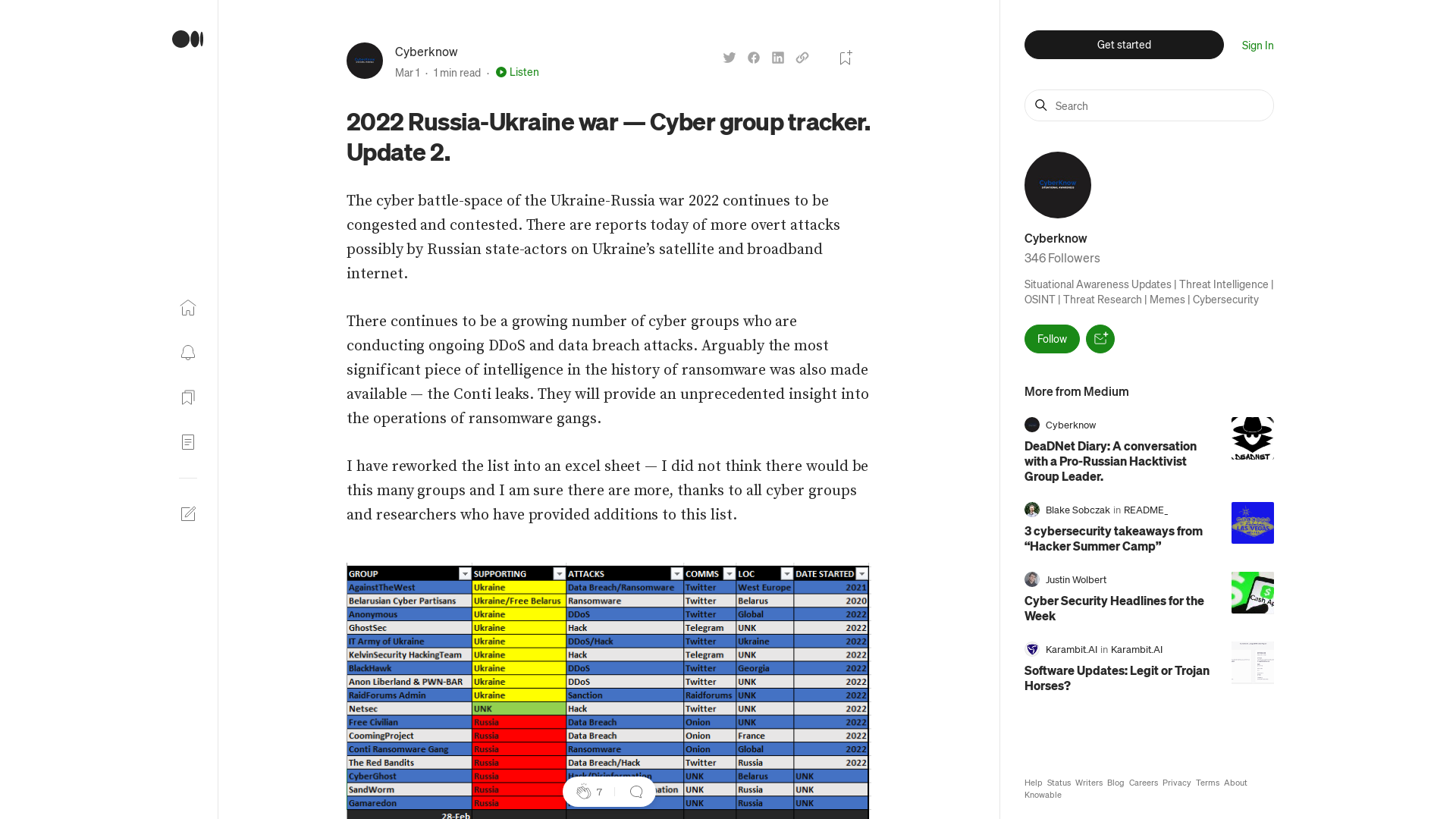
Zelensky assassination plot foiled, Ukrainian authorities say
https://www.axios.com/zelensky-assassination-plot-foiled-7bea049b-2308-4801-b75a-93104c17b82b.html?utm_source=twitter&utm_medium=social&utm_campaign=editorial&utm_content=world-russiaukraine
Example Domain
http://example.com
Log4shell exploits now used mostly for DDoS botnets, cryptominers
https://www.bleepingcomputer.com/news/security/log4shell-exploits-now-used-mostly-for-ddos-botnets-cryptominers/
Conti Ransomware source code leaked by Ukrainian researcher
https://www.bleepingcomputer.com/news/security/conti-ransomware-source-code-leaked-by-ukrainian-researcher/
Conti Ransomware Group Diaries, Part II: The Office – Krebs on Security
https://krebsonsecurity.com/2022/03/conti-ransomware-group-diaries-part-ii-the-office/
fuzzing22_fioraldi_report.pdf
https://www.s3.eurecom.fr/docs/fuzzing22_fioraldi_report.pdf
Valéry Rieß-Marchive on Twitter: "@radvadva @journalist1 @journalist2 @vxunderground @Cyberknow20 And for English ⬇️ https://t.co/BidRFoIqZU" / Twitter
https://twitter.com/ValeryMarchive/status/1499107984777035779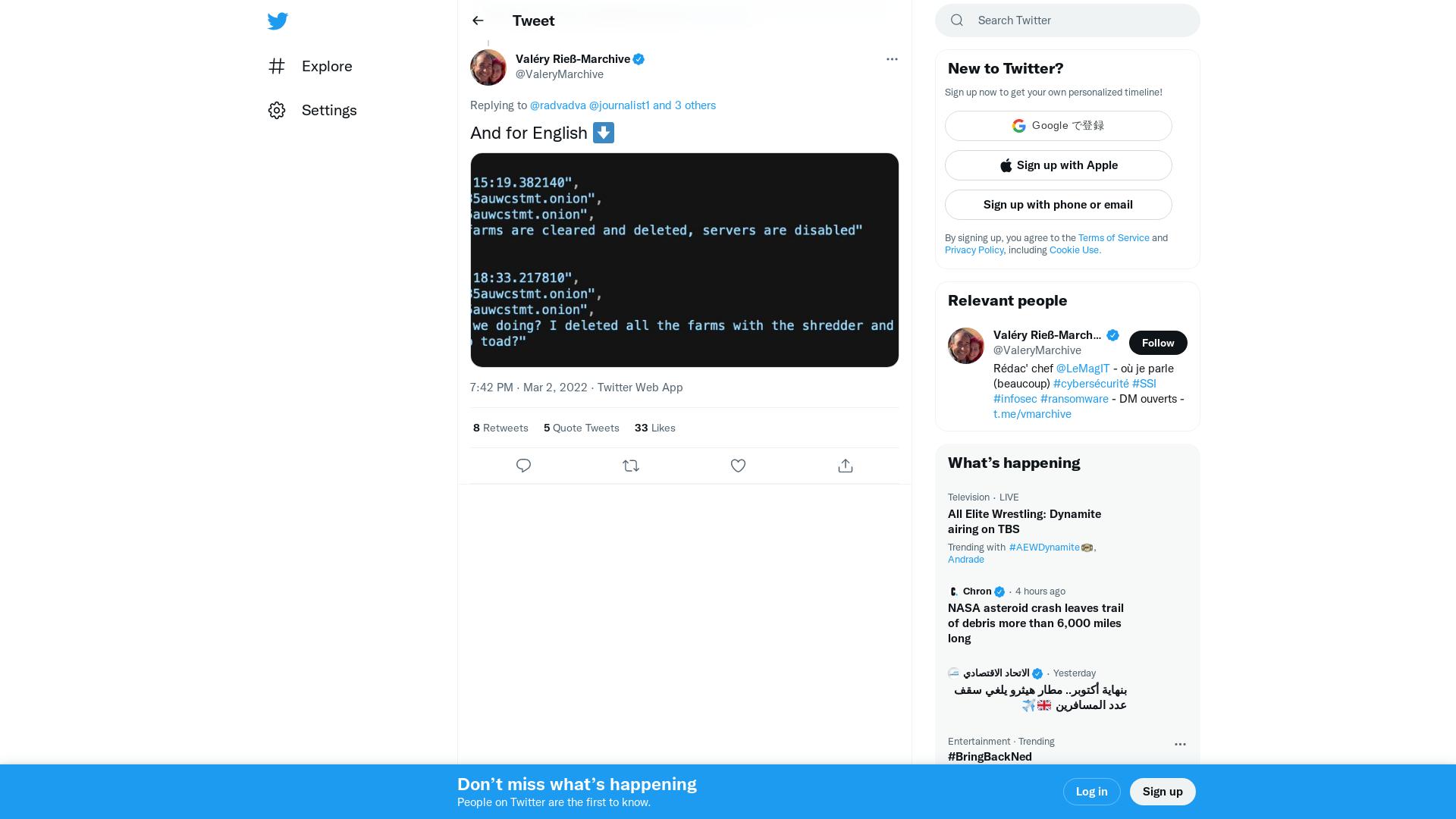
How to Decrypt the PartyTicket Ransomware Targeting Ukraine | CrowdStrike
https://www.crowdstrike.com/blog/how-to-decrypt-the-partyticket-ransomware-targeting-ukraine/