IsaacWiper and HermeticWizard: New wiper and worm targeting Ukraine | WeLiveSecurity
https://www.welivesecurity.com/2022/03/01/isaacwiper-hermeticwizard-wiper-worm-targeting-ukraine/
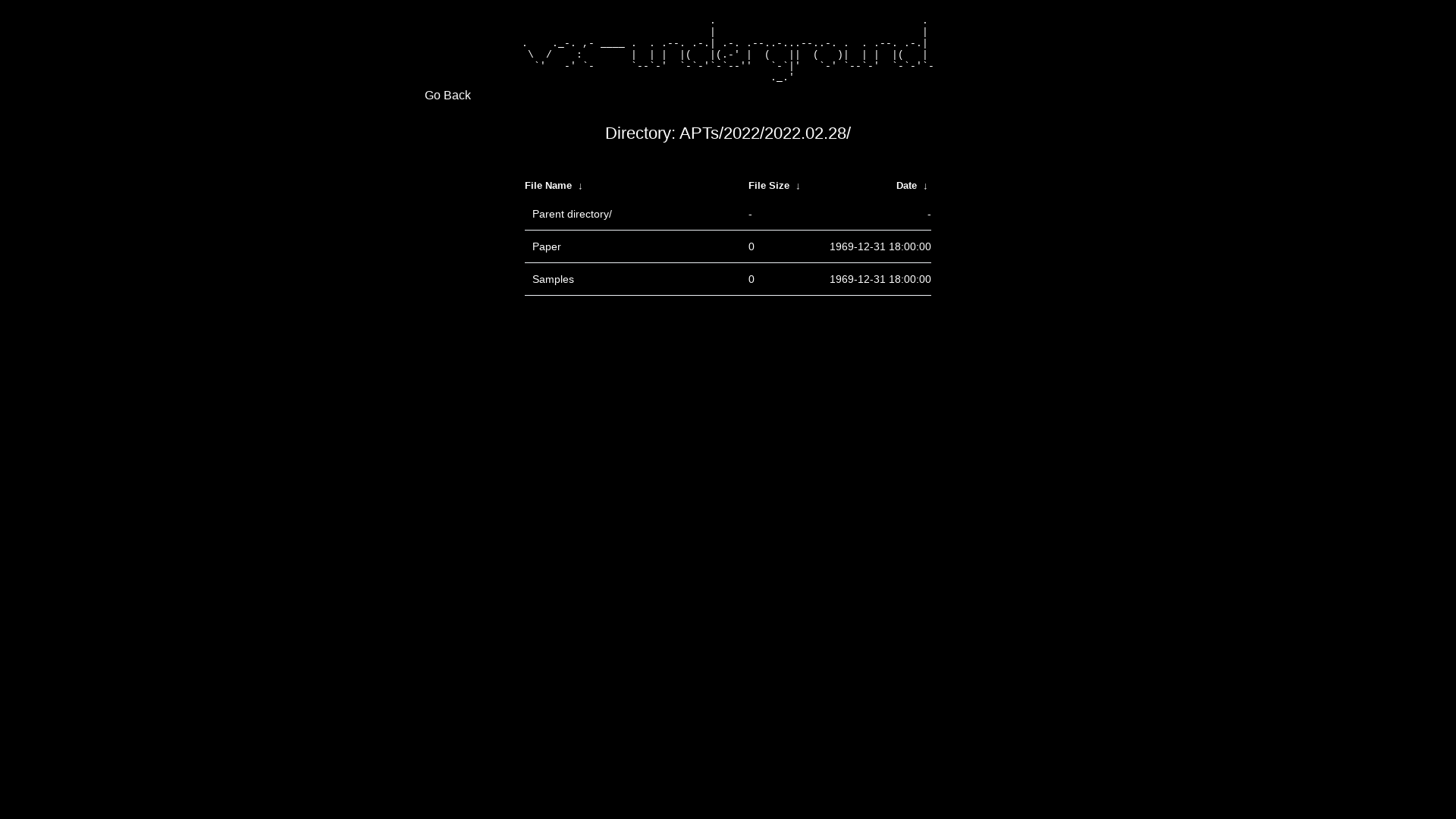
vx-underground - Directory
https://share.vx-underground.org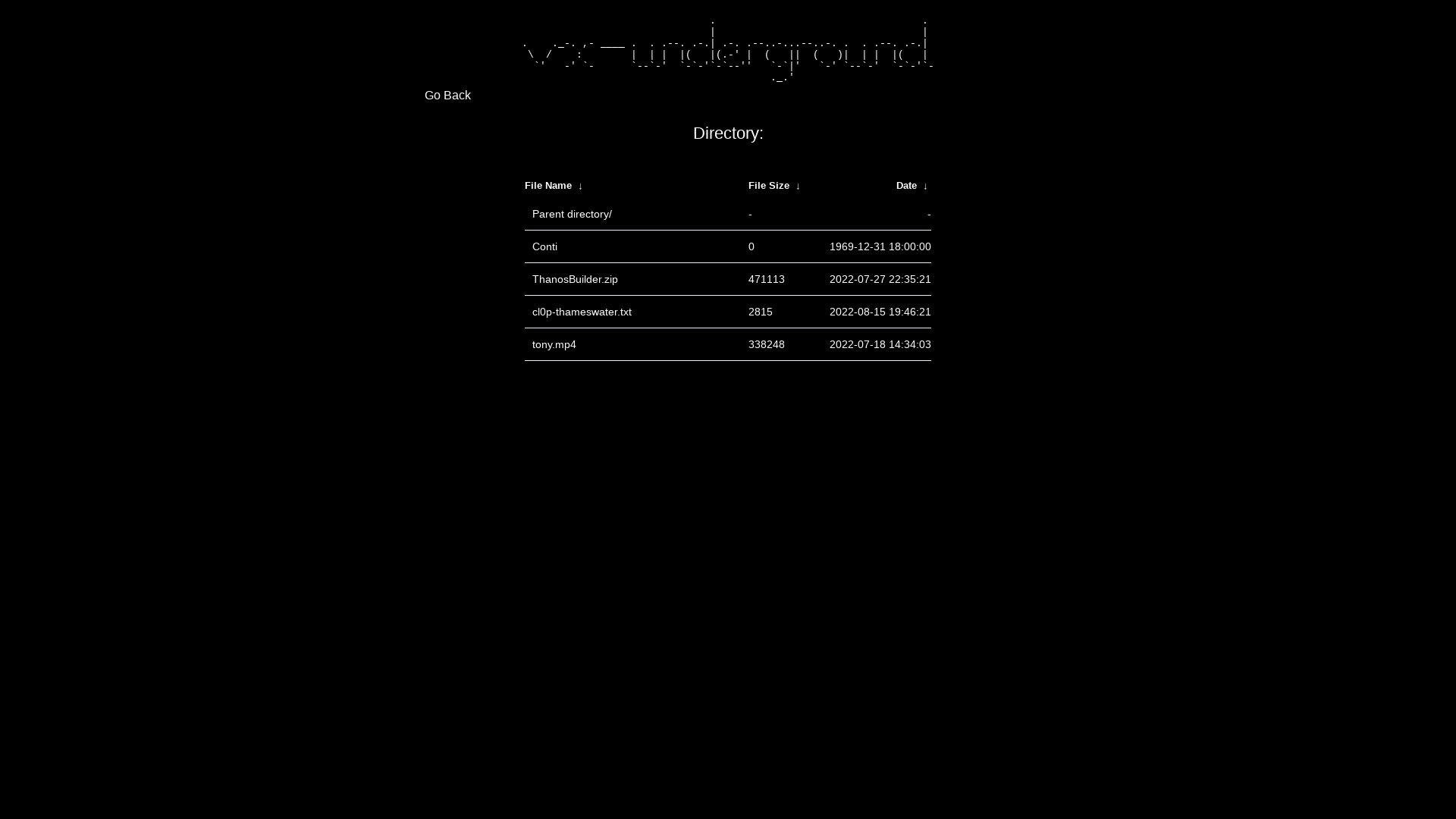
Eugene Kaspersky on Twitter: "We welcome the start of negotiations to resolve the current situation in Ukraine and hope that they will lead to a cessation of hostilities and a compromise. We believe that peaceful dialogue is the only possible instrument for resolving conflicts. War isn’t good for anyone." / Twitter
https://twitter.com/e_kaspersky/status/1498547337043525633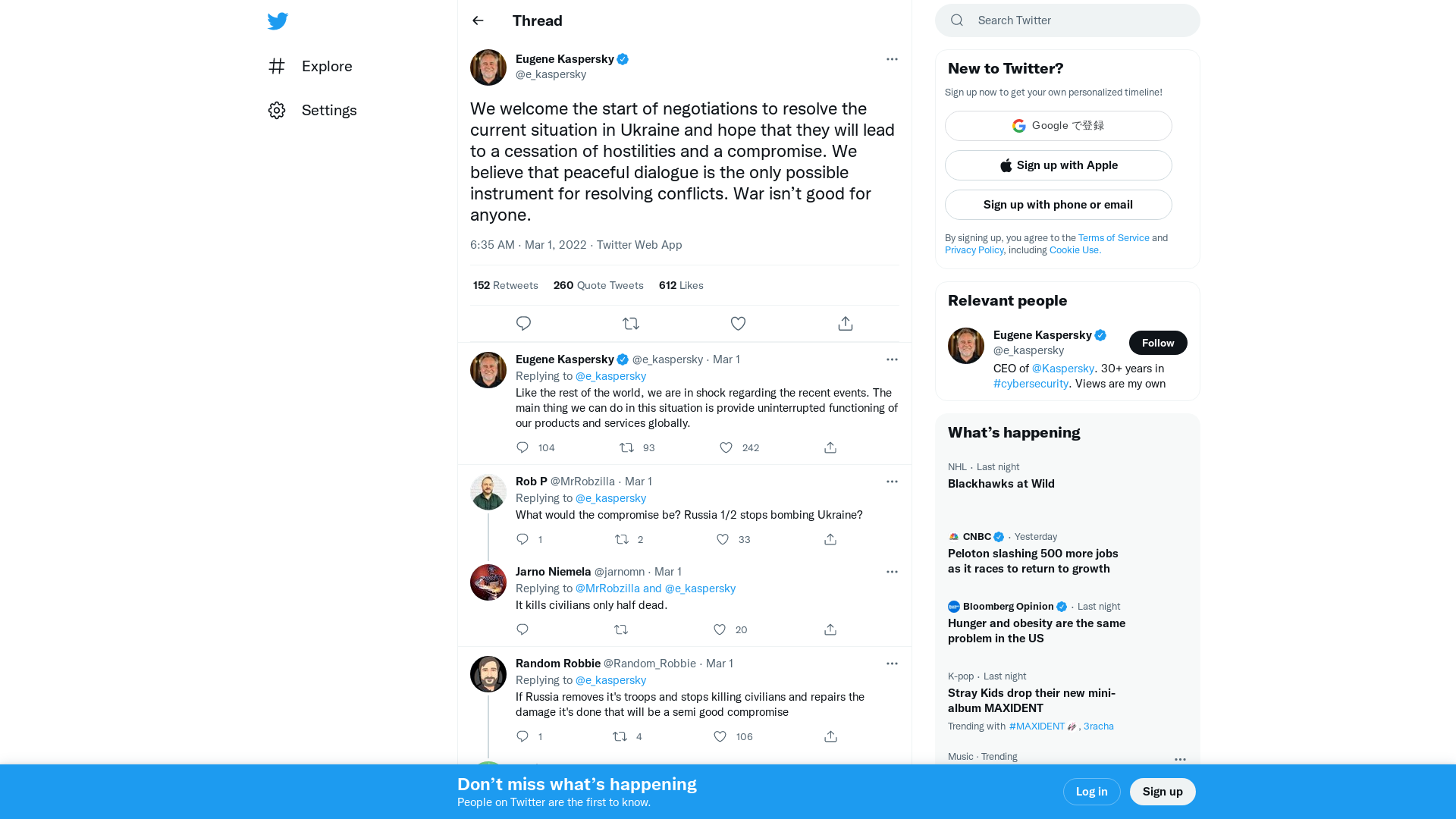
vx-underground - Directory
https://share.vx-underground.org/Conti/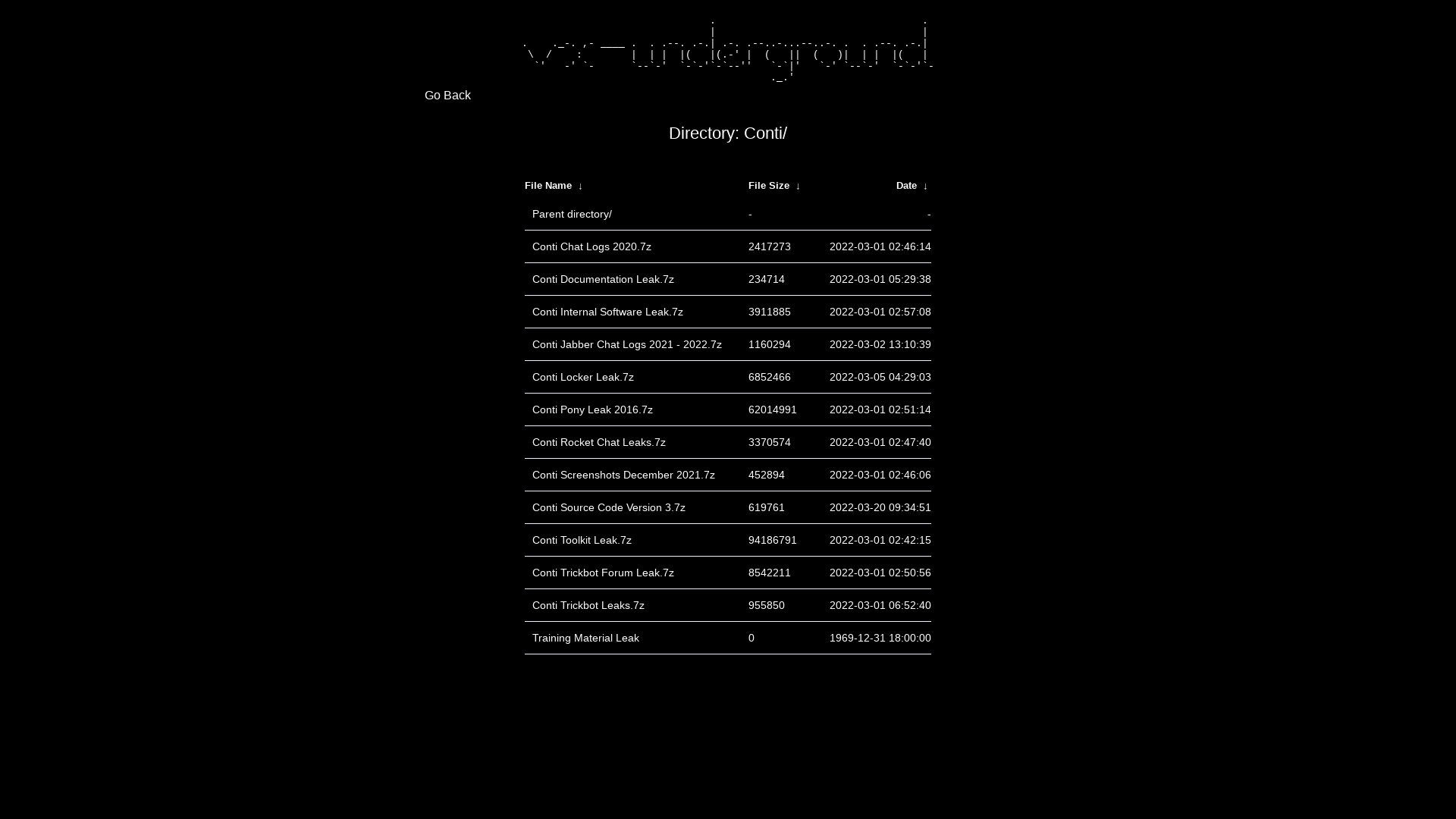
GitHub - tsale/translated_conti_leaked_comms: Leaked communication of Conti ransomware group from Jan 29, 2021 to Feb 27, 2022
https://github.com/tsale/translated_conti_leaked_comms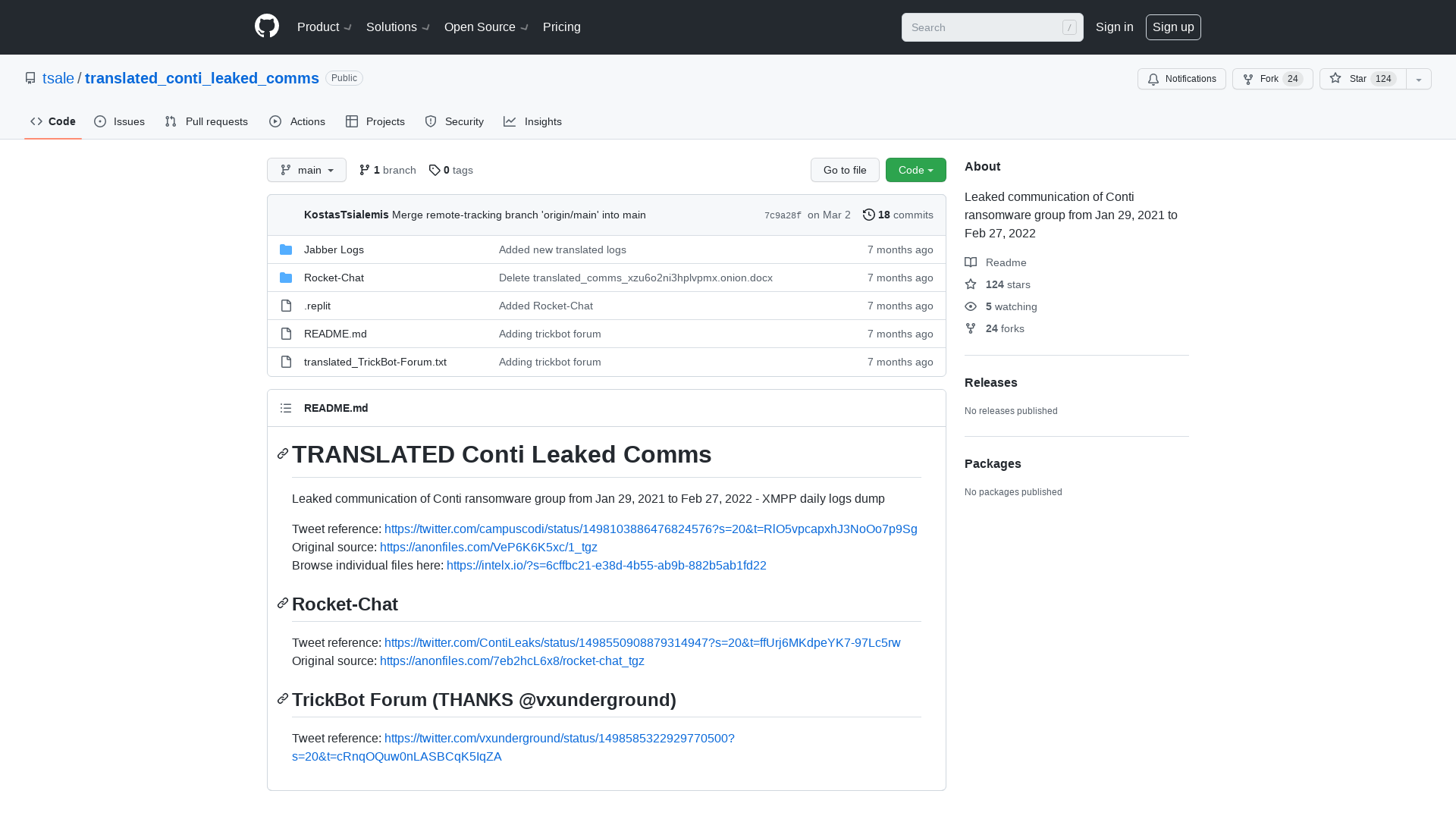
SEKTOR7 Institute
https://institute.sektor7.net/?coupon=DONATE-UKRAINE
Introducing the Golden GMSA Attack | Semperis
https://www.semperis.com/blog/golden-gmsa-attack/
ShadowBreak Intl. on Twitter: "Intelligence acquired since the beginning of the Russian military operation over Ukraine has shown an immense lack of logistic support, making this war one of the most unique in 2022 when it comes to surveillance. A thread 👇🧵 https://t.co/huILD8lEDX" / Twitter
https://twitter.com/sbreakintl/status/1498619303717142529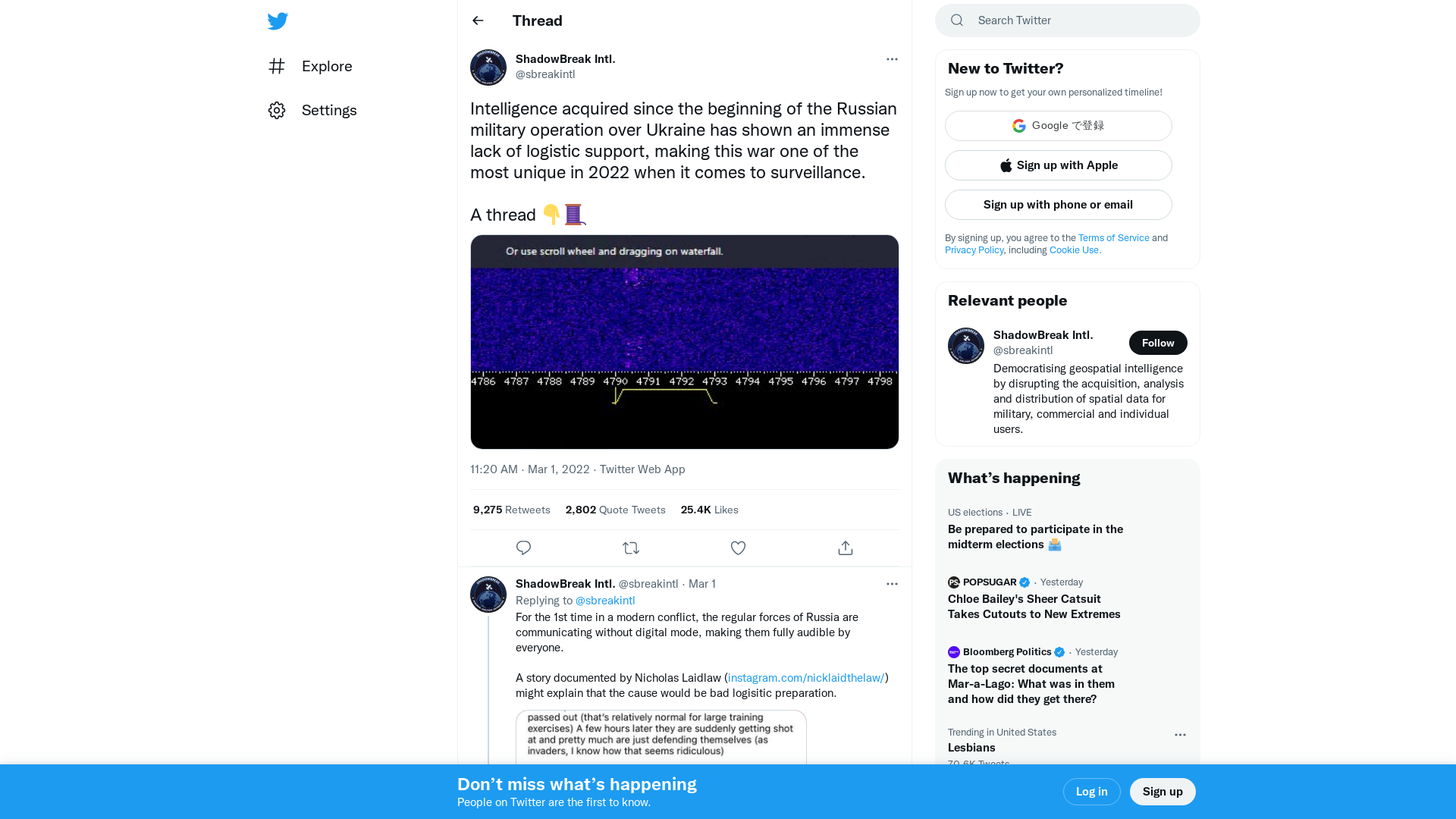
Rogue RDP – Revisiting Initial Access Methods - Black Hills Information Security
https://www.blackhillsinfosec.com/rogue-rdp-revisiting-initial-access-methods/
Особисті дані 120 тисяч військових РФ, що воюють в Україні – ЦОС | Українська правда
https://www.pravda.com.ua/news/2022/03/1/7327081/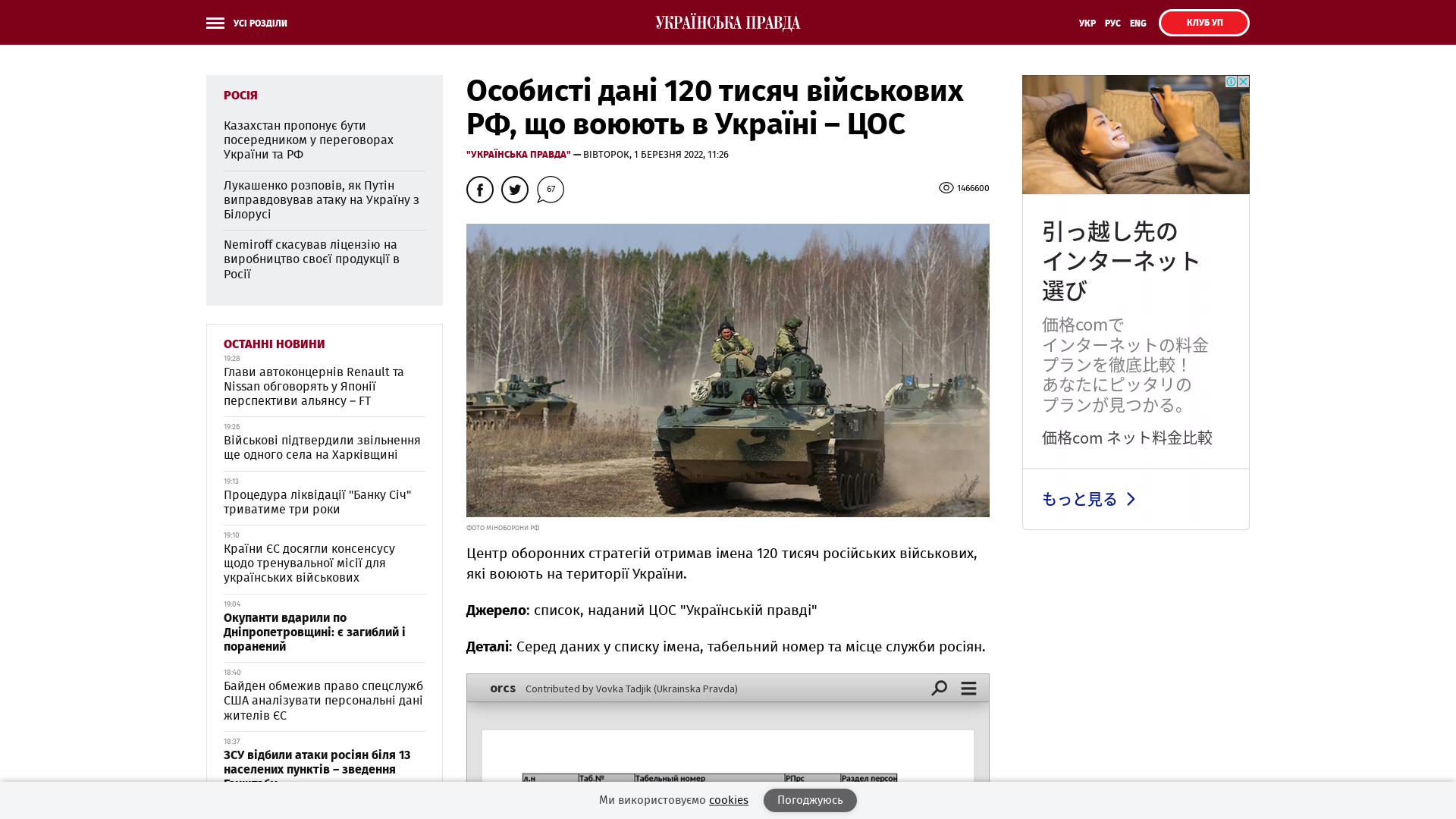
x86matthew - NTSockets - Downloading a file via HTTP using the NtCreateFile and NtDeviceIoControlFile syscalls
https://www.x86matthew.com/view_post?id=ntsockets
Namecheap is banning Russians, asks them to switch registrars
https://www.bleepingcomputer.com/news/technology/namecheap-terminates-services-for-russians-asks-them-to-move-domains/
vx-underground on Twitter: "The Conti ransomware leaks have unveiled Conti's primary Bitcoin address. From April 21st, 2017 - February 28th, 2022 Conti has received 65,498.197 BTC That is 2,707,466,220.29 USD. https://t.co/sUdRnkLsoo" / Twitter
https://twitter.com/vxunderground/status/1498394338027610124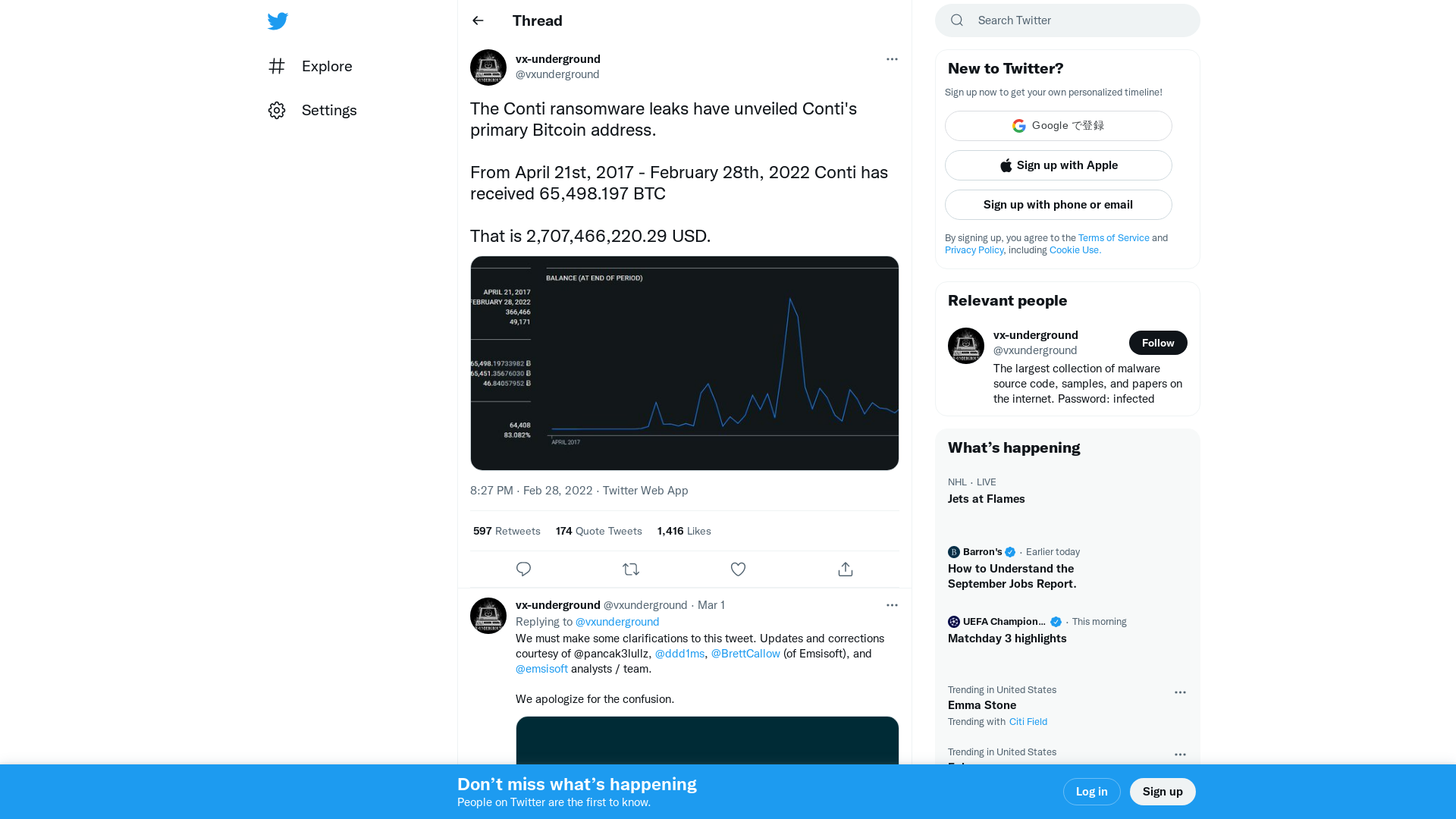
Asylum Ambuscade: State Actor Uses Compromised Private Ukrainian Military Emails to Target European Governments and Refugee Movement | Proofpoint US
https://www.proofpoint.com/us/blog/threat-insight/asylum-ambuscade-state-actor-uses-compromised-private-ukrainian-military-emails
GitHub - wumb0/rust_bof: Cobalt Strike Beacon Object Files (BOFs) written in rust with rust core and alloc.
https://github.com/wumb0/rust_bof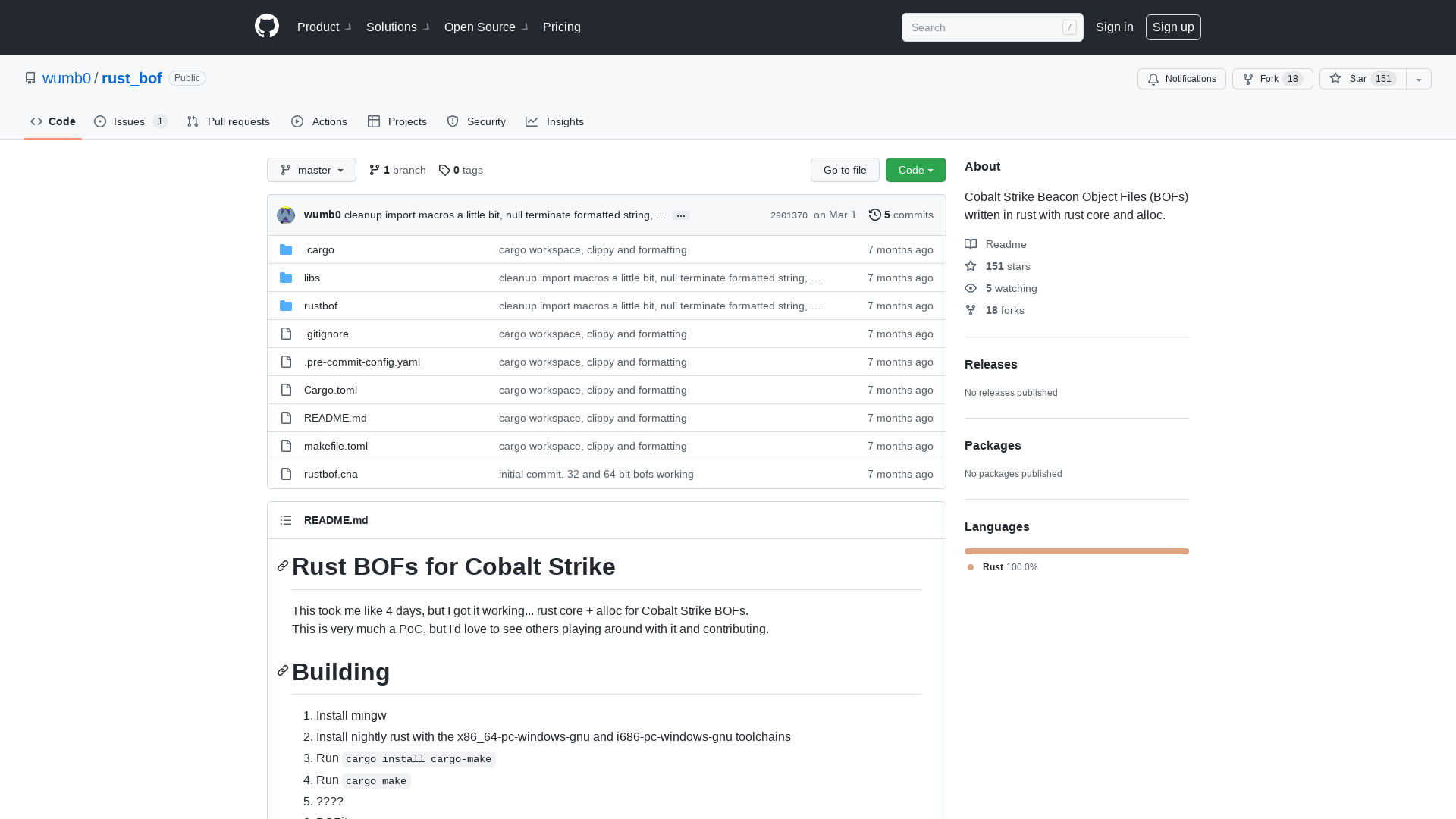
404 Page not found
https://hardenedvault.net/2022/03/01/poc-cve-2021-26708.html
Signal on Twitter: "We've had an uptick in usage in Eastern Europe & rumors are circulating that Signal is hacked & compromised. This is false. Signal is not hacked. We believe these rumors are part of a coordinated misinformation campaign meant to encourage people to use less secure alternatives." / Twitter
https://twitter.com/signalapp/status/1498437474611343367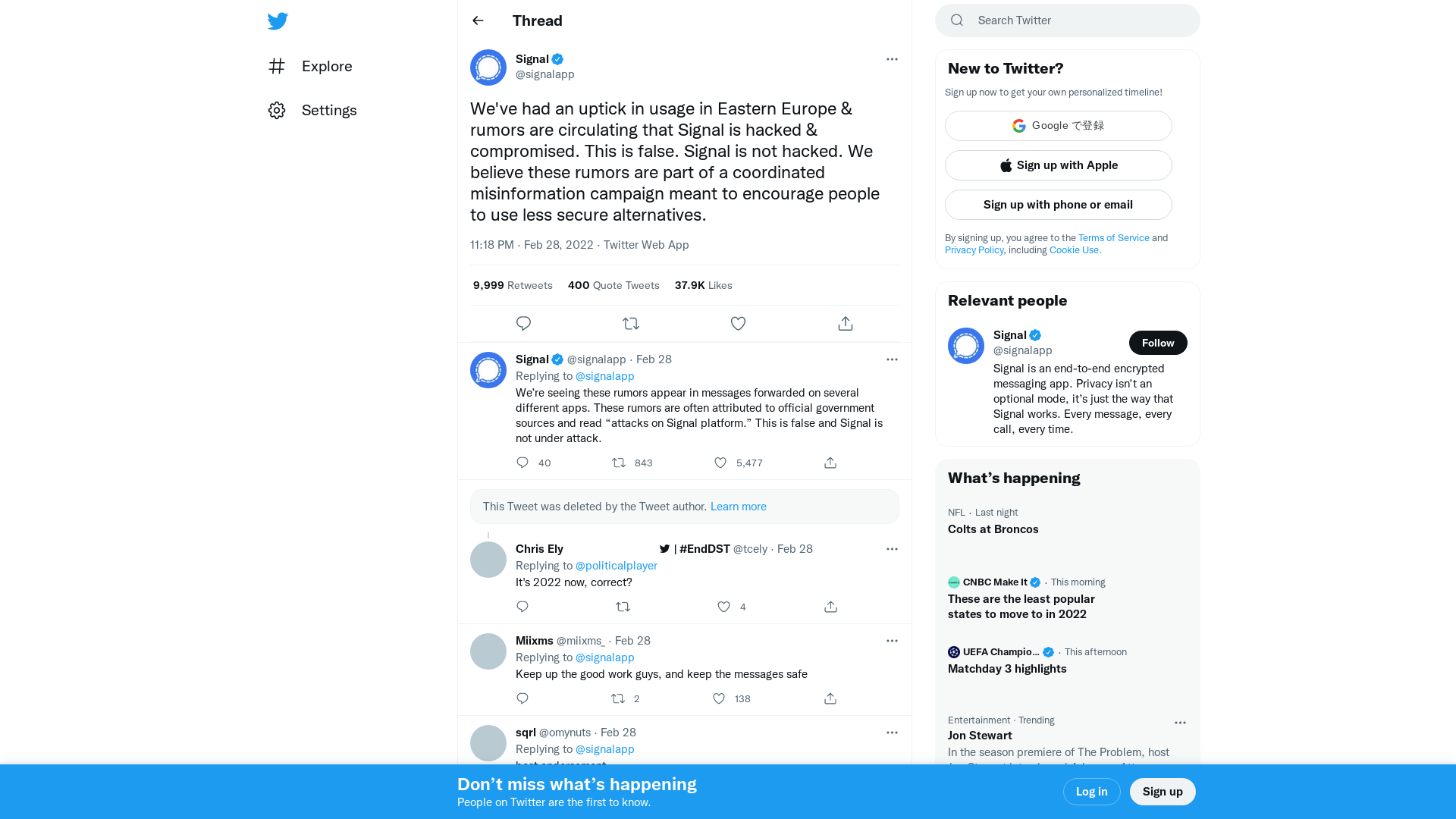
Learning Linux kernel exploitation - Part 1 - Laying the groundwork
https://0x434b.dev/dabbling-with-linux-kernel-exploitation-ctf-challenges-to-learn-the-ropes/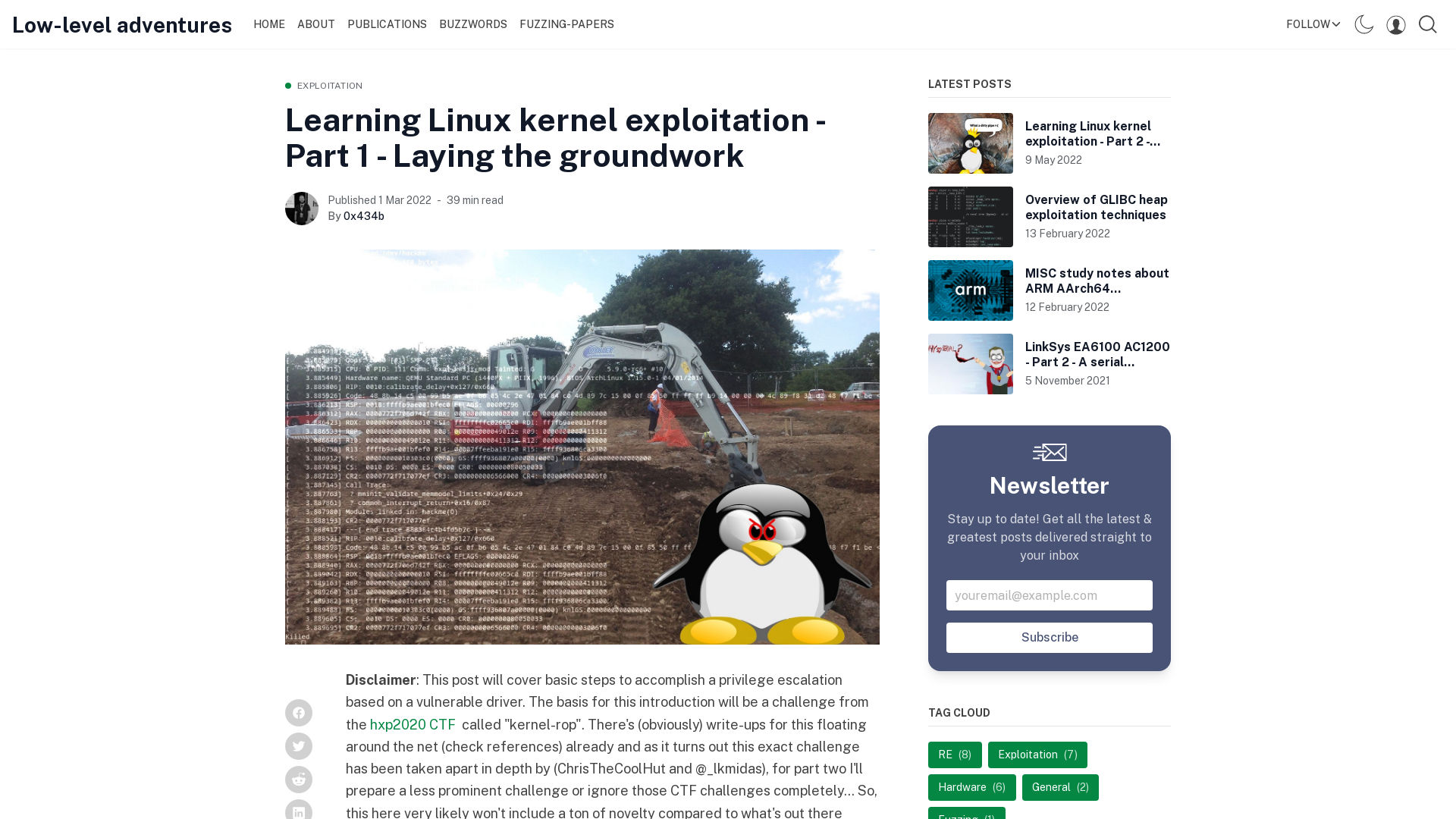
How I Cracked CONTI Ransomware Group’s Leaked Source Code ZIP File - Wade Hickey - Medium
https://medium.com/@whickey000/how-i-cracked-conti-ransomware-groups-leaked-source-code-zip-file-e15d54663a8
Daxin: Stealthy Backdoor Designed for Attacks Against Hardened Networks | Broadcom Software Blogs
https://symantec-enterprise-blogs.security.com/blogs/threat-intelligence/daxin-backdoor-espionage
z0man on Twitter: "Conti Leaks show hacked company "ZOOM". #ransomware https://t.co/AEeoLnz8YX" / Twitter
https://twitter.com/z0man/status/1498576211093729284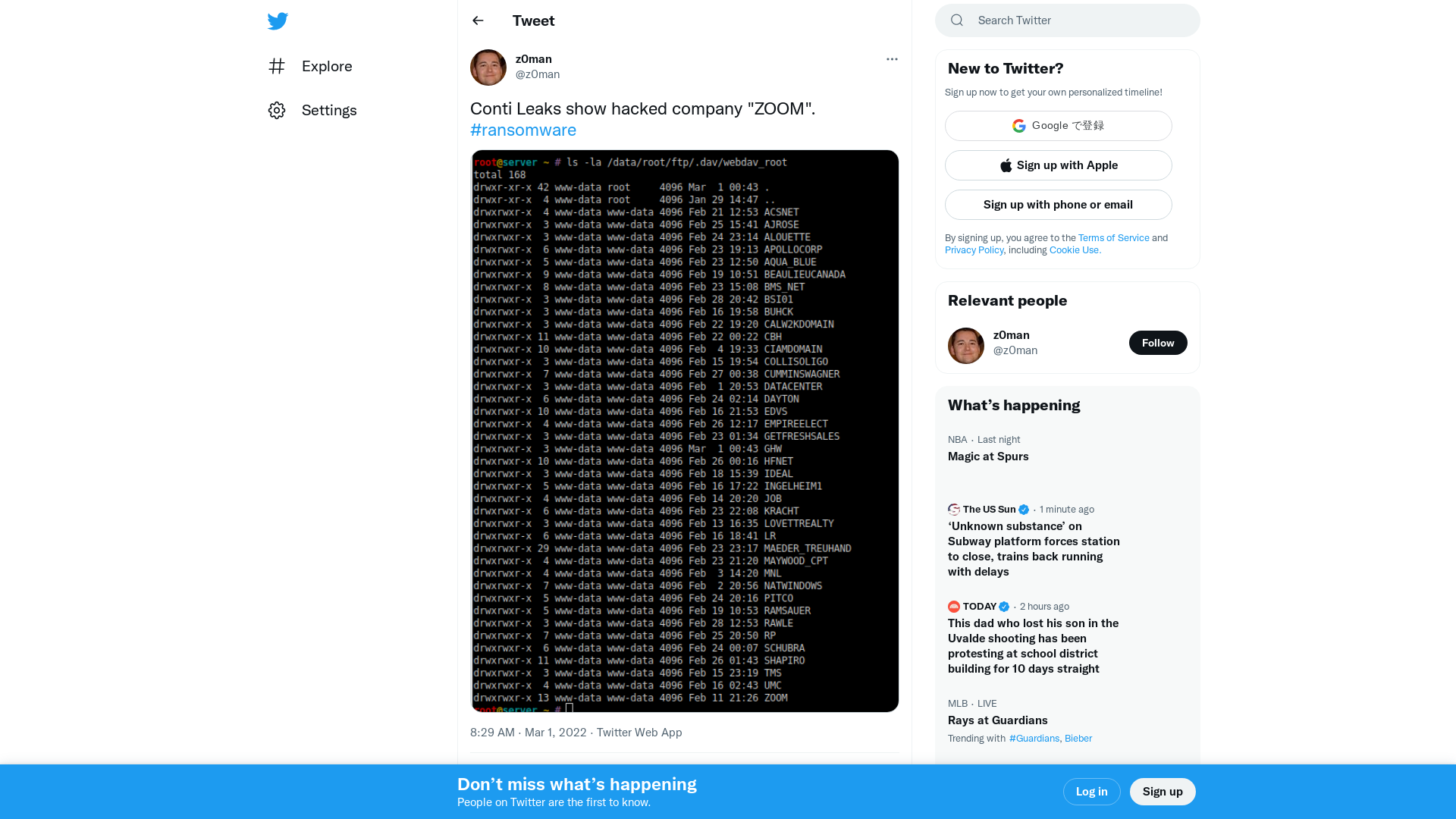
Triage | Malware sandboxing report by Hatching Triage
https://tria.ge/220228-lvldtsdhg4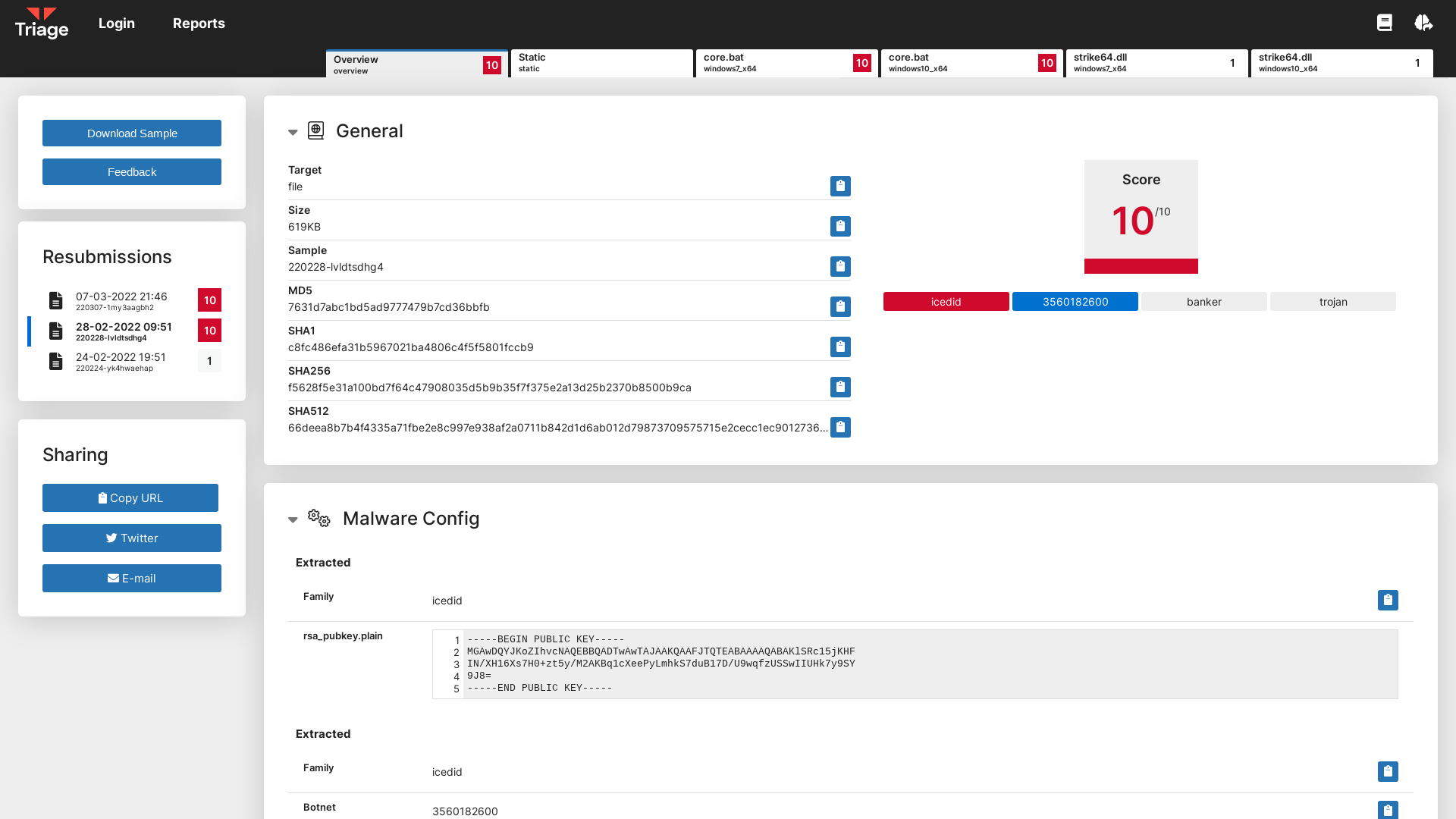
Conti Ransomware Group Diaries, Part I: Evasion – Krebs on Security
https://krebsonsecurity.com/2022/03/conti-ransomware-group-diaries-part-i-evasion/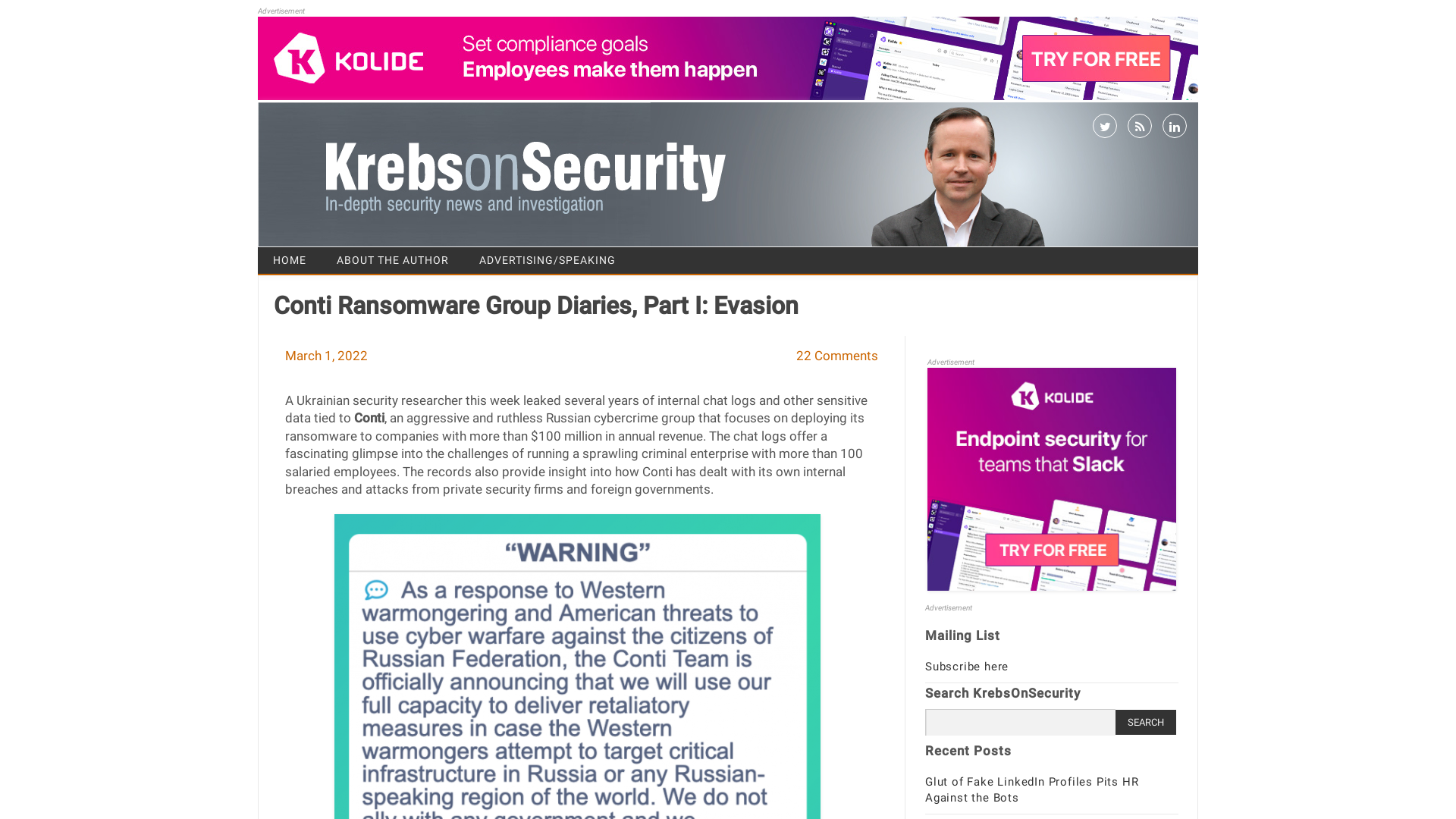
Ready, Set, Go — Golang Internals and Symbol Recovery | Mandiant
https://www.mandiant.com/resources/golang-internals-symbol-recovery
Digital technology and the war in Ukraine - Microsoft On the Issues
https://blogs.microsoft.com/on-the-issues/2022/02/28/ukraine-russia-digital-war-cyberattacks/
'Help Ukraine' crypto scams emerge as Ukraine raises over $37 million
https://www.bleepingcomputer.com/news/security/help-ukraine-crypto-scams-emerge-as-ukraine-raises-over-37-million/
conti leaks on Twitter: "Sergei Loguntsov (https://t.co/bGad1NzIZG) aka. begemot https://t.co/rlkyRpAq7p" / Twitter
https://twitter.com/ContiLeaks/status/1498633447866343429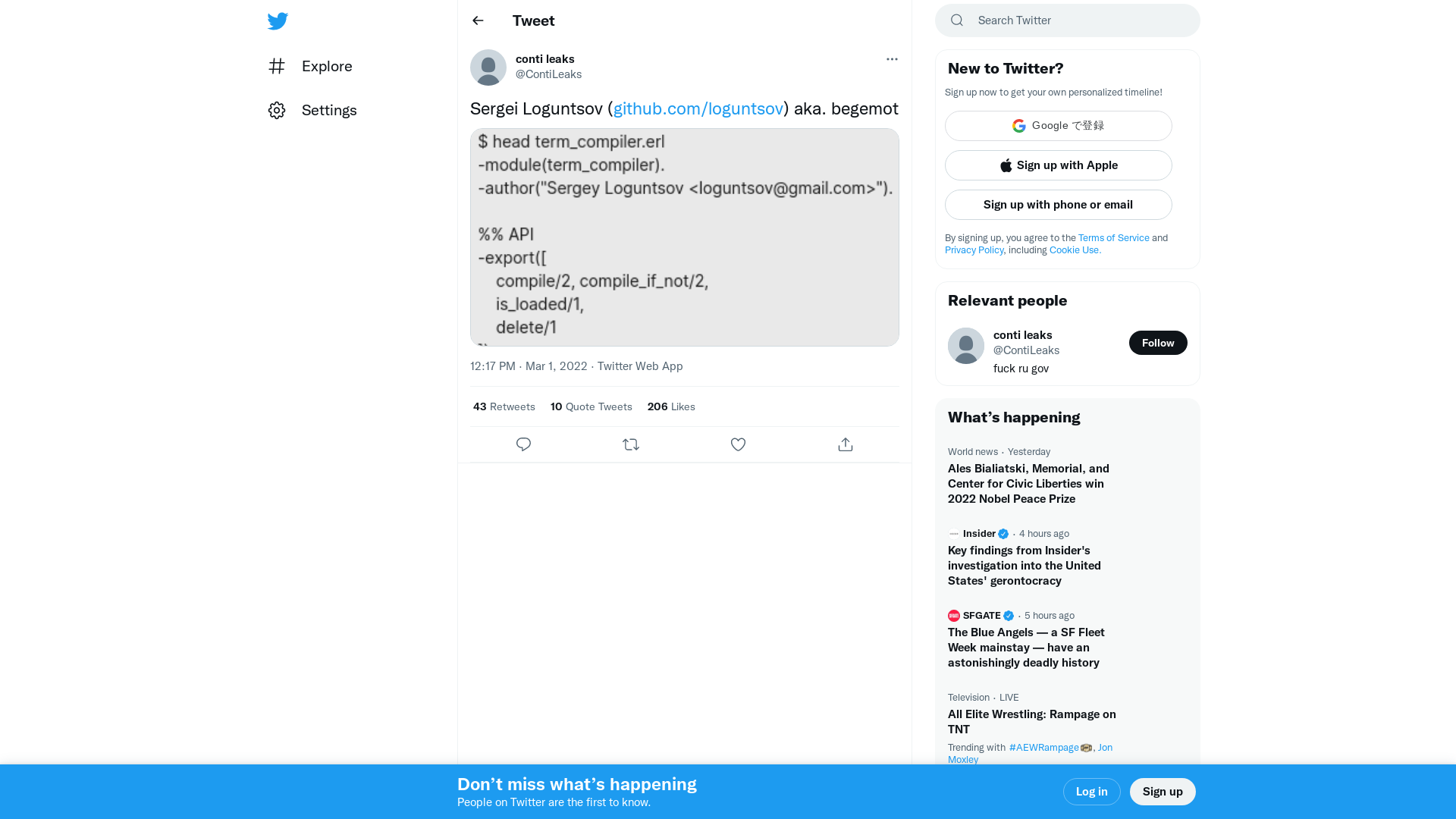
[email protected] to ICANN: Ukraine urgently need ICANN's support - Pastebin.com
https://pastebin.com/DLbmYahS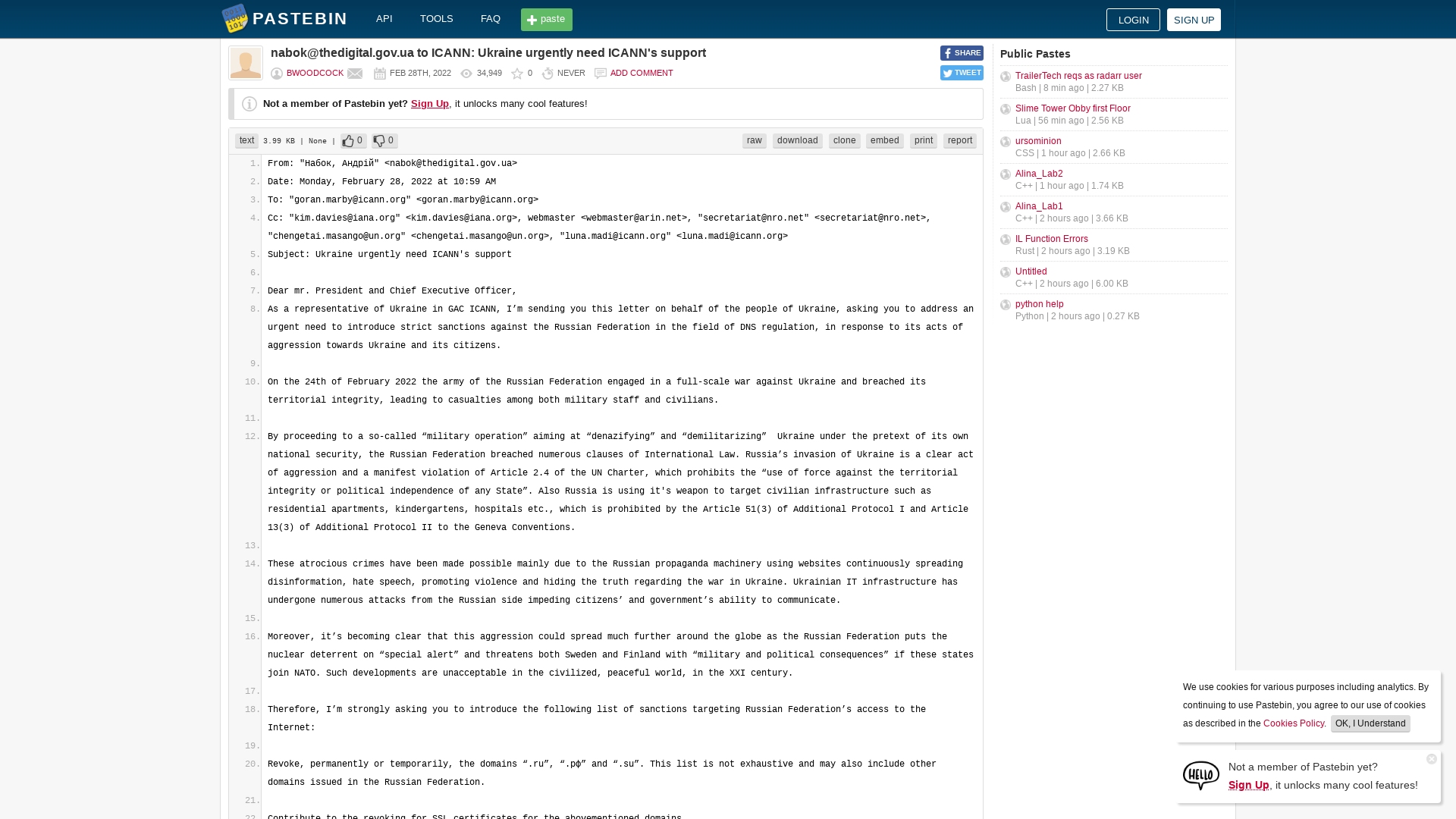
‘Yes, He Would’: Fiona Hill on Putin and Nukes - POLITICO
https://www.politico.com/news/magazine/2022/02/28/world-war-iii-already-there-00012340
DiskKill/HermeticWiper and NotPetya (Dis)similarities
https://marcoramilli.com/2022/03/01/diskkill-hermeticwiper-and-notpetya-dissimilarities/
Microsoft: Windows domain controller restarts caused by LSASS crashes
https://www.bleepingcomputer.com/news/microsoft/microsoft-windows-domain-controller-restarts-caused-by-lsass-crashes/
Sign Up | LinkedIn
https://www.linkedin.com/posts/lcarhart_im-happy-to-share-that-im-starting-a-new-activity-6901974949796679680-Oqa_
Thomas van Linge on Twitter: "#Ukraine 🇺🇦: in occupied Krupyansk (#Kharkiv) people are rising up against the Russian invasion force, literally chasing them out of town. https://t.co/y17OFCJsWF" / Twitter
https://twitter.com/thomasvlinge/status/1498628238427496448
Making Space for Diversity in Cybersecurity - Ms. Magazine
https://msmagazine.com/2022/02/25/diversity-cybersecurity-black-women/
Costin Raiu on Twitter: "Just in case - #FoxBlade == #HermeticWiper https://t.co/EJAnLNSDfm" / Twitter
https://twitter.com/craiu/status/1498681137681547268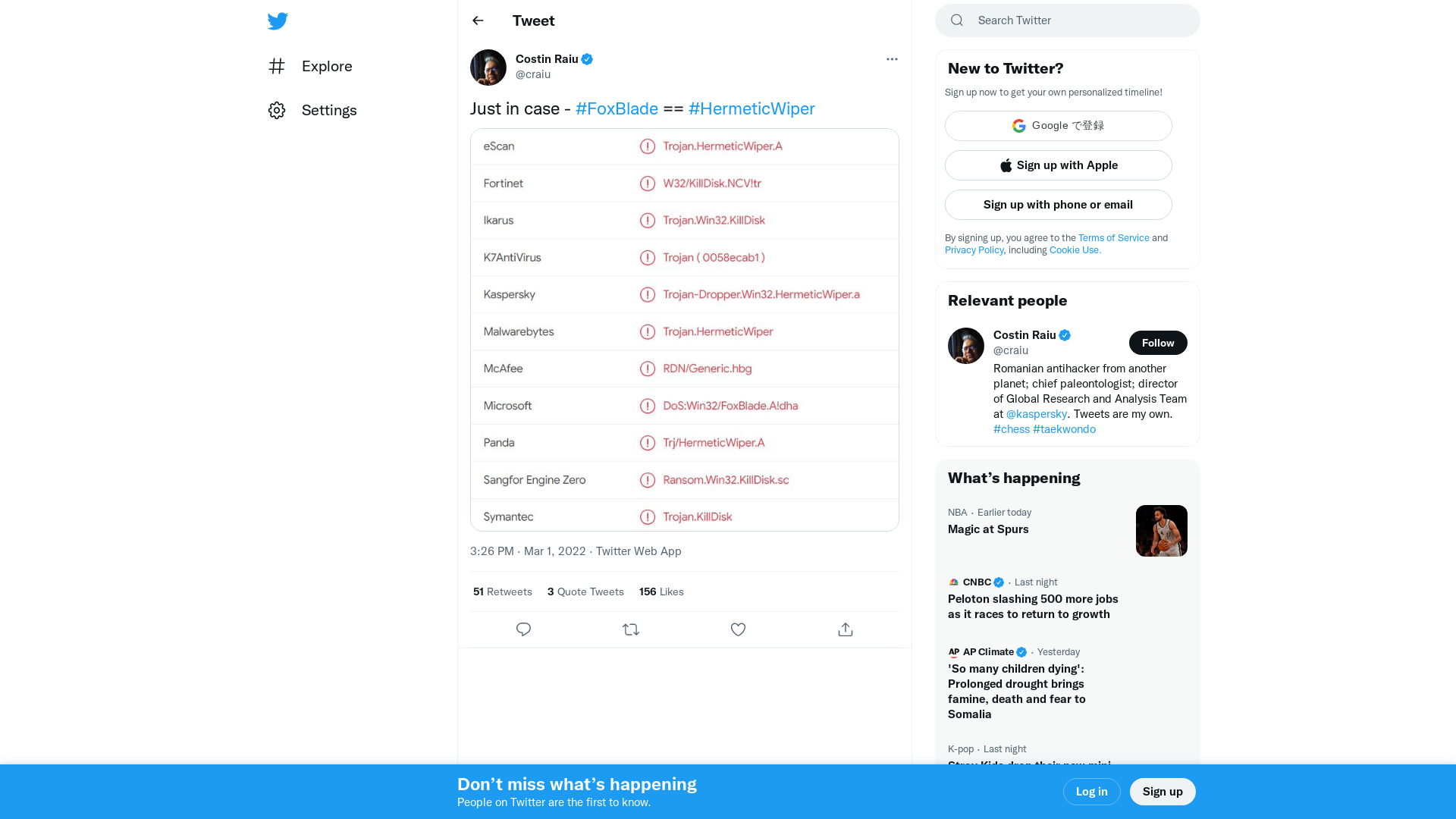
TrickBot Malware Gang Upgrades its AnchorDNS Backdoor to AnchorMail
https://thehackernews.com/2022/03/trickbot-malware-gang-upgrades-its.html
Lawrence Abrams on Twitter: "Always been speculation that Conti is a rebrand of Ryuk. However this chat sounds like the affiliates were surprised that Ryuk uses the same TTPs as Conti. Or were both operations run by the same "managers," but the affiliates were left in the dark? #ContiLeaks https://t.co/GgLzbuPAsZ" / Twitter
https://twitter.com/lawrenceabrams/status/1498525119148351489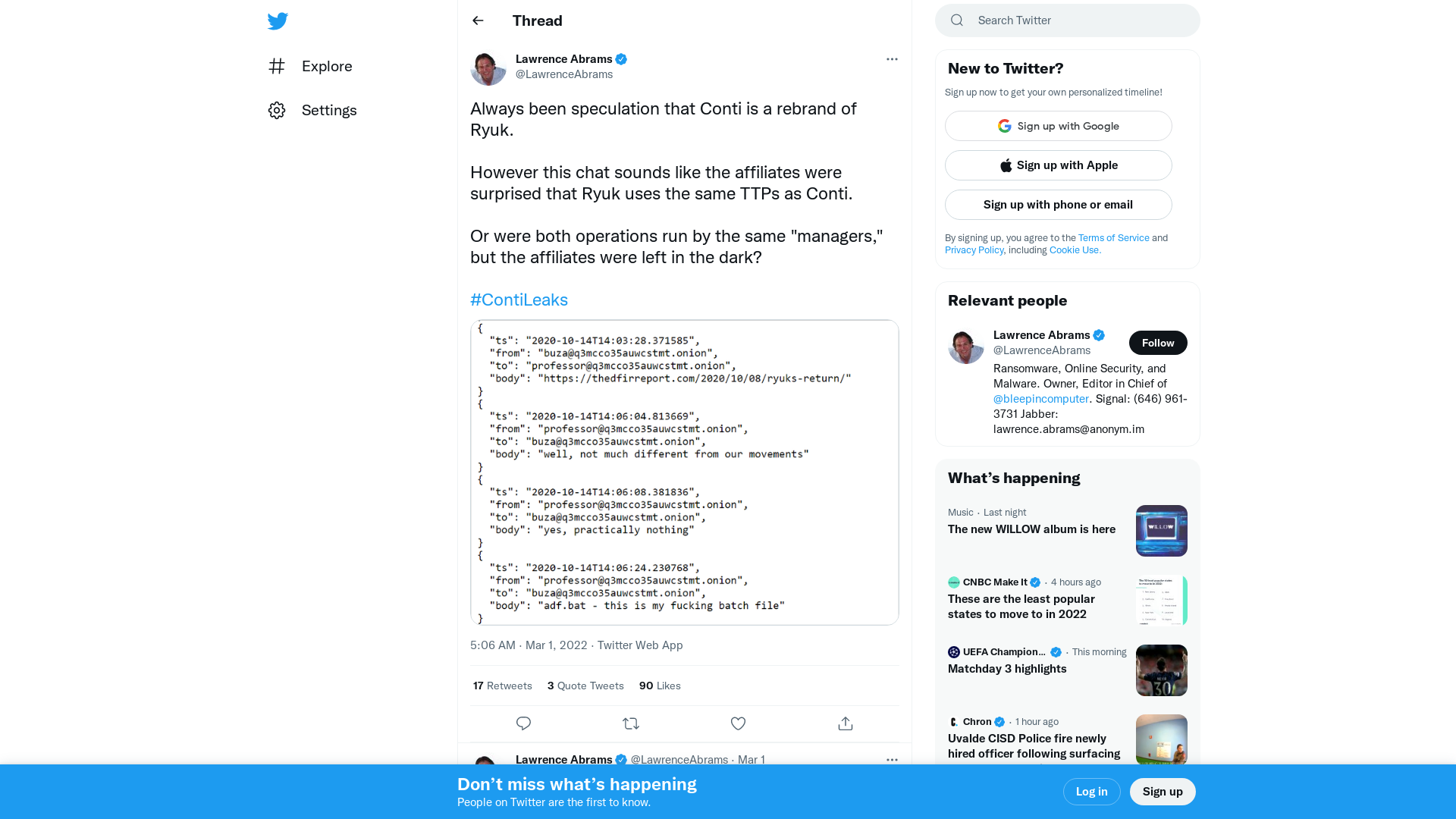
Shields Up | CISA
http://cisa.gov/shields-up
Infosecurity Magazine Cybersecurity Online Summit - 22nd March, 2022
https://bit.ly/3t6ZQub
URLhaus | Checking your browser
https://urlhaus.abuse.ch/url/2068673/
Skarbonka Pomagacza Anonimowy Pomagacz - #CTFforUA | Siepomaga.pl
https://www.siepomaga.pl/ctfforua
Tweet / Twitter
https://twitter.com/elbeardsley/status/1498640644339908609
BrokenPrint: A Netgear stack overflow – NCC Group Research
https://research.nccgroup.com/2022/02/28/brokenprint-a-netgear-stack-overflow/
Microsoft Finds FoxBlade Malware Hit Ukraine Hours Before Russian Invasion
https://thehackernews.com/2022/03/microsoft-finds-foxblade-malware-hit.html
vx-underground - Directory
https://samples.vx-underground.org/APTs/2022/2022.02.28/