x86matthew - EmbedExeLnk - Embedding an EXE inside a LNK with automatic execution
https://www.x86matthew.com/view_post?id=embed_exe_lnk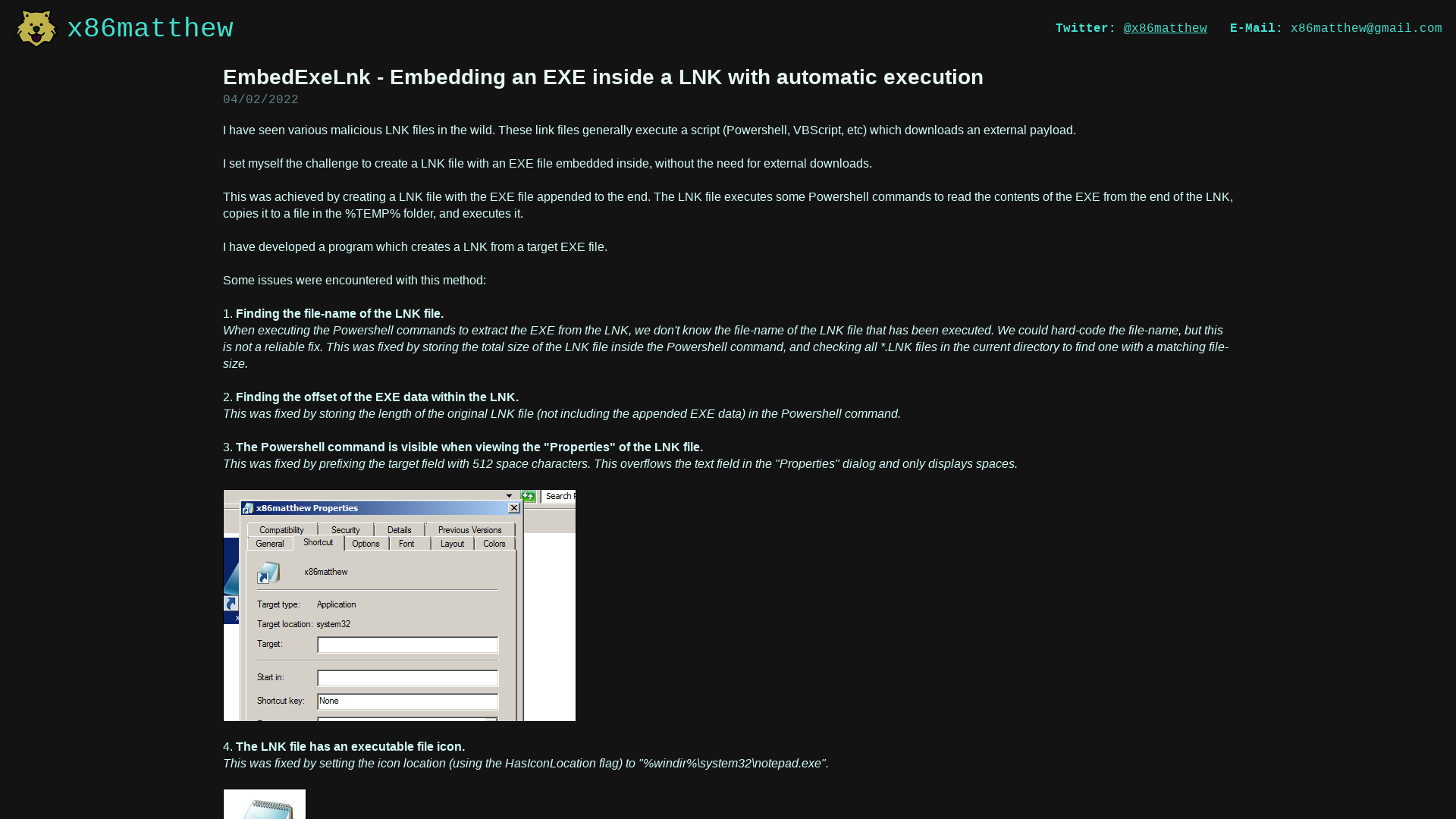
x86matthew - CreateSvcRpc - A custom RPC client to execute programs as the SYSTEM user
https://www.x86matthew.com/view_post?id=create_svc_rpc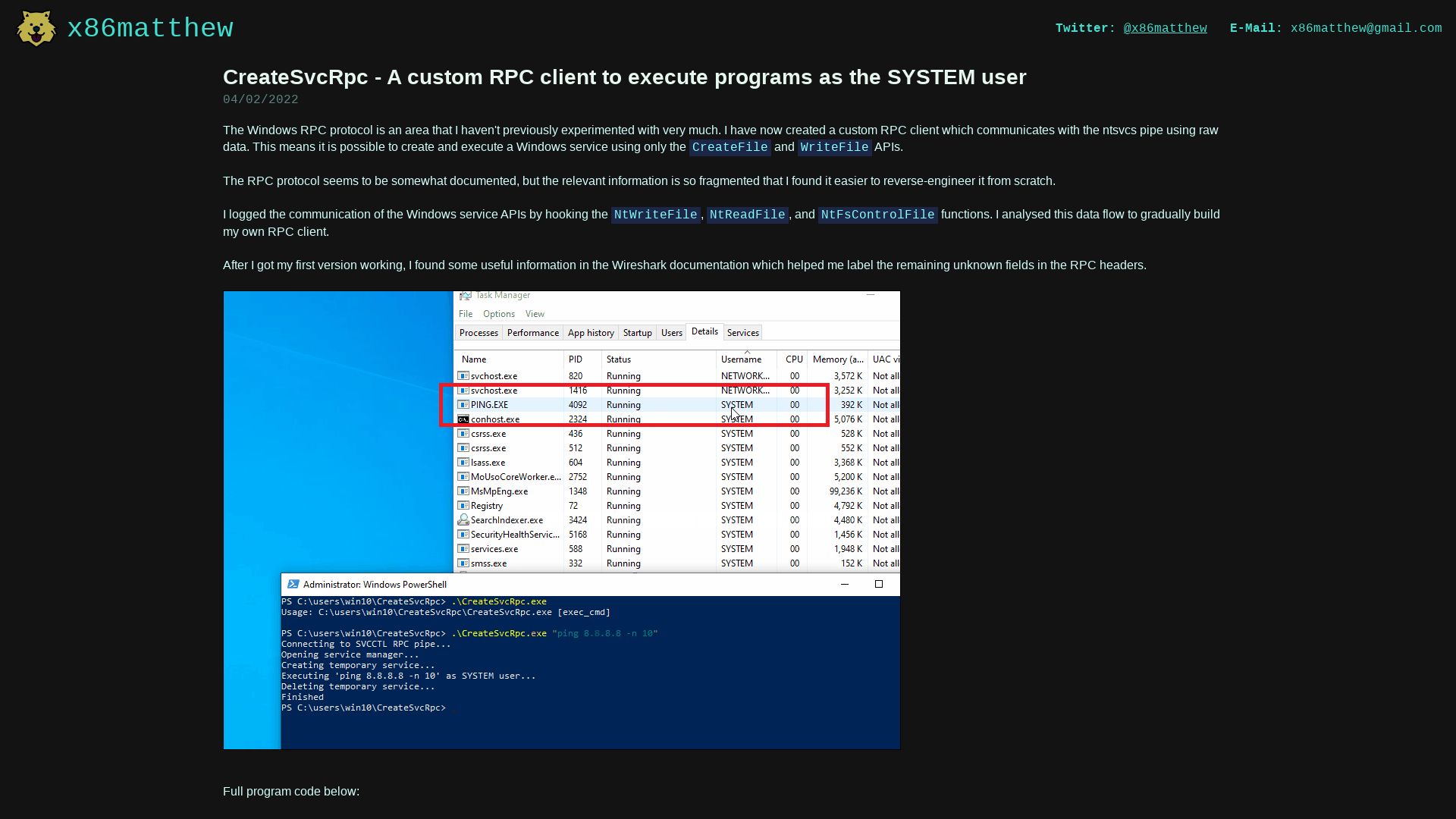
Microsoft disables MSIX protocol handler abused in Emotet attacks
https://www.bleepingcomputer.com/news/microsoft/microsoft-disables-msix-protocol-handler-abused-in-emotet-attacks/
conti-cyber-attack-on-the-hse-full-report.pdf
https://www.hse.ie/eng/services/publications/conti-cyber-attack-on-the-hse-full-report.pdf
offensivecon_22_attacking_javascript_engines.pdf
https://saelo.github.io/presentations/offensivecon_22_attacking_javascript_engines.pdf
GitHub - S3cur3Th1sSh1t/Nim-RunPE: A Nim implementation of reflective PE-Loading from memory
https://github.com/S3cur3Th1sSh1t/Nim-RunPE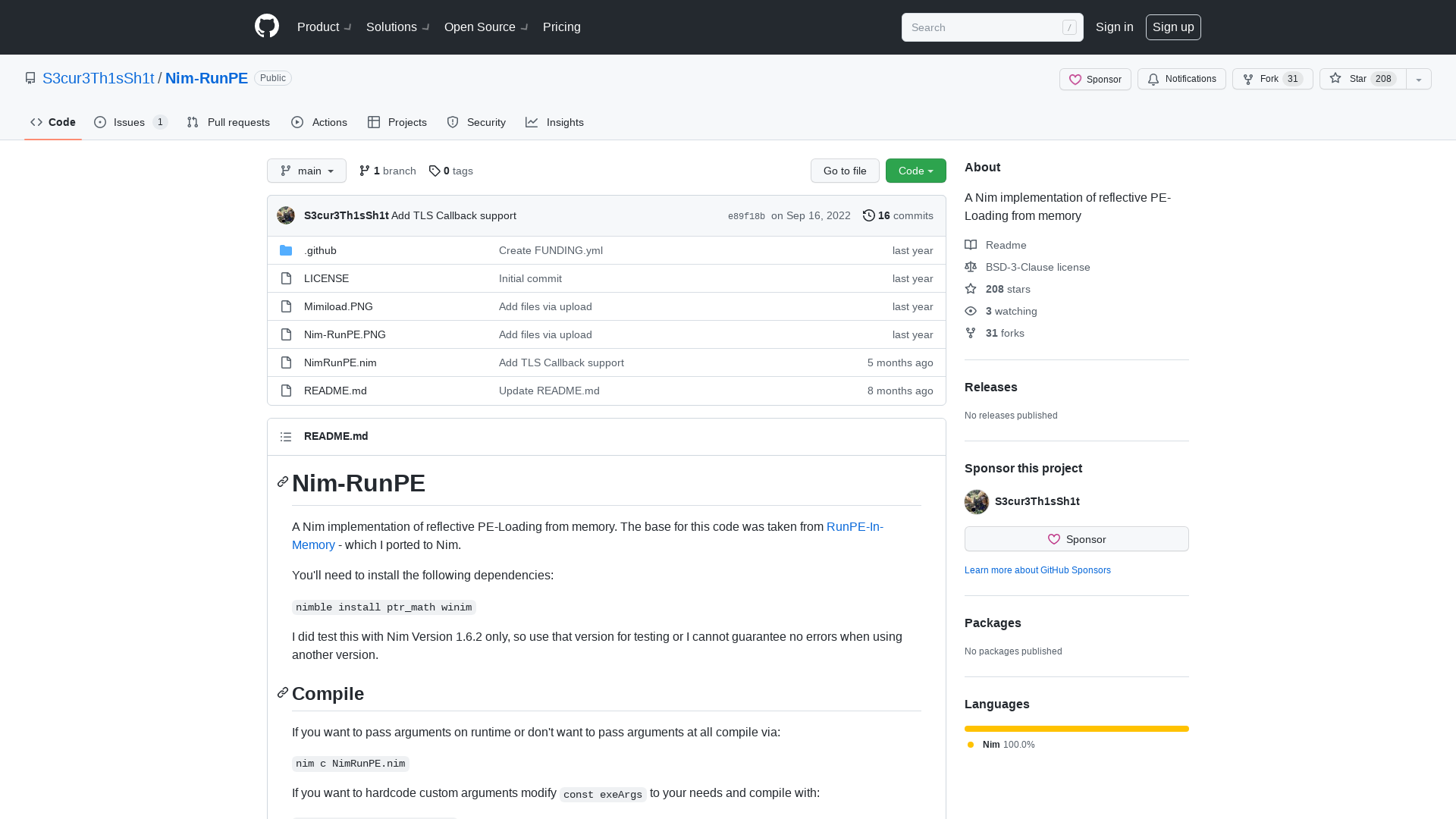
Malware-Traffic-Analysis.net - 2022-02-04 (Friday) - BazarLoader infection with Cobalt Strike
https://www.malware-traffic-analysis.net/2022/02/04/index.html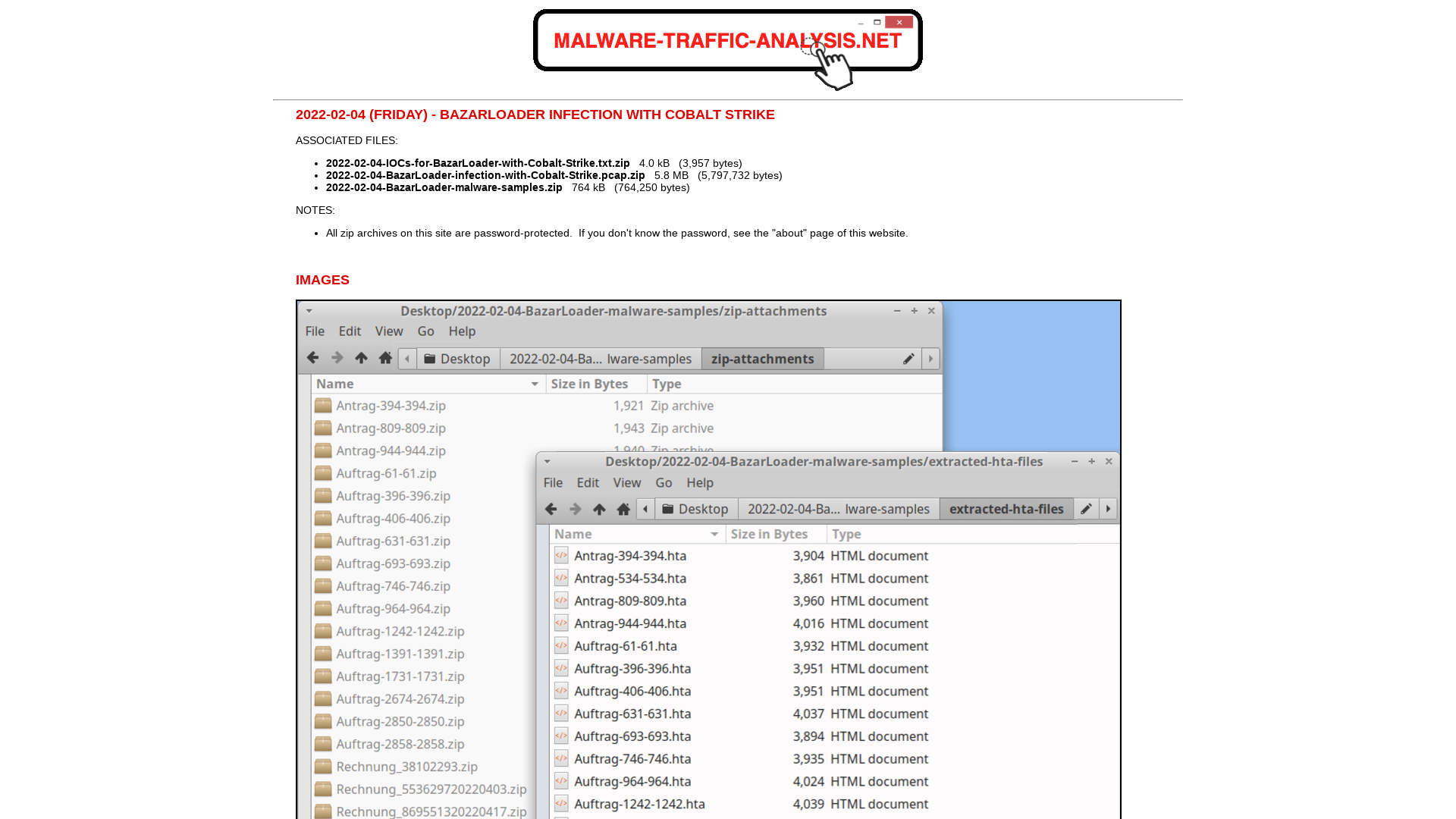
GitHub - hfiref0x/UACME: Defeating Windows User Account Control
https://github.com/hfiref0x/UACME
Operation EmailThief: Active Exploitation of Zero-day XSS Vulnerability in Zimbra | Volexity
https://www.volexity.com/blog/2022/02/03/operation-emailthief-active-exploitation-of-zero-day-xss-vulnerability-in-zimbra/
OffensiveCon 2022 - Bug Hunting S21s 10ADAB1E FW.pdf
https://www.dropbox.com/s/2f14ga52jguu5cy/OffensiveCon%202022%20-%20Bug%20Hunting%20S21s%2010ADAB1E%20FW.pdf?dl=0
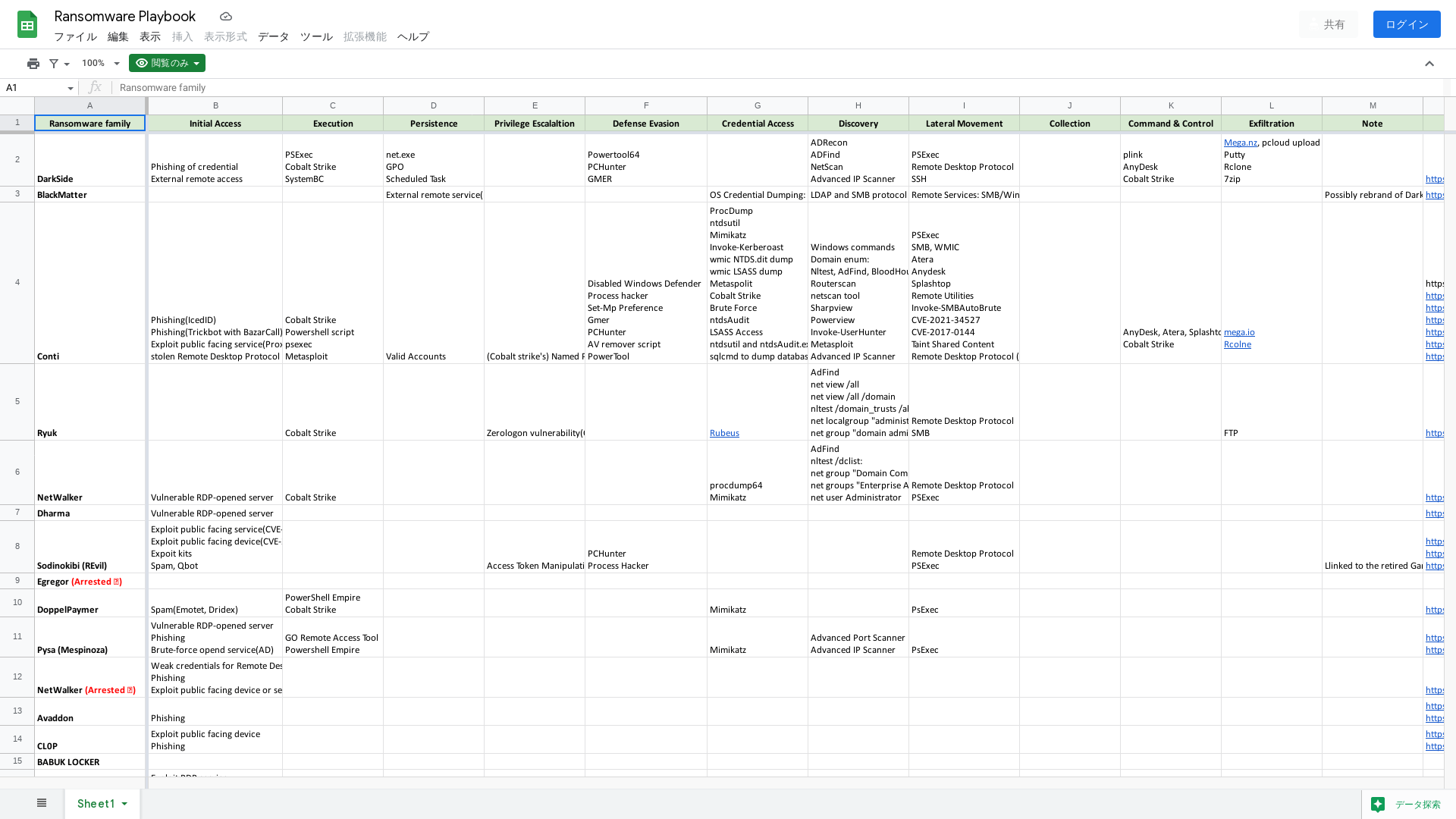
Ransomware Playbook - Google スプレッドシート
https://docs.google.com/spreadsheets/d/1lOrsSEUWze4lJyQkHSZXzS6iXsFtoNOFwXf1dYSXIw8/edit?usp=sharing