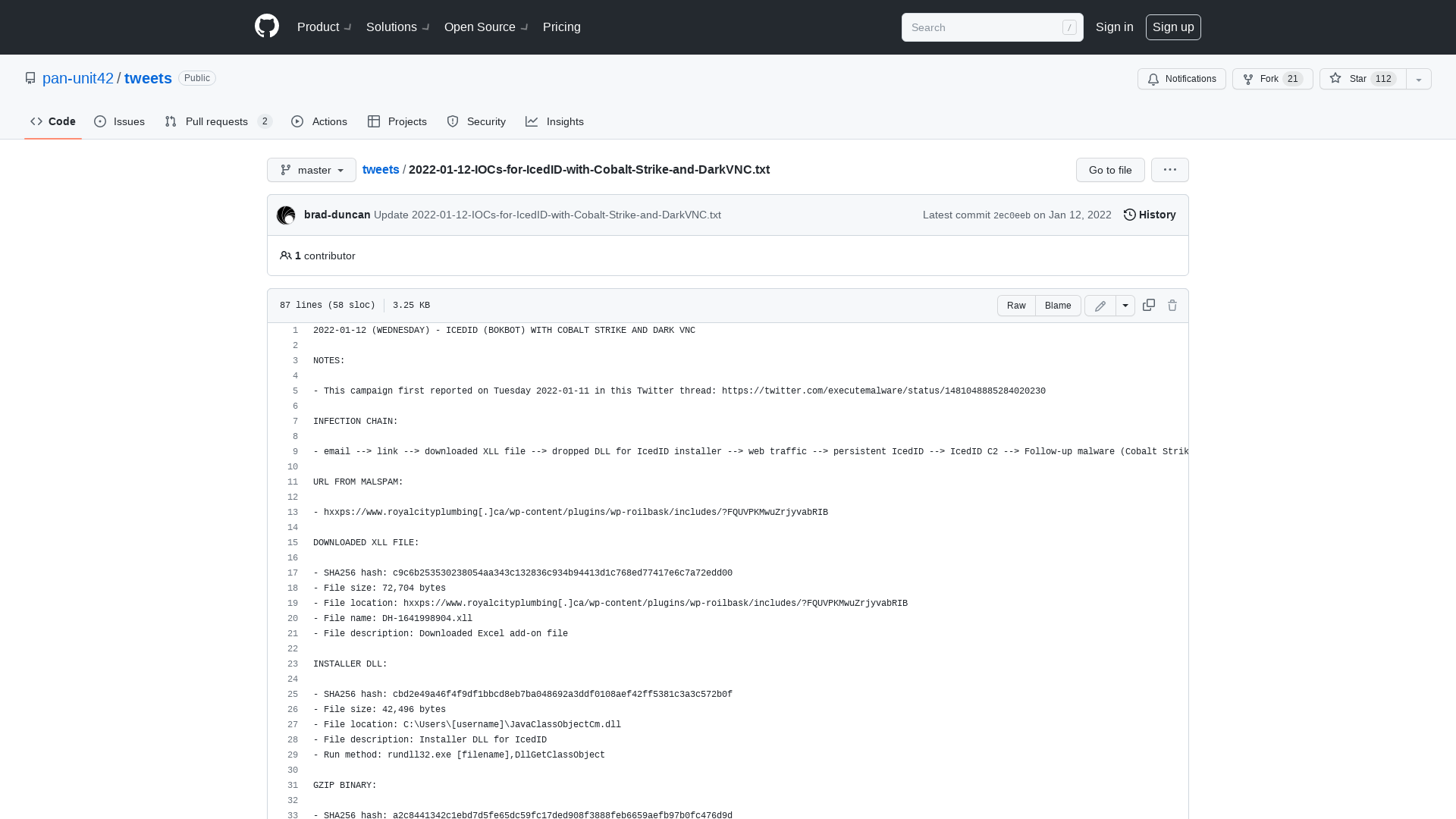
VirusTotal - User - CYBERCOM_Malware_Alert
http://www.Virustotal.com/en/user/CYBERCOM_Malware_Alert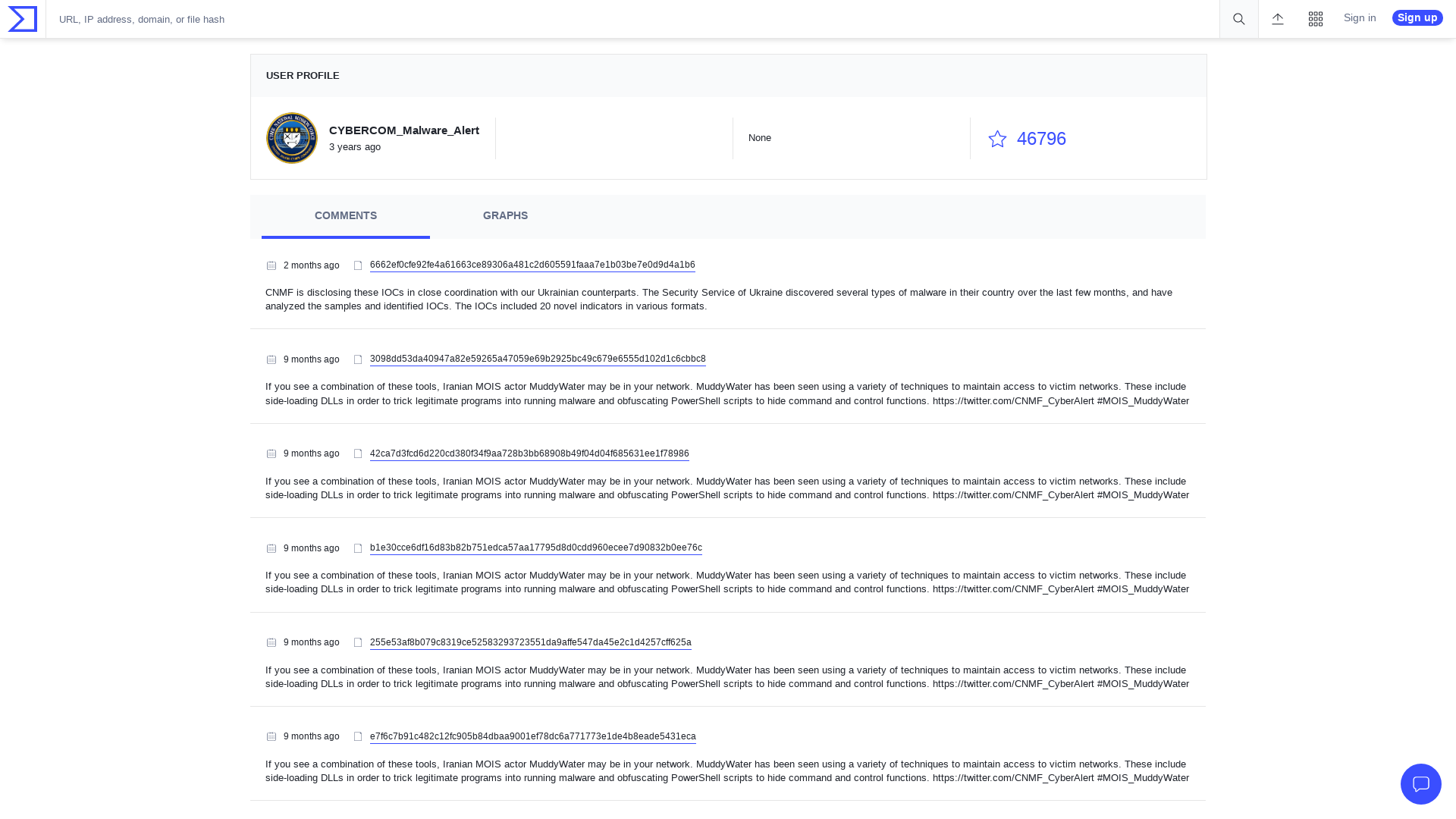
USCYBERCOM Cybersecurity Alert on Twitter: "Iranian MOIS hacker group #MuddyWater is using a suite of malware to conduct espionage and malicious activity. If you see two or more of these malware on your network, you may have MuddyWater on it: https://t.co/xTI6xuQOg3. Attributed through @NCIJTF @FBI" / Twitter
https://twitter.com/cnmf_cyberalert/status/1481341952247349248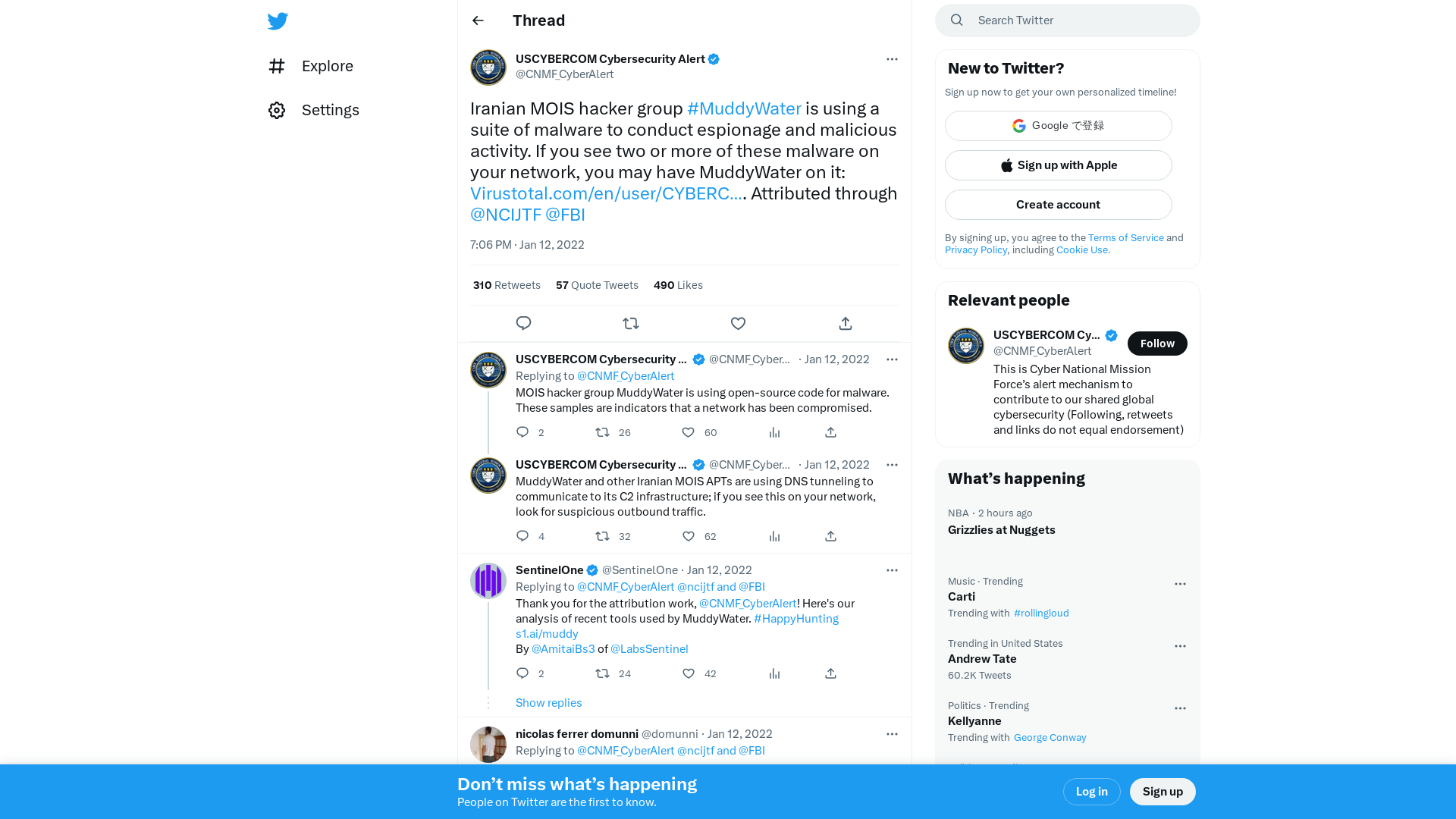
FBI Honeypot Phone Company Anom Shipped Over 100 Phones to the United States
https://www.vice.com/en/article/epxp8w/fbi-anom-shipped-100-phones-united-states
firmwire-ndss22-hernandez.pdf
https://hernan.de/research/papers/firmwire-ndss22-hernandez.pdf
Pre-Auth RCE in Moodle Part II - Session Hijack in Moodle's Shibboleth · Haxolot.com
https://haxolot.com/posts/2022/moodle_pre_auth_shibboleth_rce_part2/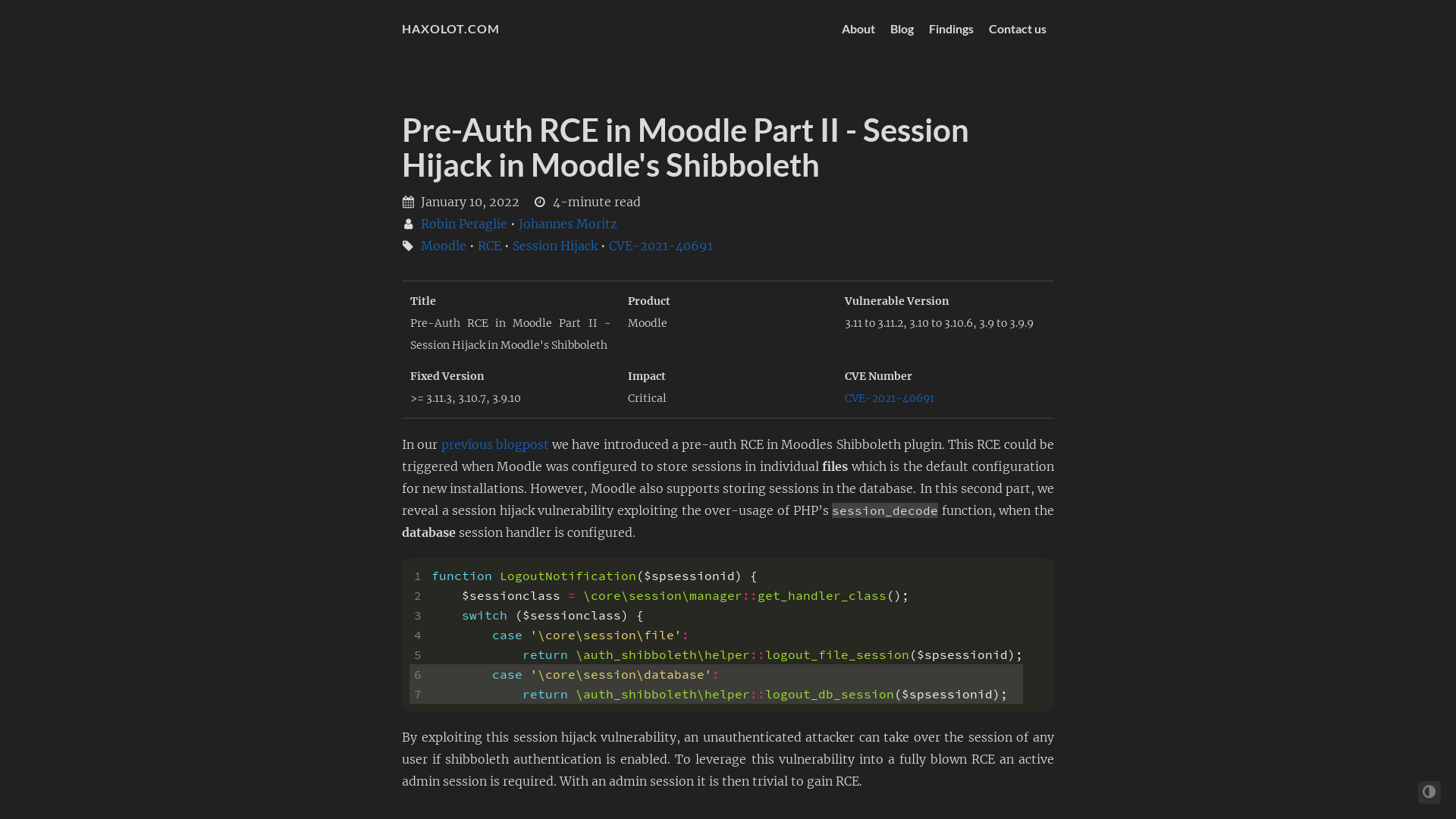
Objective-See's Blog
https://objective-see.com/blog/blog_0x6C.html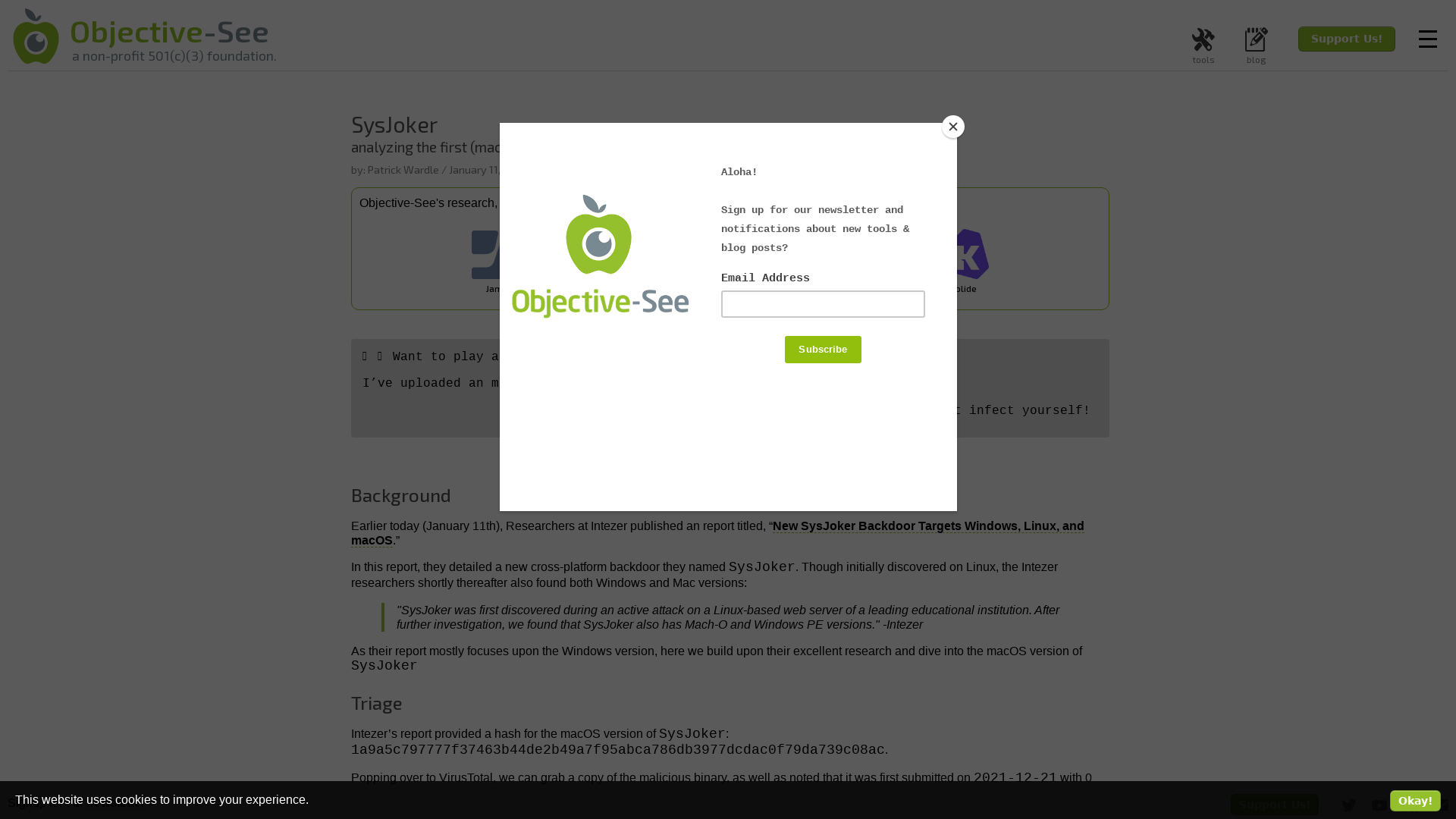
Zero Day Initiative — Pwn2Own Vancouver Returns for the 15th Anniversary of the Contest
https://www.zerodayinitiative.com/blog/2022/1/12/pwn2own-vancouver-2022-luanch
New SysJoker Backdoor Targets Windows, Linux, and macOS - Intezer
https://www.intezer.com/blog/malware-analysis/new-backdoor-sysjoker/
Malware development part 1 - basics – 0xPat blog – Red/purple teamer
https://0xpat.github.io/Malware_development_part_1/
Malware development part 3 - anti-debugging – 0xPat blog – Red/purple teamer
https://0xpat.github.io/Malware_development_part_3/
Malware development part 2 - anti dynamic analysis & sandboxes – 0xPat blog – Red/purple teamer
https://0xpat.github.io/Malware_development_part_2/
Malware development part 9 - hosting CLR and managed code injection – 0xPat blog – Red/purple teamer
https://0xpat.github.io/Malware_development_part_9/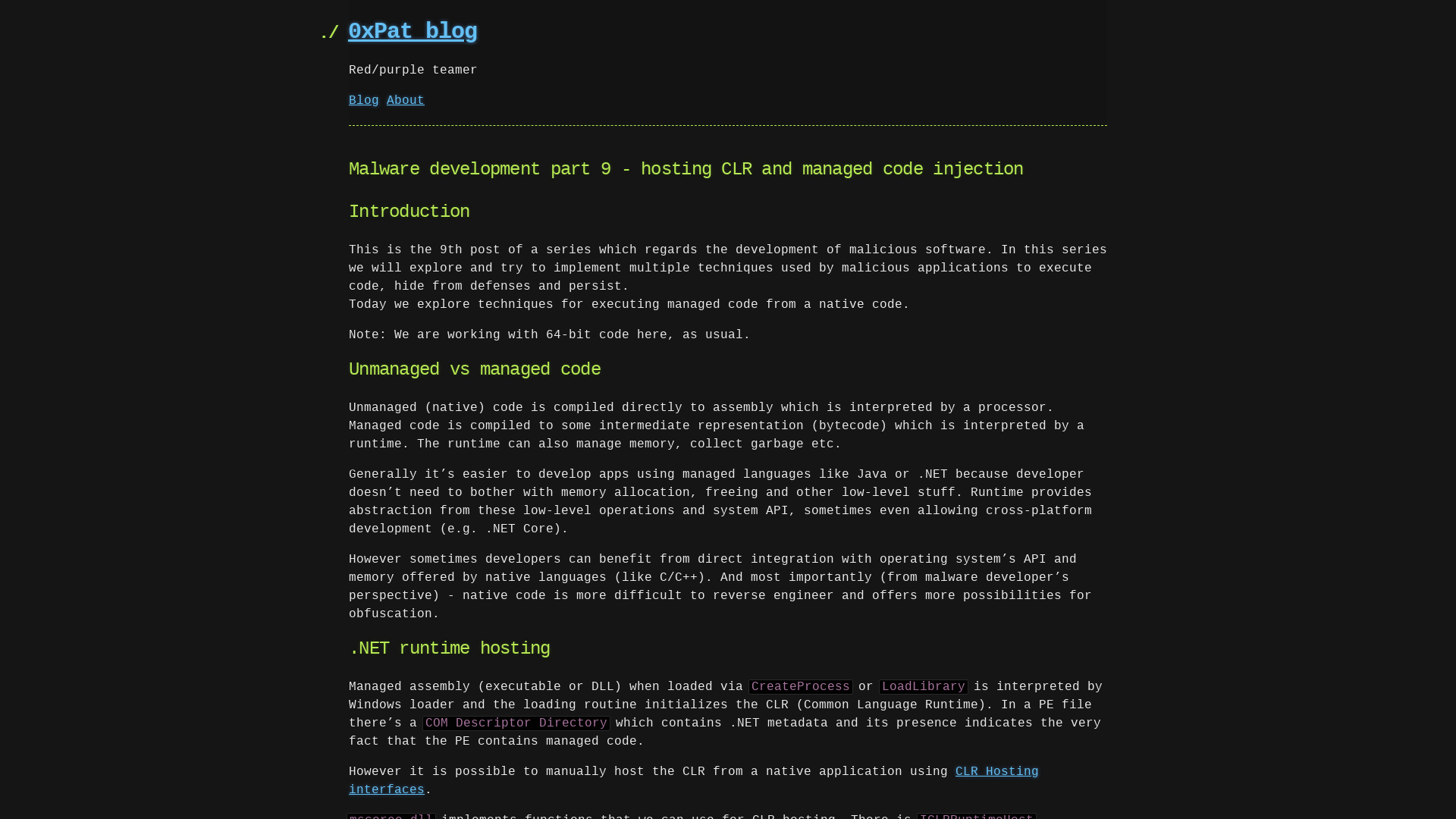
Who is the Network Access Broker ‘Wazawaka?’ – Krebs on Security
https://krebsonsecurity.com/2022/01/who-is-the-network-access-broker-wazawaka/
Iranian intel cyber suite of malware uses open source tools > U.S. Cyber Command > News
https://www.cybercom.mil/Media/News/Article/2897570/iranian-intel-cyber-suite-of-malware-uses-open-source-tools/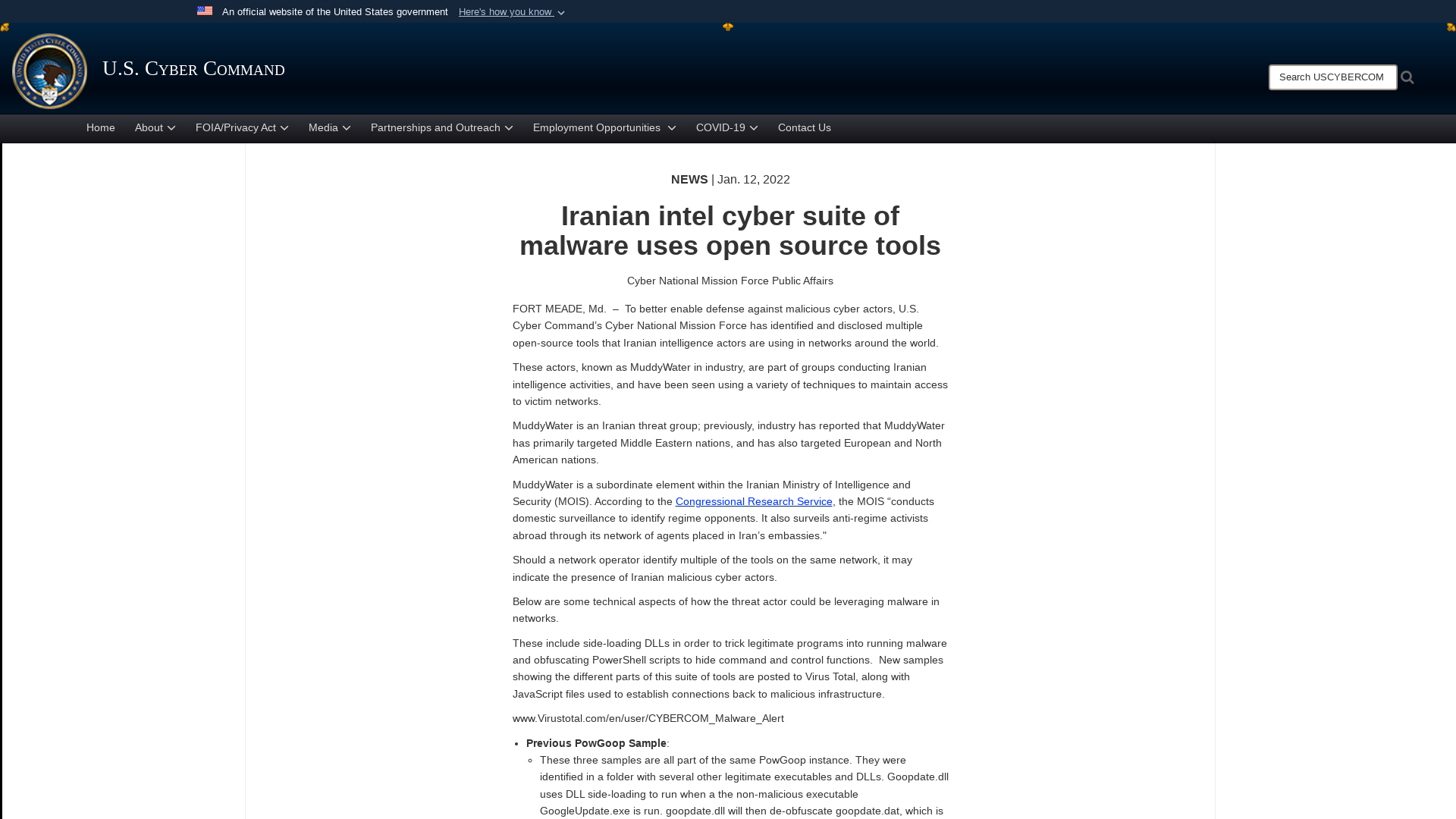
Searching for Deserialization Protection Bypasses in Microsoft Exchange (CVE-2022–21969) | by frycos | Medium
https://medium.com/@frycos/searching-for-deserialization-protection-bypasses-in-microsoft-exchange-cve-2022-21969-bfa38f63a62d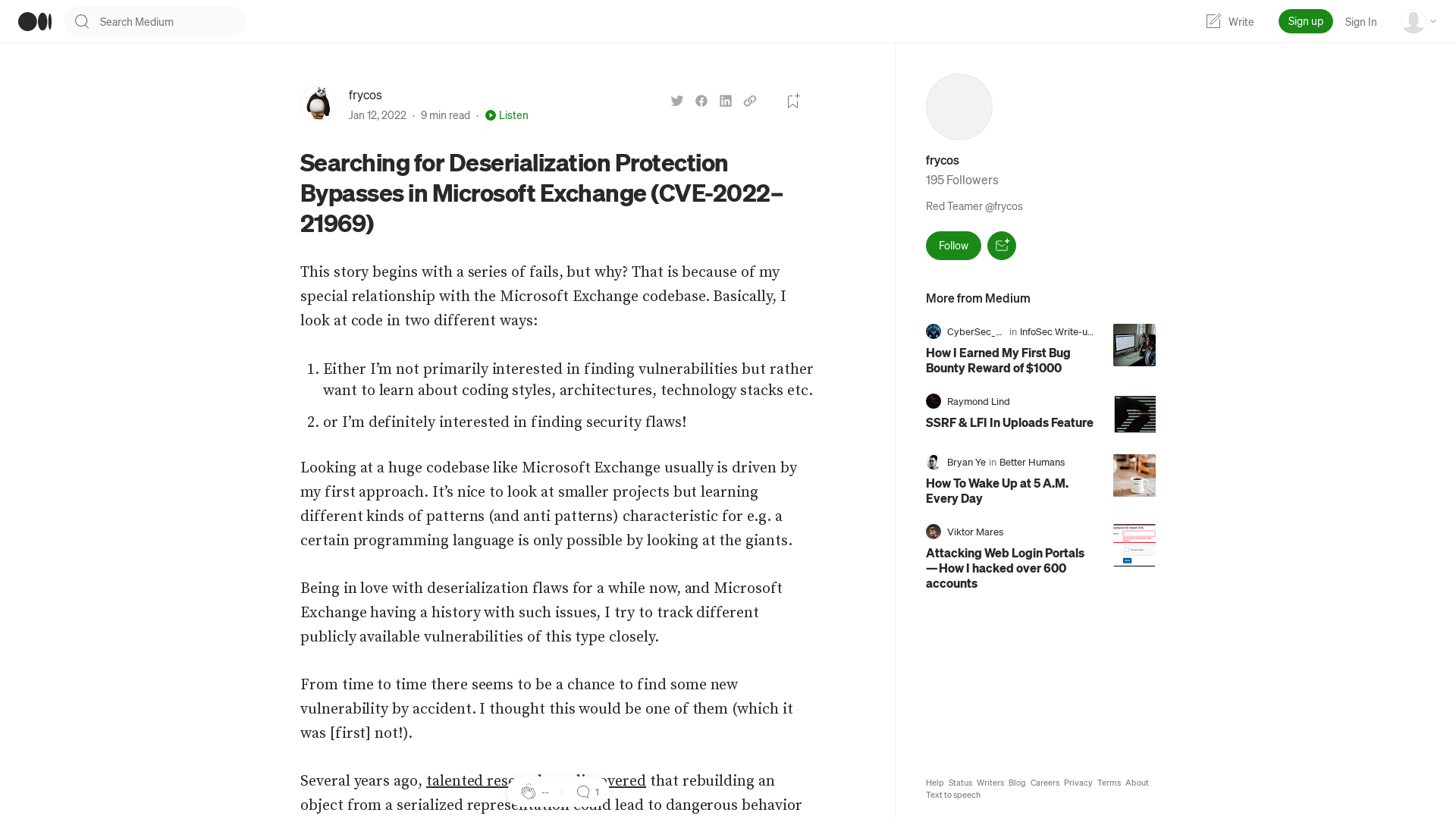
New SysJoker Espionage Malware Targeting Windows, macOS, and Linux Users
https://thehackernews.com/2022/01/new-sysjoker-espionage-malware.html
Antonio Cocomazzi on Twitter: "Windows Defender AV allows Everyone to read the configured exclusions on the system 🤦 reg query "HKLM\SOFTWARE\Microsoft\Windows Defender\Exclusions" /s https://t.co/dpTFwMVRje" / Twitter
https://twitter.com/splinter_code/status/1481073265380581381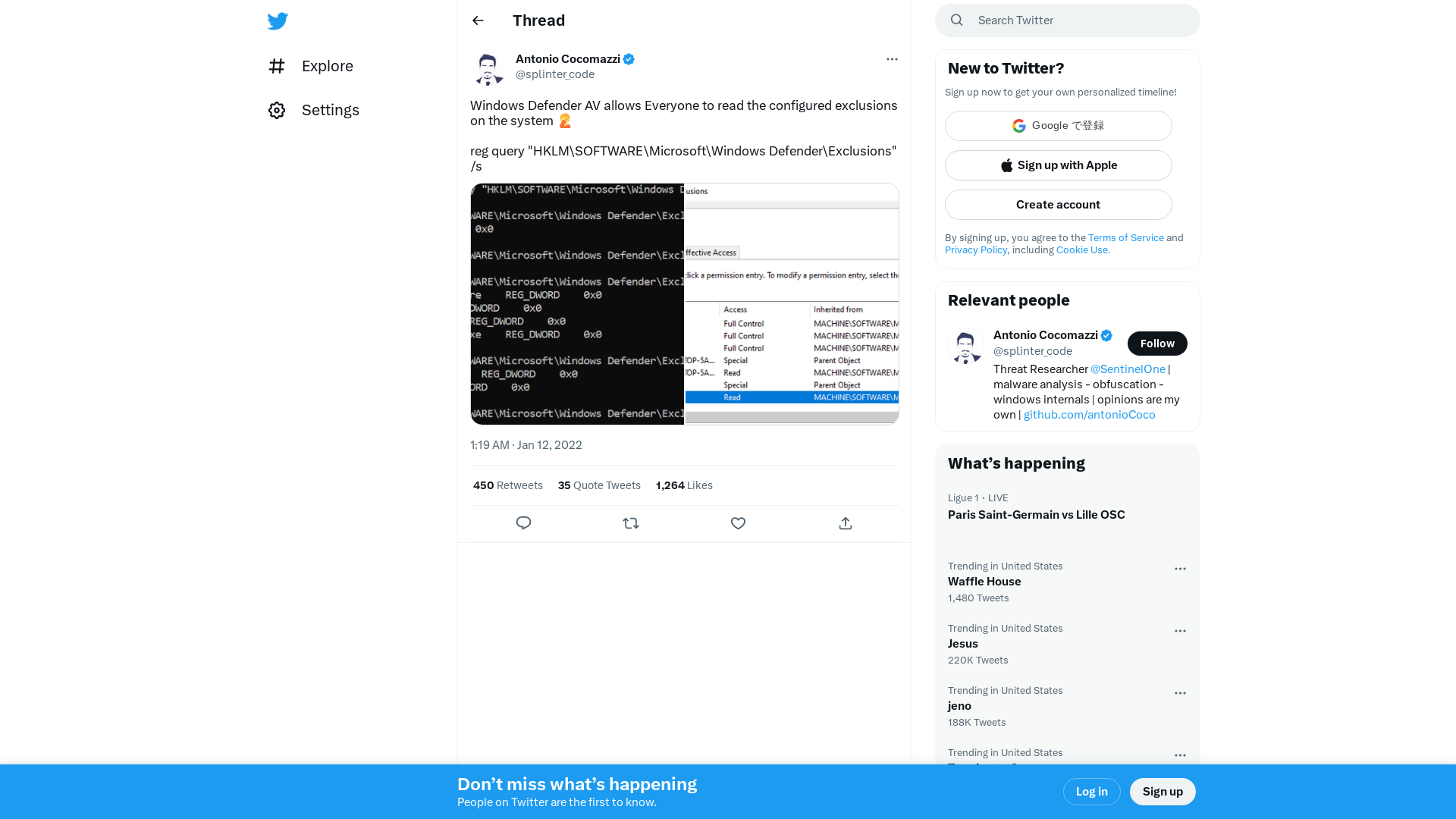
A World to Win on Twitter: "What’s a major problem in your field that is unsolved?" / Twitter
https://twitter.com/davidkaib/status/1480371168326688769
Malware-Traffic-Analysis.net - 2022-01-11 (Tuesday) - Emotet activity
https://www.malware-traffic-analysis.net/2022/01/11/index.html
🇺🇦Evan Kirstel #B2B #TechFluencer on Twitter: "😡 Folks what do you think about #cancelculture? @Clubhouse was the “it” thing in 2021 but has slowly faded. Now I only go to listen to @JTFoxx but #clubhouse cancelled him ‘cause he said his 94 year old father figure / coach recovered from #COVID! Let’s stick to @TwitterSpaces!? https://t.co/bCI2ptfJw3" / Twitter
https://twitter.com/evankirstel/status/1481297270679216138
OceanLotus hackers turn to web archive files to deploy backdoors
https://www.bleepingcomputer.com/news/security/oceanlotus-hackers-turn-to-web-archive-files-to-deploy-backdoors/
CVE-2021-20038 | AttackerKB
https://attackerkb.com/topics/QyXRC1wbvC/cve-2021-20038/rapid7-analysis?fbclid=IwAR1ldORiwotSY0HeF_aLrYra1LuvJk7nlzfWg1HOT8AvnnvBfVcvUE1siTw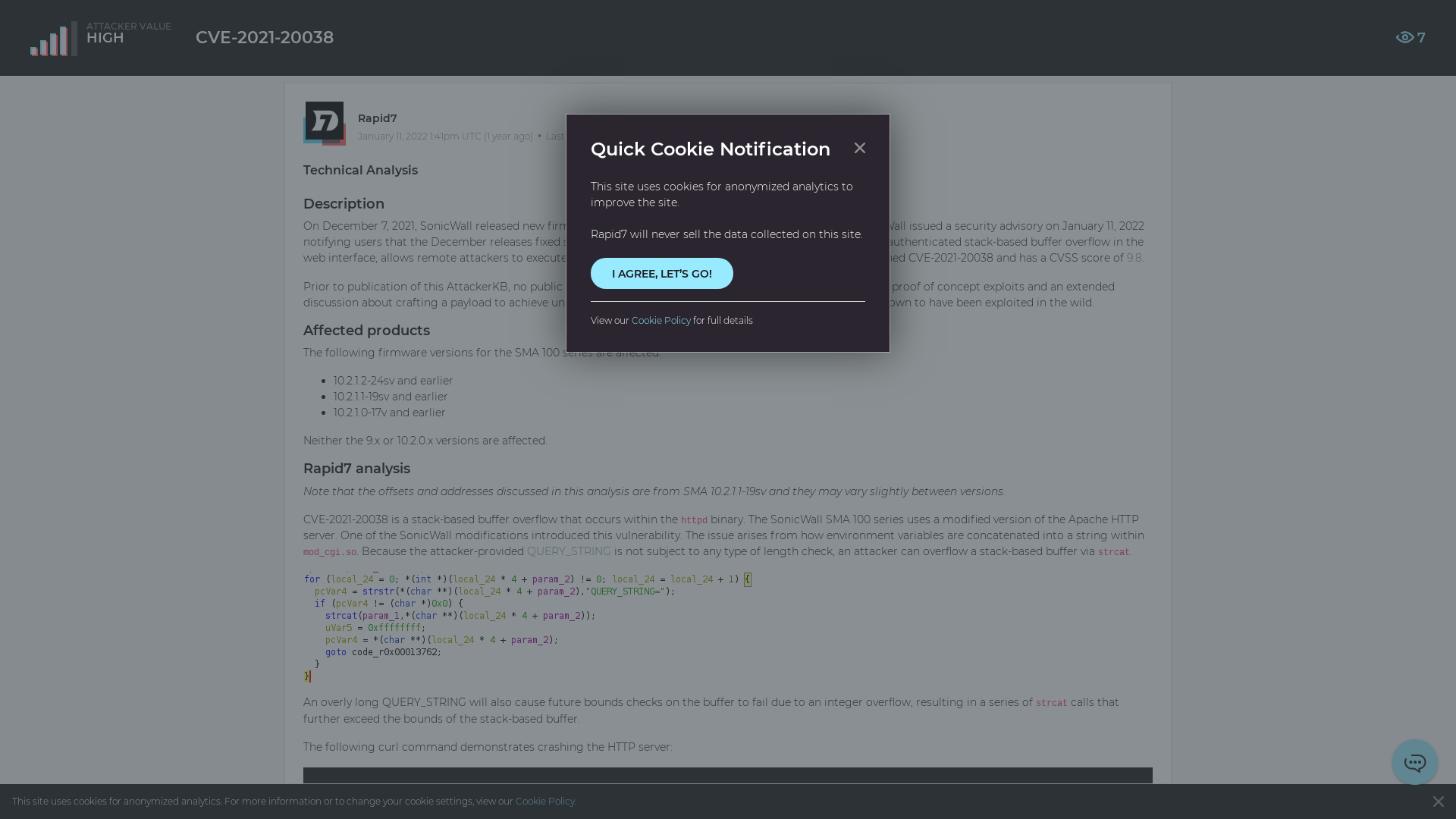
405 Banned
https://urlhaus.abuse.ch/browse/tag/emotet/
Hackers Use Cloud Services to Distribute Nanocore, Netwire, and AsyncRAT Malware
https://thehackernews.com/2022/01/hackers-use-cloud-services-to.html
