Guidance for preventing, detecting, and hunting for exploitation of the Log4j 2 vulnerability - Microsoft Security Blog
https://www.microsoft.com/security/blog/2021/12/11/guidance-for-preventing-detecting-and-hunting-for-cve-2021-44228-log4j-2-exploitation/
Page Not Found | CISA
http://go.usa.gov/xtYHj
Jen🛡Easterly on Twitter: "🛡️ Russian state-sponsored malicious cyber activity is a continuing threat to our critical infrastructure—why we’re working closely w/public & private sector partners to reinforce the importance of vigilance against these threats; read our latest advisory: https://t.co/d0NRcKyDF4 https://t.co/gR86Ti3DcR" / Twitter
https://twitter.com/cisajen/status/1480919948046262274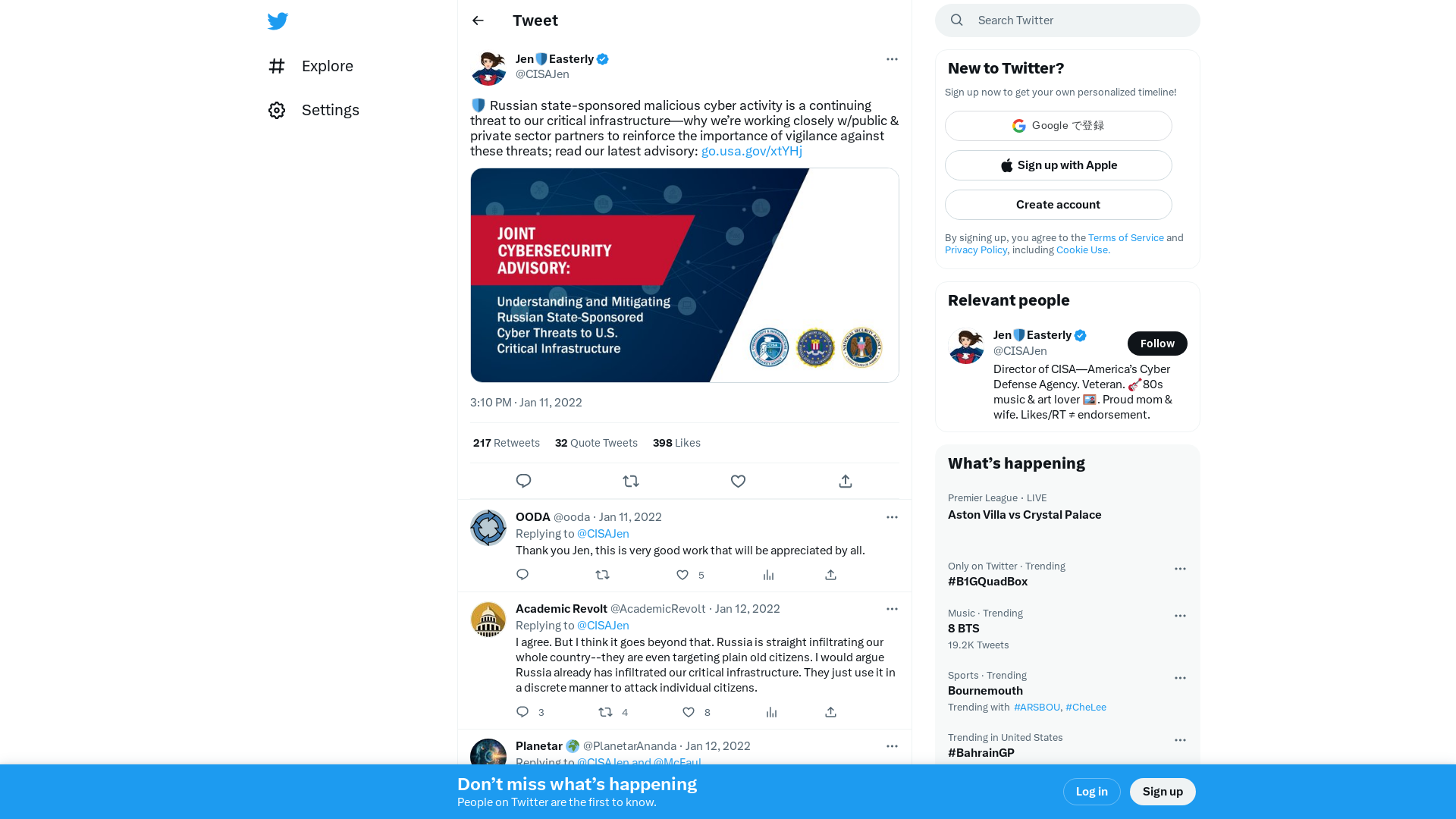
Understanding and Mitigating Russian State-Sponsored Cyber Threats to U.S. Critical Infrastructure | CISA
https://www.cisa.gov/uscert/ncas/alerts/aa22-011a
Malware-analysis-and-Reverse-engineering/NightSky_Ransomware–just_a_Rook_RW_fork_in_VMProtect_suit.md at main · Dump-GUY/Malware-analysis-and-Reverse-engineering · GitHub
https://github.com/Dump-GUY/Malware-analysis-and-Reverse-engineering/blob/main/NightSky_Ransomware%E2%80%93just_a_Rook_RW_fork_in_VMProtect_suit/NightSky_Ransomware%E2%80%93just_a_Rook_RW_fork_in_VMProtect_suit.md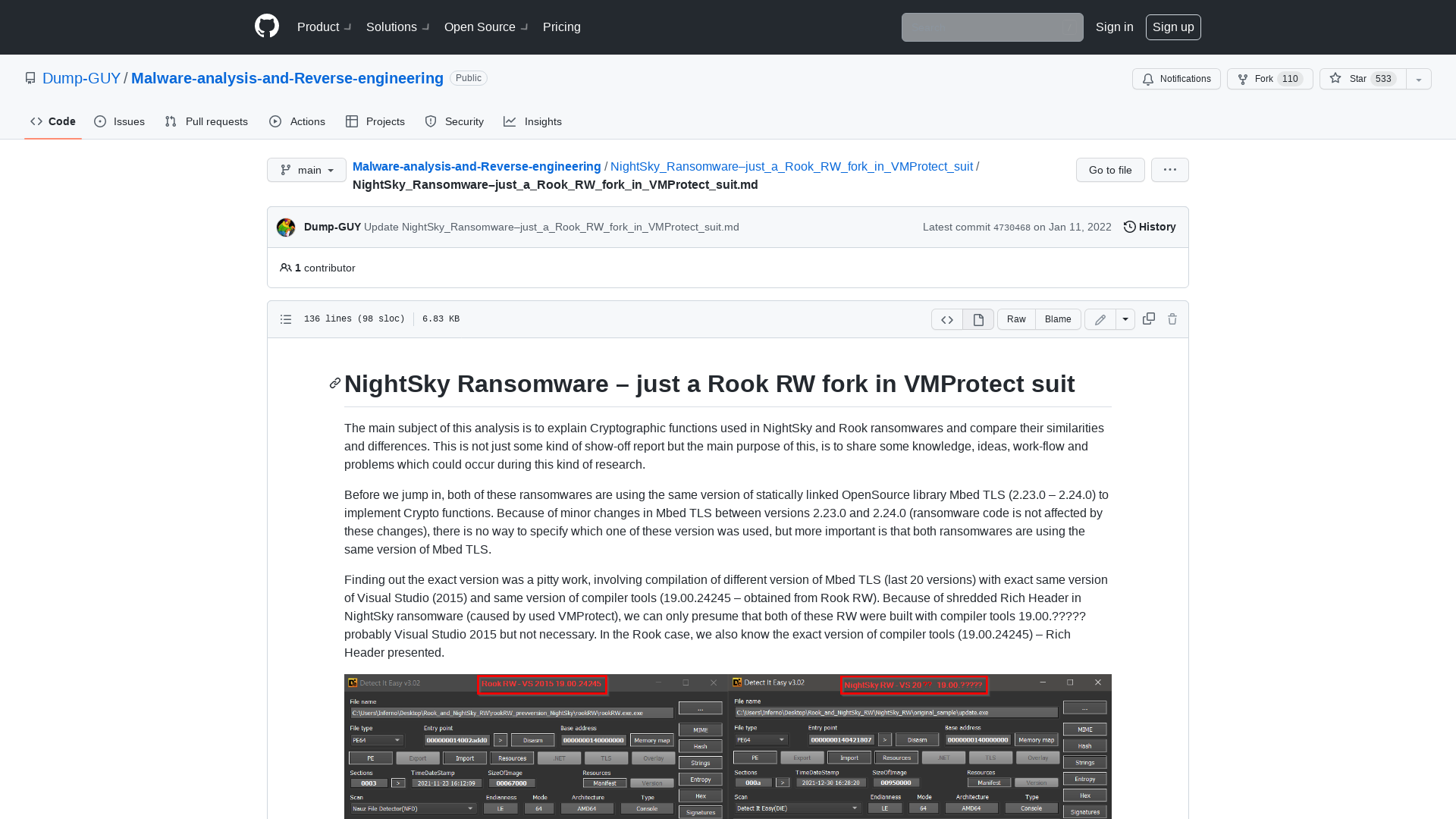
APT35 exploits Log4j vulnerability to distribute new modular PowerShell toolkit - Check Point Research
https://research.checkpoint.com/2022/apt35-exploits-log4j-vulnerability-to-distribute-new-modular-powershell-toolkit/
Page Not Found | Armor Cybersecurity
https://www.armor.com/resources/threat-intelligence/the-evolution-of-doppel-spider-from-bitpaymer-to-grief-ransomware/
How the Pentagon enlisted ethical hackers amid the Log4j crisis - The Record from Recorded Future News
https://therecord.media/how-the-pentagon-enlisted-ethical-hackers-amid-the-log4j-crisis/
JOINT_CSA_UNDERSTANDING_MITIGATING_RUSSIAN_CYBER_THREATS_TO_US_CRITICAL_INFRASTRUCTURE_20220111.PDF
https://media.defense.gov/2022/Jan/11/2002919950/-1/-1/1/JOINT_CSA_UNDERSTANDING_MITIGATING_RUSSIAN_CYBER_THREATS_TO_US_CRITICAL_INFRASTRUCTURE_20220111.PDF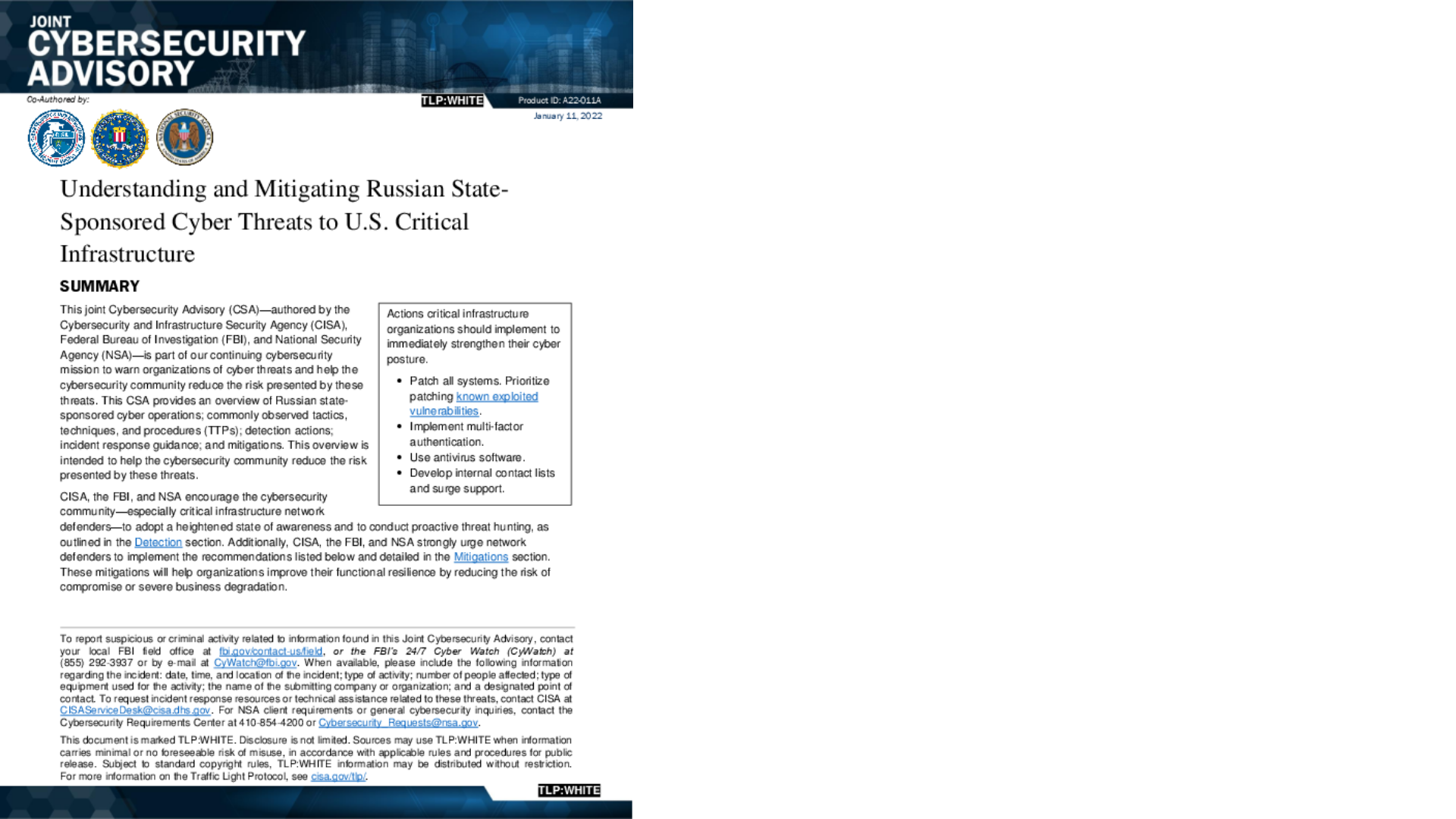
Signed kernel drivers – Unguarded gateway to Windows’ core | WeLiveSecurity
https://www.welivesecurity.com/2022/01/11/signed-kernel-drivers-unguarded-gateway-windows-core/
Exploiting URL Parsing Confusion | Claroty
https://claroty.com/2022/01/10/blog-research-exploiting-url-parsing-confusion/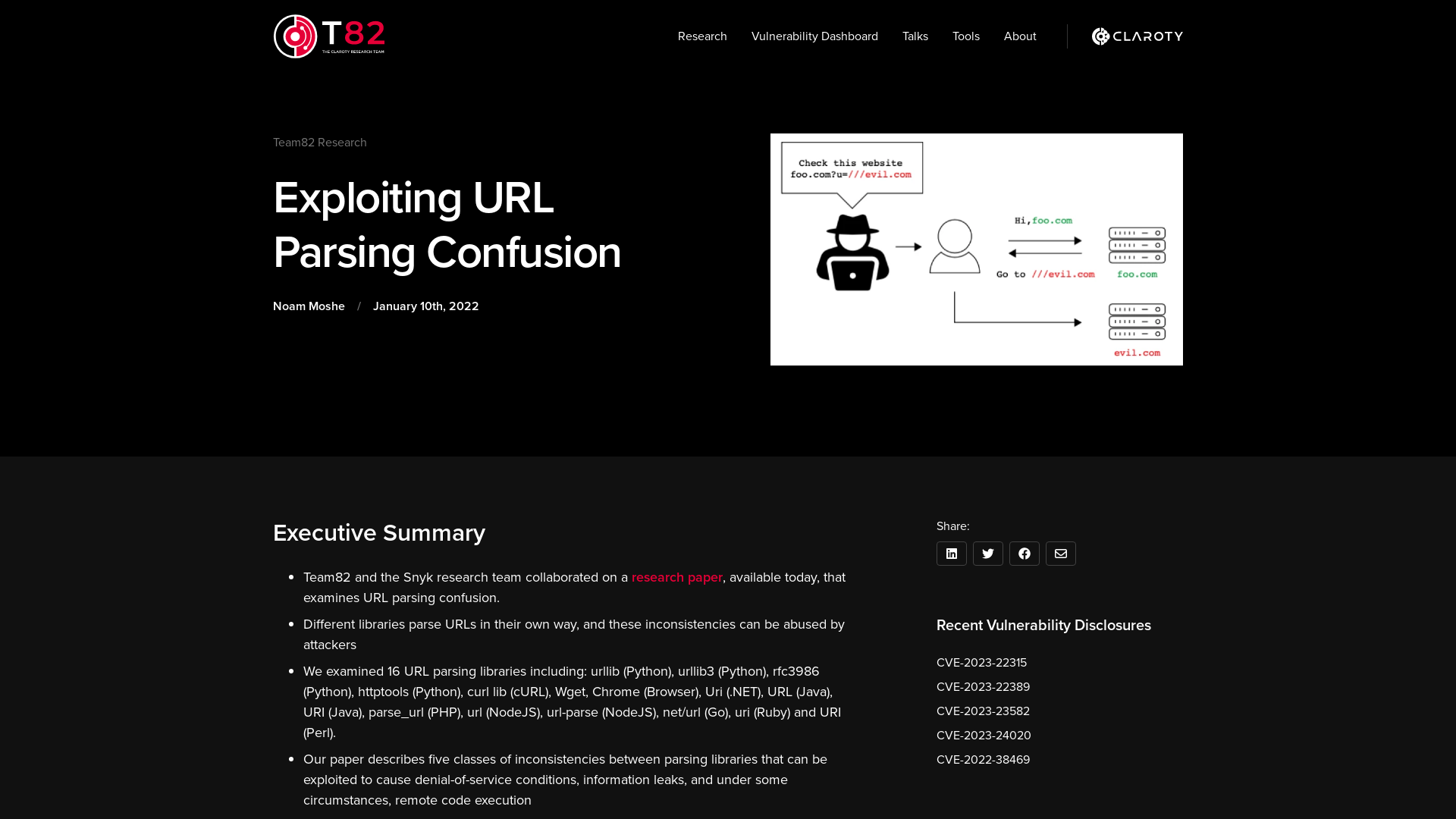
Pirates of the Metaverse 🔛 FLOW on Twitter: "🚨DEGENS🚨 This is your captain speaking. I hope you're ready to have your mind blown... After this post gets 300 RETWEETS, we drop the first MAJOR reveal and share some booty with the crew Turn those tweet alerts on..." / Twitter
https://twitter.com/PiratesMeta/status/1480917838470778882
CVE-2021-20038..42: SonicWall SMA 100 Multiple Vulnerabilities (FIXED) | Rapid7 Blog
https://www.rapid7.com/blog/post/2022/01/11/cve-2021-20038-42-sonicwall-sma-100-multiple-vulnerabilities-fixed-2/
Triage | Behavioral Report
https://tria.ge/220111-xwczmaggf8/behavioral2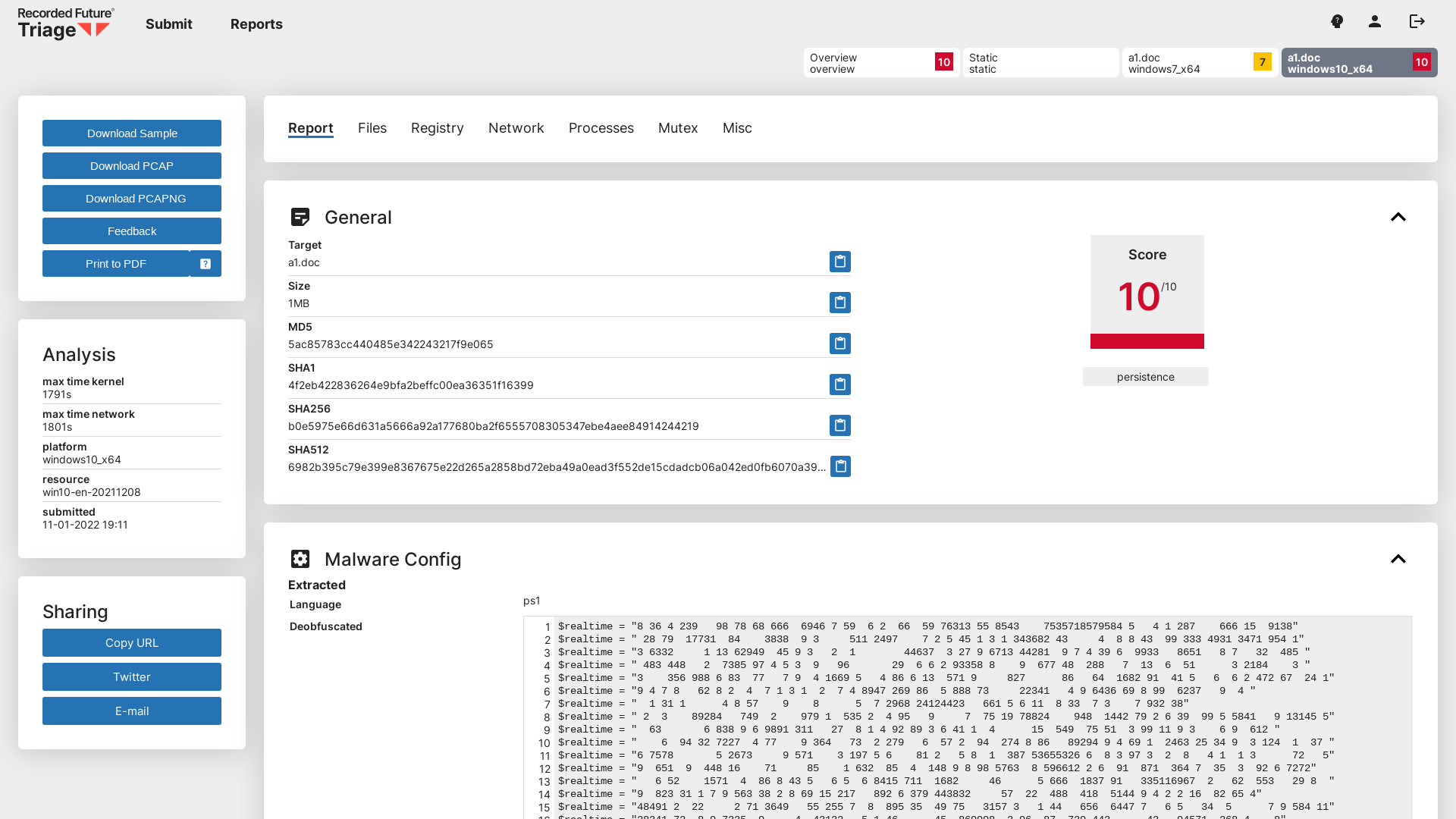
Max_Malyutin on Twitter: "#Emotet is here🧟♂️ New Year 2022 ❗️ MalDoc XLS macro ver 4.0 Auto_Open Exec Flow #DFIR #BlueTeam Excel > Rundll32 > Rundll32 > Rundll32 rundll32.exe ..\sun.ocx,D"&"l"&"lR"&"egister"&"Serve"&"r Thanks, @pr0xylife 💪 https://t.co/xCnPJT9f8O" / Twitter
https://twitter.com/Max_Mal_/status/1480859608814129153
Signal >> Blog >> New year, new CEO
https://signal.org/blog/new-year-new-ceo/
proxylife on Twitter: "#Emotet is back :) hxxp://djokoproperties.com/w0fxf/D99XJ7gfsYlFF/ @executemalware @James_inthe_box @ffforward @ankit_anubhav @Max_Mal_ @Cryptolaemus1 @Myrtus0x0 @fr0s7_ @JAMESWT_MHT @1ZRR4H" / Twitter
https://twitter.com/pr0xylife/status/1480850321077383170
Domain Escalation – sAMAccountName Spoofing – Penetration Testing Lab
https://pentestlab.blog/2022/01/10/domain-escalation-samaccountname-spoofing/
ShadowCoerce | Pentest Laboratories
https://pentestlaboratories.com/2022/01/11/shadowcoerce/
Signal CEO Resigns, WhatsApp Co-Founder Takes Over as Interim CEO
https://thehackernews.com/2022/01/signal-ceo-resigns-whatsapp-co-founder.html
CVE-2021-20039 | AttackerKB
https://attackerkb.com/topics/9szJhq46lw/cve-2021-20039/rapid7-analysis?referrer=twitter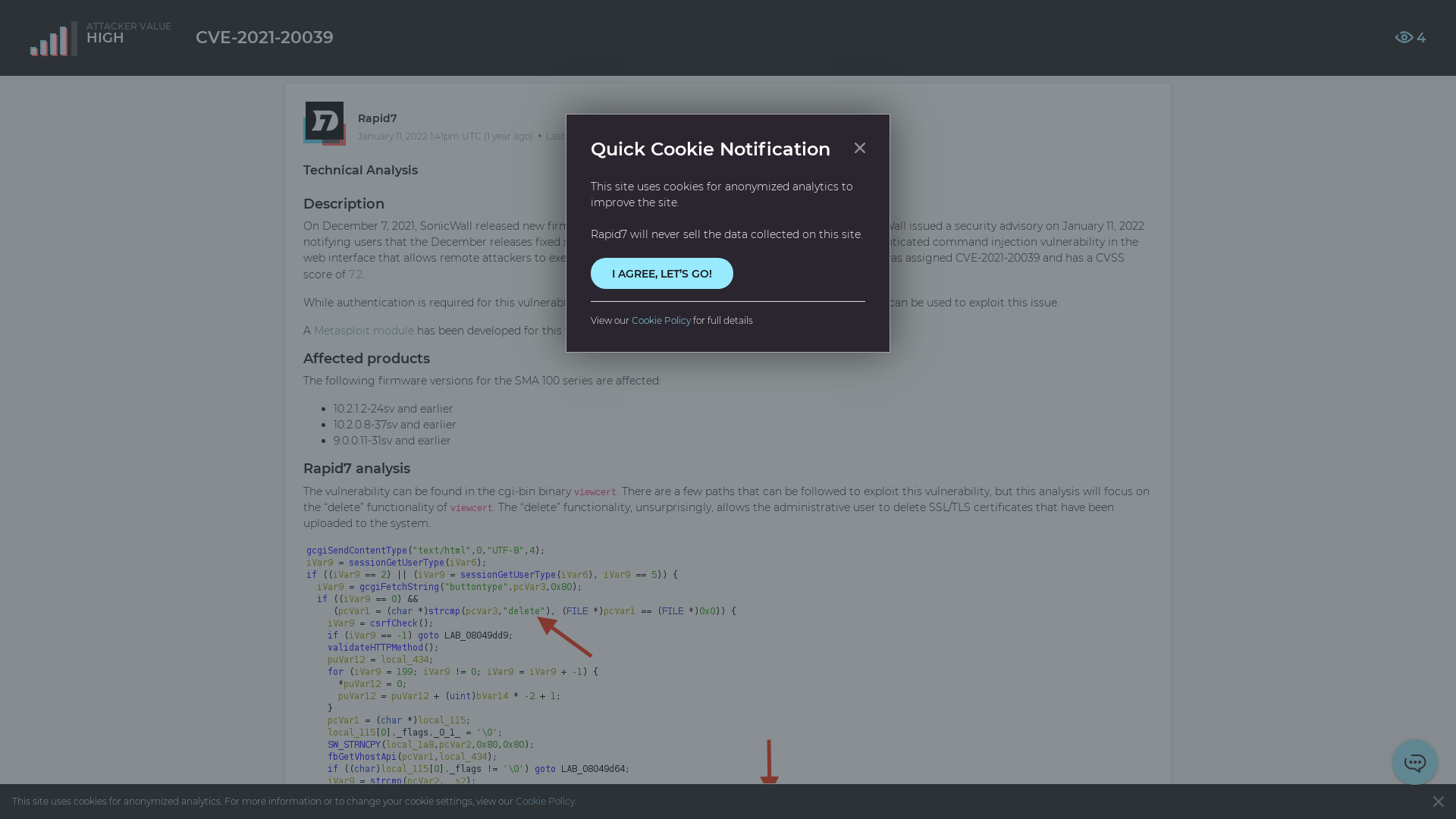
Microsoft Security Intelligence on Twitter: "We have observed a China-based ransomware operator that we’re tracking as DEV-0401 exploiting the CVE-2021-44228 vulnerability in Log4j 2 (aka #log4shell) targeting internet-facing systems running VMWare Horizon. https://t.co/6GOdRwRTjk" / Twitter
https://twitter.com/msftsecintel/status/1480730559739359233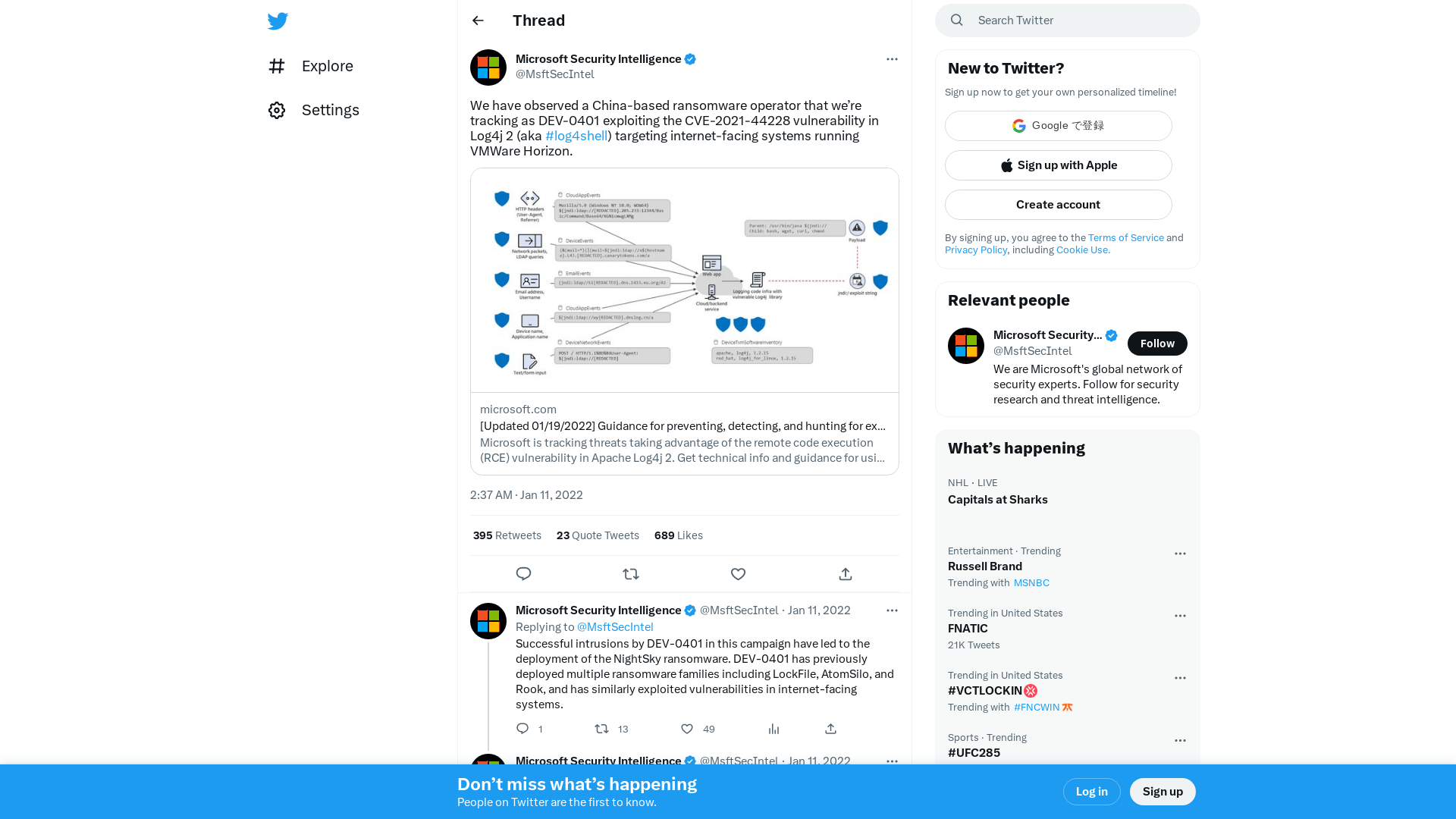
2112.15561.pdf
https://arxiv.org/pdf/2112.15561.pdf
SΛMΛNTHΛ on Twitter: "give this book a title https://t.co/Wxg7lt3N37" / Twitter
https://twitter.com/_uid0/status/1479505275723792385
New SysJoker backdoor targets Windows, macOS, and Linux
https://www.bleepingcomputer.com/news/security/new-sysjocker-backdoor-targets-windows-macos-and-linux/
Signed DLL campaigns as a service | by Jason Reaves | Walmart Global Tech Blog | Medium
https://medium.com/walmartglobaltech/signed-dll-campaigns-as-a-service-7760ac676489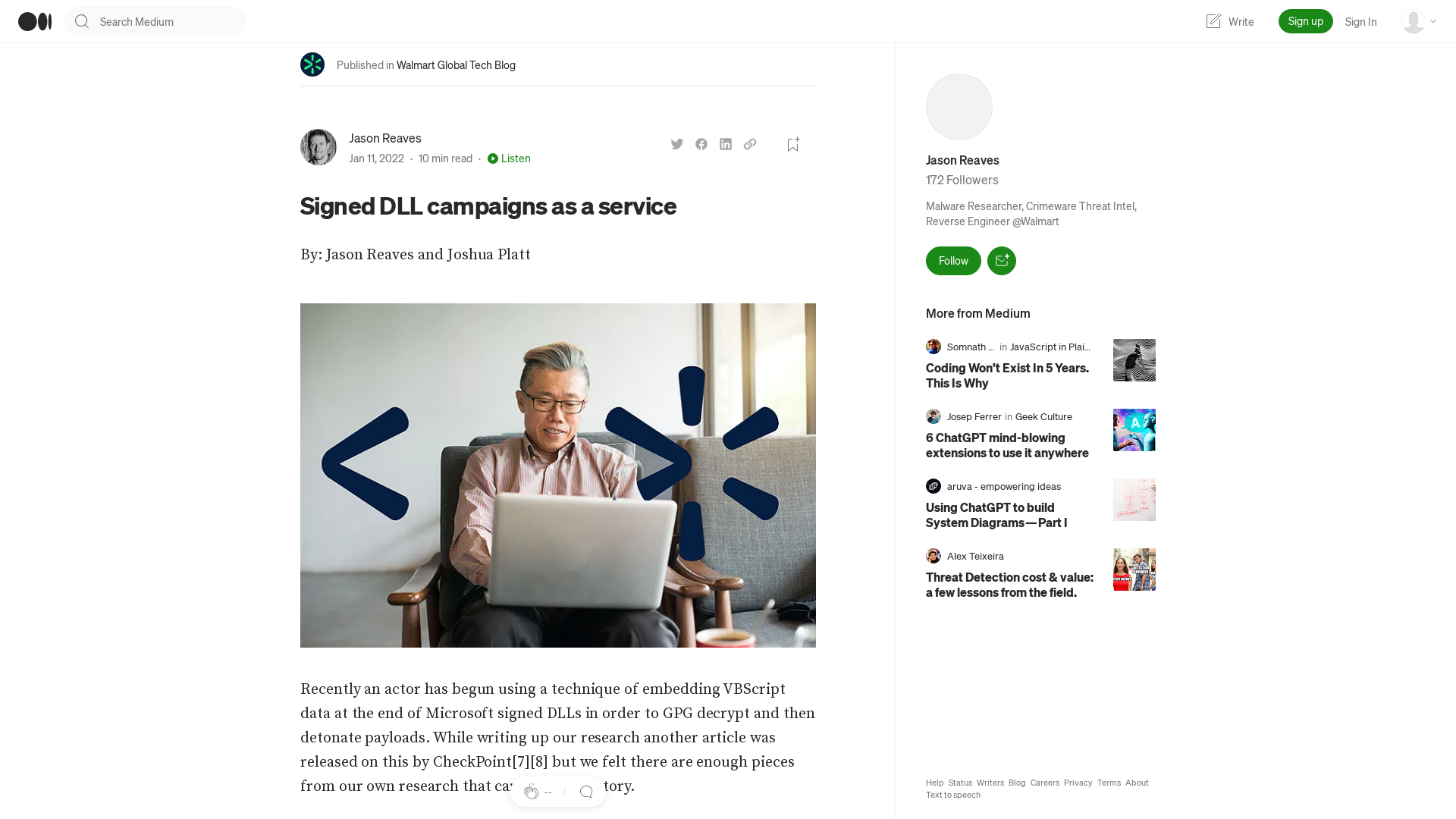
Tweet / Twitter
https://twitter.com/th3_protoCOL/status/1480621526764322817
APT_REPORT/summary/2022 at master · blackorbird/APT_REPORT · GitHub
https://github.com/blackorbird/APT_REPORT/tree/master/summary/2022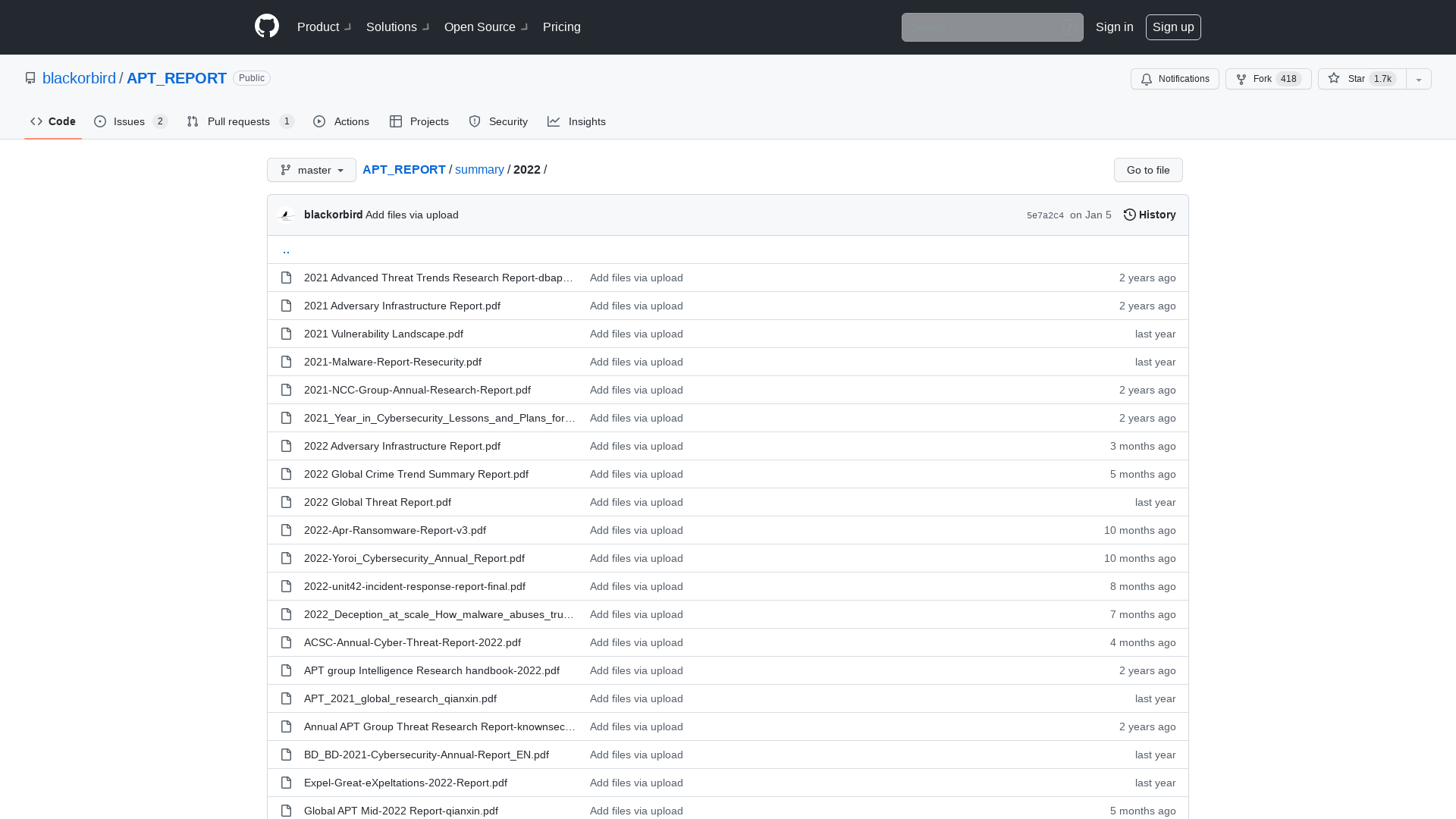
Ned Pyle on Twitter: "Windows Server 2016 mainstream support ends today." / Twitter
https://twitter.com/NerdPyle/status/1480948835551567878