New KadNap botnet hijacks ASUS routers to fuel cybercrime proxy network
https://www.bleepingcomputer.com/news/security/new-kadnap-botnet-hijacks-asus-routers-to-fuel-cybercrime-proxy-network/
An iPhone-hacking toolkit used by Russian spies likely came from U.S military contractor | TechCrunch
https://techcrunch.com/2026/03/09/an-iphone-hacking-toolkit-used-by-russian-spies-likely-came-from-u-s-military-contractor/
GTIG AI Threat Tracker: Advances in Threat Actor Usage of AI Tools | Google Cloud Blog
https://bit.ly/3N9n4hu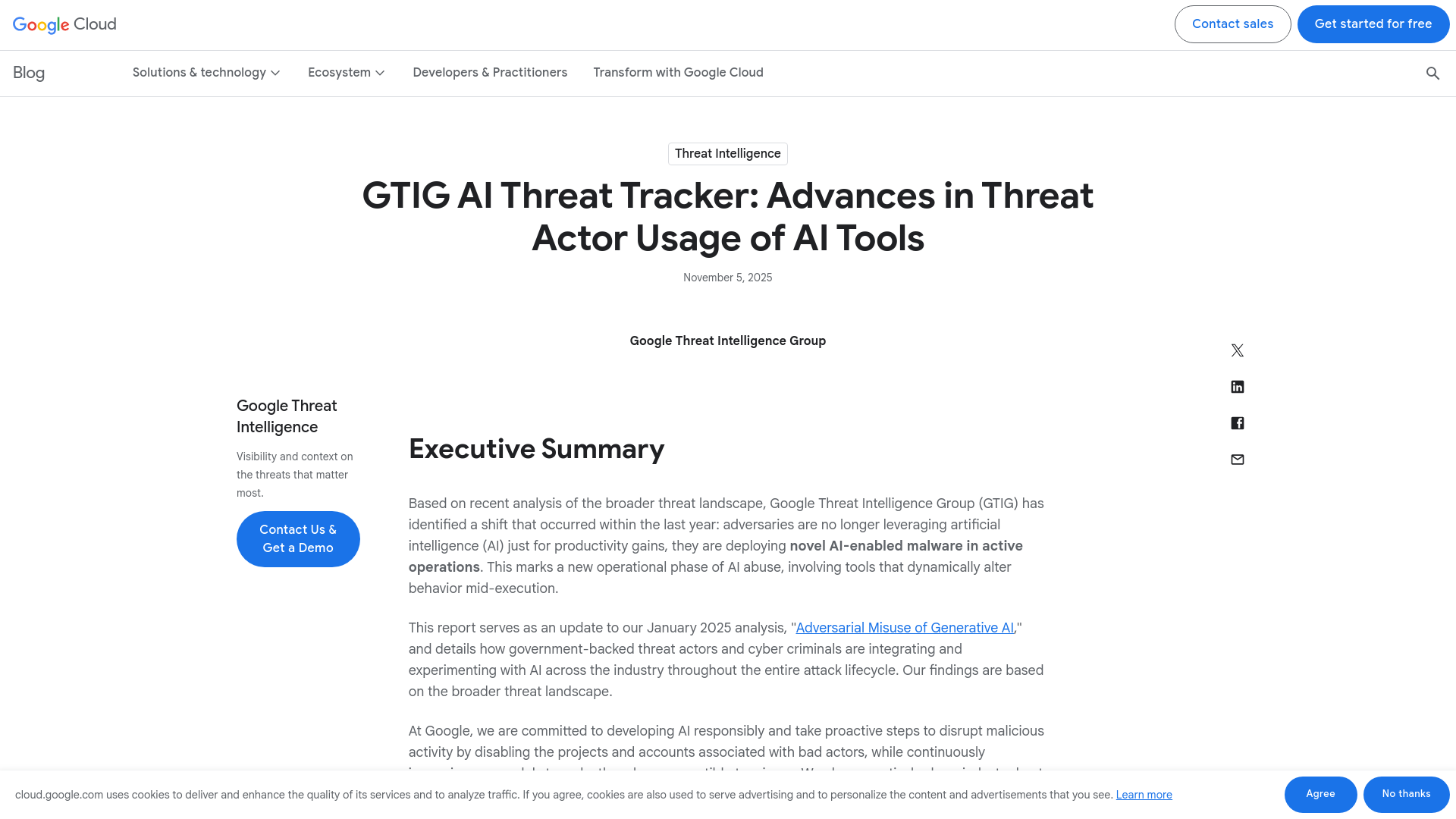
Release v.0.9.205 · trustedsec/Titanis · GitHub
https://github.com/trustedsec/Titanis/releases/tag/v0.9.205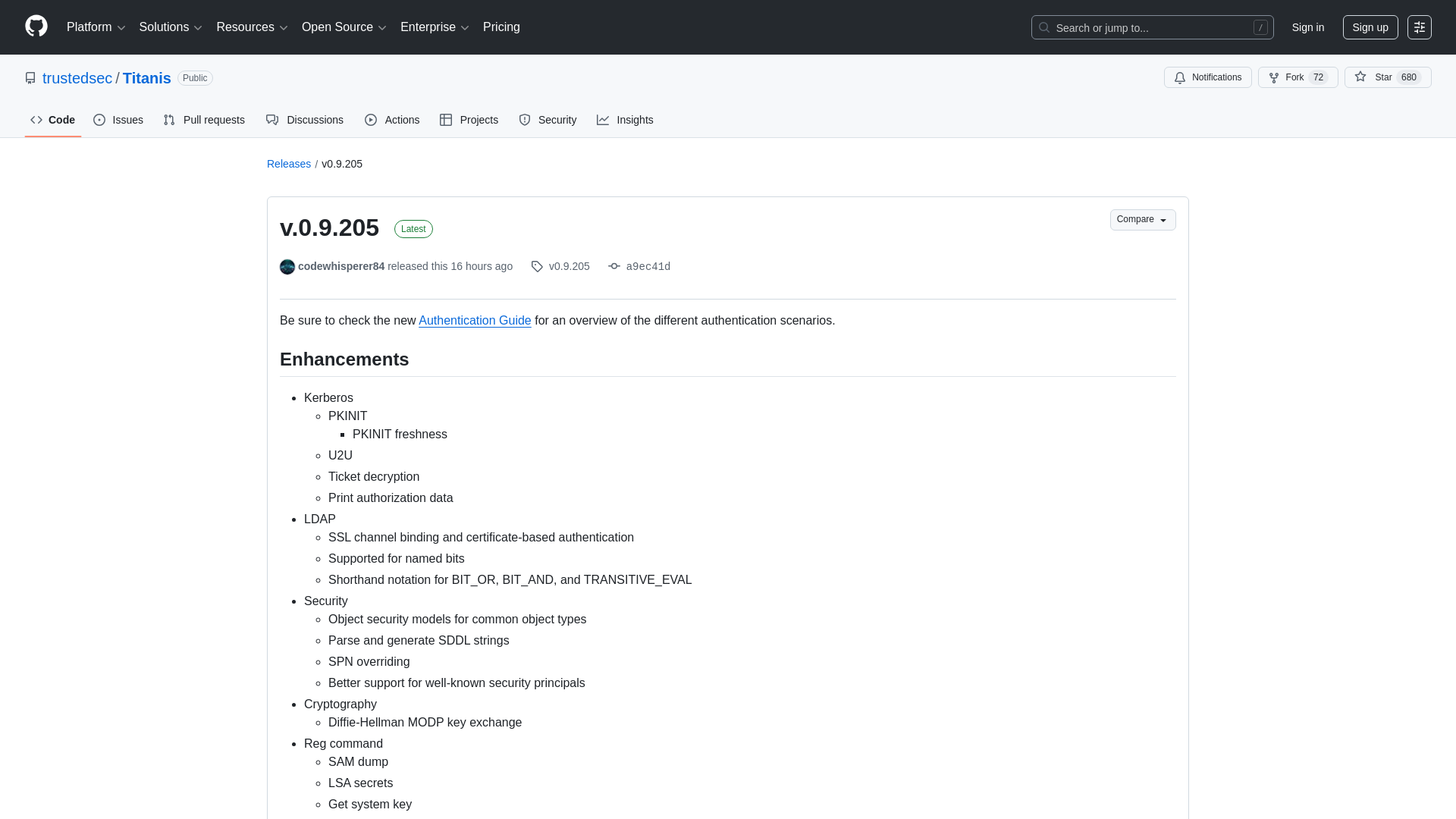
VirusTotal - File - ff6e13de81fcfda3a6bca573c6f23ed5150a233f3c4c0ff6f6a81fffa0583377
https://www.virustotal.com/gui/file/ff6e13de81fcfda3a6bca573c6f23ed5150a233f3c4c0ff6f6a81fffa0583377/behavior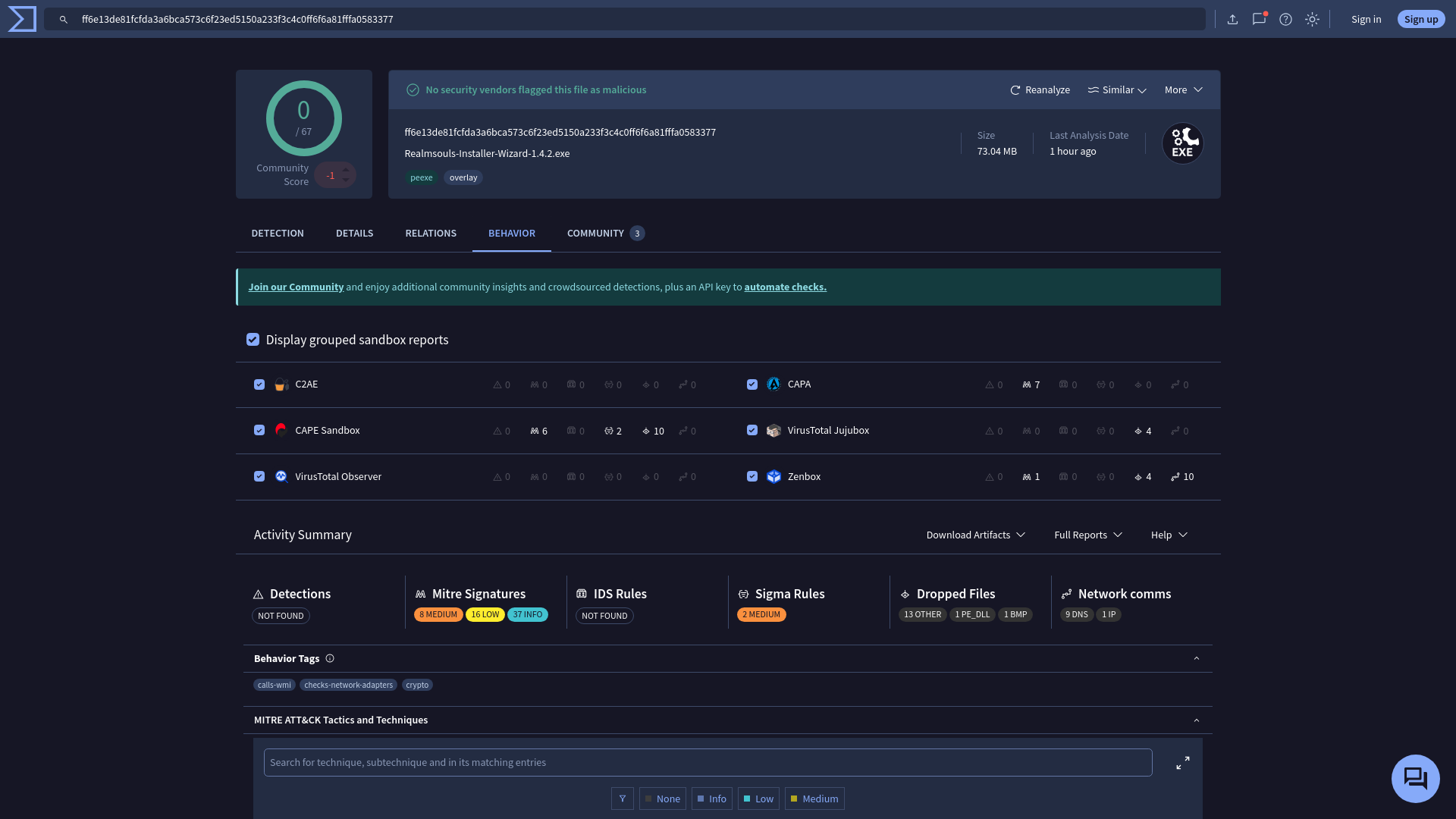
[Research] LLVM based VMProtect Devirtualization: Part 1 (EN) - hackyboiz
https://hackyboiz.github.io/2025/09/11/banda/LLVM_based_VMP/en/![[Research] LLVM based VMProtect Devirtualization: Part 1 (EN) - hackyboiz](/image/screenshot/00b644776e2c4c9e244b50fc307126b2.png)
Polish cyber police busts gang of alleged teen DDoS peddlers • The Register
http://dlvr.it/TRPXCG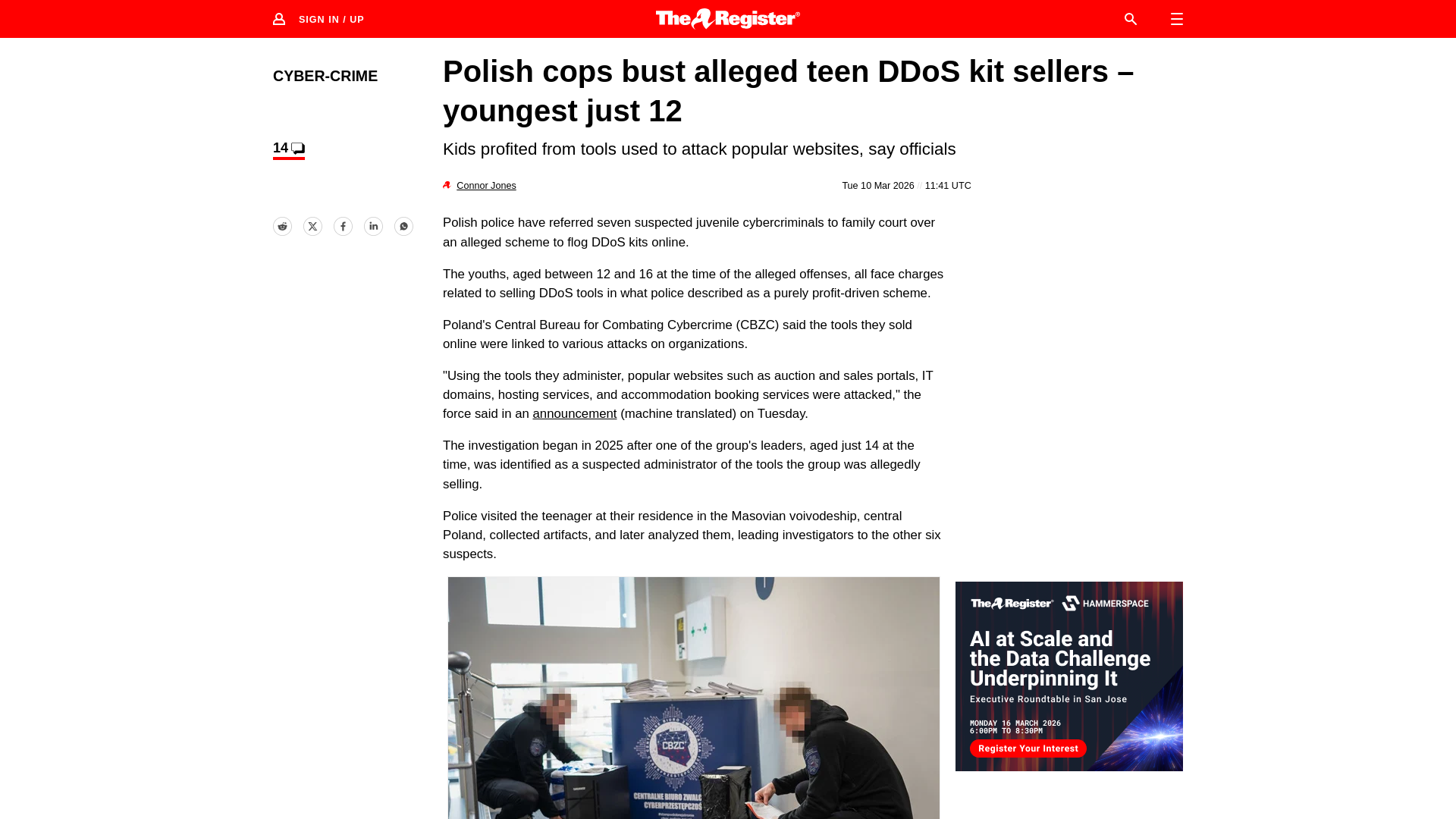
Cybersecurity’s Need for Speed & Where To Find It
https://www.philvenables.com/post/cybersecurity-s-need-for-speed-where-to-find-it
Internet Infrastructure TLD .arpa Abused in Phishing Attacks - SecurityWeek
https://www.securityweek.com/internet-infrastructure-tld-arpa-abused-in-phishing-attacks/
GitHub - HavocFramework/Havoc: The Havoc Framework
https://github.com/HavocFramework/Havoc
What Windows Server 2025 Quietly Did to Your NTLM Relay – Decoder's Blog
https://decoder.cloud/2026/02/25/what-windows-server-2025-quietly-did-to-your-ntlm-relay/
Reverse Engineering for Beginners | Learn the Basics Step-by-Step
https://www.networkintelligence.ai/blogs/reverse-engineering-for-beginners-xor-encryption-windows-x64/
Reverse engineering of Apple's iOS 0-click CVE-2025-43300: 2 bytes that make size matter - Quarkslab's blog
https://blog.quarkslab.com/patch-analysis-of-Apple-iOS-CVE-2025-43300.html
Censys Unveils Censys ARC, Formalizing Its Global Internet Threat Research Team
https://www.prnewswire.com/news-releases/censys-unveils-censys-arc-formalizing-its-global-internet-threat-research-team-302707258.html
APT28 hackers deploy customized variant of Covenant open-source tool
https://www.bleepingcomputer.com/news/security/apt28-hackers-deploy-customized-variant-of-covenant-open-source-tool/