New AirSnitch attack breaks Wi-Fi encryption in homes, offices, and enterprises - Ars Technica
https://arstechnica.com/security/2026/02/new-airsnitch-attack-breaks-wi-fi-encryption-in-homes-offices-and-enterprises/
Kali Linux Integrates Claude AI for Penetration Testing via Model Context Protocol
https://cybersecuritynews.com/kali-linux-integrates-claude-ai/
PlugX Meeting Invitation via MSBuild and GDATA
https://lab52.io/blog/plugx-meeting-invitation-via-msbuild-and-gdata/
Abusing Windows File Explorer and WebDAV for Malware Delivery
https://cofense.com/blog/abusing-windows-file-explorer-and-webdav-for-malware-delivery
What Windows Server 2025 Quietly Did to Your NTLM Relay – Decoder's Blog
https://decoder.cloud/2026/02/25/what-windows-server-2025-quietly-did-to-your-ntlm-relay/
Kali Linux Introduces Claude AI for Automated Penetration Testing Using Model Context Protocol
https://gbhackers.com/kali-linux-introduces-claude-ai-for-automated-penetration-testing/
Caught in the Hook: RCE and API Token Exfiltration Through Claude Code Project Files | CVE-2025-59536 | CVE-2026-21852 - Check Point Research
https://research.checkpoint.com/2026/rce-and-api-token-exfiltration-through-claude-code-project-files-cve-2025-59536/
Developer-targeting campaign using malicious Next.js repositories | Microsoft Security Blog
https://www.microsoft.com/en-us/security/blog/2026/02/24/c2-developer-targeting-campaign/
Chinese cyberspies breached dozens of telecom firms, govt agencies
https://www.bleepingcomputer.com/news/security/chinese-cyberspies-breached-dozens-of-telecom-firms-govt-agencies/
Critical Cisco SD-WAN 0-Day Vulnerability Exploited Since 2023 to Gain Root Access
https://cybersecuritynews.com/cisco-sd-wan-0-day-vulnerability/
Tracking DPRK operator IPs over time | kmsec.uk
https://kmsec.uk/blog/dprk-opsec-3/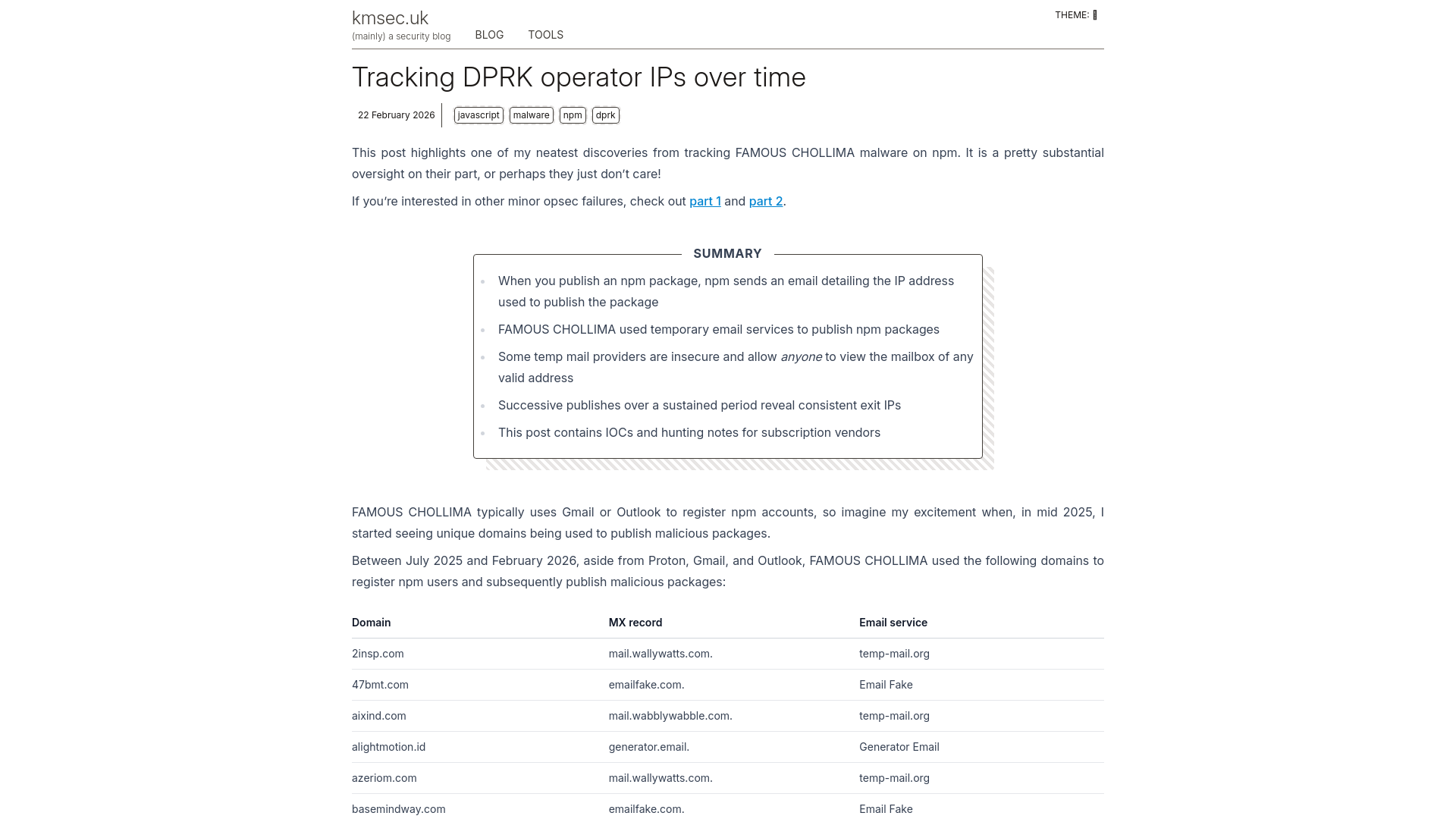
TP-Link Tapo C200: Hardcoded Keys, Buffer Overflows and Privacy in the Era of AI Assisted Reverse Engineering | evilsocket
https://evilsocket.net/2025/12/18/TP-Link-Tapo-C200-Hardcoded-Keys-Buffer-Overflows-and-Privacy-in-the-Era-of-AI-Assisted-Reverse-Engineering/
Critical Juniper Networks PTX flaw allows full router takeover
https://www.bleepingcomputer.com/news/security/critical-juniper-networks-ptx-flaw-allows-full-router-takeover/