Google says hackers are abusing Gemini AI for all attacks stages
https://www.bleepingcomputer.com/news/security/google-says-hackers-are-abusing-gemini-ai-for-all-attacks-stages/
Bypassing Administrator Protection by Abusing UI Access - Project Zero
https://projectzero.google/2026/02/windows-administrator-protection.html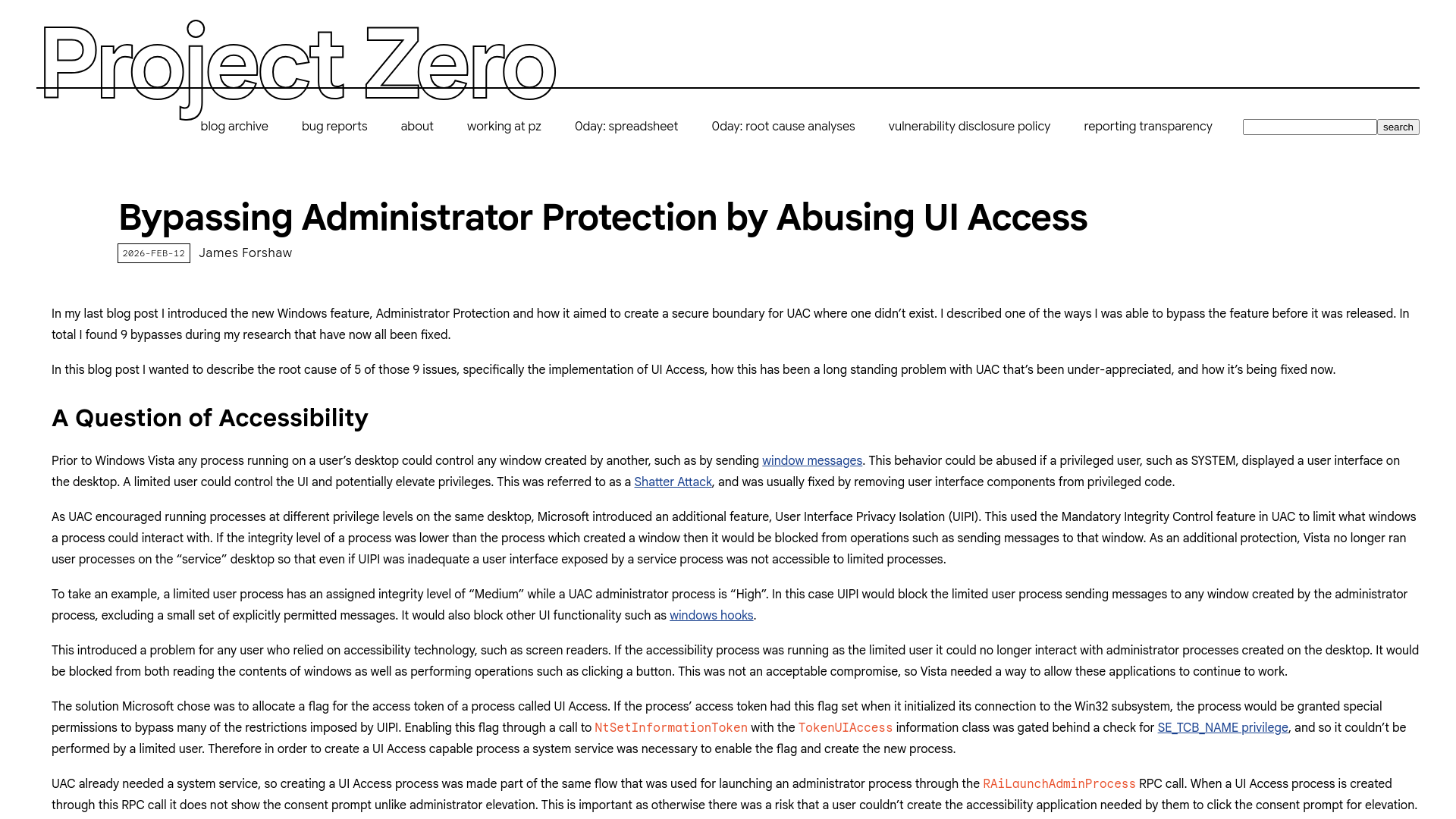
Apple fixes zero-day flaw used in 'extremely sophisticated' attacks
https://www.bleepingcomputer.com/news/security/apple-fixes-zero-day-flaw-used-in-extremely-sophisticated-attacks/
Log in to X / X
https://x.com/rx
Bypass PAC in JIT - CVE-2024-27834 · GitHub
https://gist.github.com/WHW0x455/3c21930d916c74733e8701f397c5660d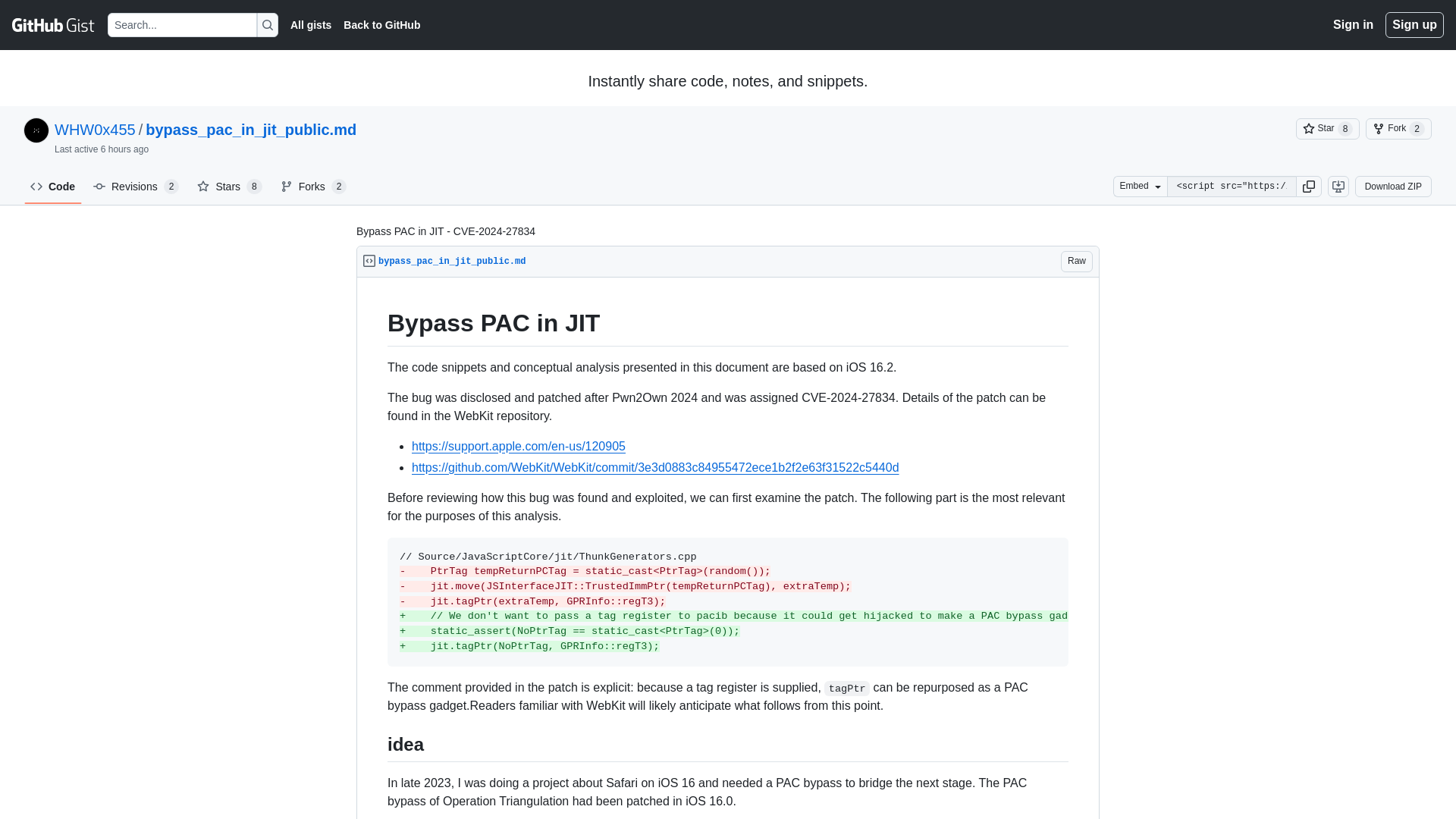
Microsoft Office Word 0-day Vulnerability Actively Exploited in the Wild
https://cybersecuritynews.com/microsoft-office-word-0-day-vulnerability/
Fake AI Chrome extensions with 300K users steal credentials, emails
https://www.bleepingcomputer.com/news/security/fake-ai-chrome-extensions-with-300k-users-steal-credentials-emails/
WordPress plugin with 900k installs vulnerable to critical RCE flaw
https://www.bleepingcomputer.com/news/security/wordpress-plugin-with-900k-installs-vulnerable-to-critical-rce-flaw/
GTIG AI Threat Tracker: Distillation, Experimentation, and (Continued) Integration of AI for Adversarial Use | Google Cloud Blog
https://cloud.google.com/blog/topics/threat-intelligence/distillation-experimentation-integration-ai-adversarial-use/
83% of Ivanti EPMM Exploits Linked to Single IP on Bulletproof Hosting Infrastructure
https://thehackernews.com/2026/02/83-of-ivanti-epmm-exploits-linked-to.html
Hai Security & Trust | HackerOne Help Center
https://docs.hackerone.com/en/articles/10908081-hai-security-trust
REMnux v8: 15 Years of Building a Malware Analysis Toolkit
https://zeltser.com/remnux-v8-release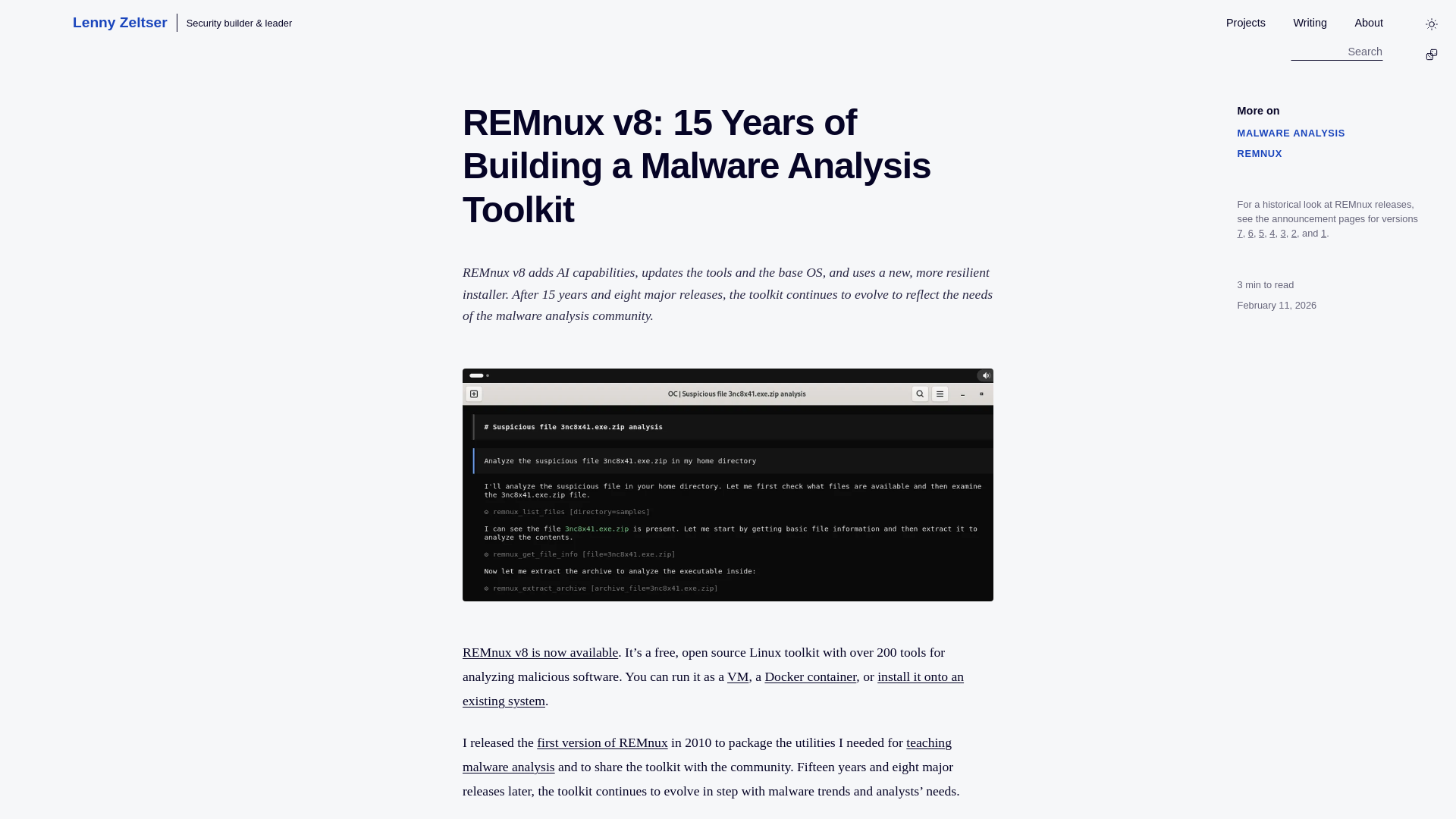
Lazarus Campaign Plants Malicious Packages in npm and PyPI Ecosystems
https://thehackernews.com/2026/02/lazarus-campaign-plants-malicious.html
Microsoft Store Outlook add-in hijacked to steal 4,000 Microsoft accounts
https://www.bleepingcomputer.com/news/security/microsoft-store-outlook-add-in-hijacked-to-steal-4-000-microsoft-accounts/