Week 24 – 2024 – This Week In 4n6
https://thisweekin4n6.com/2024/06/16/week-24-2024/
U.K. Hacker Linked to Notorious Scattered Spider Group Arrested in Spain
https://thehackernews.com/2024/06/uk-hacker-linked-to-notorious-scattered.html
New Linux malware is controlled through emojis sent from Discord
https://www.bleepingcomputer.com/news/security/new-linux-malware-is-controlled-through-emojis-sent-from-discord/
ManageEngine ADAudit - Reverse engineering Windows RPC to find CVEs - part 2 / reverse engineering | Shelltrail - Swedish offensive security experts
https://www.shelltrail.com/research/manageengine-adaudit-reverse-engineering-windows-rpc-to-find-cve-2024-36036-and-cve-2024-36037-part2/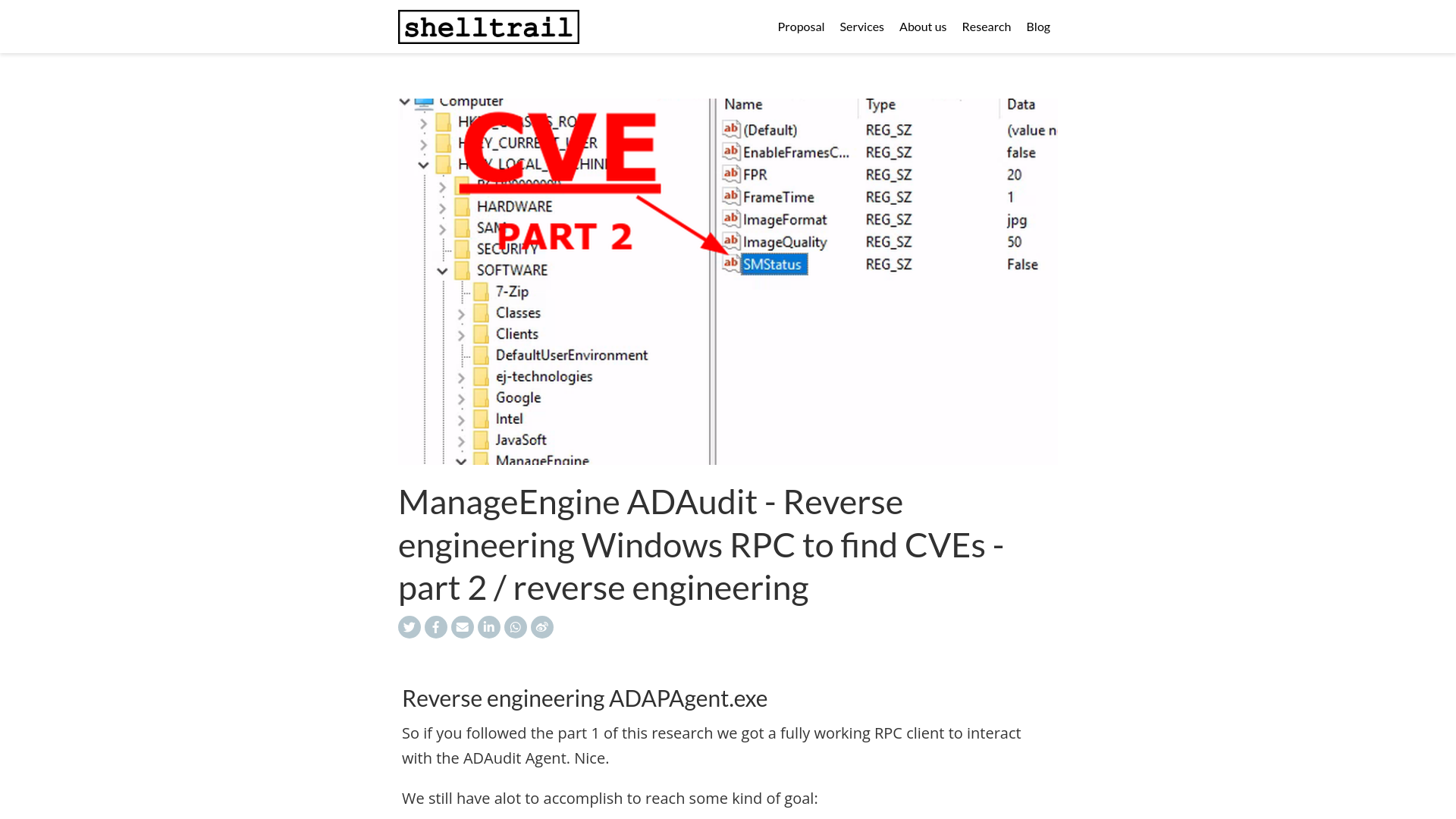
ManageEngine ADAudit - Reverse engineering Windows RPC to find CVEs - part 1 / RPC | Shelltrail - Swedish offensive security experts
https://www.shelltrail.com/research/manageengine-adaudit-reverse-engineering-windows-rpc-to-find-cve-2024-36036-and-cve-2024-36037-part1/
GitHub - vxCrypt0r/Voidgate: A technique that can be used to bypass AV/EDR memory scanners. This can be used to hide well-known and detected shellcodes (such as msfvenom) by performing on-the-fly decryption of individual encrypted assembly instructions, thus rendering memory scanners useless for that specific memory page.
https://github.com/vxCrypt0r/Voidgate
Two Bytes is Plenty: FortiGate RCE with CVE-2024-21762
https://www.assetnote.io/resources/research/two-bytes-is-plenty-fortigate-rce-with-cve-2024-21762
Post-Exploiting an F5 Big-IP: root, and now what? - Almond Offensive Security Blog
https://offsec.almond.consulting/post-exploiting-f5-BIG-IP.html
VBA: having fun with macros, overwritten pointers & R/W/X memory - Adepts of 0xCC
https://adepts.of0x.cc/vba-hijack-pointers-rwa/
The First Decade of Corporate Ransomware - YouTube
https://youtu.be/Ap8gWBNQ24g?feature=shared