Unrar Path Traversal Vulnerability affects Zimbra Mail
https://blog.sonarsource.com/zimbra-pre-auth-rce-via-unrar-0day/
The Phantom Credentials of SCCM: Why the NAA Won’t Die | by Duane Michael | Jun, 2022 | Posts By SpecterOps Team Members
https://posts.specterops.io/the-phantom-credentials-of-sccm-why-the-naa-wont-die-332ac7aa1ab9
code white | Blog: Bypassing .NET Serialization Binders
https://codewhitesec.blogspot.com/2022/06/bypassing-dotnet-serialization-binders.html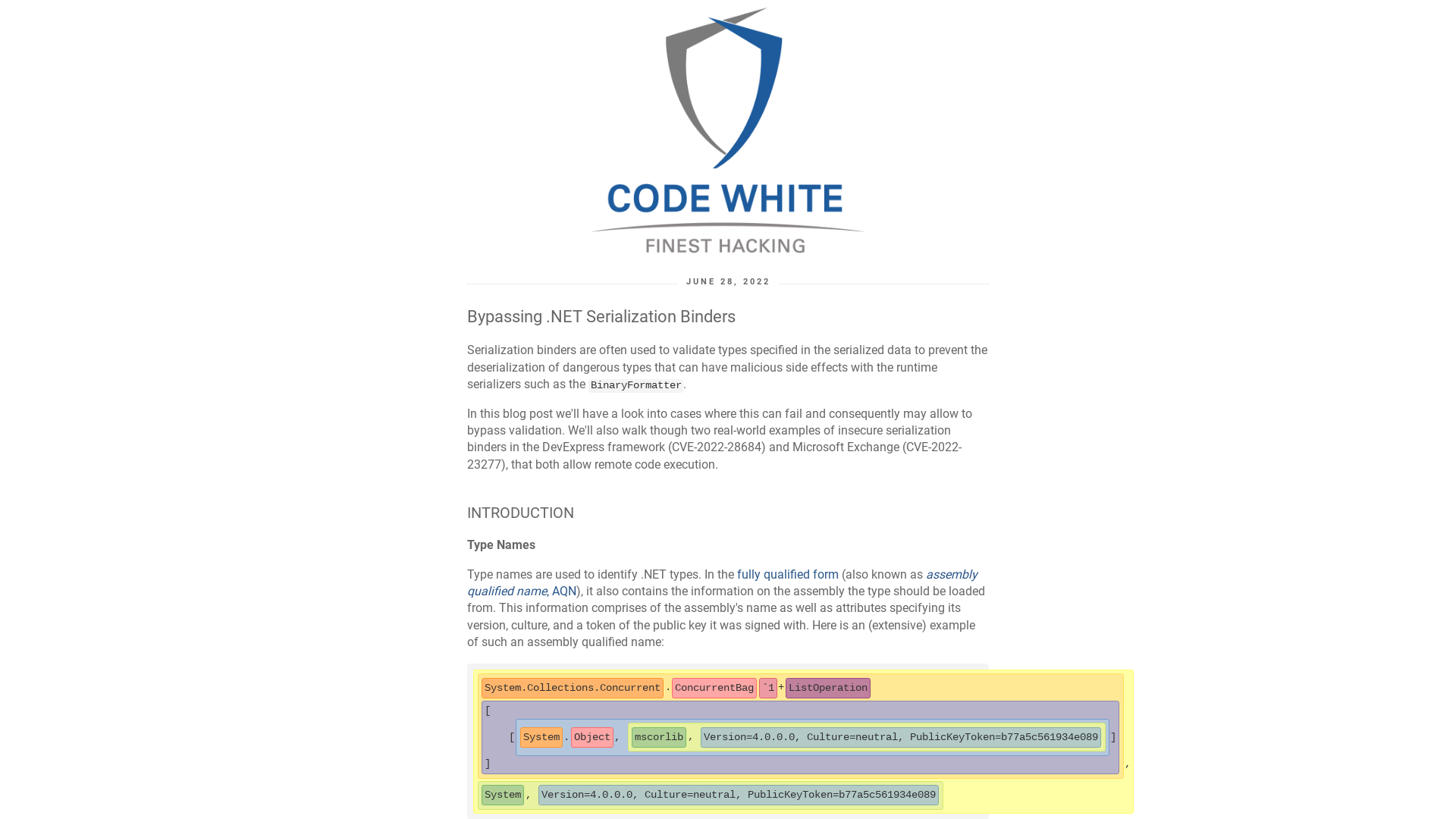
Cisco Talos Intelligence Group - Comprehensive Threat Intelligence: De-anonymizing ransomware domains on the dark web
https://blog.talosintelligence.com/2022/06/de-anonymizing-ransomware-domains-on.html
Cloud Vulnerabilities & Security Issues Database
https://www.cloudvulndb.org/
Evilnum APT returns with updated TTPs and New Targets | Blog
https://www.zscaler.com/blogs/security-research/return-evilnum-apt-updated-ttps-and-new-targets
The hidden side of Seclogon part 3: Racing for LSASS dumps
https://splintercod3.blogspot.com/p/the-hidden-side-of-seclogon-part-3.html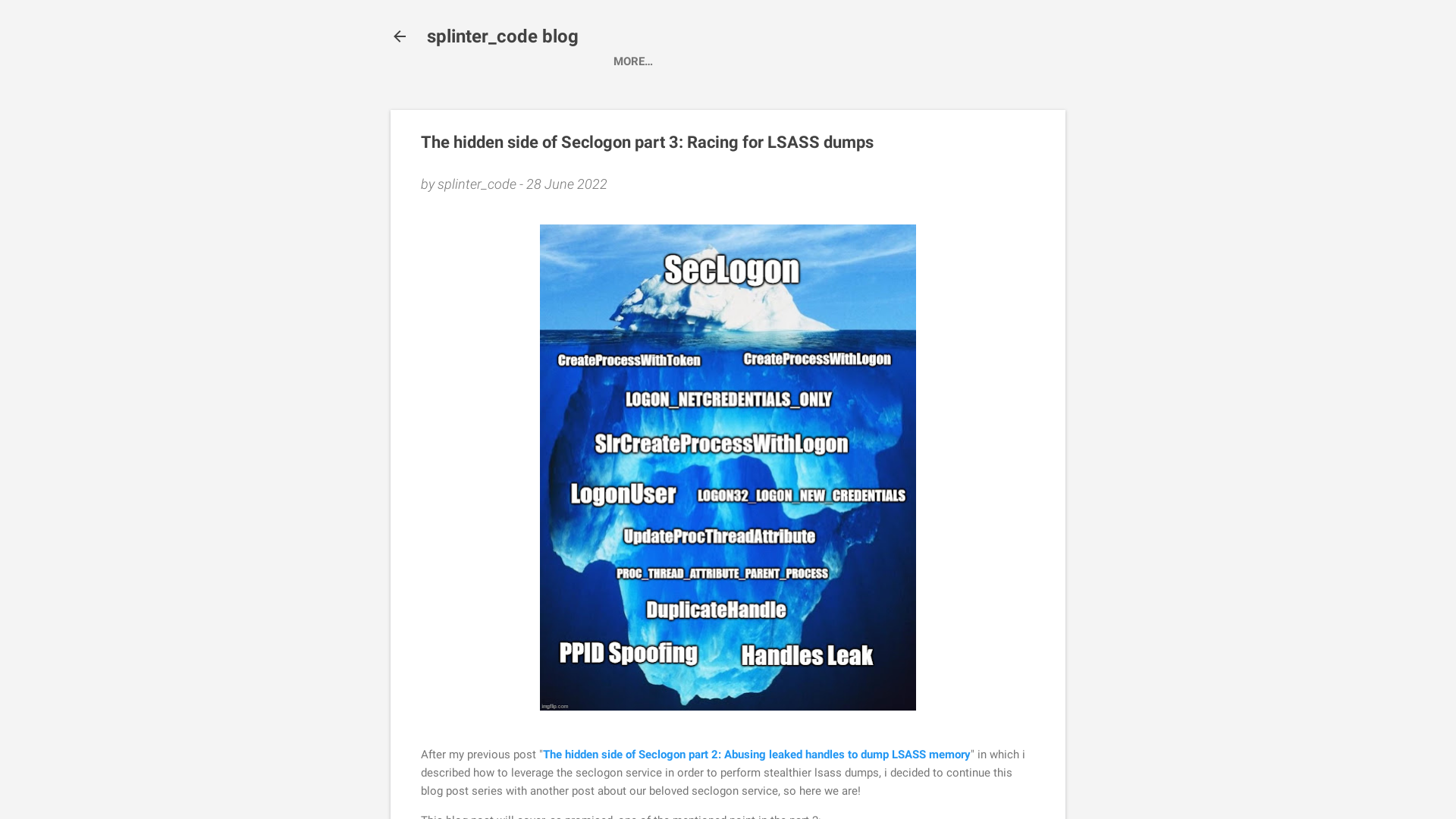
Over 900,000 Kubernetes instances found exposed online
https://www.bleepingcomputer.com/news/security/over-900-000-kubernetes-instances-found-exposed-online/
LockBit 3.0 introduces the first ransomware bug bounty program
https://www.bleepingcomputer.com/news/security/lockbit-30-introduces-the-first-ransomware-bug-bounty-program/
Check Point Research on Twitter: "#BREAKING We found files related to the attack against the Steel Industry in Iran. Initial analysis shows that the malware is connected to the attacks against Iran Railways last year, an attack that was thoroughly described in our previous research. Here's what we know so far >> https://t.co/f8nhoSi7cF" / Twitter
https://twitter.com/_CPResearch_/status/1541753913732366338
Put MITRE ATT&CK® at Your Fingertips | by Ingrid Skoog | MITRE-Engenuity | Jun, 2022 | Medium
https://hubs.ly/Q01fJ1HD0
random/28_06_2022_QBOT.csv at main · aanubhav-ioc/random · GitHub
https://github.com/aanubhav-ioc/random/blob/main/28_06_2022_QBOT.csv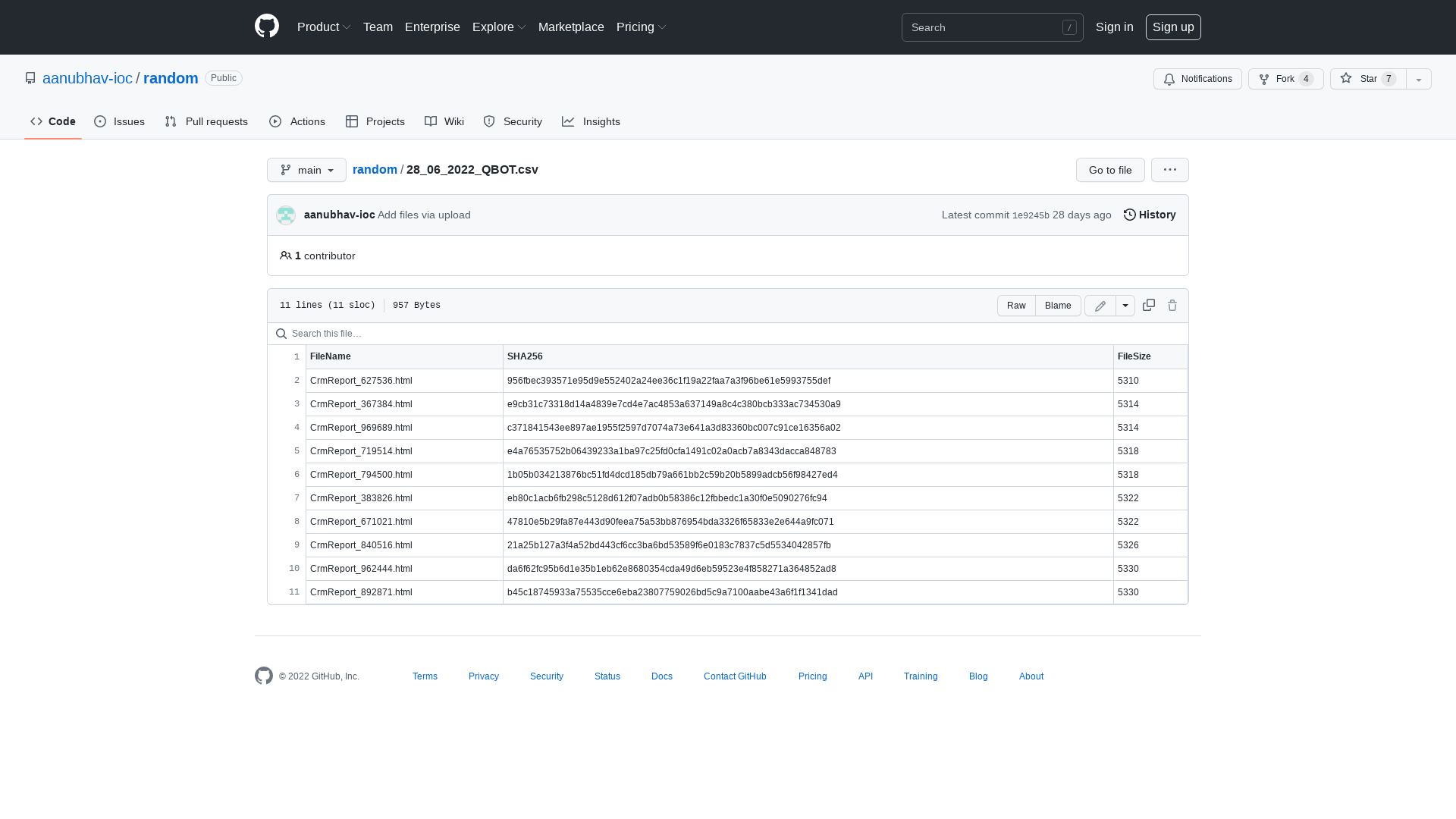
SANSNew2Cyber on Twitter: "We firmly believe entry level should mean entry level. #cybersecurity #InfosecMemes #CybersecurityMemes https://t.co/qTz4THqnKt" / Twitter
https://twitter.com/new_2_cyber/status/1541380830672601090
KISA 암호이용활성화 - 암호 역기능 대응 - 자료실
https://seed.kisa.or.kr/kisa/Board/133/detailView.do
APT Hackers Targeting Industrial Control Systems with ShadowPad Backdoor
https://thehackernews.com/2022/06/apt-hackers-targeting-industrial.html
MalwareBazaar | Browse malware samples
https://bazaar.abuse.ch/sample/247331dfc1ff971623e169a302fc2c8eb5c895573d055ca1b985d6ac1cfd6720/
Hatching Triage | Malware sandboxing report by Hatching Triage
https://tria.ge/220627-3fnzvadhdq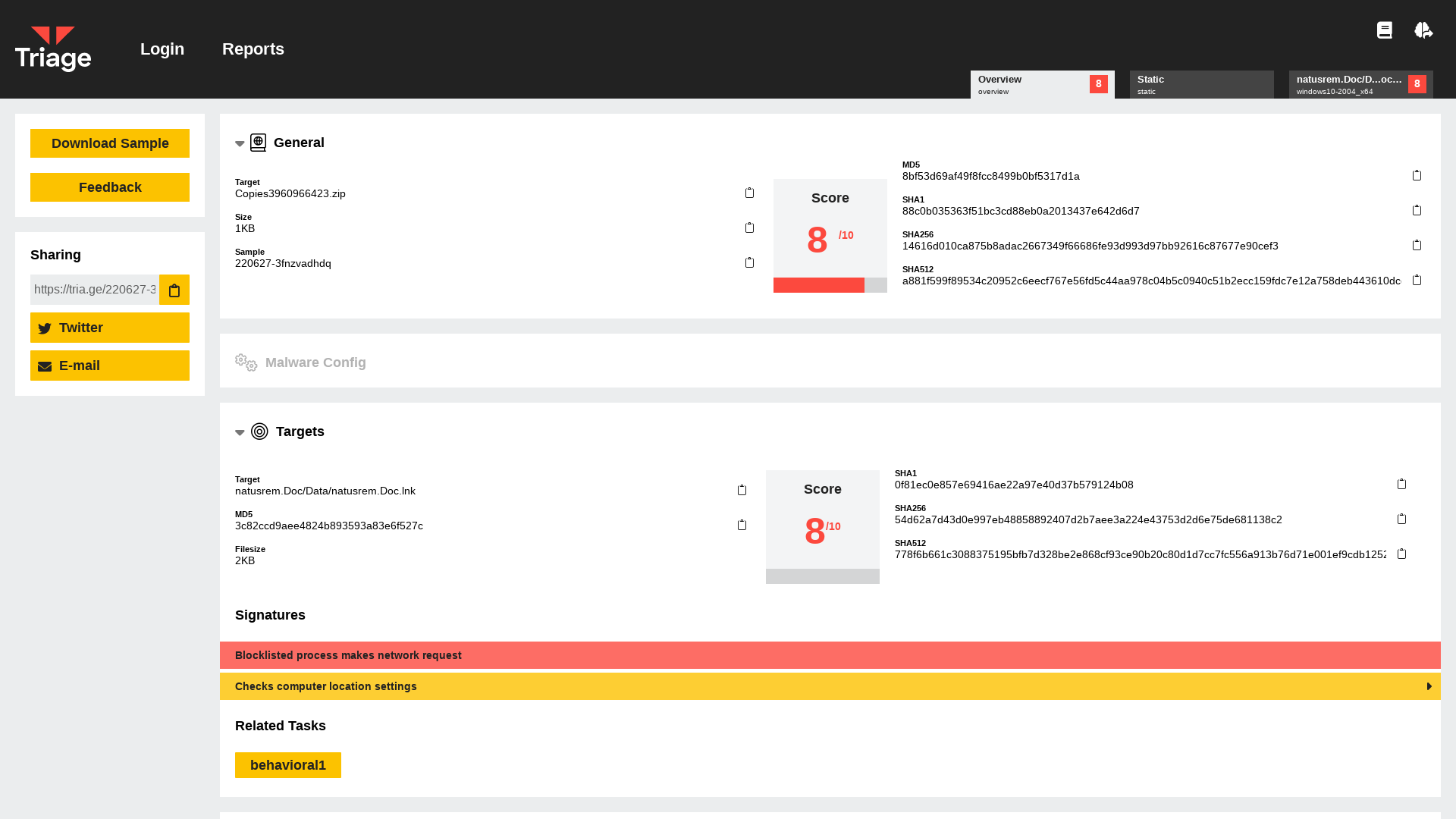
ZuoRAT Hijacks SOHO Routers to Silently Stalk Networks - Lumen
https://blog.lumen.com/zuorat-hijacks-soho-routers-to-silently-stalk-networks/
MalwareBazaar | Browse malware samples
https://bazaar.abuse.ch/sample/7284dbccfd2327ead9ea433fe75a1e164723abf9fd5fbad4b363e7e0311da83a/
Raccoon Stealer v2 - Part 1: The return of the dead - SEKOIA.IO Blog
https://blog.sekoia.io/raccoon-stealer-v2-part-1-the-return-of-the-dead/
Catalin Cimpanu on Twitter: "NEW: A team of four South Korean academics have published a paper detailing a method to recover data encrypted by the Hive ransomware gang https://t.co/ub8hSSIN76 https://t.co/SyEYcjUN4O" / Twitter
https://twitter.com/campuscodi/status/1494671053355982848
MalwareBazaar | SHA256 ba43866447e97dea2a94cfb5ae8974be90809331cb9d90ab5abf6f1d8dcd49f2 (AgentTesla)
https://bazaar.abuse.ch/sample/ba43866447e97dea2a94cfb5ae8974be90809331cb9d90ab5abf6f1d8dcd49f2/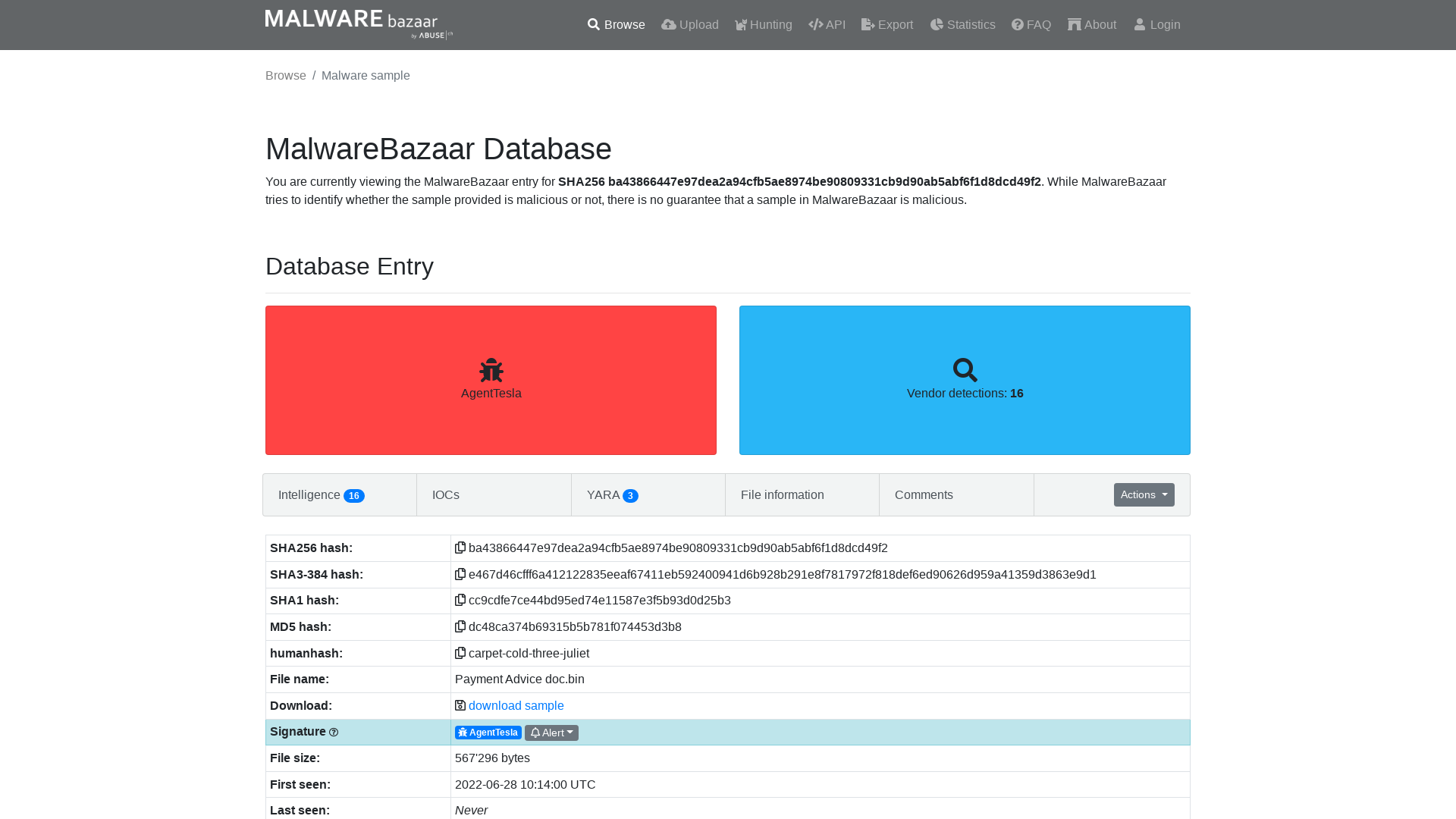
https://pastebin.com/raw/dNxptGCe
https://pastebin.com/raw/dNxptGCe
gov.uscourts.flmd.386126.33.0.pdf
https://storage.courtlistener.com/recap/gov.uscourts.flmd.386126/gov.uscourts.flmd.386126.33.0.pdf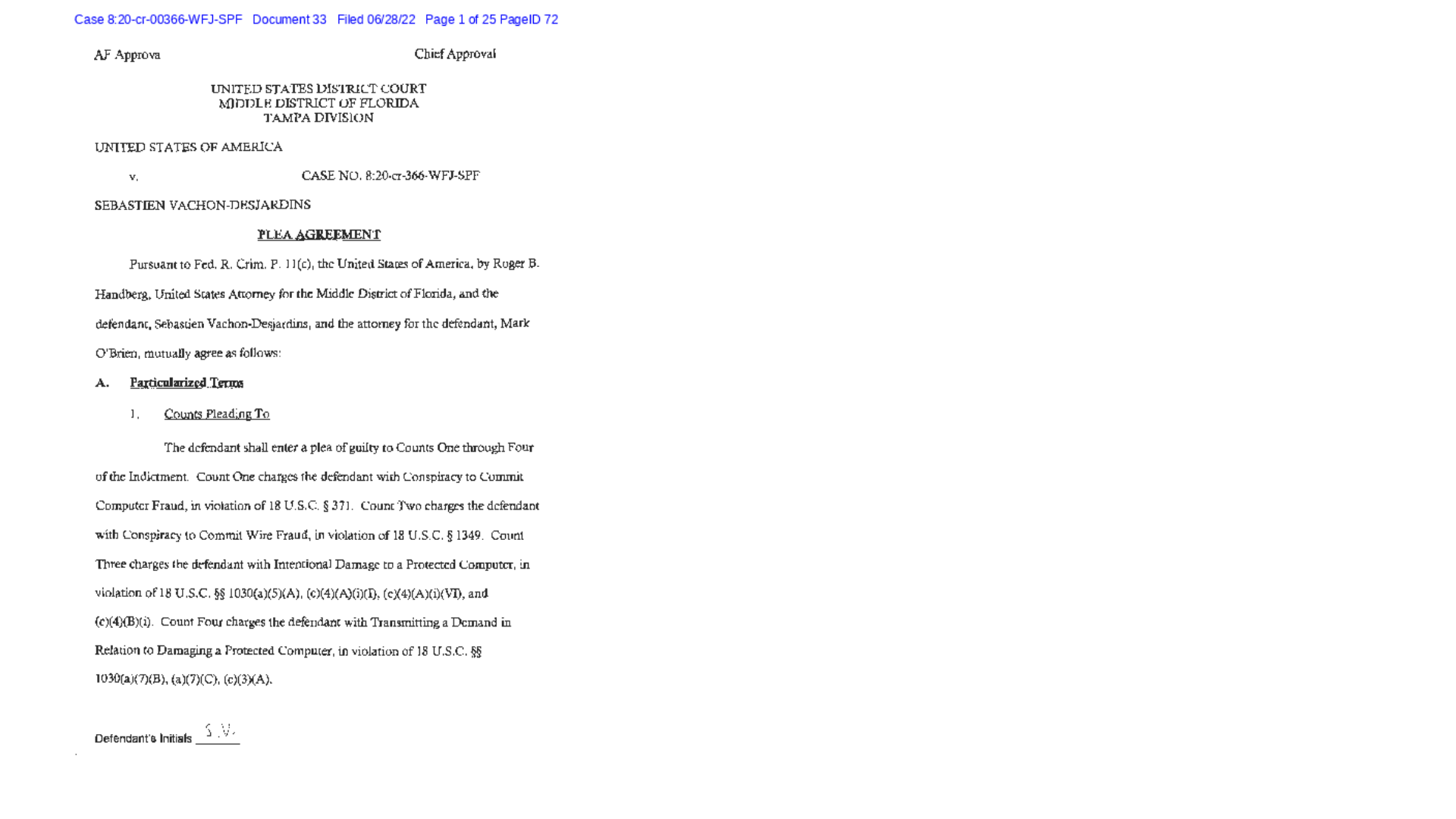
odbcconf | LOLBAS
https://lolbas-project.github.io/lolbas/Binaries/Odbcconf/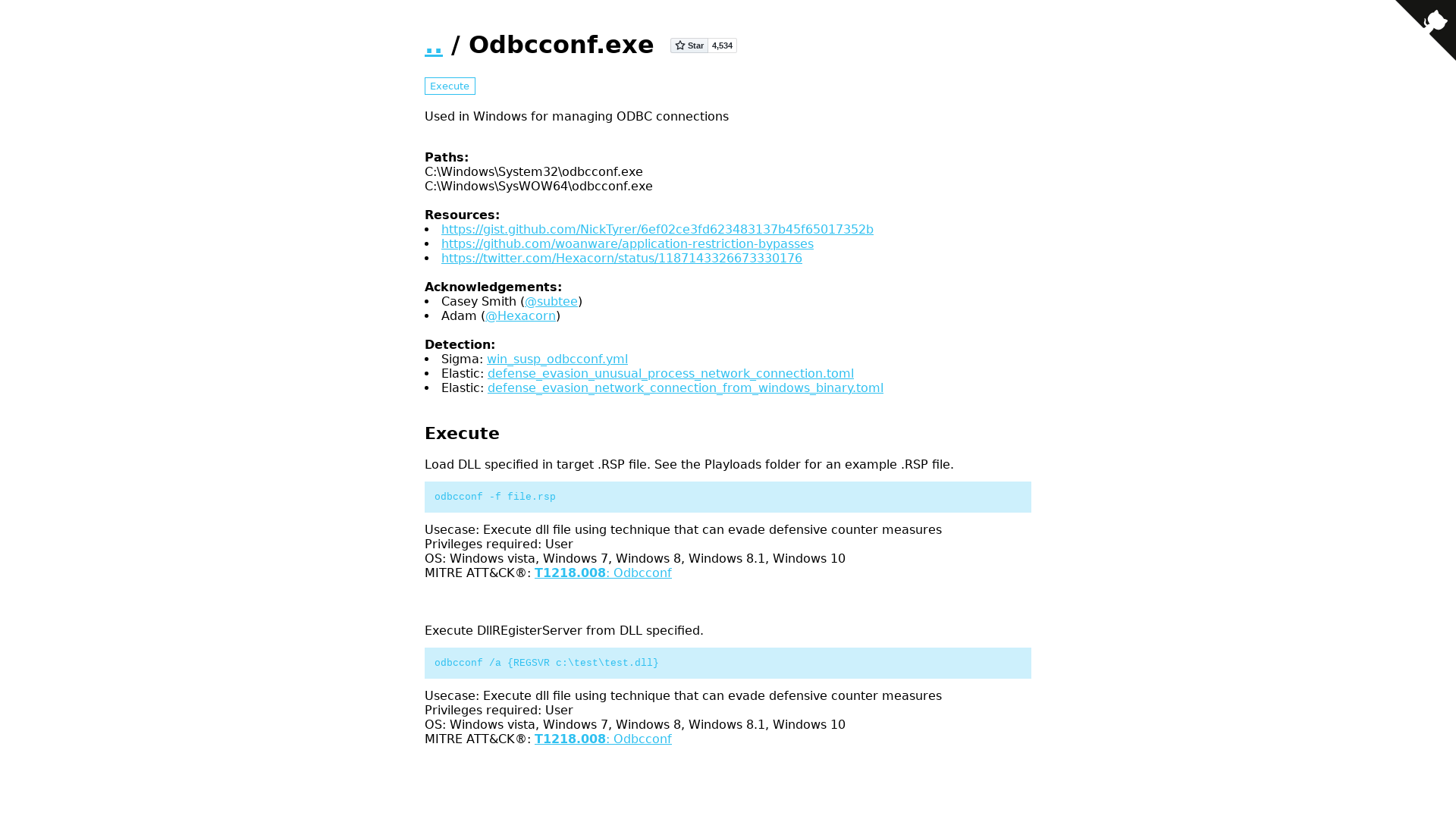
Red Canary on Twitter: "The #BumbleBee dropper/downloader continues to change. We’re now seeing odbcconf.exe load the malicious DLL (rather than Rundll32). While odbcconf.exe can execute DLL files, we don’t commonly observe it doing so in the wild, so this is an interesting change! #RCIntel https://t.co/oXtXAu77V8" / Twitter
https://twitter.com/redcanary/status/1541838407894171650