Project Zero: The curious tale of a fake Carrier.app
https://googleprojectzero.blogspot.com/2022/06/curious-case-carrier-app.html
PHP-binary-bugs/cve_2022_31626_remote_exploit at main · CFandR-github/PHP-binary-bugs · GitHub
https://github.com/CFandR-github/PHP-binary-bugs/tree/main/cve_2022_31626_remote_exploit
Miracle - One Vulnerability To Rule Them All | by Peterjson | Jun, 2022 | Medium
https://peterjson.medium.com/miracle-one-vulnerability-to-rule-them-all-c3aed9edeea2
GitHub - HackingLZ/ExtractedDefender
https://github.com/HackingLZ/ExtractedDefender
Spyware vendor targets users in Italy and Kazakhstan
https://blog.google/threat-analysis-group/italian-spyware-vendor-targets-users-in-italy-and-kazakhstan/
Lisa Farbstein, TSA Spokesperson on Twitter: "Display of oversized liquids, gels and aerosols that travelers had in their carry-on bags at the @SyracuseAirport @TSA Checkpoint in a 3-day span. The limit for liquids through a checkpoint is 3.4 oz. https://t.co/Fan95TLrLy" / Twitter
https://twitter.com/tsa_northeast/status/1539668938916651008
Malicious Windows 'LNK' attacks made easy with new Quantum builder
https://www.bleepingcomputer.com/news/security/malicious-windows-lnk-attacks-made-easy-with-new-quantum-builder/
Extracting Whitelisted Paths from Windows Defender ASR Rules
https://adamsvoboda.net/extracting-asr-rules/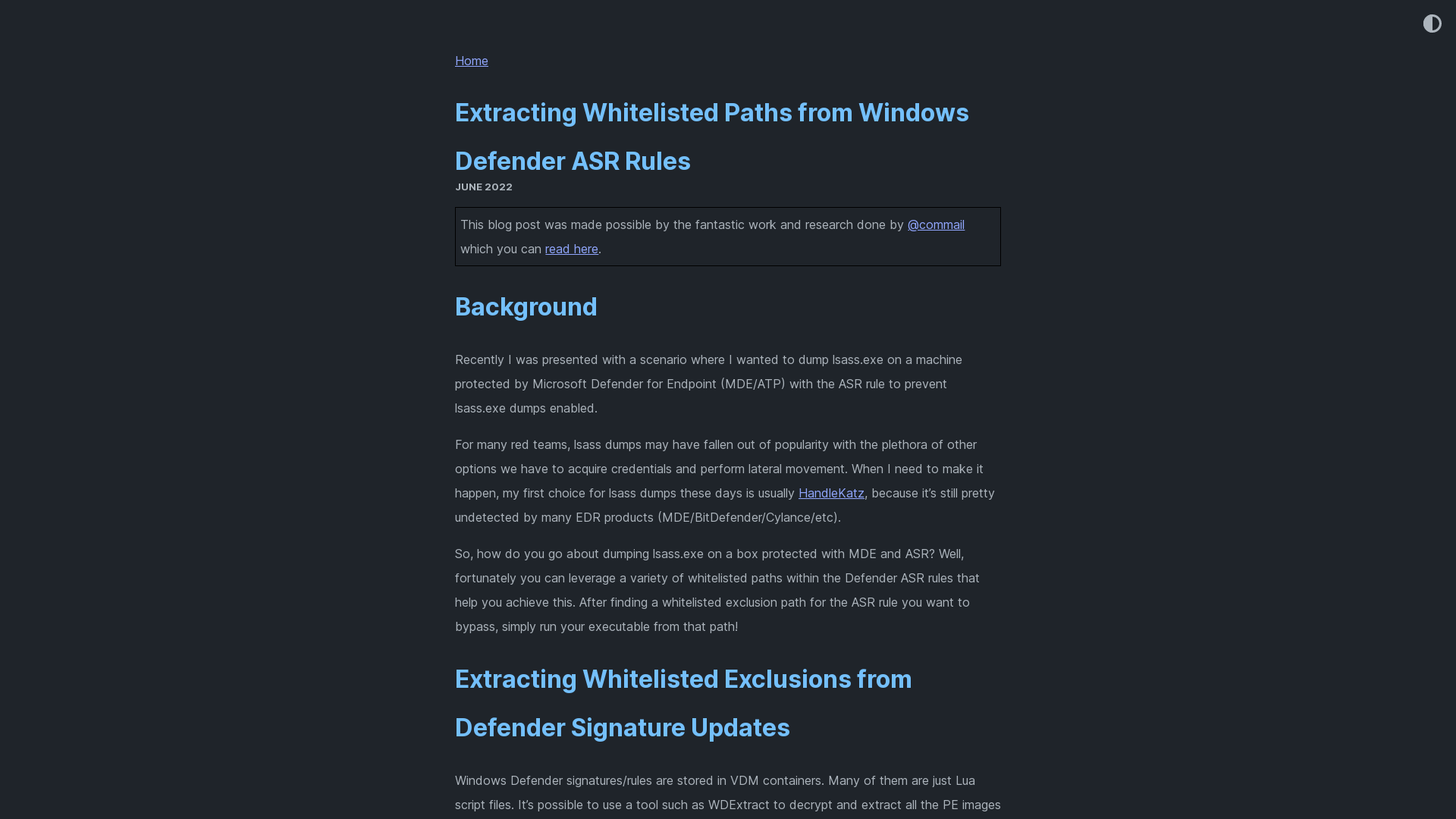
add WerFault Silent Process Exit: --werfault · helpsystems/nanodump@578116f · GitHub
https://github.com/helpsystems/nanodump/commit/578116faea3d278d53d70ea932e2bbfe42569507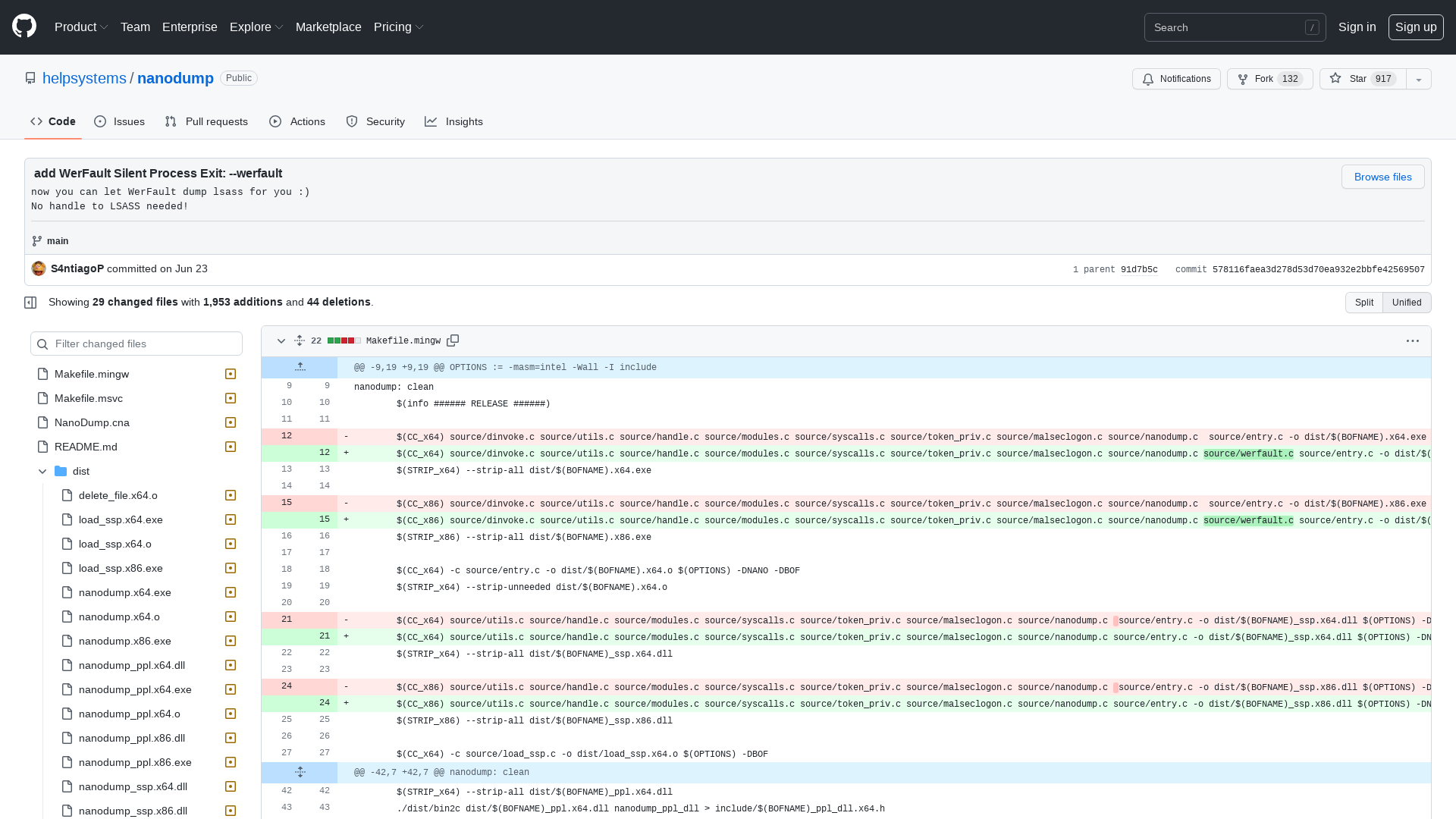
The hateful eight: Kaspersky’s guide to modern ransomware groups’ TTPs | Securelist
https://securelist.com/modern-ransomware-groups-ttps/106824/
CISA experts propose ‘311’ cybersecurity emergency call line for small businesses - The Record by Recorded Future
https://therecord.media/cisa-experts-propose-311-cybersecurity-emergency-call-line-for-small-businesses/
Security Researcher - Malware Reverse Engineer (Remote)
https://crowdstrike.wd5.myworkdayjobs.com/crowdstrikecareers/job/USA---Remote/Security-Researcher---Malware-Reverse-Engineer--Remote-_R9054
BRONZE STARLIGHT Ransomware Operations Use HUI Loader | Secureworks
https://www.secureworks.com/research/bronze-starlight-ransomware-operations-use-hui-loader
Conti ransomware hacking spree breaches over 40 orgs in a month
https://www.bleepingcomputer.com/news/security/conti-ransomware-hacking-spree-breaches-over-40-orgs-in-a-month/
GitHub - paranoidninja/Brute-Ratel-C4-Community-Kit: This repository contains scripts, configurations and deprecated payload loaders for Brute Ratel C4 (https://bruteratel.com/)
https://github.com/paranoidninja/Brute-Ratel-C4-Community-Kit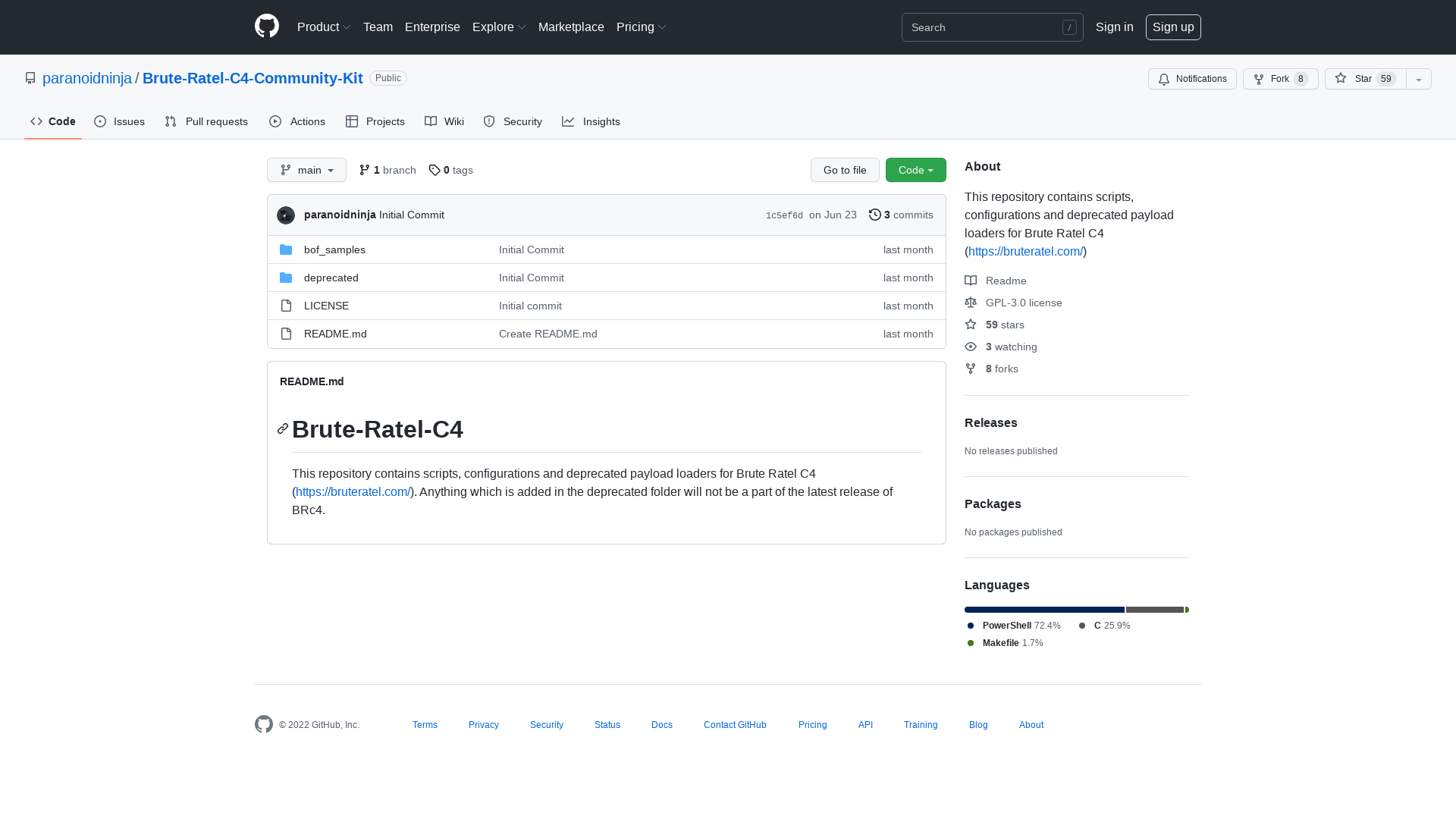
NSA, Partners Recommend Properly Configuring, Monitoring PowerShell in New Report > National Security Agency/Central Security Service > Article
https://www.nsa.gov/Press-Room/News-Highlights/Article/Article/3069620/nsa-partners-recommend-properly-configuring-monitoring-powershell-in-new-report/
VirusTotal - File - 2e2d0764920efb1f36bbd318ea3dde465ec686acda0b815d90067909952b247f
https://www.virustotal.com/gui/file/2e2d0764920efb1f36bbd318ea3dde465ec686acda0b815d90067909952b247f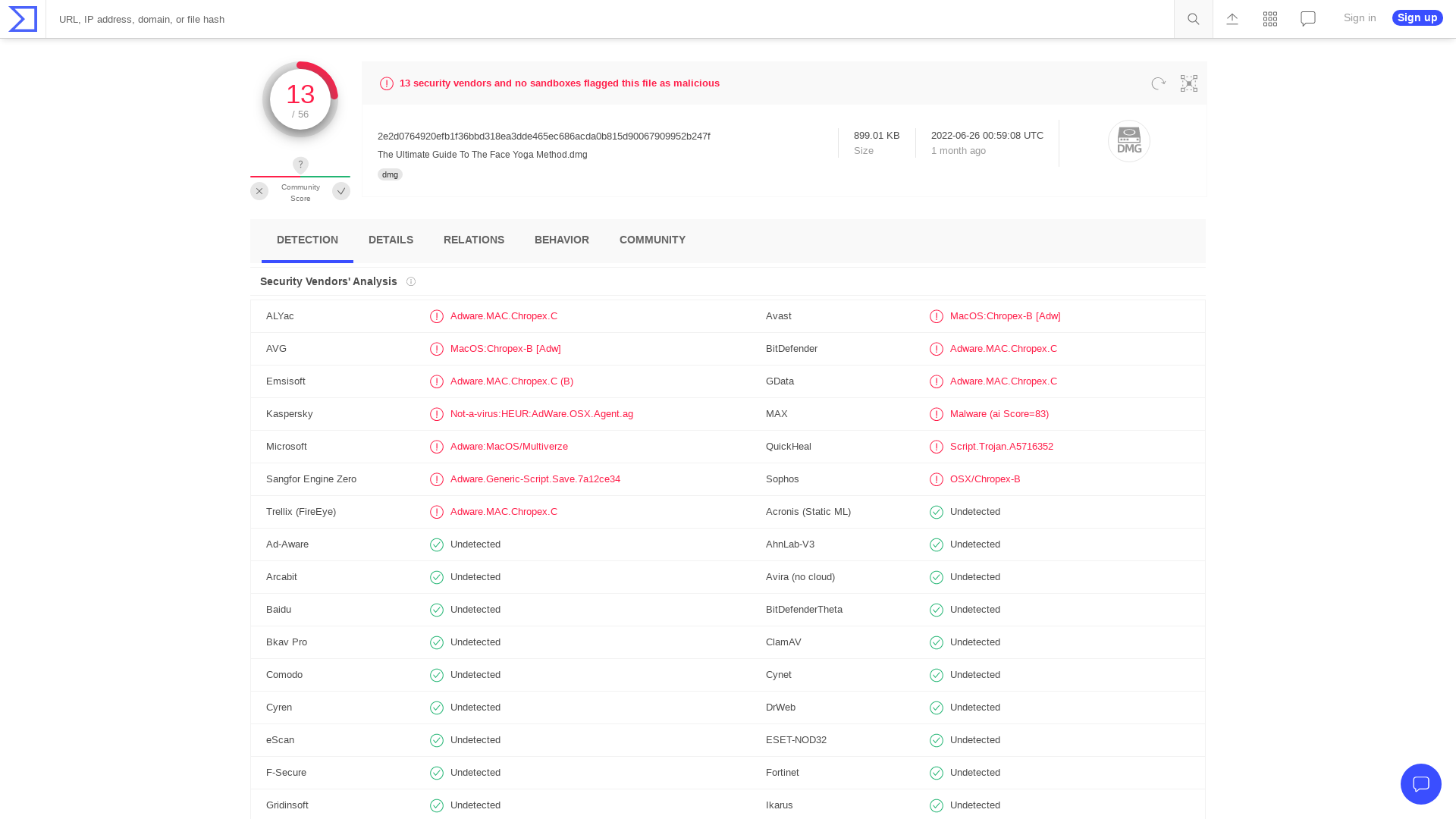
VirusTotal - File - d9d7b7d00d37a147cdd664f8f7aad6ceaa0d7ea08d7ea33724333dd9383310c1
https://www.virustotal.com/gui/file/d9d7b7d00d37a147cdd664f8f7aad6ceaa0d7ea08d7ea33724333dd9383310c1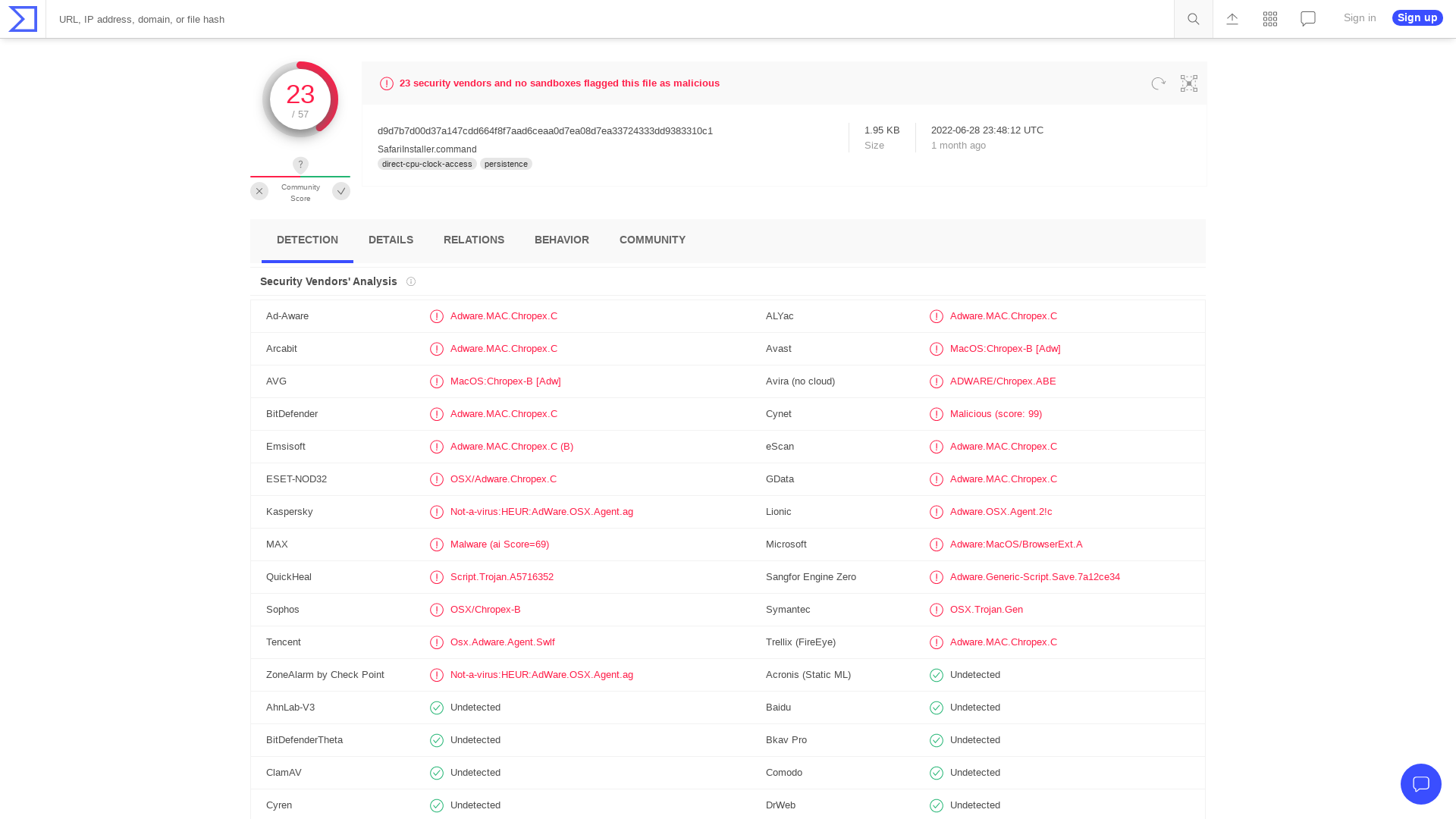
Kostas on Twitter: "Microsoft disables the execution of VBA macros by default! It was about time 🥳 I anticipate that TTPs for initial access will continue with standalone vbs/js scripts, iso/lnk/hta files etc. However, this is still a big win! https://t.co/137k0QRF2R https://t.co/LOlnyf57il" / Twitter
https://twitter.com/kostastsale/status/1490783531701706752
Defending Ukraine: Early Lessons from the Cyber War - Microsoft On the Issues
https://blogs.microsoft.com/on-the-issues/2022/06/22/defending-ukraine-early-lessons-from-the-cyber-war/
FLOSS Version 2.0 | Mandiant
https://www.mandiant.com/resources/floss-version-2
NSO Confirms Pegasus Spyware Used by at least 5 European Countries
https://thehackernews.com/2022/06/nso-confirms-pegasus-spyware-used-by-at.html
MalwareBazaar | SHA256 83402accb7cacbb3d6f6cc570ae9f1668b650324ad3c2489452e4378e9141012 (Heodo)
https://bazaar.abuse.ch/sample/83402accb7cacbb3d6f6cc570ae9f1668b650324ad3c2489452e4378e9141012/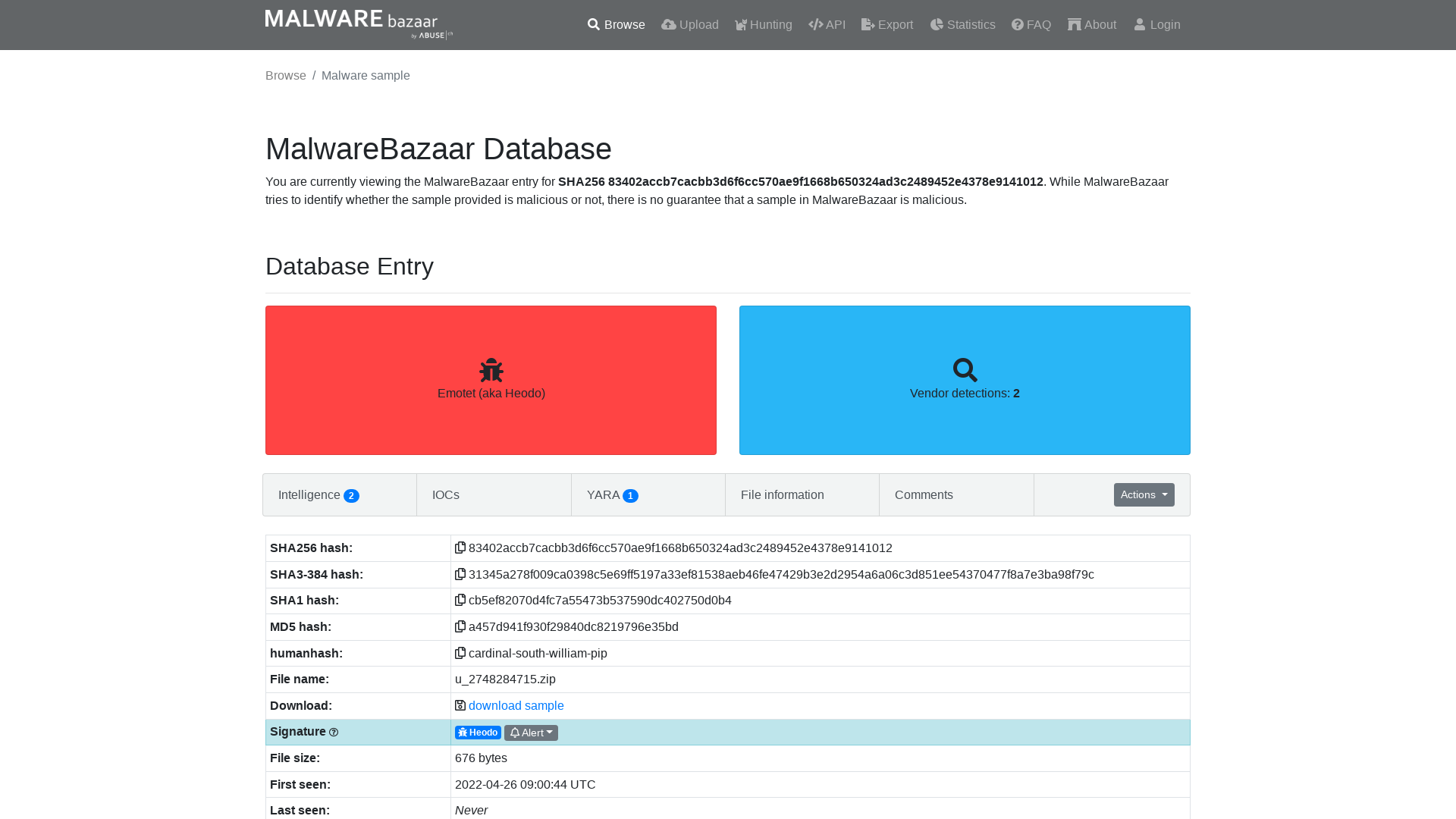
peterjson on Twitter: "As promised, I and @testanull publish our adventure last year. Hope you enjoy it ! https://t.co/wLXa4B6f5k" / Twitter
https://twitter.com/peterjson/status/1539920744129634305