Hertzbleed Attack
https://www.hertzbleed.com/
Soatok @ Megaplex, DEFCON 30 on Twitter: "@Bugcrowd is woefully unprepared for accepting reports of cryptographic issues in software. https://t.co/q41BmJfZRZ" / Twitter
https://twitter.com/SoatokDhole/status/1536765180645974016
Interpol seizes $50 million, arrests 2000 social engineers
https://www.bleepingcomputer.com/news/security/interpol-seizes-50-million-arrests-2000-social-engineers/
CVE-2022-30190 - Security Update Guide - Microsoft - Microsoft Windows Support Diagnostic Tool (MSDT) Remote Code Execution Vulnerability
https://msrc.microsoft.com/update-guide/en-US/vulnerability/CVE-2022-30190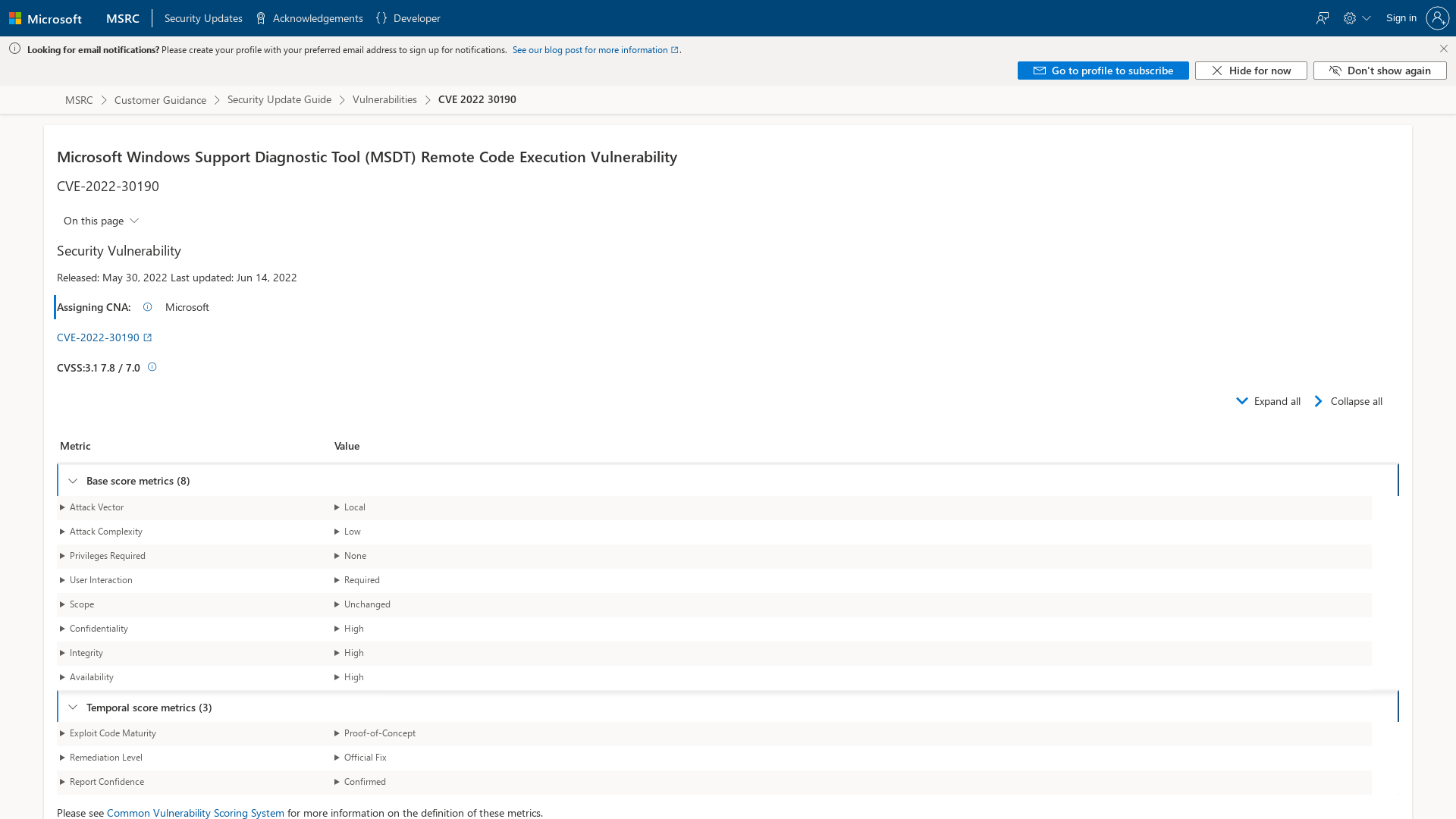
Zimbra Email - Stealing Clear-Text Credentials via Memcache injection
https://blog.sonarsource.com/zimbra-mail-stealing-clear-text-credentials-via-memcache-injection/
GreyNoise to expand its threat intel collection after securing $15M in funding | TechCrunch
https://techcrunch.com/2022/06/15/greynoise-threat-intel-funding/
2277 - XNU: Flow Divert Race Condition Use After Free - project-zero
https://bugs.chromium.org/p/project-zero/issues/detail?id=2277
Pulling MikroTik into the Limelight | Margin Research
https://margin.re/blog/pulling-mikrotik-into-the-limelight.aspx
PSBits/NetstatWithTimestamps at master · gtworek/PSBits · GitHub
https://github.com/gtworek/PSBits/tree/master/NetstatWithTimestamps
Red Team Ops
https://training.zeropointsecurity.co.uk/courses/red-team-ops
DriftingCloud: Zero-Day Sophos Firewall Exploitation and an Insidious Breach | Volexity
https://www.volexity.com/blog/2022/06/15/driftingcloud-zero-day-sophos-firewall-exploitation-and-an-insidious-breach/
Bypassing CSP with dangling iframes | PortSwigger Research
https://portswigger.net/research/bypassing-csp-with-dangling-iframes
New Hertzbleed Side Channel Attack Affects All Modern AMD and Intel CPUs
https://thehackernews.com/2022/06/new-hertzbleed-side-channel-attack.html
Ransomware gang creates site for employees to search for their stolen data
https://www.bleepingcomputer.com/news/security/ransomware-gang-creates-site-for-employees-to-search-for-their-stolen-data/
VirusTotal - File - c61fe40f46226d24f0f17c46acc4db6a0091c68abc6a3d995b3f6df1bbfcbb1e
https://www.virustotal.com/gui/file/c61fe40f46226d24f0f17c46acc4db6a0091c68abc6a3d995b3f6df1bbfcbb1e/detection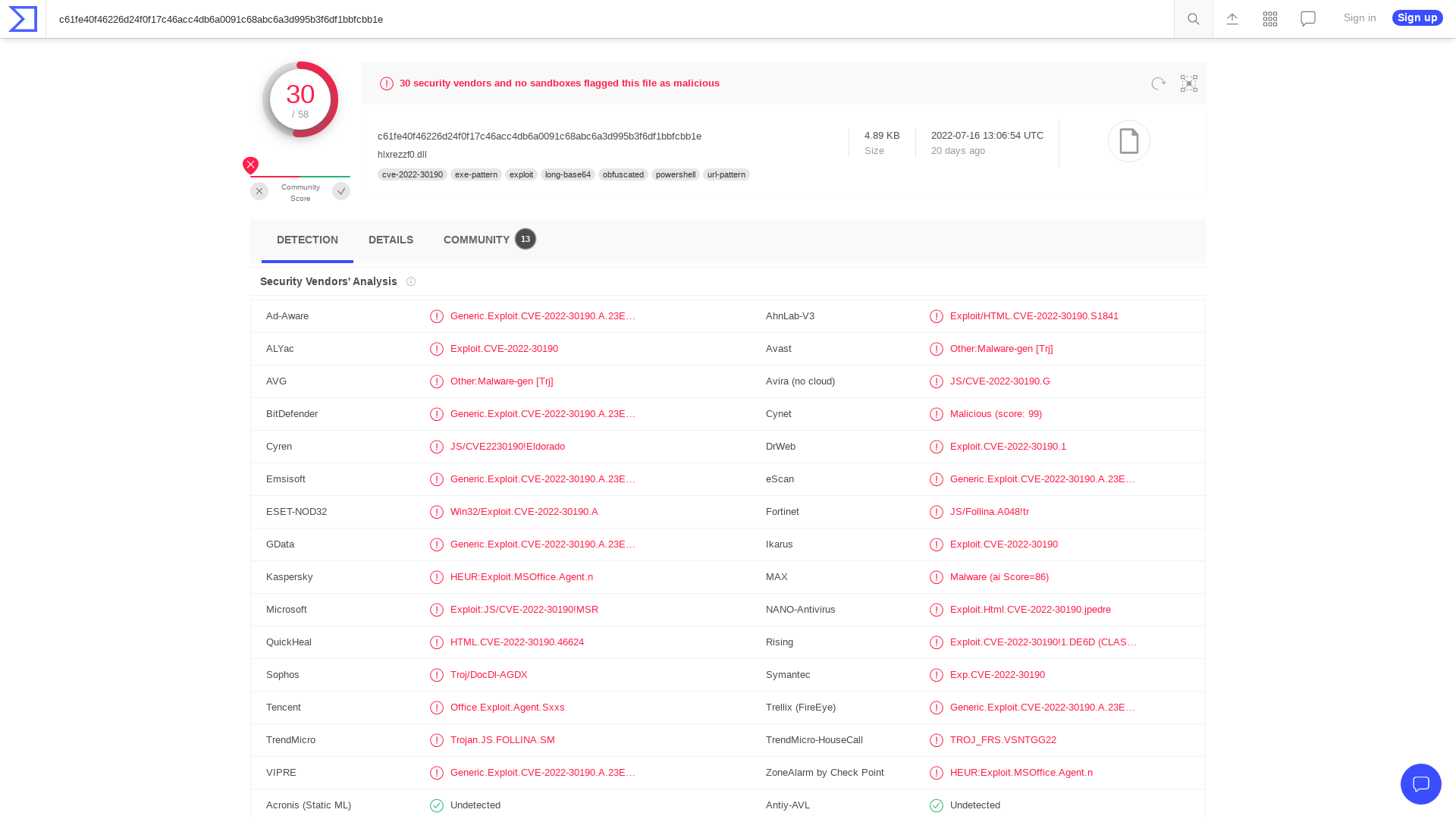
Hatching Triage | Malware sandboxing report by Hatching Triage
https://tria.ge/220614-24849ahdgk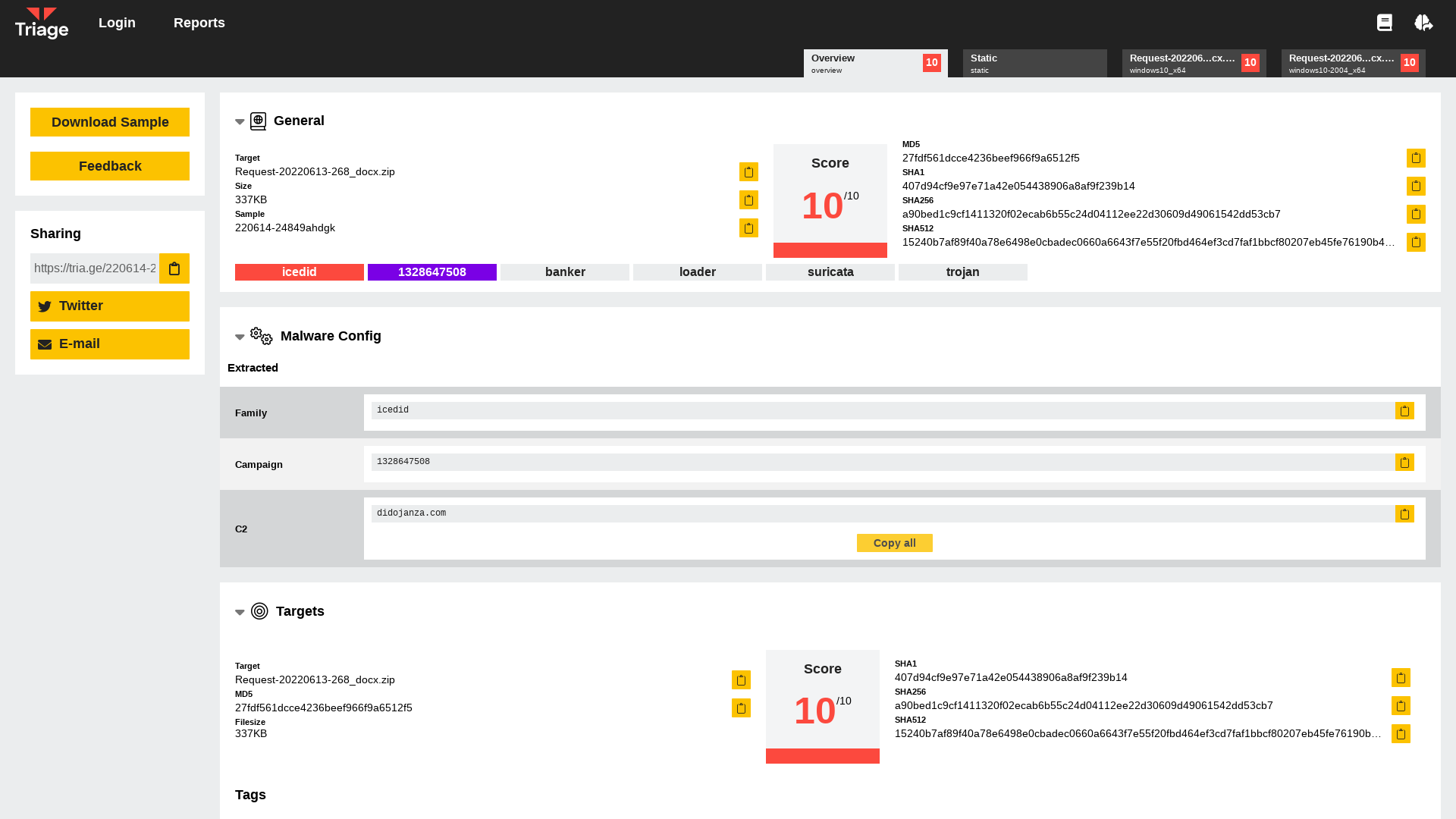
GitHub - MalwareTech/FollinaExtractor: Extract payload URLs from Follina (CVE-2022-30190) docx and rtf files
https://github.com/MalwareTech/FollinaExtractor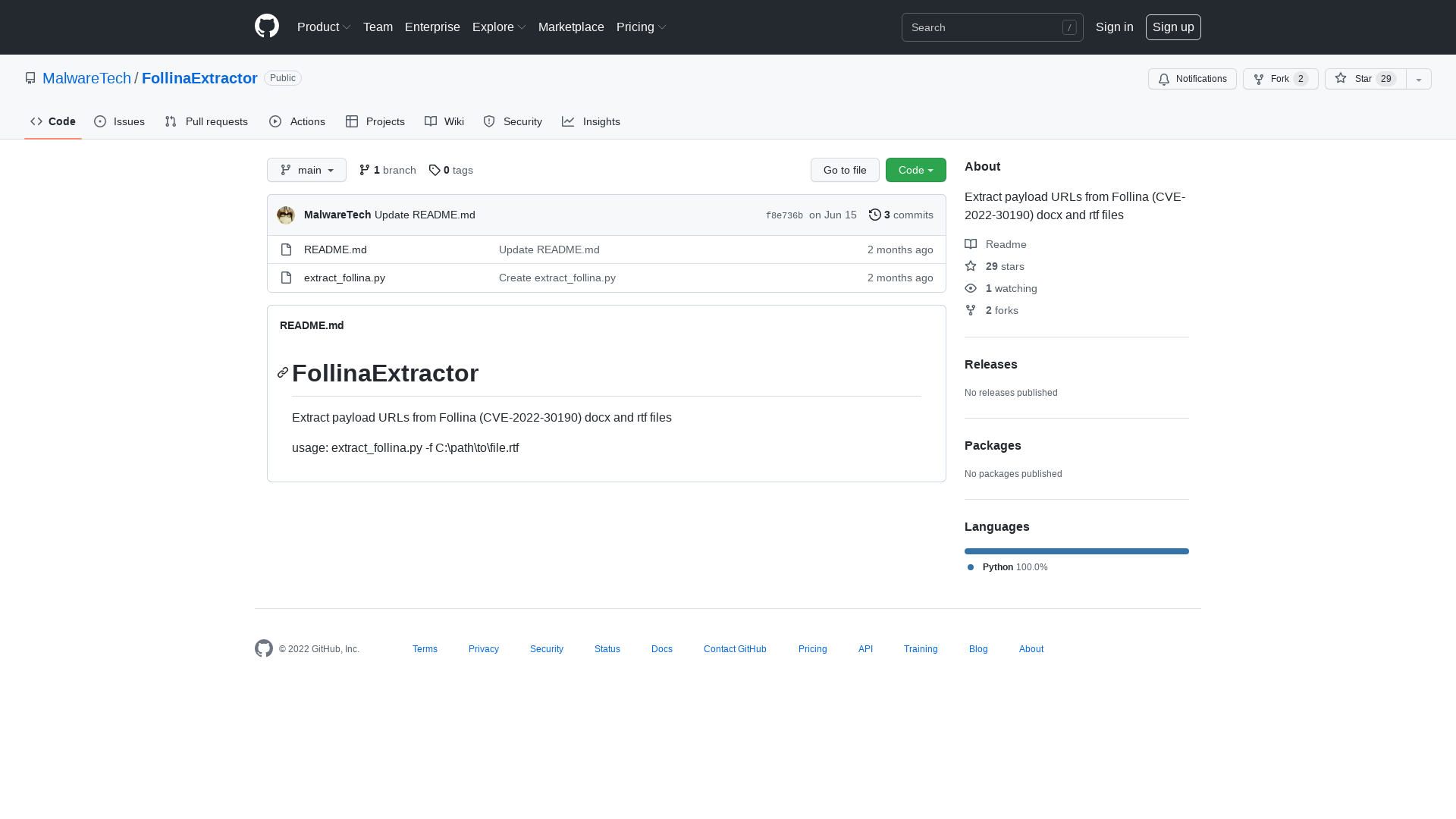
IoCs/Troj-Miner-AED.csv at master · sophoslabs/IoCs · GitHub
https://github.com/sophoslabs/IoCs/blob/master/Troj-Miner-AED.csv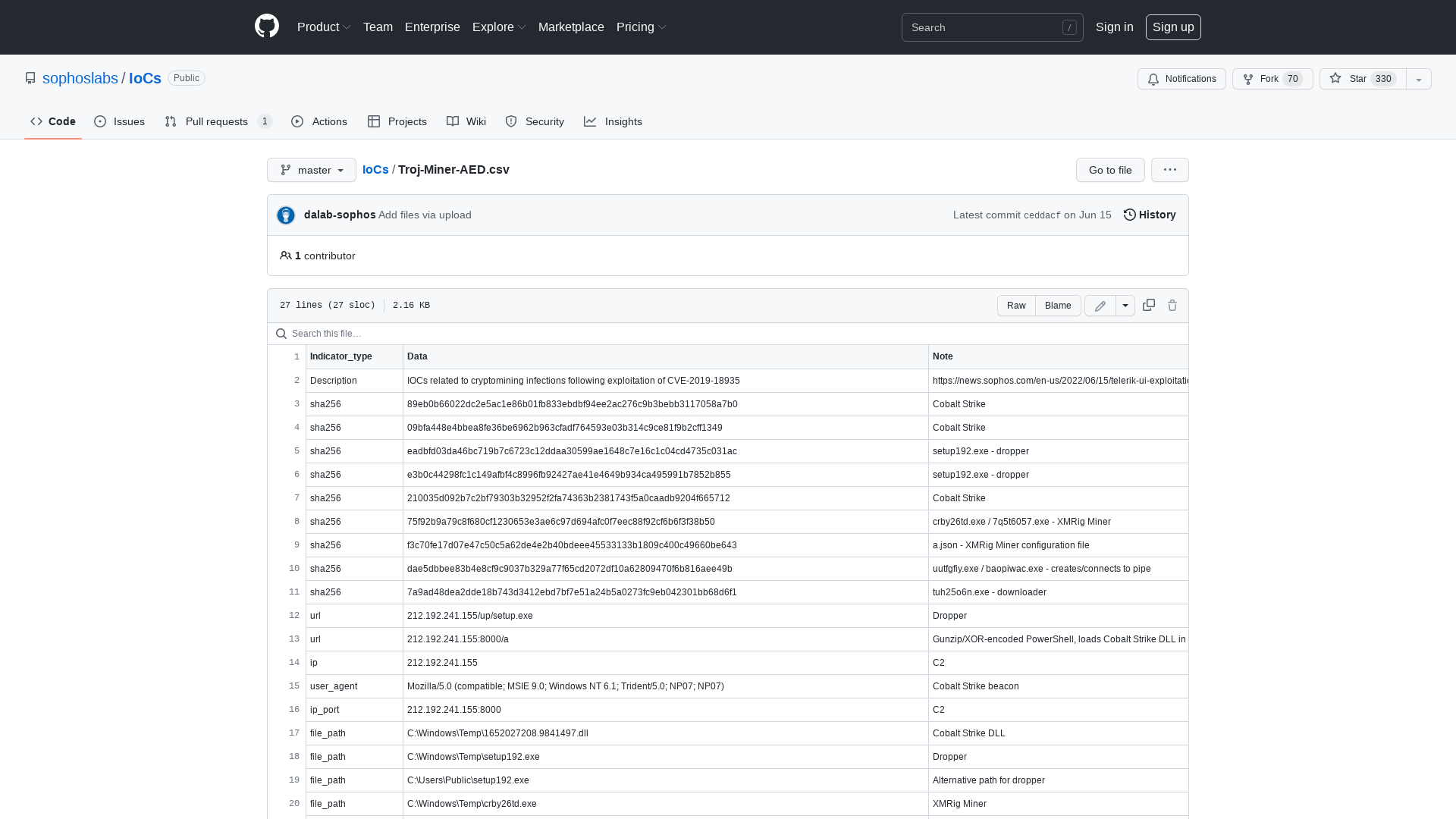
VirusTotal - File - 52b48c4b2f4a63fc6611dea7e9146a440d41e306143788ea20c56c3ab292cf00
https://www.virustotal.com/gui/file/52b48c4b2f4a63fc6611dea7e9146a440d41e306143788ea20c56c3ab292cf00/detection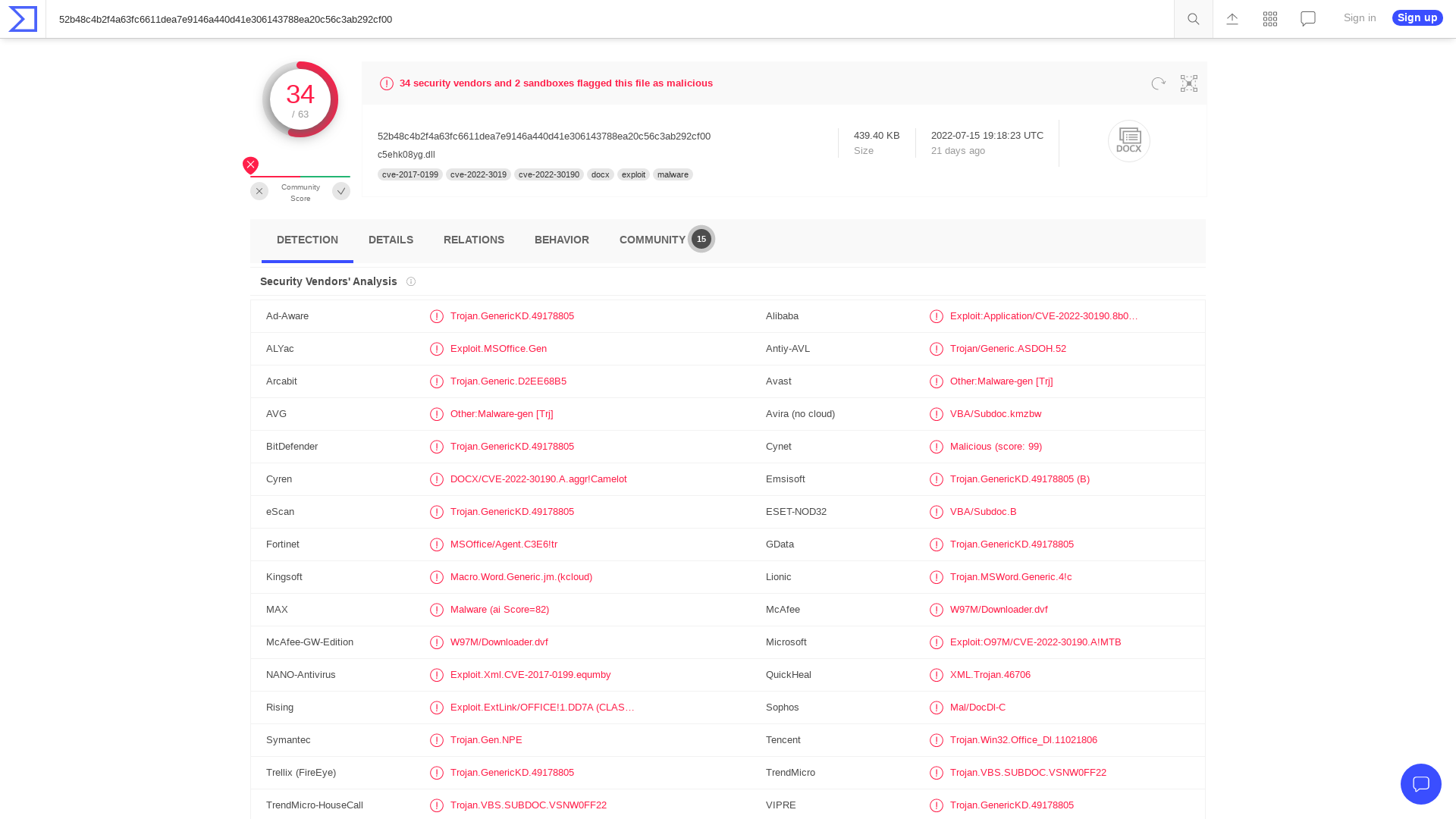
Kat Cosgrove, Svelte Traffic Cone on Twitter: "Well uh I was excited to go to Defcon 30 but apparently they've lifted their vaccine mandate, so I will not be seeing y'all there. Maybe next year" / Twitter
https://twitter.com/dixie3flatline/status/1536759349523017729
Research Paper | Emulating Phineas Phisher Attacks in Modern EDR Environments - SentinelOne
https://www.sentinelone.com/blog/research-paper-emulating-phineas-phisher-attacks-in-modern-edr-environments/
Akamai Blog | Panchan’s Mining Rig: New Golang Peer-to-Peer Botnet Says “Hi!”
https://www.akamai.com/blog/security/new-p2p-botnet-panchan
Soatok @ Megaplex, DEFCON 30 on Twitter: "@Bugcrowd Goodbye Bugcrowd. You won't be missed. https://t.co/uuAWEmDTWl" / Twitter
https://twitter.com/SoatokDhole/status/1536769827230126080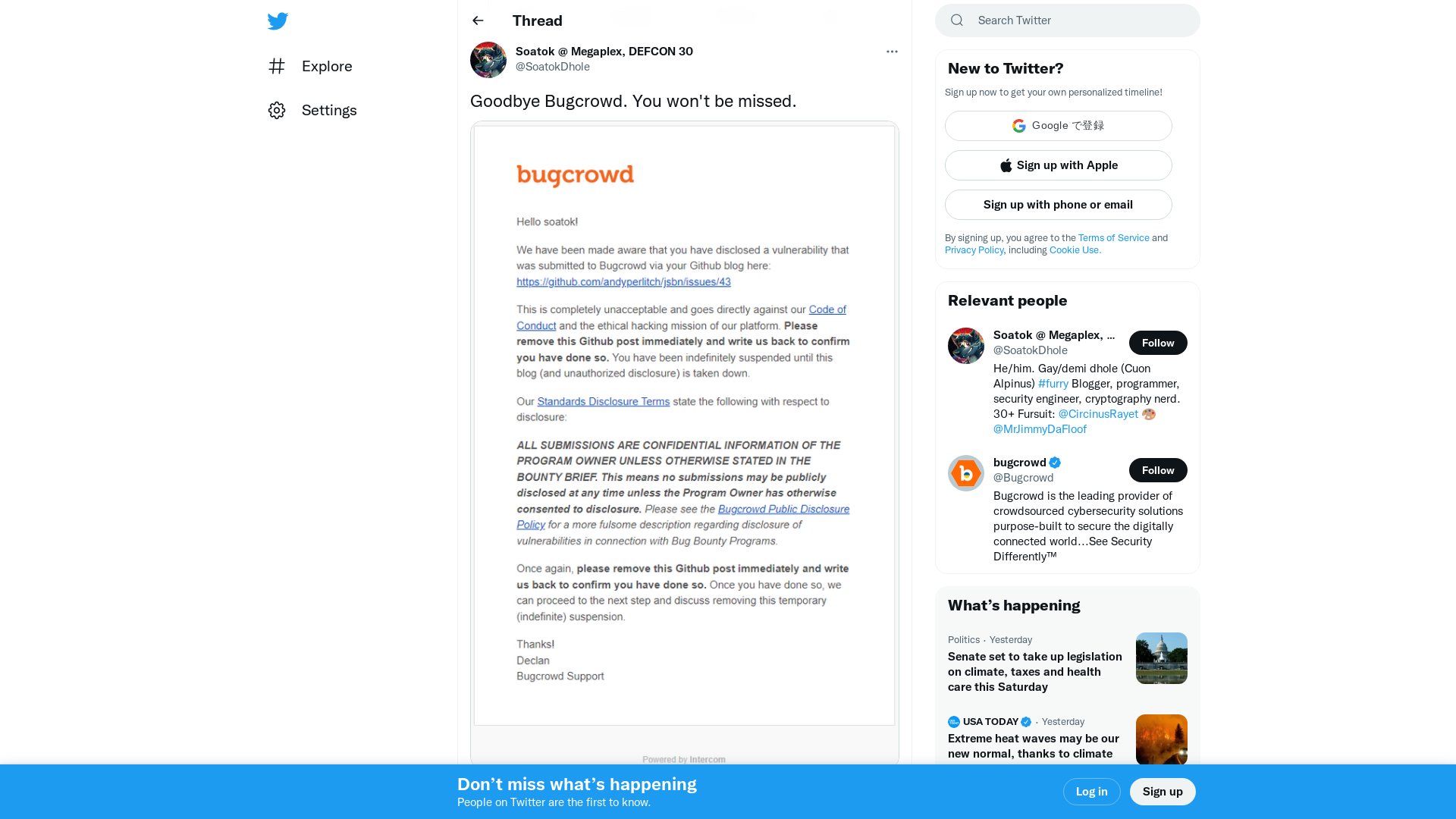
Pwn2Own 2021 Canon ImageCLASS MF644Cdw writeup
https://doar-e.github.io/blog/2022/06/11/pwn2own-2021-canon-imageclass-mf644cdw-writeup/
Cisco Secure Email bug can let attackers bypass authentication
https://www.bleepingcomputer.com/news/security/cisco-secure-email-bug-can-let-attackers-bypass-authentication/
Telerik UI exploitation leads to cryptominer, Cobalt Strike infections – Sophos News
https://news.sophos.com/en-us/2022/06/15/telerik-ui-exploitation-leads-to-cryptominer-cobalt-strike-infections/
Zero Day Initiative — CVE-2022-26937: Microsoft Windows Network File System NLM Portmap Stack Buffer Overflow
https://www.zerodayinitiative.com/blog/2022/6/7/cve-2022-26937-microsoft-windows-network-file-system-nlm-portmap-stack-buffer-overflow