Watcher.Guru on Twitter: "🚨BREAKING: Bored Ape Yacht Club and Otherside Metaverse Discord servers have been hacked. Millions worth of #NFTs reportedly stolen." / Twitter
https://twitter.com/watcherguru/status/1533106970630270982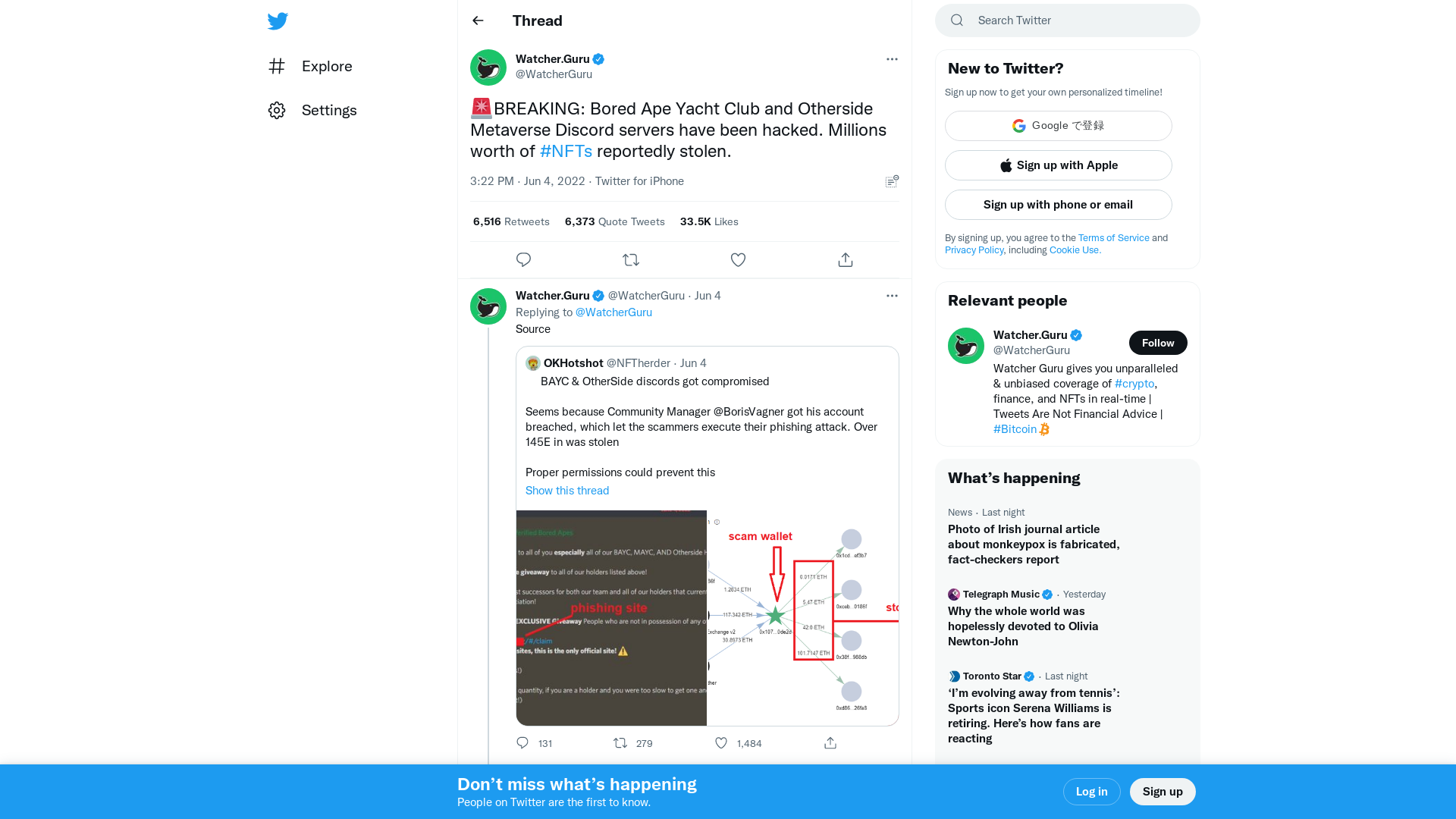
GitHub - mattifestation/AntimalwareBlight: Execute PowerShell code at the antimalware-light protection level.
https://github.com/mattifestation/AntimalwareBlight
Brute force attacks against Windows Remote Desktop
https://trunc.org/learning/brute-force-attacks-against-windows-remote-desktop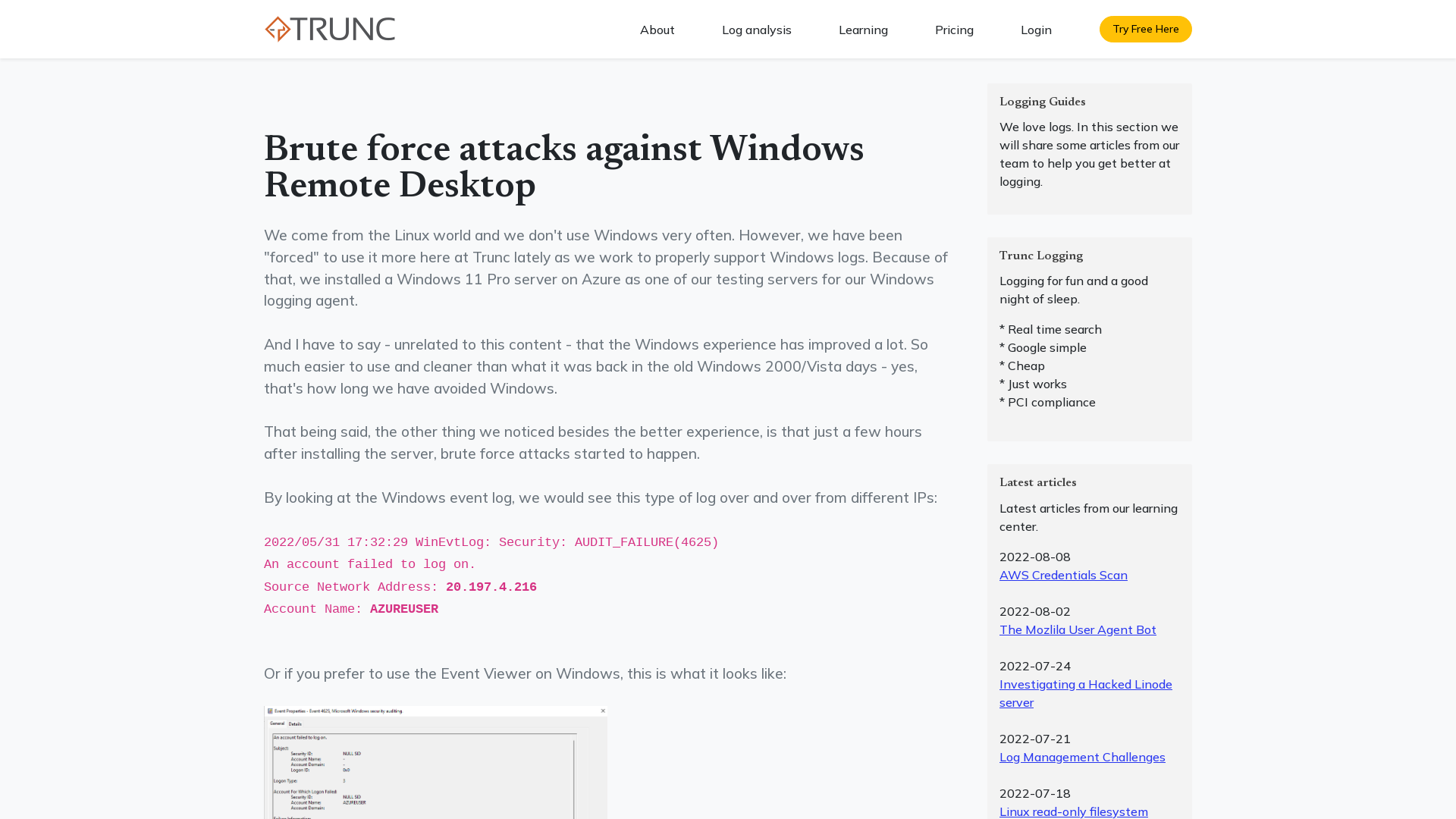
404 Page Not Found - Xmind - Mind Mapping Software
https://www.xmind.net/m/5dypm8/
El Universal (@ElUniversal) / Twitter
https://twitter.com/ElUniversal
PiRogue tool suite - Mobile forensic & Network traffic analysis
https://piroguetoolsuite.github.io/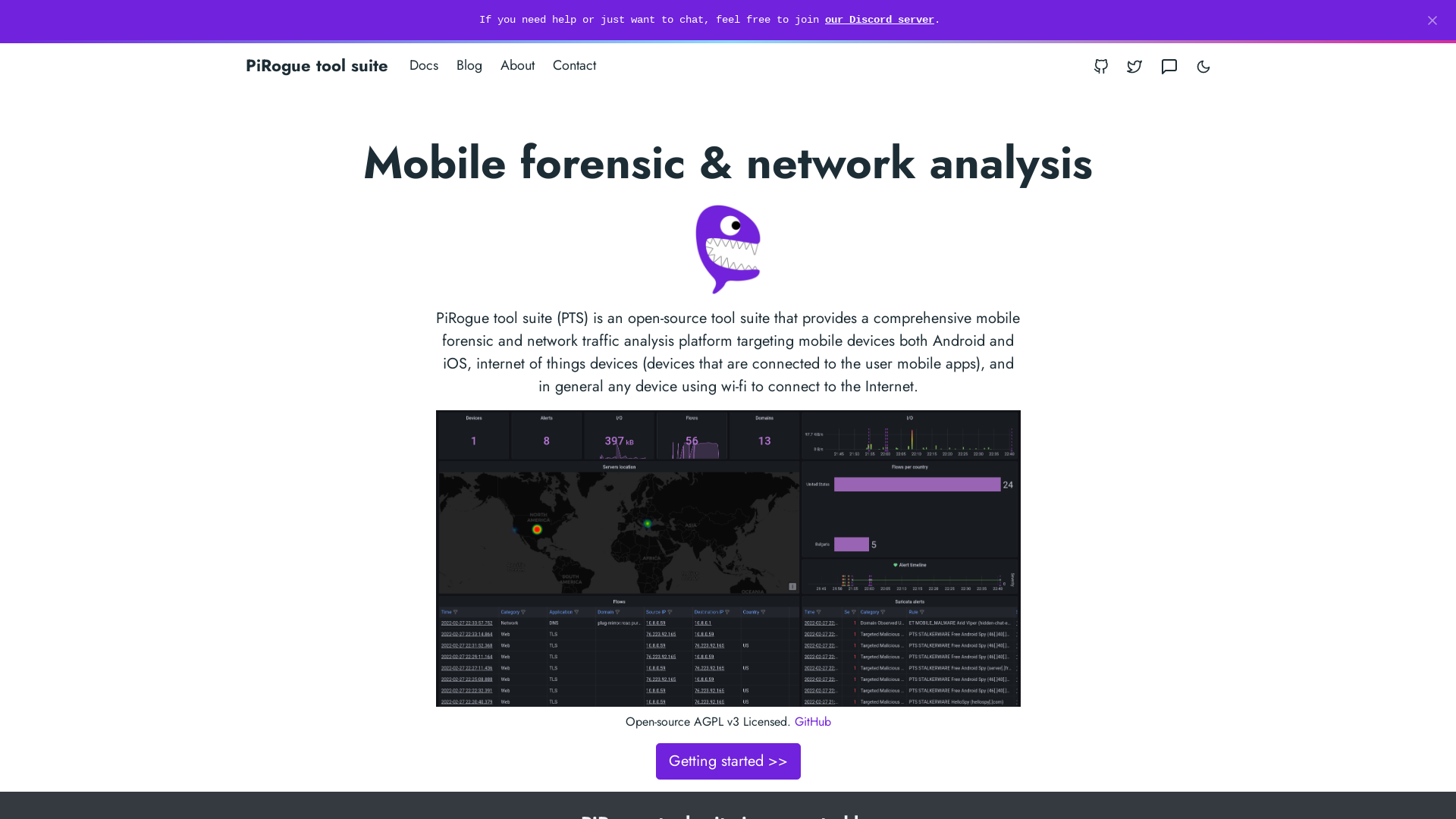
Pole Vault Power on Twitter: "This is my daughter. She just turned 9. Here is why I would never allow her to play middle or high school sports if we lived in Ohio… https://t.co/K7CDgFVhr0" / Twitter
https://twitter.com/polevaultpower/status/1533263117911613440
Corey Quinn on Twitter: "Corporate Infosec sends a phishing test email, I click, and somehow I'm the asshole because "[I] failed the test; had this been real it would have destroyed the company network"? If me clicking can destroy the network, I'm not the one in this conversation who sucks at their job." / Twitter
https://twitter.com/QuinnyPig/status/1532724283079700480![Corey Quinn on Twitter: "Corporate Infosec sends a phishing test email, I click, and somehow I'm the asshole because "[I] failed the test; had this been real it would have destroyed the company network"? If me clicking can destroy the network, I'm not the one in this conversation who sucks at their job." / Twitter](/image/screenshot/6548f092e3925834a138e52eccbef8d7.png)
j.d.christopher on Twitter: "Catastrophic failure at an aluminum extrusion line. Looks like an overpressure event and the oil itself (over a drop ceiling no less) open a portal to a demon dimension… https://t.co/VQeM0f85Mw" / Twitter
https://twitter.com/jdchristopher/status/1533089680274731010
Rata ✨ on Twitter: "the best part of Morbius was when he said "IT'S MORBIN' TIME" and morbed all over those guys" / Twitter
https://twitter.com/RANK10YGO/status/1510361009621450761

MakeItHackin on Twitter: "The Hacker TikTok panel will be answering audience questions during our @BSidesSF talk today. Use the link below to submit a question, BUT only from 2:30-3:20pm Pacific time. Choose "Theater 14" for the venue. :) @kyliebytes @notshenetworks @kylekyle https://t.co/tmvqlJ9sEo" / Twitter
https://twitter.com/makeithackin/status/1533479288845922304
SANS DFIR on Twitter: "New @SANSInstitute's #FOR528 #Ransomware for #IncidentResponders teaches how to prepare for, detect, hunt, & deal the aftermath of ransomware Learn more in this livestream with course author @rj_chap https://t.co/jj0HjEum1p" / Twitter
https://twitter.com/sansforensics/status/1533176949148946437
Zero Day Initiative — Is exploiting a null pointer deref for LPE just a pipe dream?
https://www.zerodayinitiative.com/blog/2022/6/1/is-exploiting-a-null-pointer-deref-for-lpe-just-a-pipe-dream
Analysis and Attribution of the Eternity Ransomware: Timeline and Emergence of the Eternity Group - CloudSEK
https://cloudsek.com/analysis-and-attribution-of-the-eternity-ransomware-timeline-and-emergence-of-the-eternity-group/

KnowledgeSharing/CyberSecurity/Web/CVEs/CVE-2022/CVE-2022-30190 at main · NafisiAslH/KnowledgeSharing · GitHub
https://github.com/NafisiAslH/KnowledgeSharing/tree/main/CyberSecurity/Web/CVEs/CVE-2022/CVE-2022-30190?fbclid=IwAR0UczaWjJNKWTnlvZHCXsWhABuae0kDRKx3hj-wo0LS1y8TZ32HR5w9t3w
Hishan Shouketh on Twitter: "The Discovery of the #MSDT protocol abuse opens up a whole new area of attacks surface. Querying the registry, e.g. for MS protocols, "Get-Item Registry::HKEY_CLASSES_ROOT\ms-* | Out-String | select-string -Pattern "URL" -SimpleMatch" #MSDT #follina https://t.co/ZPfSnRQ5r9" / Twitter
https://twitter.com/hishanxp/status/1532245439172468737
signatures/template.suricata-6.0.5.rules at master · c3rb3ru5d3d53c/signatures · GitHub
https://github.com/c3rb3ru5d3d53c/signatures/blob/master/signatures/attack/injection/template/template.suricata-6.0.5.rules
WebDAV Traffic To Malicious Sites | Didier Stevens
https://blog.didierstevens.com/2017/11/13/webdav-traffic-to-malicious-sites/
Andrew Morris @ Blackhat/Defcon on Twitter: "Widespread Atlassian Confluence CVE-2022-26134 exploitation, specifically that is *confirmed functional*, has just started. 23 unique IPs so far. -Tags available to all @GreyNoiseIO users now - Create an account to deploy a dynamic block list to block it https://t.co/dbXTw2LWY6 https://t.co/xXldngWdPH" / Twitter
https://twitter.com/andrew___morris/status/1533139425122713600
sop.png (2000×1253)
https://securityzines.com/assets/img/flyers/downloads/intigriti/sop.png
Ken Johnson Scholarship 2022 | SANS Institute
https://www.sans.org/u/1kYm
Business Email Compromise Scams Are Poised to Eclipse Ransomware | WIRED
https://www.wired.com/story/business-email-compromise-bec-ransomware-scams/
Intelligence or Marketing? Which is it and how to tell using the ADEPT model - Threat Intelligence Academy
https://www.threatintel.academy/intelligence-or-marketing/
GitHub - airbus-cert/ttddbg: Time Travel Debugging IDA plugin
https://github.com/airbus-cert/ttddbg
[QuickNote] CobaltStrike SMB Beacon Analysis | 0day in {REA_TEAM}
https://tinyurl.com/mr3k6svd![[QuickNote] CobaltStrike SMB Beacon Analysis | 0day in {REA_TEAM}](/image/screenshot/9b9d7b9ea9fa766d21fe831c1fc53c91.png)
Exploit released for Atlassian Confluence RCE bug, patch now
https://www.bleepingcomputer.com/news/security/exploit-released-for-atlassian-confluence-rce-bug-patch-now/
Zero Day Initiative — Is exploiting a null pointer deref for LPE just a pipe dream?
https://www.thezdi.com/blog/2022/6/1/is-exploiting-a-null-pointer-deref-for-lpe-just-a-pipe-dream
Get-Item Registry::HKEY_CLASSES_ROOT\* | Select-Object "Property","PSChildName" | Where-Object -Property Property -Match "^URL*" | Export-Csv -path c:\temp\url_all.csv · GitHub
https://gist.github.com/MHaggis/a0d3edb57d36e0916c94c0a464b2722e
Link Found Connecting Chaos, Onyx and Yashma Ransomware | Threatpost
https://bit.ly/3wYK86y
[QuickNote] CobaltStrike SMB Beacon Analysis | 0day in {REA_TEAM}
https://tinyurl.com/mrshmhp9![[QuickNote] CobaltStrike SMB Beacon Analysis | 0day in {REA_TEAM}](/image/screenshot/79260f5dacee66e569ae5c253722a7e5.png)
MalwareBazaar | 103-199-211-138
https://bazaar.abuse.ch/browse/tag/103-199-211-138/
Elon Musk on Twitter: "Some hate humanity, but I love humanity so much" / Twitter
https://twitter.com/elonmusk/status/1533413197629296640