https://whova.com/web/GKSmlhCK%2FWzBY2c8qqJ%2Bp7kNcnjsUQAQJ%2ByBsjLrbOo%3D/
https://whova.com/web/GKSmlhCK%2FWzBY2c8qqJ%2Bp7kNcnjsUQAQJ%2ByBsjLrbOo%3D/
Multi-Factor Authentication | CISA
http://cisa.gov/mfa
GitHub - GhostPack/Invoke-Evasion: PowerShell Obfuscation and Data Science
https://github.com/GhostPack/Invoke-Evasion
Learning Machine Learning Part 3: Attacking Black Box Models | by Will Schroeder | Posts By SpecterOps Team Members
https://posts.specterops.io/learning-machine-learning-part-3-attacking-black-box-models-3efffc256909
Introducing MalSCCM - Nettitude Labs
https://labs.nettitude.com/blog/introducing-malsccm/
Introduction to Firebloom (iBoot) | iBoot_firebloom
https://saaramar.github.io/iBoot_firebloom/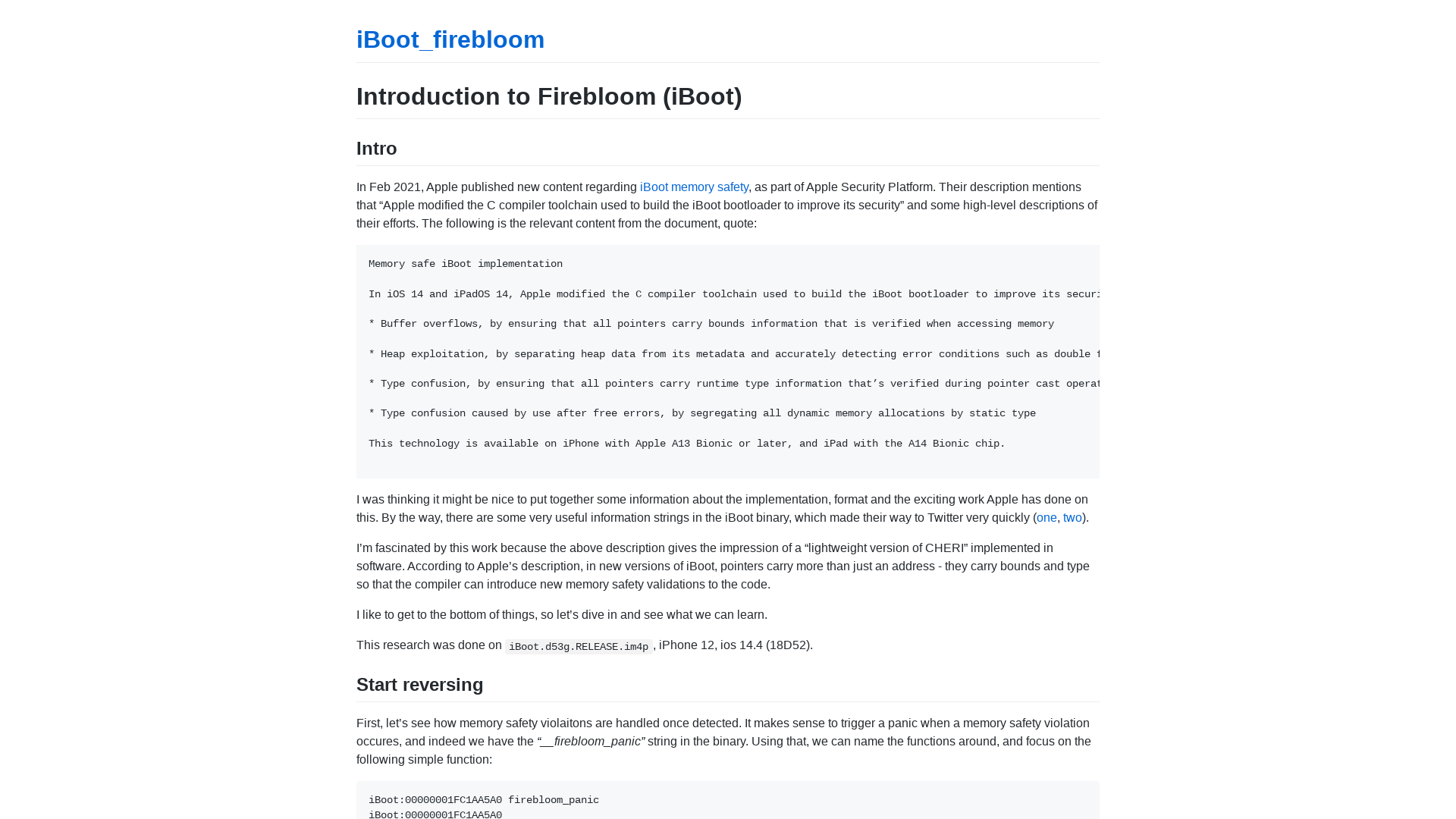
Operation CuckooBees: Cybereason Uncovers Massive Chinese Intellectual Property Theft Operation
https://www.cybereason.com/blog/operation-cuckoobees-cybereason-uncovers-massive-chinese-intellectual-property-theft-operation
BIG-IP iControl REST vulnerability CVE-2022-1388
https://support.f5.com/csp/article/K23605346
Authenticating with certificates when PKINIT is not supported - Almond Offensive Security Blog
https://offsec.almond.consulting/authenticating-with-certificates-when-pkinit-is-not-supported.html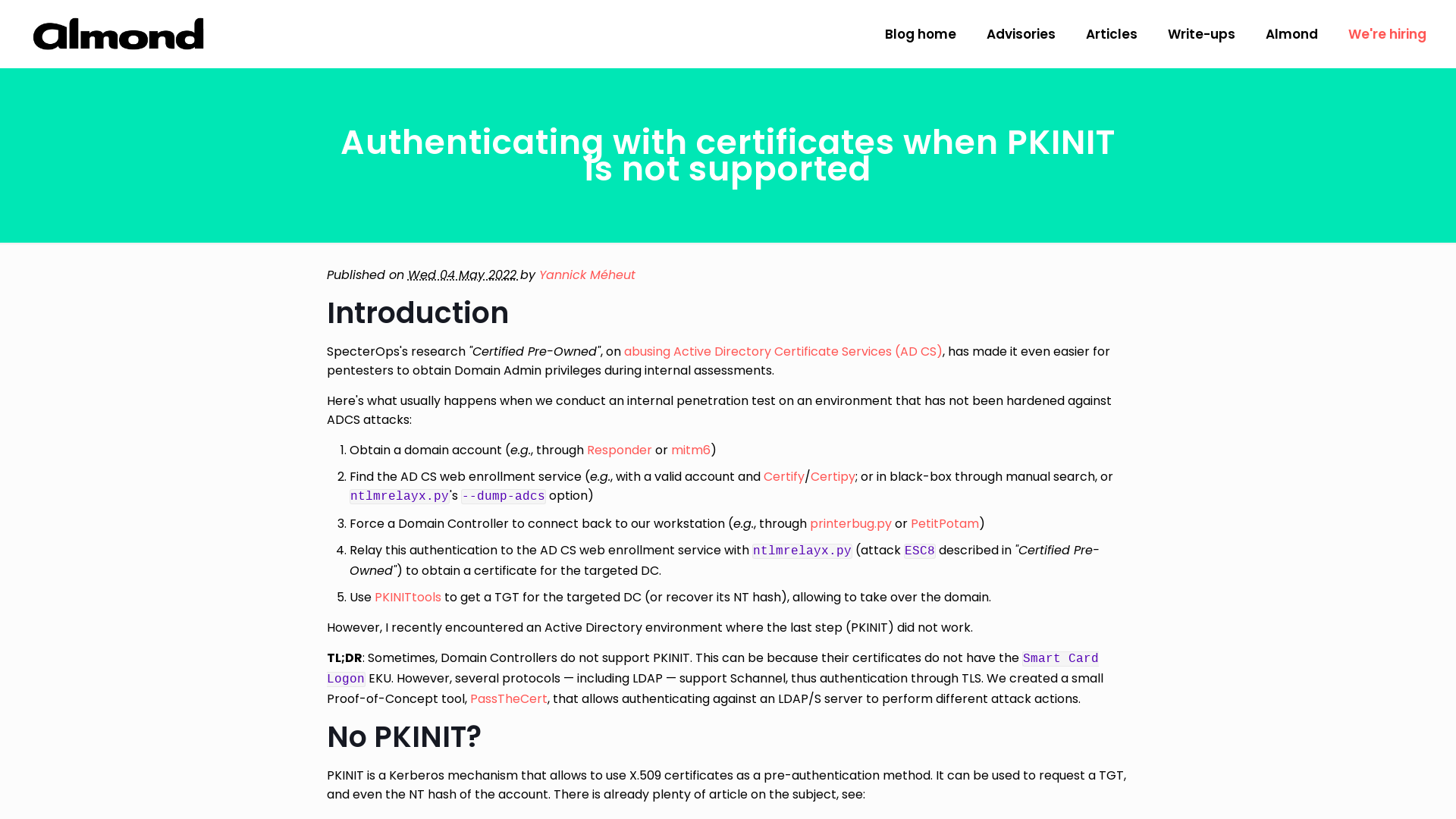
A new secret stash for “fileless” malware | Securelist
https://securelist.com/a-new-secret-stash-for-fileless-malware/106393/

Old Services, New Tricks: Cloud Metadata Abuse by UNC2903 | Mandiant
https://www.mandiant.com/resources/cloud-metadata-abuse-unc2903
The Hermit Kingdom’s Ransomware Play
https://www.trellix.com/en-us/about/newsroom/stories/threat-labs/the-hermit-kingdoms-ransomware-play.html
(1) New Messages!
https://www.cybereason.com/blog/operation-cuckoobees-a-winnti-malware-arsenal-deep-dive
Ransomware Threat Actors Pivot from Big Game to Big Shame Hunting
https://www.coveware.com/blog/2022/5/3/ransomware-threat-actors-pivot-from-big-game-to-big-shame-hunting
(1) New Messages!
https://www.cybereason.com/blog/operation-cuckoobees-deep-dive-into-stealthy-winnti-techniques
| Job Preference
http://www.jobpreference.com
Critical RCE Bug Reported in dotCMS Content Management Software
https://thehackernews.com/2022/05/critical-rce-bug-reported-in-dotcms.html
MalwareBazaar | SHA256 a635b98a8c5fa3cac2deda41b9f9c5b04adf161901c8405b71208062104b895d (BumbleBee)
https://bazaar.abuse.ch/sample/a635b98a8c5fa3cac2deda41b9f9c5b04adf161901c8405b71208062104b895d/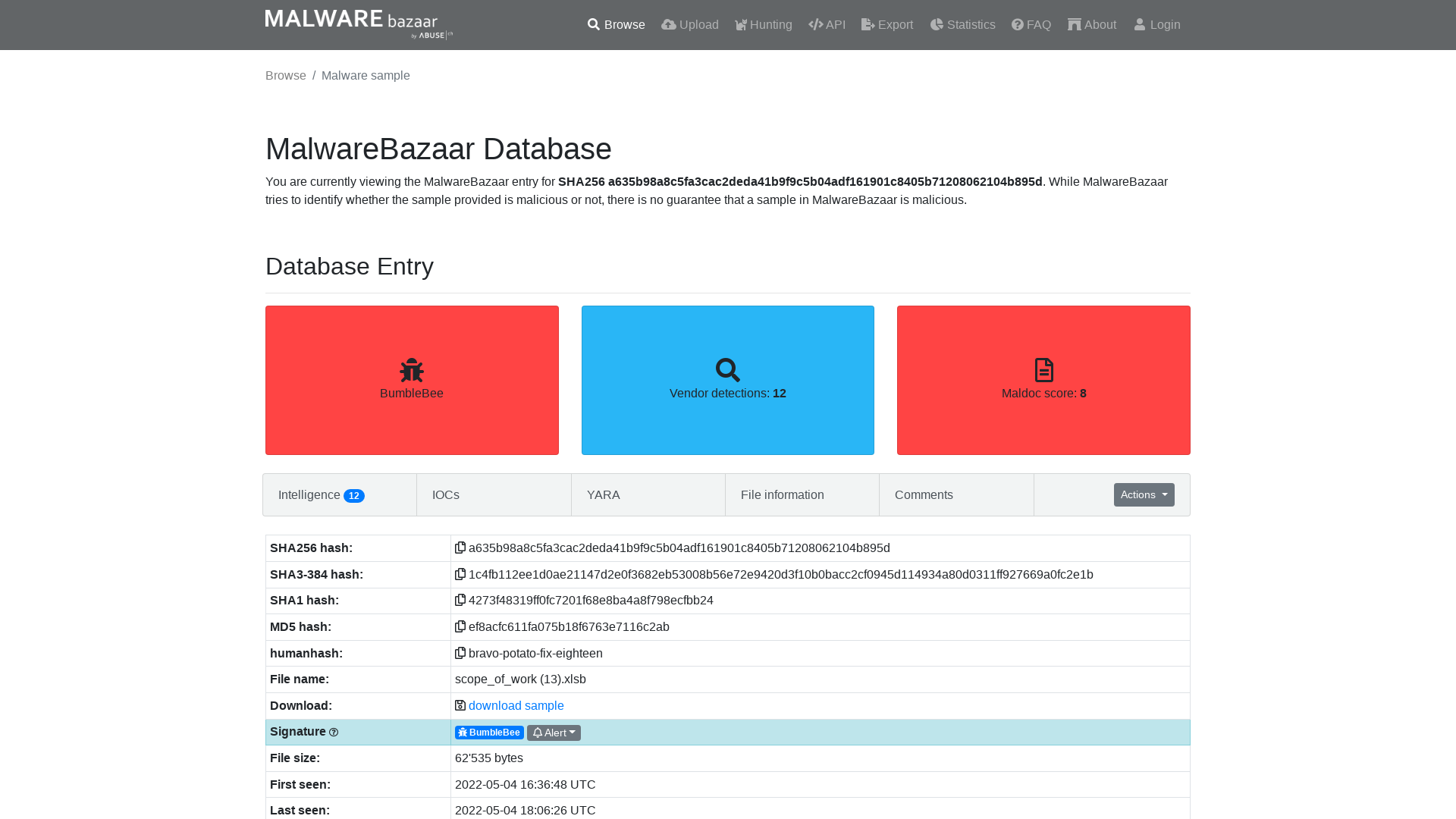
GitHub - trustedsec/ELFLoader
https://github.com/trustedsec/ELFLoader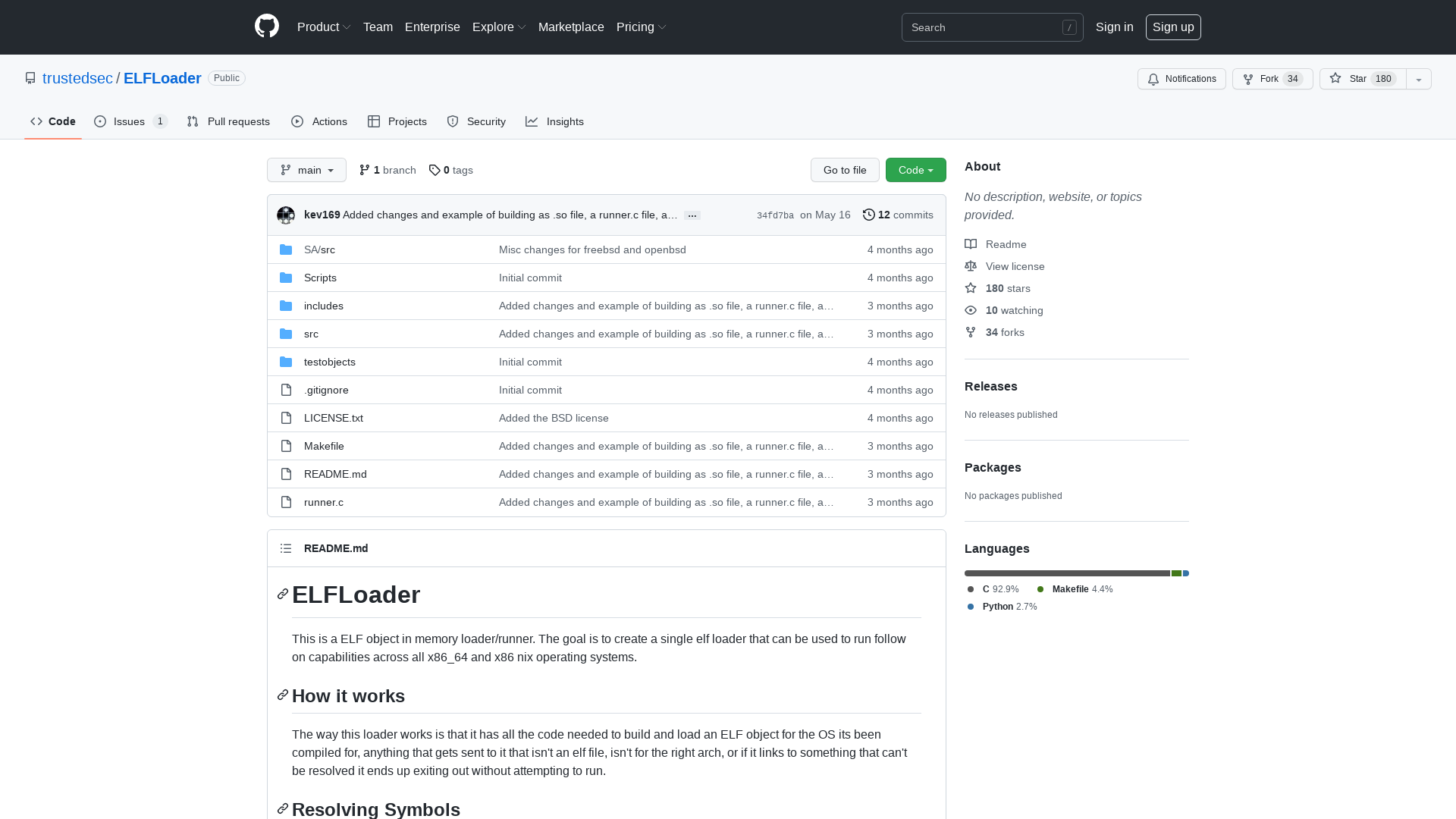
ELFLoader: Another In Memory Loader Post - TrustedSec
https://hubs.la/Q019vMpC0
APIsec: The Only Fully Automated API Security Testing Solution
http://APIsec.ai
Conti, REvil, LockBit ransomware bugs exploited to block encryption
https://www.bleepingcomputer.com/news/security/conti-revil-lockbit-ransomware-bugs-exploited-to-block-encryption/
Ukraine War Themed Files Become the Lure of Choice for a Wide Range of Hackers
https://thehackernews.com/2022/05/ukraine-war-themed-files-become-lure-of.html
Mitsubishi Electric faked safety and quality control tests for decades
https://www.bleepingcomputer.com/news/technology/mitsubishi-electric-faked-safety-and-quality-control-tests-for-decades/