Demystifying Security Research - Part 1 – Blog – Random Security Research
https://alexplaskett.github.io/demystifying-security-research-part1/
mRr3b00t #StandWithUkraine #DefendAsOne on Twitter: "Do you think MSPs (in the main) do a good job for their customers and create appropriately secure environments? #Cyber #Securty #Quality #MSPs" / Twitter
https://twitter.com/UK_Daniel_Card/status/1518170472856309761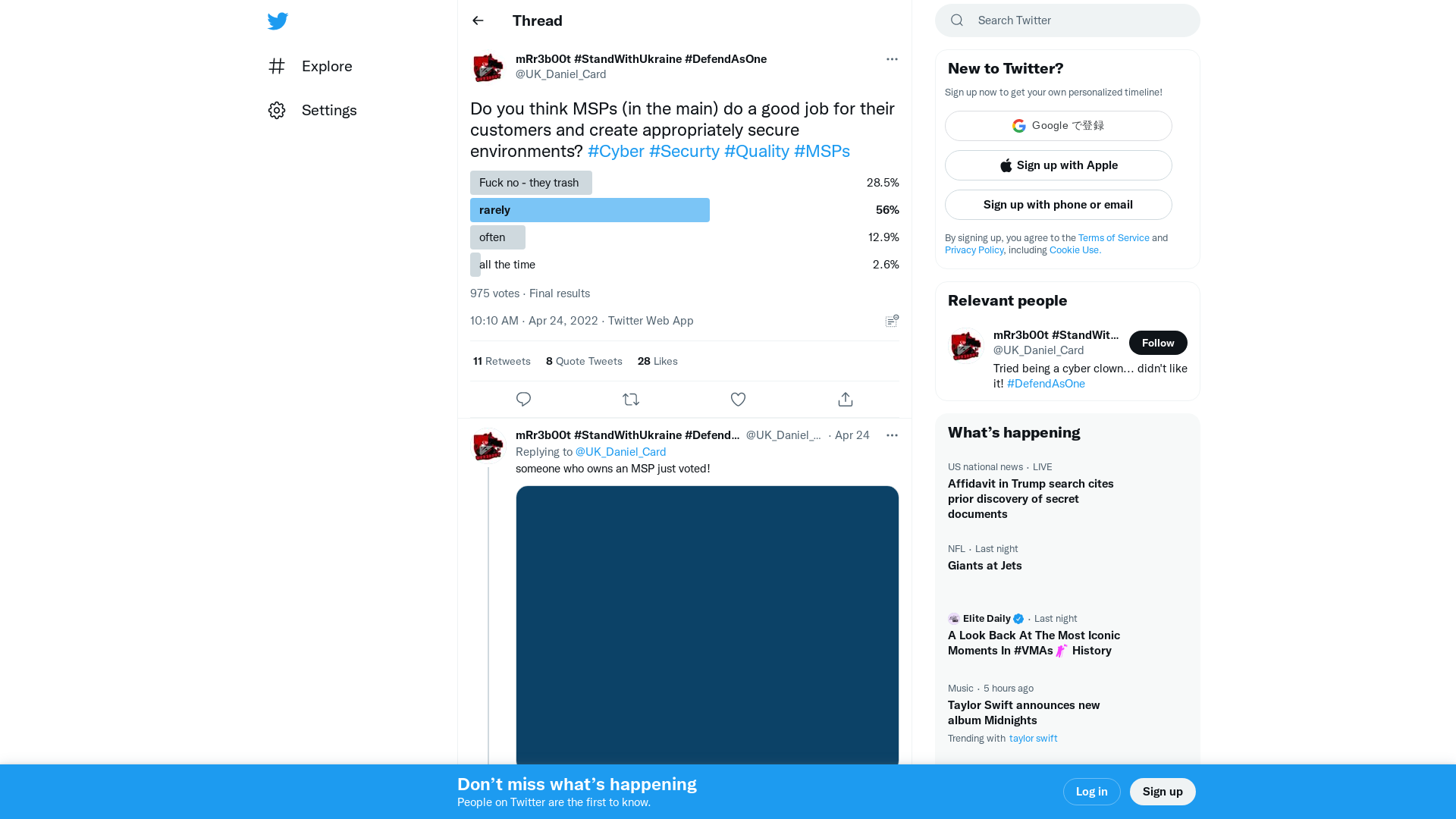
Industrial Cyber Security & IIoT - Cyber Innovation Summits
https://www.cyberinnovationsummits.com/industrial-cyber-security-iiot/
Thanks, but no Thanks, AI. This is a hard pass on anything you… | by Remington Write | The Partnered Pen | Medium
https://medium.com/the-partnered-pen/thanks-but-no-thanks-ai-8d7b39d1604c
| Job Preference
http://www.jobpreference.com
MER CONFERENCE
https://www.merconference.com/page/1901703/registration
Flangvik - Twitch
https://www.twitch.tv/flangvik/
GitHub - glebarez/cero: Scrape domain names from SSL certificates of arbitrary hosts
https://github.com/glebarez/cero
Tarrask malware uses scheduled tasks for defense evasion - Microsoft Security Blog
https://www.microsoft.com/security/blog/2022/04/12/tarrask-malware-uses-scheduled-tasks-for-defense-evasion/
Active Directory Security Beginner Bootcamp [May 2022]: Earn CRTP | Pentester Academy
https://bit.ly/3CPKfUy![Active Directory Security Beginner Bootcamp [May 2022]: Earn CRTP | Pentester Academy](/image/screenshot/b9d88269d53f0543a35d7f2dc22fdb91.png)
Home - PowerofTenOnline.com
http://PowerofTenOnline.com
[Video] Exploiting Windows RPC - CVE-2022-26809 Explained | Patch Analysis - MalwareTech
https://www.malwaretech.com/2022/04/video-exploiting-windows-rpc-cve-2022-26809-explained-patch-analysis.html![[Video] Exploiting Windows RPC - CVE-2022-26809 Explained | Patch Analysis - MalwareTech](/image/screenshot/e73da507aa52831e576bfd3a64cd042a.png)
