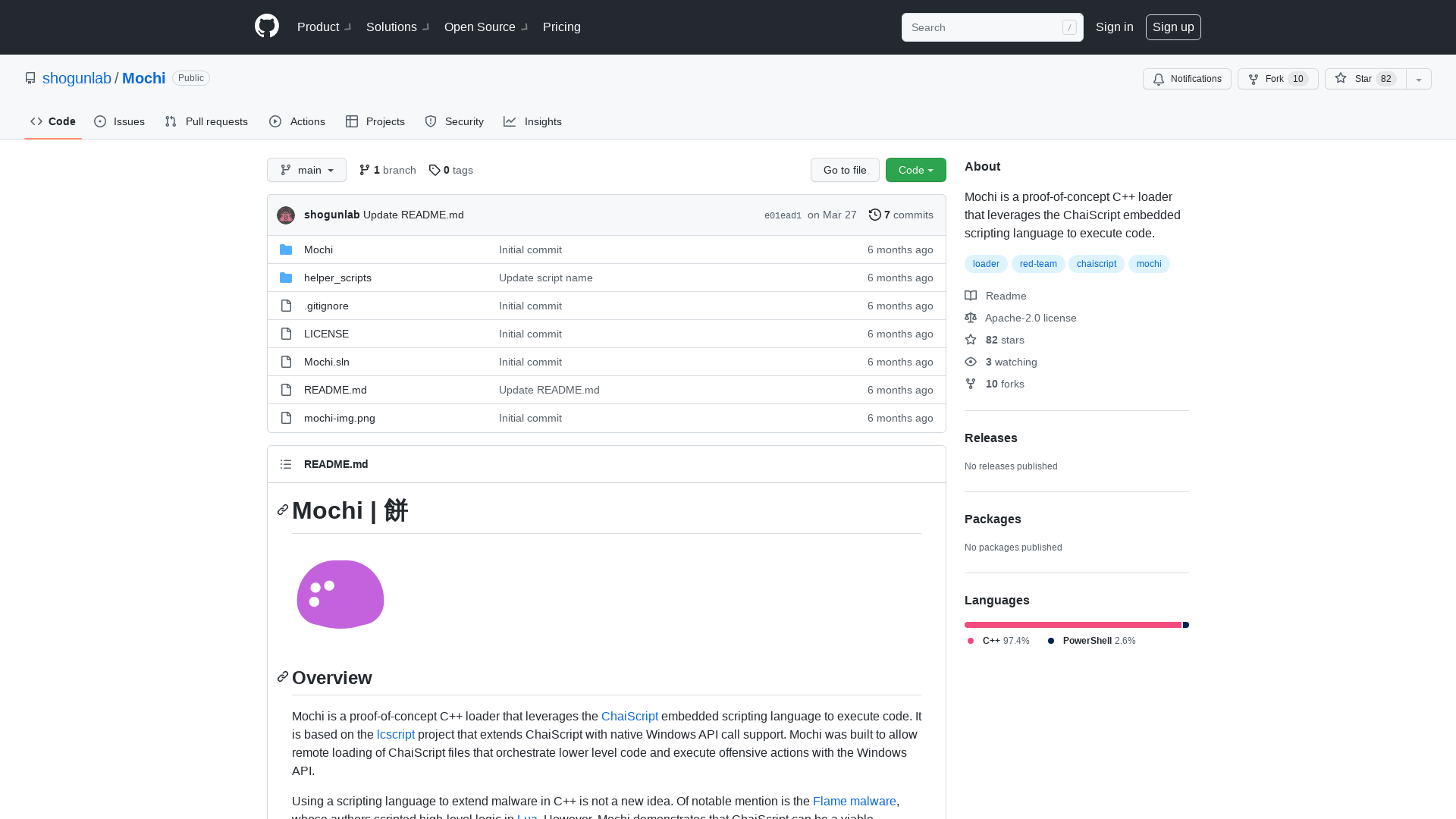
GitHub - Bonfee/CVE-2022-0995: CVE-2022-0995 exploit
https://github.com/Bonfee/CVE-2022-0995
oss-security - Re: zlib memory corruption on deflate (i.e. compress)
https://www.openwall.com/lists/oss-security/2022/03/26/1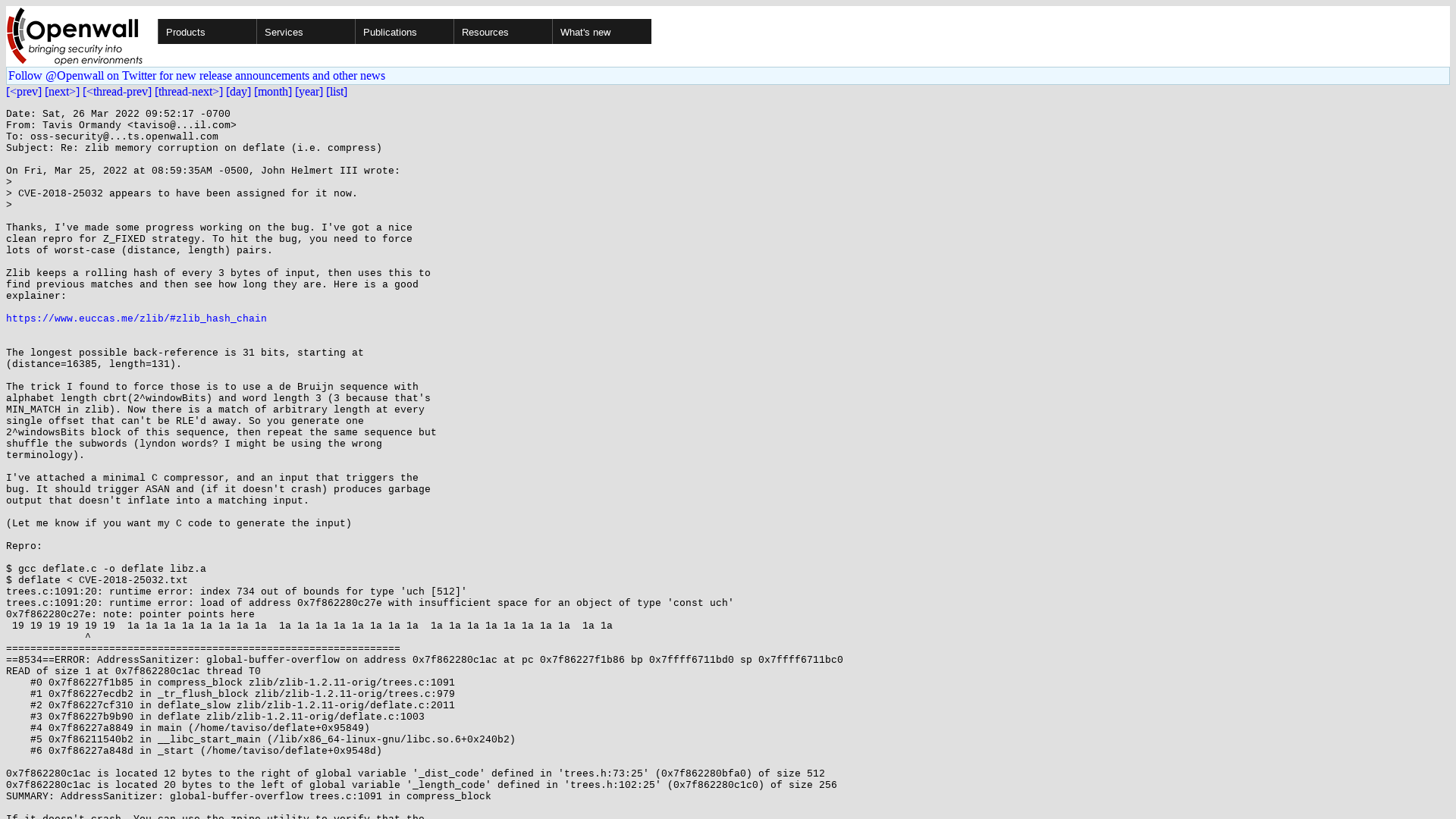
SymbolicExecutionDemystified/Symbolic Execution Demystified 2022.pdf at main · JannisKirschner/SymbolicExecutionDemystified · GitHub
https://github.com/JannisKirschner/SymbolicExecutionDemystified/blob/main/Symbolic%20Execution%20Demystified%202022.pdf
Critical Sophos Firewall vulnerability allows remote code execution
https://www.bleepingcomputer.com/news/security/critical-sophos-firewall-vulnerability-allows-remote-code-execution/
Google issues emergency security update for all Chrome users, zero-day
https://www.forbes.com/sites/daveywinder/2022/03/26/google-confirms-emergency-security-update-for-32-billion-chrome-users-attacks-underway/
GitHub - Sh0ckFR/DLLirant: DLLirant is a tool to automatize the DLL Hijacking researches on a specified binary.
https://github.com/Sh0ckFR/DLLirant
blueblue on Twitter: "GitHub - Throns1956/watchguard_cve-2022-26318: Watchguard RCE POC CVE-2022-26318 - https://t.co/b4MFbOTGaF" / Twitter
https://twitter.com/piedpiper1616/status/1508106160758730758
C++ Memory Corruption (std::string) - part 4
https://blog.infosectcbr.com.au/2022/03/c-memory-corruption-stdstring-part-4.html
InQuest Labs - DFI - InQuest.net
https://labs.inquest.net/dfi/hash/60167b6a14b7da2257cb6cbdc7f1ebcb4bdfa16c76cc9a7539c9b8d36478d127
Okta: "We made a mistake" delaying the Lapsus$ hack disclosure
https://www.bleepingcomputer.com/news/security/okta-we-made-a-mistake-delaying-the-lapsus-hack-disclosure/
WSIS Prizes
https://www.itu.int/net4/wsis/stocktaking/Prizes/2022
Finding bugs to trigger Unauthenticated Command Injection in a NETGEAR router (PSV-2022–0044) | by Flatt Security Inc. | Medium
https://flattsecurity.medium.com/finding-bugs-to-trigger-unauthenticated-command-injection-in-a-netgear-router-psv-2022-0044-2b394fb9edc
Melvin langvik on Twitter: "Going live today at 16:30 UTC , join me for some C2 testing madness https://t.co/t5bf9IbVW8" / Twitter
https://twitter.com/Flangvik/status/1508078257421357058