xnwup on Twitter: "Today, Hackerone took $25k from me, because I am a belarusian citizen. 1/9 https://t.co/1PgBrDF80d" / Twitter
https://twitter.com/xnwup/status/1502789820149608452
Blog: Cyberwarfare is Happening Today. Critical Infrastructure is in the Crosshairs.
https://cybersec.otorio.com/s/cyberwarfare-is-happening-today-critical-infrastructure-is-in-the-crosshairs-3393
Space / Twitter
https://twitter.com/i/spaces/1OyKADomoPDxb
GitHub - six2dez/OneListForAll: Rockyou for web fuzzing
https://github.com/six2dez/OneListForAll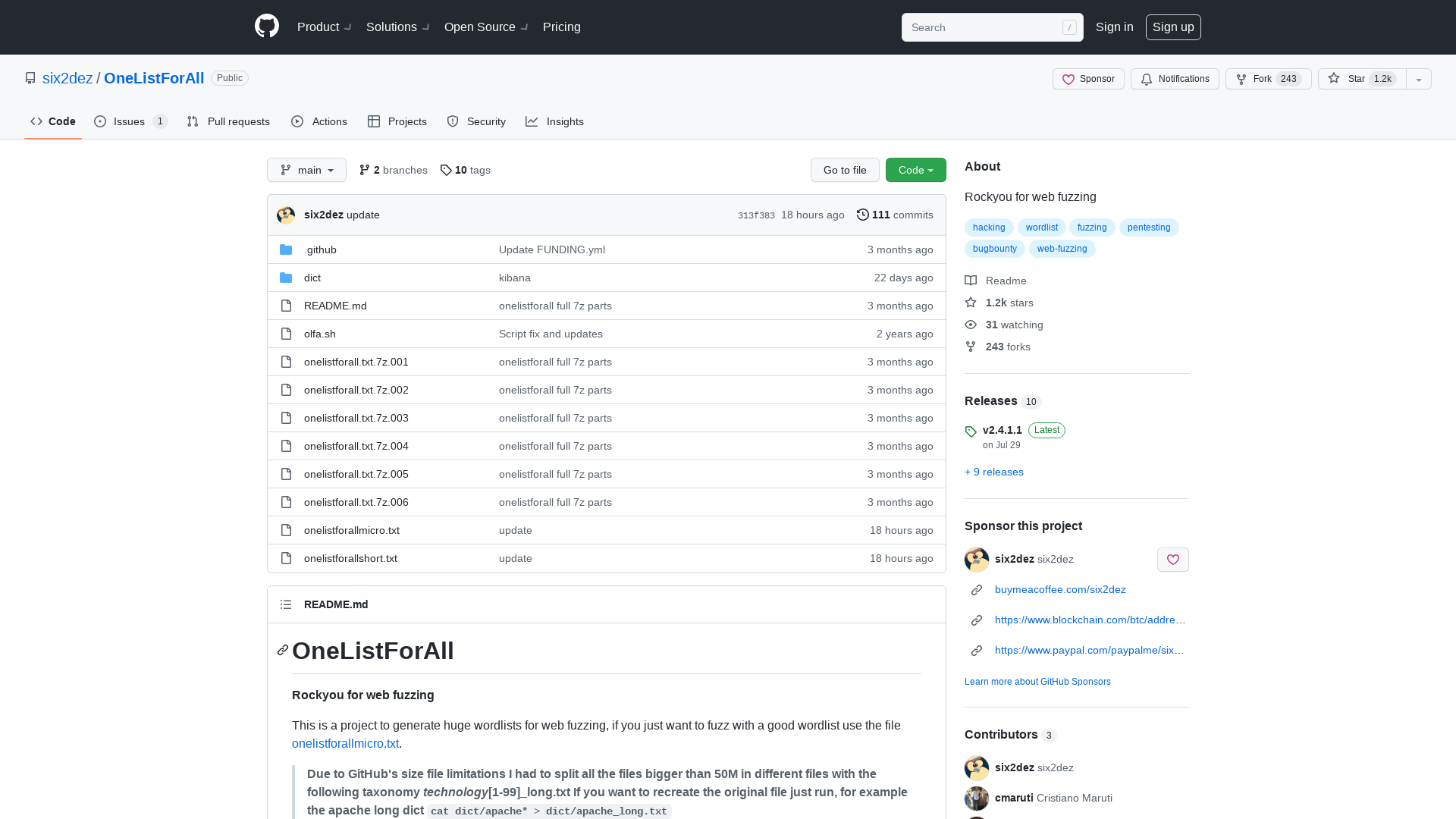
Edwin Weijdema 🇺🇦 on Twitter: "Vulnerability (CVE-2022-26503) in Veeam Agent for Microsoft Windows allows local privilege escalation. An attacker who successfully exploited this vulnerability could run arbitrary code with LOCAL SYSTEM privileges. #veeam https://t.co/Sla74zabkJ https://t.co/1yvp1Ag144" / Twitter
https://twitter.com/viperian/status/1502748344514396167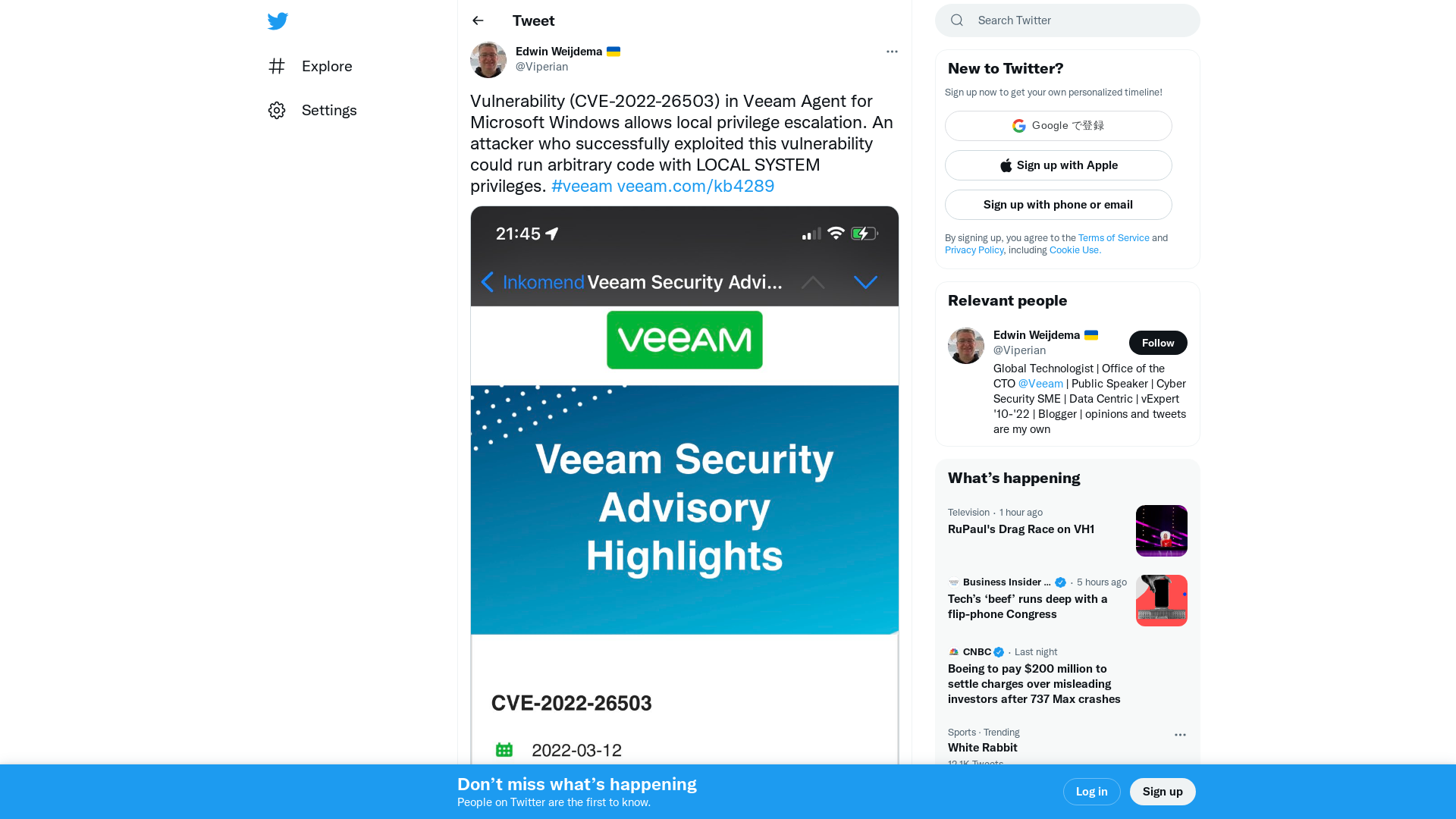
Tutorials « The Legend Of Random
https://legend.octopuslabs.io/sample-page.html
Expert IT Training for Networking, Cyber Security and Cloud | INE
https://bit.ly/3tCo0wS
IDA Python loader for /proc/pid/mem without debugging a process · GitHub
https://gist.github.com/gamozolabs/bade2ac5e69ce7af24a2f6b8c189721c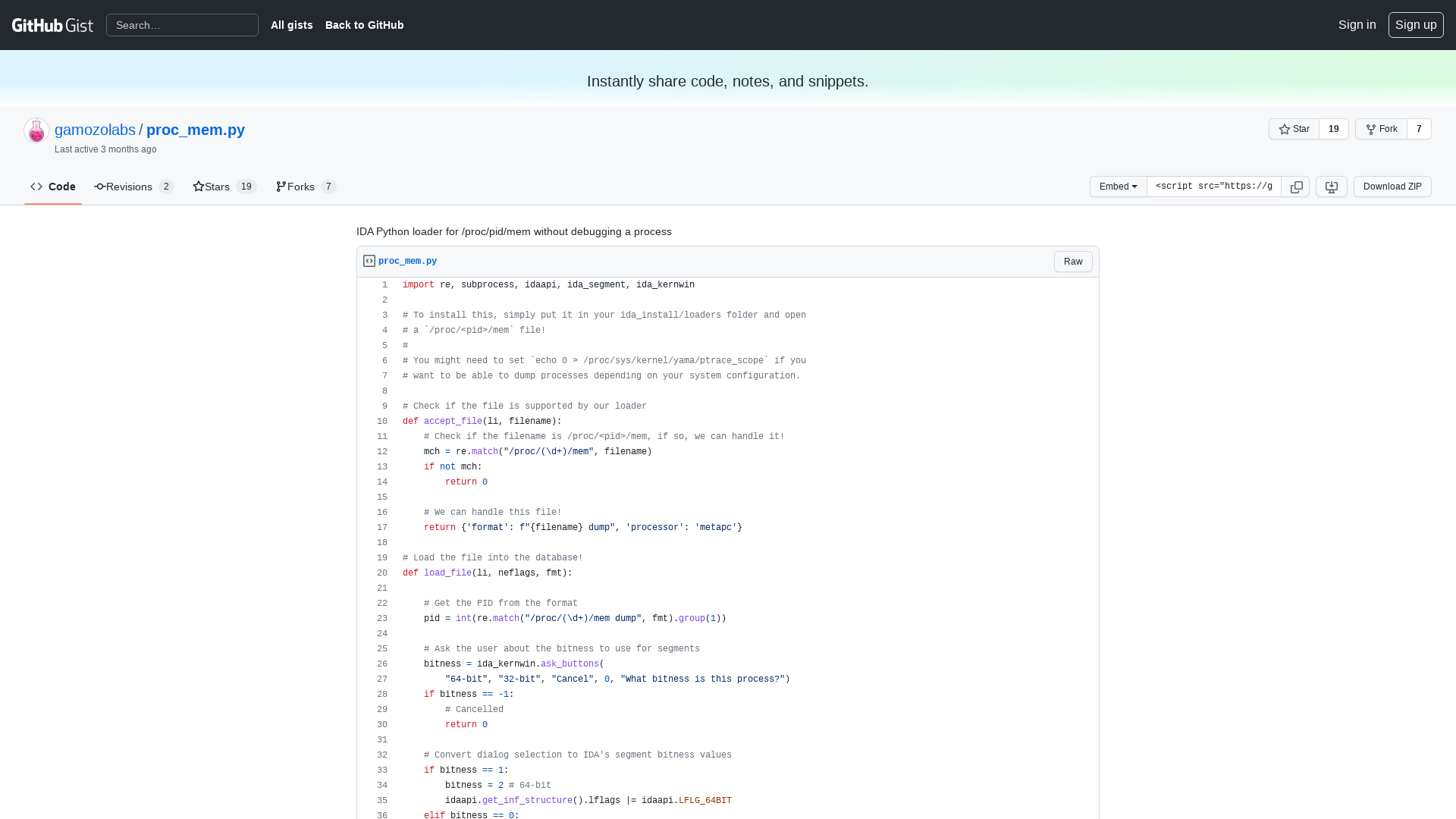
Ubisoft confirms 'cyber security incident', resets staff passwords
https://www.bleepingcomputer.com/news/security/ubisoft-confirms-cyber-security-incident-resets-staff-passwords/
The Discovery and Exploitation of CVE-2022-25636 · Nick Gregory
https://nickgregory.me/linux/security/2022/03/12/cve-2022-25636/
John Lambert on Twitter: "I am preparing for an internal talk on career advice learned from working security crises. My notes 🧵" / Twitter
https://twitter.com/JohnLaTwC/status/1503050104843882496